
Hack Like a Pro: Linux Basics for the Aspiring Hacker, Part 14 (MySQL)
Welcome back, my greenhorn hackers!


Welcome back, my greenhorn hackers!

So your friend started humming "Who Let the Dogs Out" and now you CAN'T get it out of your head. Oh yes you can! This helpful little video shows you what unhearit.com can do for you. This website generates random catchy tunes, so you can dump what's in your head and move on to something fresh. Here comes Lady Gaga!

It's not the best part of owning a pet, but somebody's gotta do it. You Will Need

Developed by Open Whisper Systems, Signal is a free, open-source encrypted communications app for both mobile and desktop devices that allows users to make voice calls, send instant messages, and even make video calls securely. However, a vulnerability was recently discovered for the desktop version that can be turned into a USB Rubber Ducky payload to steal signal messages with a single click.

Back in the '80s, I was just a kid with a LEGO hobby. I remember building castles and floating boats, spaceships and monster trucks, even a working LEGO train powered by battery, lights and all.

GardenOfImagination demonstrates how to make clay molds. To make clay molds with rubber stamps you can use your scrap clay. First, you need to condition your clay by working it in your hands. This will make it easy to work with and get all of the wrinkles in it. Then roll it into a ball and flatten it out just a tiny bit to get it ready for the rubber stamp. Next, pick out the rubber stamp you wish to use for your mold. Make sure that the clay is spread out to the size that you need. Then tak...

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

Hearthstone, Blizzard's online card game, combines strategy with a fun spin on the World of Warcraft lore to create a unique experience. With the latest expansion (The Witchwood) on the horizon, you'll want to make sure your collection is ready for when the set drops in April. Fortunately, you can get free packs on iPhone or Android to help prepare.
If you're a Harry Potter fan who has ever wanted to have your own Hogwarts adventure, you're in luck — Jam City is close to releasing "Harry Potter: Hogwarts Mystery," a mobile game that allows you to attend the magical school yourself. In fact, it's so close you can pre-register for the game right now.
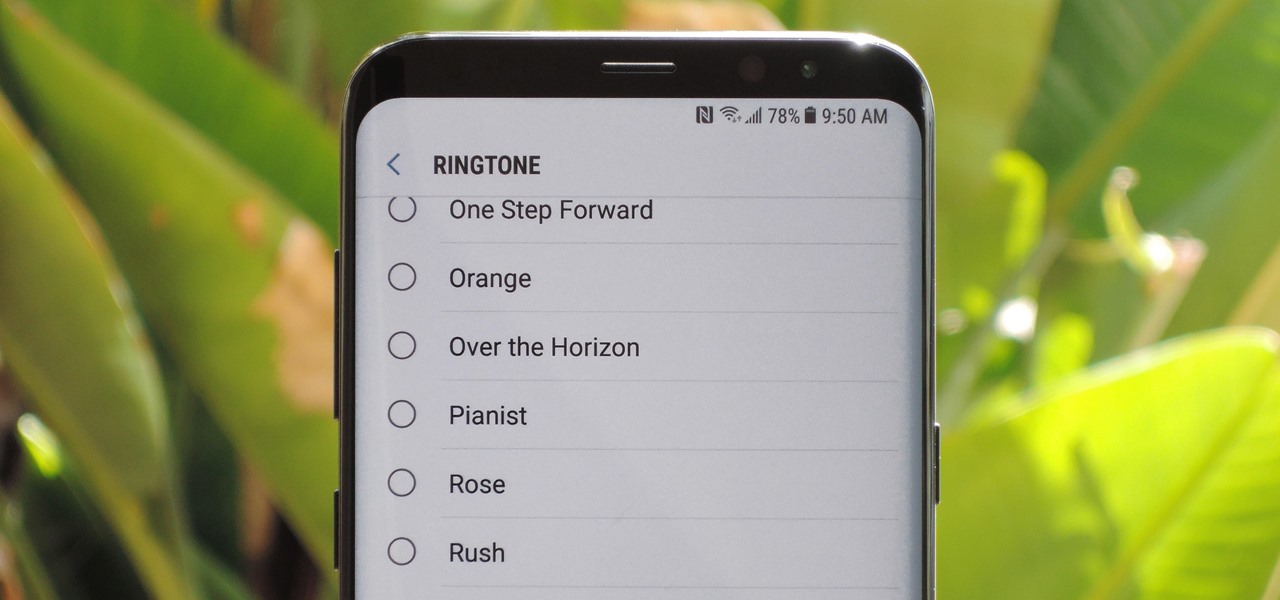
The Galaxy S9 was announced February 25, and it's jam-packed with features like AR Emojis and and a Dual Aperture camera. You really love the cut of its jib, but maybe you don't have the means to get your hands on one. Well now, you can get the Galaxy S9's notification sounds and ringtones, to help you feel like you own one.
Tuesday gave us what I am dubbing a "patent dump." Can you blame me? The U.S. Patent Office released 56 patents from Apple. 56! Among them, there are patents confirming Apple is working on embedded Touch ID, edge-to-edge displays, and a 3D camera system (surprise, surprise). Some of those things we've heard rumors on for some time, but what is new is one of the patents hidden amongst the bunch, describing an Apple-made avatar system. One whose end-goal is to reflect your current emotional sta...
Google worked with design agency B-Reel to create some unique wallpapers for its Pixel and Pixel XL flagships, and the end result is quite stunning. These "Live Earth" wallpapers, as they're called, combine Google Earth's high-def satellite imagery with a 3D parallax effect that changes perspective as you move between screens.
As the first phones to be made by Google, the new Pixel and Pixel XL have several slick customizations that you won't find on any other Android device. There's tons of functional stuff like the new Google Assistant and a much-improved camera app, but also a few aesthetic tweaks to help class up the joint.
A few months ago, LlabTooFeR leaked a full system dump from Google's then-unreleased Pixel and Pixel XL smartphones. That may not seem like a big deal at first glance, but the system dump contained all of the preinstalled apps and services from Google's new flagships—including the much-anticipated Google Assistant.

