Sony's latest flagship, the Xperia Z3, comes with some pretty high-end hardware, but what really draws me to it are the aesthetics of its ROM, Xperia UI. Even though my HTC One M8 can still go toe-to-toe with the Z3 in a performance matchup, there is something about Sony's UI that is simply missing from my HTC.

John Kass from the Chicago Tribune and Gary Wiviott, author of Low & Slow, demonstrate how to make perfect ribs. The first step is to run them under cool water and rinse them with cider vinegar to clean them off. Second, coat them with mustard. This holds the rub on the rib. By holding the rub on, you will get more bark (the spicy, smokey, crusty exterior) on your rib. Gary's rub is a mix of 7 different toasted Mexican peppers, paprika, salt, black pepper. Make sure to place a good layer of r...
Paulant Films has some great information on how to download and rip Xbox 360 games. In these four video tutorials, you'll learn how to hotswap, stealth patch, and burn Xbox 360 games.

Samy Kamkar, the security researcher known for the MySpace Worm and his combination lock cracking skills (using an online calculator), is back—and this time, he's after your credit cards!

Are your plants dying? Are they in dire need of some fertilizer? Is your compost not cutting it anymore? Well, save your garden plants with this recipe for nitrogen rich manure tea fertilizer. It's a really easy all natural fertilizer anyone can make. You can collect manure in your pasture or buy it by the bag at a garden center. You can also reuse the manure over and over again. Keep chemicals out of your garden and go green!

tastyfoodtv teaches the viewers how to make Italian chocolate cake in this video. First gather all the ingredients necessary. You'll need 200 grams of almonds, 100 grams of nuts, 6 eggs, 200 grams of butter, 200 grams of dark chocolate, 200 grams of sugar, and yeast for cakes. Break the chocolate into small pieces in a medium-sized bowl. Put the bowl on top of a pot filled with water and put it on the stove. This method will allow the boiling water beneath to melt the chocolate. Next put piec...

This video has a man by the name of Dr. Neder and he has a book by the name, ‘how to be a man in a woman’s world.’ He answers a series of questions. The first question asked is how to get a girl with a boyfriend. The answer this video provides is simply that all girls are looking to date up. Meaning your value and assets, if there is a greater attraction then the girl will end up with you and dump the guy that she is with. Does size matter? The average size of most man is five inches to five ...

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast.

Watch this science video tutorial from Nurd Rage on how to make a chemiluminescent reaction with home chemicals. Make a chemiluminescent singlet oxygen red light pulse from two simple chemicals almost anyone can buy: pool chlorine and hydrogen peroxide.

Welcome back, my budding hackers! One of the most basic skills the forensic investigator must master is the acquisition of data in a forensically sound manner. If data is not captured in a forensically sound manner, it may not be admissible in court. In my Kali Forensics series, I showed you how to acquire a forensically sound, bit-by-bit image of a storage device such as a hard drive or flash drive, but now let's dive into live memory.

This is second post in my series of posts for finding hacked accounts online. Please do read the part 1 of the post at http://null-byte.wonderhowto.com/how-to/find-hacked-accounts-online-part-1-0164611/

Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to broadcast live online.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

So much information exists online that it's easy to get lost in data while researching. Understanding the bigger picture can take a lot of time and energy, but narrowing the question to one that's easy to answer is the first step of any investigation. That's why analysts use open-source intelligence (OSINT) tools like Maltego — to help refine raw data into a complete understanding of a situation.

Google's new Pixel phones are shaking things up in the world of Android, as the Nexus line is no more, and the Mountain View tech giant has now become a smartphone OEM. The long-term impact of these moves remains to be seen, but we already know that Google, the manufacturer, will be adding extra software and UI features to the version of Android that ships with its Pixels.

Verizon Wireless executives recently cooked up a plan so devious that it could have only come from one of the four major US carriers. Apparently, they aren't satisfied with simply loading every Android device they sell with their own bloatware, so now they're reaching out to big brands to see who would be the highest bidder for a spot on your home screen.

