Last week, the U.S. Justice Department issued criminal indictments against seven Iranian hackers. These hackers, working for private companies in Iran, are accused of orchestrating DDoS attacks against U.S. financial institutions from 2011-2013 as well as intruding into the control panel of a small dam in Rye, New York. It is thought that these attacks were a response to the U.S. tightening financial restrictions on Iran during those years and the NSA-based Stuxnet attack on their uranium enr...

If you're gluten-free, on a diet, or just cutting the carbs like me, eating a sandwich can be a dangerous game. There are traditional alternatives such as lettuce or egg wraps, but they have their drawbacks: they can't hold as many ingredients, they can be lack flavor when raw and un-rendered, and it's hard to layer the toppings and condiments to create your perfect bite.

I'm starting to wonder if the people at Boston Dynamics have ever watched a Terminator movie. Not just because the robotics company with the oxymoronic name develops machines that are able to move around environments with animal- and human-like agility, but because the people testing them seem to take such joy in openly antagonizing their creations. It's one thing to tempt fate by creating superhuman robots that could potentially end mankind. You've reached a whole new level of hubris when yo...

SentrySafe puts all sorts of measures in place to protect your valuables and important documents. This particular SentrySafe has an electronic lock, four 1-inch bolts to keep the door firmly in place, pry-resistant hinges, and it's able to withstand drops of up to 15 feet. That all sounds great, until you find out that you can open this safe—and pretty much every safe like it—in a matter of seconds using only a magnet. A rare earth magnet, to be precise.
If you read my previous post, "How to Hack into a Mac Without the Password", you know that it is very easy to break into someone's Mac if you have physical access to the computer. Now the question that lies is, how do we protect ourselves from this happening to us? Well, here is a way that guarantees that no one will be able to change your password through OS X Recovery.

So, how does someone keep their hacking life completely secret? What This Is:

If you have seen the movie Fast and Furious 7, you know what "God's Eye" is. Well this might spark interest to you.

Sushi aficionados and Simpsons fans alike know all about the joys of fugu. Known also as blowfish, it's reputed for being tasty if sliced from the correct part of the animal and many even say they experience a "fugu high" after eating the fish. Alas, if you have an unskilled chef, fugu is famous for being deadly.

"Cooking" with liquid nitrogen seems like one of those activities that should be strictly limited to pros who are appearing on Top Chef, but it's the only way you'd ever be able to make Dippin' Dots at home. If that isn't enough of a reason for you to get some LN2 for your kitchen, check out this dose of pretty:

In order to unleash the full potential of your Samsung Galaxy Note 3, you've got to root it. These days, it's easier than ever, and can be done by just plugging your device into a Windows computer and pressing one button. It's so easy, your grandmother could do it, so what's stopping you?

A few weeks ago, Bluebox Security uncovered a bug that could potentially effect 99% of Android devices. Bug 8219321, dubbed the Master Key bug, works by allowing applications with modified code to pass Android's signature verification system, thereby bypassing security measures that normally wouldn't allow these apps to be installed.

"What is dead may never die." That's easily one of the best lines (and episode title) from HBO's Game of Thrones series. While the saying may ring true for the Ironborn, it's not quite as catchy when it comes to batteries.

Who am I? First let me introduce myself. I am Th3skYf0x, an -well lets call it

Approximately 380 billion plastic bags are used in the United States every year. That’s more than 1,200 bags per U.S. resident and more than 54 times the number of people who live on the planet. That's why here in Santa Monica, thanks to a city-wide plastic bag ban, you won't find a plastic bag at any of the major retail stores.

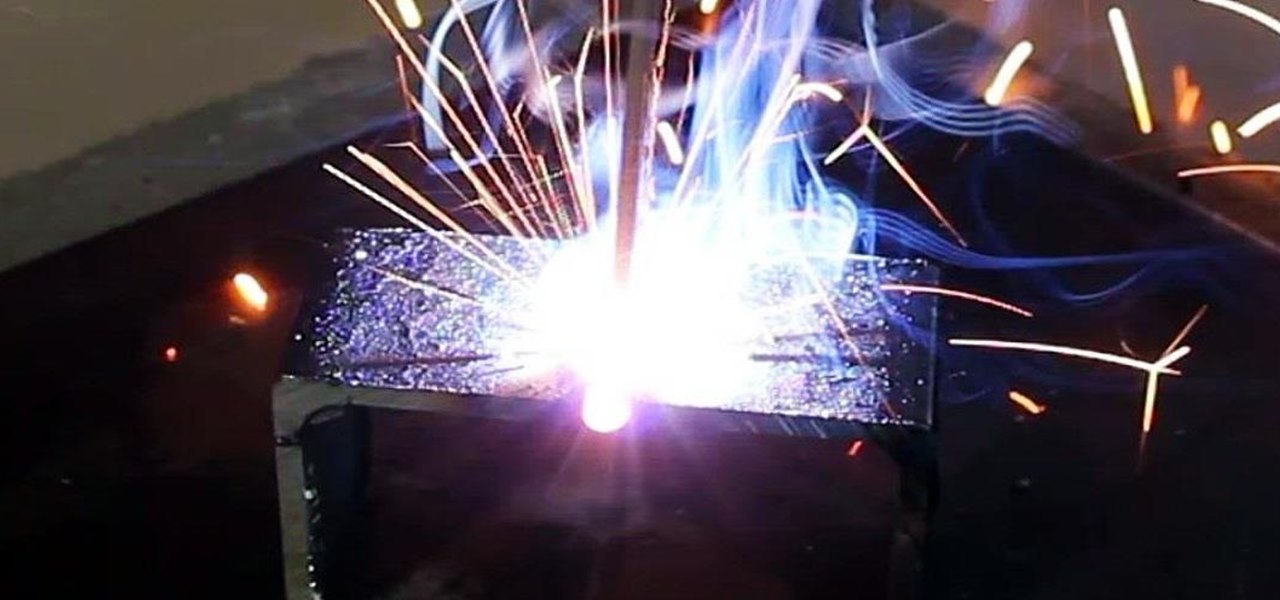
Last time, I showed how to start putting together an AC arc welder from scavenged microwave parts, focusing on the transformer modifications. Now, I'll show you how to finish up your DIY stick welding machine by fixing up the electrical system and performing the finishing touches.