It's fall—so whether or not it's cold in your part of the world, it's time for apples and anything apple-related. (Please, don't get me started on pumpkin things. Seriously.)

Most augmented/mixed reality hardware still exists in the development stage, whether that's one of the more robust headsets or a high-powered smartphone. Most everything else isn't widely used or monetized. Snapchat, however, snuck in under the radar and created the foundation for the first social network to focus on augmented reality.

This is a familiar scenario: you light up the grill, get cooking, eat the fruits of your labor, then clean up every trace of your barbecuing once you're finished — except maybe the hot charcoal, which usually gets dumped right before the next cookout.

The following are 10 simple yet effective pranks you can set up around the house, school or the office on April Fools' Day. You'll won't need any special tools or materials to pull these off.

In this article I will show you how to obtain victim's credentials without cracking any hashes. There are a couple of ways to perform this task (for example dumping the SAM file and cracking the NTLM hashes), but here I will explain how to do it using PowerShell and a bit of social engineering. We are going to create a fake login popup.
Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1
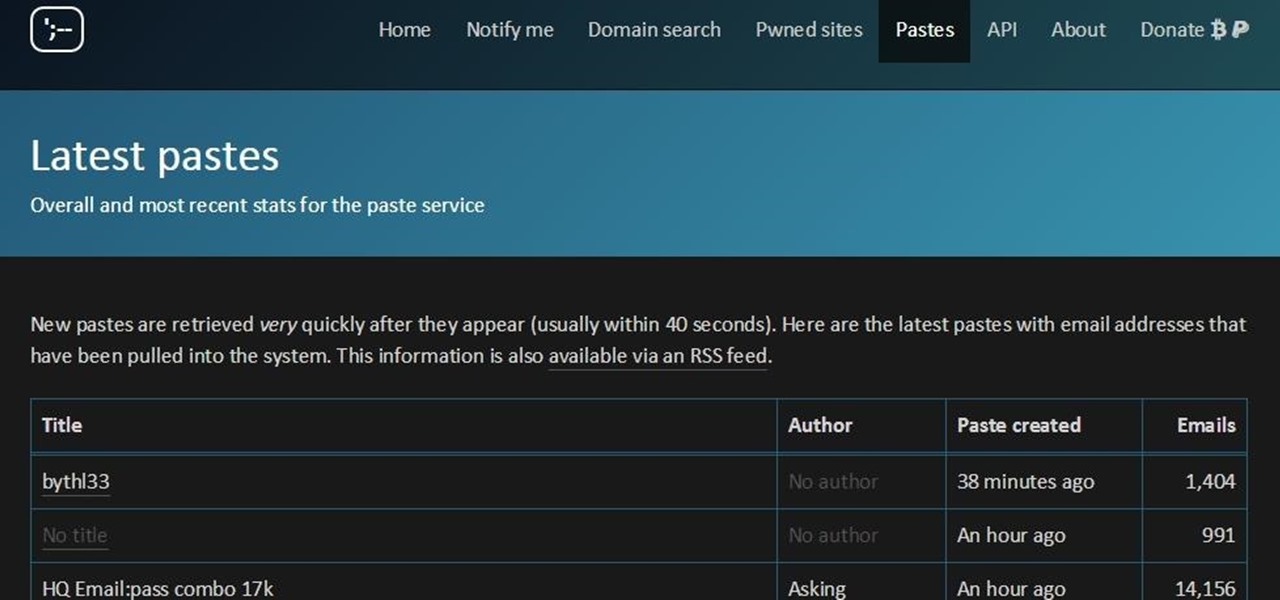
You must have read news about hackers dumping the data online, recent one was Ashely Madison. It's only the big companies' data, which gets noticed once it is out. There are many other small leaks which don't even get a mention. So this article is the first one of my series which will help you to find hacked accounts. Some of you must already know about this, but this post is intended for the new learners. This also serves as an example of my learning how a good service can be used in other w...