Video: . For the first prank you're going to need an empty container, preferably black, a smoke bomb and a lighter. I gotta say though this prank is not for just anybody so prank at your own risk. Let me show you how its done, first apply some hot glue on the bottom of the smoke bomb, then stick it inside the container.

In this video from lachoneus87 we learn how to make silly putty. You need 3 small cups or bowls, warm water, a teaspoon of borax, a big bowl to mix it all in, 2 cups of glue, liquid measuring cup, 1 cup measure, a spoon to mix, and a teaspoon to measure. Optional is food coloring.

Maria demonstrates how to make pita bread. First, she runs hot water over her mixing bowl to warm it. Then, take a cup of warm water and dump it in the bowl. Add one package of active, dry yeast. Then add a tablespoon of sugar. Let that sit for about five minutes. It should bubble up in that time. Next, add a teaspoon of sea salt, two tablespoons of olive oil, and one cup of flour. Using the dough hook on her mixer she stirs in the flour. Next, add a half cup of flour at a time to the mixture...

In this video, Chef Jay shows how to make strawberry cheesecake from scratch. You will need 1 c sugar, 1 tbsp corn starch, 1 tbsp vanilla, 3 large eggs, 1 stick butter, 8-10 large strawberries, 2 (8 oz) packages of cream cheese, 2 c sour cream and 2 c graham crackers. You will also need a small sauce pan, spring form pan and large pan. First, put room temperature cream cheese and sugar into mixing bowl and cream them together. After this, add the eggs in one at a time then add vanilla, corn s...

To make this jelly you will need a food puree-r. Start with a large bowl of blueberries. Take a small amount of the blueberries and put them into a separate bowl and mash them up. You don't want to puree all the blueberries. Dump the rest of the blueberries into the puree and start pureeing them into the bowl with the smashed blueberries in it. Turn the handle a few turns and then add the grapes into the puree-r with the blueberries. Puree the rest of the of the grapes and blueberries until t...

Cleaning a toaster can be tricky if you've never done it before, but this appliance only requires a little bit of your time to keep it clean, safe, and functional.

Impress your friends and become an expert mixologist with drinks that are "stirred, not shaken." You Will Need

Keep your fish healthy and your fish tank clean with these simple steps. You Will Need

Watch this video tutorial to learn how to clean a toaster. The secret to good toast is keeping your toaster clean, and it only takes a few minutes of your time.

There’s an art to packing boxes without breaking your good china—or breaking your back. You Will Need

To some, SCRABBLE is just a board game to play during family game night or during a casual get-together. Others think of SCRABBLE as a mere hobby. But with any activity, there will always be fanatics—the ones who would rather sell their soul than stop—the ones with a constant yearning for self-improvement—the merciless.

If you're a big fan of home improvement, then you've you've probably painted a wall or item in your day. Not only can it get expensive, it's also time consuming, and very often just plain boring. Waiting for paint to dry so that you can add another coat is, well…like waiting for paint to dry.

With the release of various new and updated Samsung Galaxy S6 apps and features, like Smart Switch, Smart Remote, and wallpapers, something that's a home screen staple for most Android users was still missing.