In the Harry Potter world, there was a character by the name of Beedle the Bard, who told a story about witnessing the three Peverell brothers building a bridge out of magic and successfully crossing a very dangerous river that had claimed many lives.

The pumpkin is everyone's favorite cucurbit come Halloween time, and while there are only a few types of Halloween-friendly pumpkins out there, there is definitely no shortage of what you can do with them.

Say whatever you want, but Steampunk is primarily a maker culture. Consider that Steampunk has existed since the 1960s and yet more or less languished in obscurity until approximately 2005, which is when it made the leap to costuming. That costuming was what provided the leap to the tangible, despite the fact that Steampunk art had also existed for years.

It can be incredibly frustrating to take closeup shots with an iPhone camera—or any smartphone camera for that matter. Even if your phone's camera is top of the line, you'll still get a fuzzy picture if you get to close to your subject.

Saw is no longer just a movie, it's a video game, and you can play it on the Xbox 360, PlayStation 3, and Windows. With this video walkthrough series from Committed Gamers, you can BEAT IT (for the Xbox 360).

master! Learn how to do advanced throws with nunchucks, also known as speed chucks. With these nunchuck instructions, the basics of weapon skills and martial arts are within your grasp!

Learn how to sharpen your martial arts skills and weapon basics and use nunchucks (also speed chucks) in this free how-to video series on using nunchucks.

Learn how to shoot a bow and arrow with expert tips and techniques, in this free weapons training video series on archery tips and techniques.

In this martial arts weapon training video series, learn how to use a Hapkido bo staff. Master David Herbert will demonstrate Hapkido staff techniques for striking the stomach, eyes and groin, combination attacks, defense and escape maneuvers, and even how to fight staff to staff.

Whether you're riding the subway on your way home from work, or stuck in the backseat of the car on a long road trip, there are times when you need to entertain yourself without a mobile data connection. A good mobile game would pass the time perfectly, but not every game works without an internet connection.

Will the predicted apocalyptic date—December 21st, 2012—really be the end of the world? In this ongoing five-part series, we examine what would happen if zombies, nuclear weapons, cyber wars, earthquakes, or aliens actually destroyed our planet—and how you might survive.

I've had a handlebar mustache for about five years now, and I've learned a lot over those years about how to grow and care for it. I will now share all of that information with you! Hopefully this will encourage you to grow one for Movember! The first thing I want to address right now is that I do not use wax on a daily basis. I kind of hate using wax, but I still do it on occasion. I shall teach you my secrets, starting from the beginning!

Improve your bo staff techniques and skills for martial arts training with the expert tips in this free martial arts weapon video series.

There are different types of swords used in fencing including and Epee, a Foil, and a Saber. In this series of video clips, you’ll learn more about these different weapons.

Stephen R. Koepfer is the President and Co-Founder of the American Sambo Association & teaches at his club, New York Combat Sambo. SAMBO, sometimes called Sombo, is a martial arts program developed in the former Soviet Union in the 1930s. SAMBO is an acronym which roughly translates to “self-defense without a weapon,” and is one of four wrestling styles of amateur competitive wrestling recognized by the International Federation of Associated Wrestling Styles.

There’s a good chance that you’ll be alone in life one day, and no... I’m not talking about a couch-bound, dateless loser with a pocket pussy and a bag of potato chips. I’m talking about alone. In the wilderness. Hungry. Cold. Lost. You can’t stay in one place too long, so it would be nice to have something to carry your belongings in. Maybe it’s post-apocalyptic land where you’re the sole survivor, and all the backpacks and rucksacks in the world are but mere ash. Either way, knowing this si...

DarkStar One: Broken Alliance is an updated version of the space flight simulation video game DarkStar One (2006), and was made exclusively for the Xbox 360. It features updated graphics and presentation, making it the perfect space flight game for you wannabe astronauts.

For a hacker, there are a lot of advantages to creating a fake network. One advantage forces nearby devices to use their real MAC address if you happen upon a network that's stored in their preferred network list.

Congratulations, you've made it deep into the middle of flu season! If you're reading this, you're either a very smart preemptive sick day prepper, or already in the throes of fighting off a cold or flu situation.

Finland-based Rovio, one of the pioneers of mobile gaming, is now ready to break new ground in augmented reality with its Angry Birds franchise.

They say home is where the heart is. So, the opportunity to view the inner sanctum of Magic Leap is like gaining access to what makes the company tick, just as the fruits of its labor make it into select AT&T stores.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.

In its latest feature with an assist from augmented reality in storytelling, the New York Times shows readers the virtual crime scene it constructed to prove that the Syrian military conducted chemical warfare against its citizens.

For the unaware, RED is a company that specializes in high-end cameras and other recording devices. RED's cameras are used to shoot some of Hollywood's biggest films and TV shows. Their modular designs make them ideal for the user who does a lot of mixing and matching — and has a wallet to back their work up (their WEAPON 8K VV starts at $79,500).