Though you can use the Social Engineering Toolkit to clone websites, this way is much more customisable.
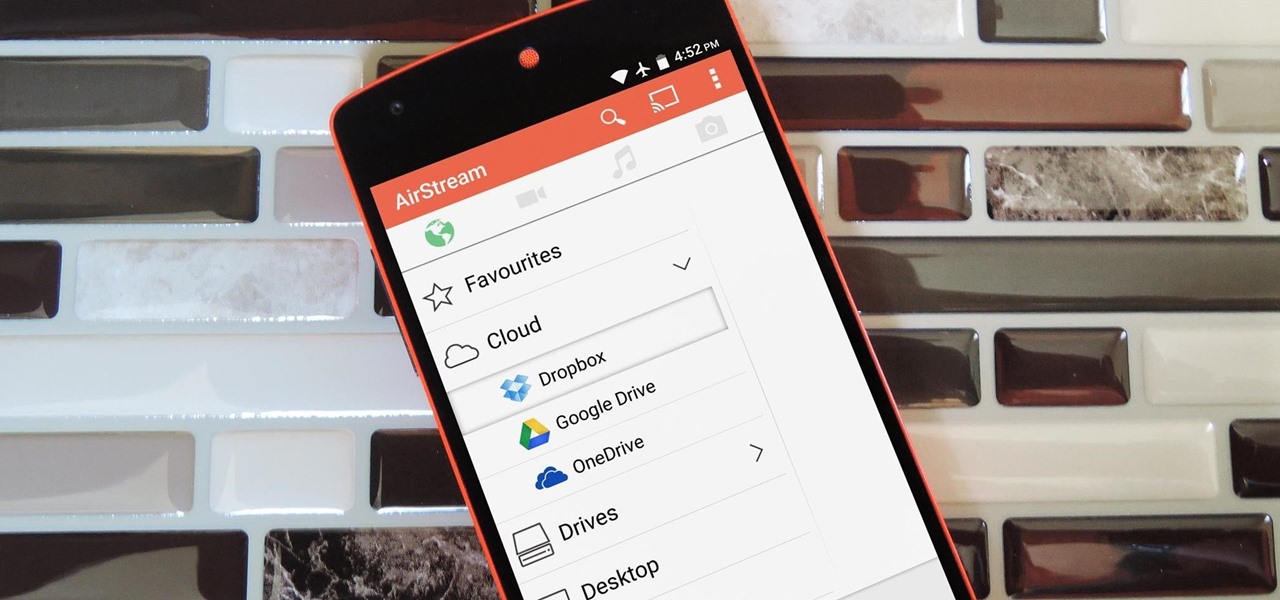
Smartphones generally have limited storage, but counter this issue with an always-on internet connection. This led to the proliferation of cloud storage services, which allow us to store and access our large media libraries remotely.

As carriers finalize their variations of the Android 4.4.4 update, we're left with only brief glimpses of what the new "Eye Experience" holds in store for us while we wait. However, thanks to a system dump of an updated European HTC One M8 and some clever hackery by donmarkoni, we can now install the new camera app on any variant of the HTC One M8.

While living alone, I grew to enjoy cooking. Not only was it necessary to my existence, but it was cheaper than eating out. One thing I really came to love was garlic, especially its smell. If a recipe didn't ask for it, I added it anyways.

It's so nice to be able to reuse old glass jars for food storage. Occasionally, though, even the sturdiest container has to be recycled because it retains the smell of its previous contents. Usually the culprit was garlic, garlic-based, or something pickled, and you're certainly not going to store your fresh herbs or fruit in that. There is, however, a quick and easy way to get that old stink out of your jar and make it usable again. You just need two things...

Toilet paper isn't the first thing that comes to mind when you want a hot meal, but when you're camping or out in the field (i.e. military training), a little TP is the difference between cold tuna and luxury.

The Google Play Store exists so you can download as many apps as your heart desires (and as your memory can hold). Sure, you may only use them once, but it's your choice—and isn't that what life is really about? With that said, the Samsung Galaxy Note 2 already comes with a ton of preloaded apps from Google, Samsung, and your device carrier, like Yellow Pages and Google Earth—both of which I never use. So why is it that Android won't let me remove or uninstall them?!