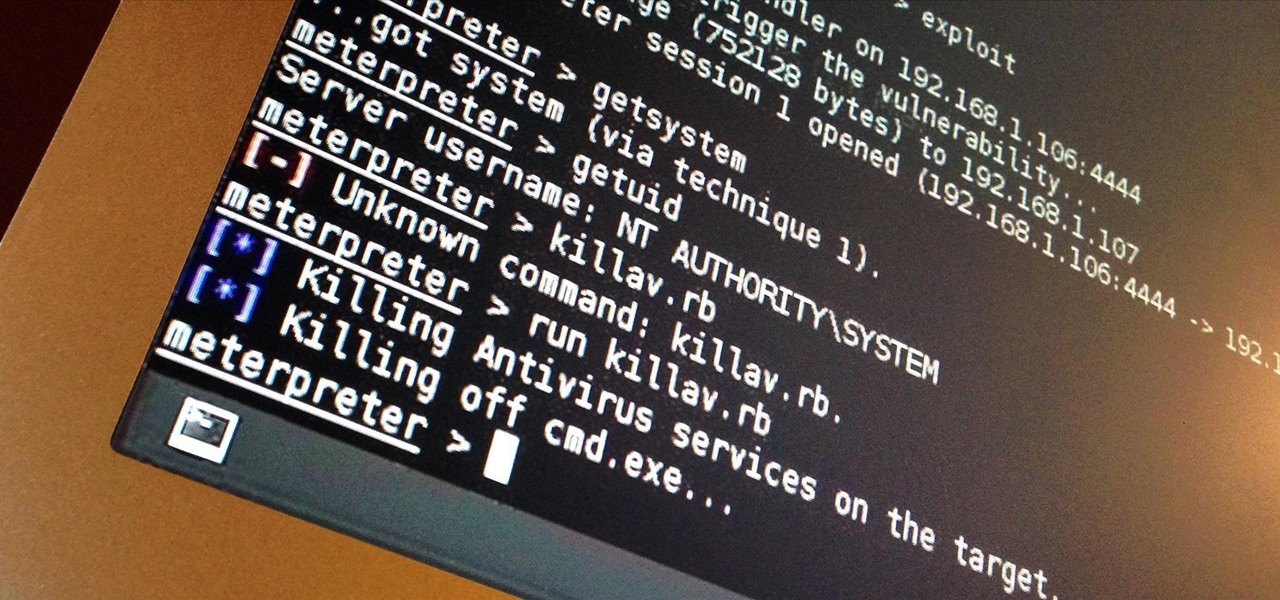
I've done numerous tutorials in Null Byte demonstrating the power of Metasploit's meterpreter. With the meterpreter on the target system, you have nearly total command of the victim.

With the release of the Samsung Galaxy S4 right around the corner, us Galaxy S3 users also have reason for excitement. We already know that many of the S4 features will make their way to our devices, but who knew it would be this soon!

Legal Services A group of lawyers refused to provide legal services to needy AARP members for $30 per hour, but when asked to do it for free, they readily agreed.

With the Xperia Z release for most major U.S. carriers expected sometime very shortly, many are both excited and curious at Sony's new flagship device. Much of the hype surrounding the new smartphone has stemmed from several ads that Sony has released, touting their waterproof phone to be as innovative as their Trinitron, PlayStation, and Walkman brands. Your worries about dropping your phone in a tiny fishbowl are finally over.

While the heyday of the Slinky may have been a few decades ago, I still think it's one of the coolest toys to ever go to market. Not to mention it probably has the best commercial ever created.

As a technology writer, phone screenshots can pile up on your computer in no time. Testing out different apps, showing buggy software, and doing step-by-steps can lead to a plethora of mobile screenshots piling up on your computer's desktop. The problem with my screenshots is that they save as photo.png or photo.jpeg, as do many of my other photos. If I haven't finished a project or article, I tend to move them to different folders to save them for later. After a while, the screenshots begin ...

Halloween is less than a couple weeks away, so it's about that time you start thinking of cool ways to decorate your house (if you haven't already), and pumpkins are an obvious choice. Pumpkins are one of the cornerstones of Halloween celebrations, dating all the way back to the early 19th century. Carved jack-o'-lanterns are a great way to add some spookiness around the house, but that takes time, skill, and effort. Creating cool glow-in-the-dark pumpkins requires no carving at all—and looks...

First you make the crust by putting a bowl of flour and a bowl of brown sugar together into a large bowl. Whisk the flour and brown sugar together in the bowl. Next add two sticks of margarine cut up into smaller pieces. Use a pastry cutter and work the butter into the mixture until you have a bowl full of small uniform chunks. Next pour the mixture into a parchment lined baking pan. It will look really crumbly but that's okay. Once it is poured into the pan use your hand to smooth it out and...

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.

It's that time of year when high school students say goodbye the their past four years of coddling, ready to enter the "real world" and the next chapter of their lives—college.