Welcome back, my greenhorn hackers! Several of you have you have emailed me asking whether it's possible to install a keylogger on a victim’s computer using Metasploit. The answer is a resounding "YES"!
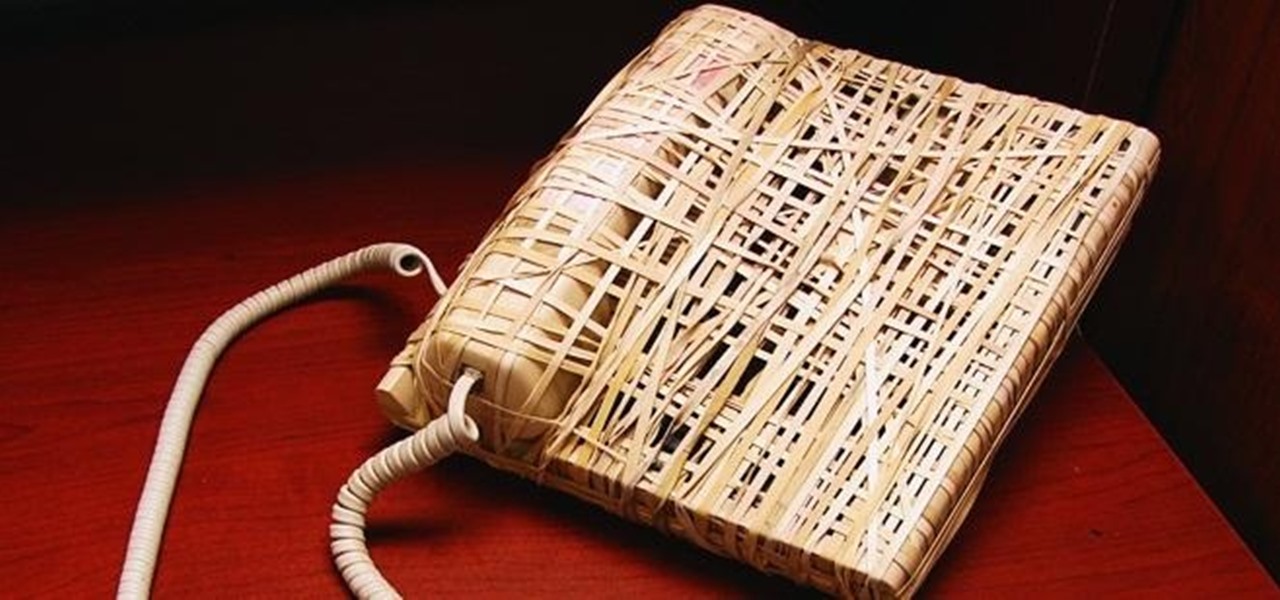
In college, I enjoyed eating, sleeping and making my roommate's life a living hell. My most satisfying prank involved 500 red cups stapled together, filled with water, and strewn across his bedroom floor. He was not happy. To clean up, he had to unstaple each cup, carry it to the bathroom, and dump the water. He was furious, but I was okay with sacrificing our friendship in exchange for a fantastic story that I'll probably tell my grandkids one day. If you're not as cruel as me, there are oth...

This video is a tutorial on how to disassemble and clean a white Apple keyboard. Most of the keys pop out easily, but the bigger ones have metal clips on the back and need to be removed very carefully. Take a picture of your keyboard to remember where each key goes, and don’t lose any.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

Post-exploitation information gathering can be a long and drawn-out process, but it is an essential step when trying to pivot or establish advanced persistence. Every hacker should know how to enumerate a target manually, but sometimes it is worth it to automate the process. Metasploit contains post modules that can quickly gather valuable information about a target, saving both time and effort.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

Welcome back, my tenderfoot hackers! As you should know from before, Snort is the most widely deployed intrusion detection system (IDS) in the world, and every hacker and IT security professional should be familiar with it. Hackers need to understand it for evasion, and IT security professionals to prevent intrusions. So a basic understanding of this ubiquitous IDS is crucial.

Welcome back, my budding hackers! In this series, we are trying to understand how AV software works so that we can learn to evade it. To that end, we are working with the open-source AV software, ClamAV. I had previously introduced ClamAV in Part 2 of this series. If you have not installed it yet, go back to that and install it.

Welcome, in this tutorial we shall we looking at creating a safe(r) way to back up your important files. The contents we will be covering are as follows;

Pizza. It's seen you through your best and worst times. It was there during your first relationship and the subsequent dumping. It got you through college, and maybe even your twenties. Domino's phone number is programmed in your speed dial, and though you won't admit it out loud, you love pizza, you really do.

Welcome back, my amateur hackers!

When I see the words "free trial," I know I'm probably going to have to whip out my credit card and enter in the number to "not get charged." Then I end up forgetting about the trial and want to kick myself in the ass when I see my statement at the end of the month.