Check out this instructional home repair video to learn how to identify and find your manufacturer's label and model number on your refrigerators and freezers. The model number is usually essential. People make the mistake of assuming that the name and number on the front panel is all you need. Many fridge and freezer manufacturers use the model number as well as the serial number. Most have the ID plate inside of the door by the salad bowl, while some hide it behind the kick plate at the bas...

Arduino is a language that's easy to learn and supported on many incredibly low-cost devices, two of which are the $2 Digispark and a $3 ESP8266-based board. We can program these devices in Arduino to hijack the Wi-Fi data connection of any unlocked macOS computer in seconds, and we can even have it send data from the target device to our low-cost evil access point.

HTC has made it their mission to get updates out to its devices as quickly as possible, with new builds slated for release 90-days after Google finalizes a build—this is dubbed HTC Advantage.

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...

You love your bike and it was stolen. Although, this is not a good scenario, you still may be able to retrieve it. Sketch the serial number or means of identification into the bike and then when it is stolen you can really get the word out to all the places that it might turn up.

Check out this video tutorial on how to get many of the multiplayer achievements in Unreal Tournament III.

This is a steamy part of Heavy Rain for PS3. Steamy and sexy. But this is edited for nudity, so don't worry about seeing anything you shouldn't. See how to beat Chapter 5 - On the Loose.

in this episode of Heavy Rain, you confront the Shark. Just try not to get yourself killed when he pulls out that shotgun. Then, are you going to kill him, or are you not? See how to beat Chapter 4 - The Shark.

Now that the identity of the Origami Killer has been revealed, it should be easy to find him. In this walkthrough of Heavy Rain (PS3), you'll be in the killer's apartment. See how to beat Chapter 5 - Killer's Place.

Is the real killer captured now, or is a different man? Will you leave the case or will you continue the hunt on your own? The Origami Killer may still be out there, and it's up to you to find him. See how to beat Chapter 5 - Solving the Puzzle.

The city is full of reptiles, and in Heavy Rain, the lizard is the most treacherous of all. See if the lizard can get you one step closer to solving the murder mystery of the Origami Killer. Porcelain isn't what it used to be. See how to beat Chapter 3 - The Lizard.

Butterflies are usually sweet and innocent, but not in the downpour that is Heavy Rain. In this PS3 walkthrough, see what's up with the Butterfly and if you're ever going to catch the Origami Killer. See how to beat Chapter 3 - The Butterfly.

Can't sleep? Of course you can't, not with a stage called "Sleepless NIght" in the video game Heavy Rain for the PS3. Watch a walkthrough of this level and see if you can get some zzz's, or see if you should be sleeping. See how to beat Chapter 2 - Sleepless Night.

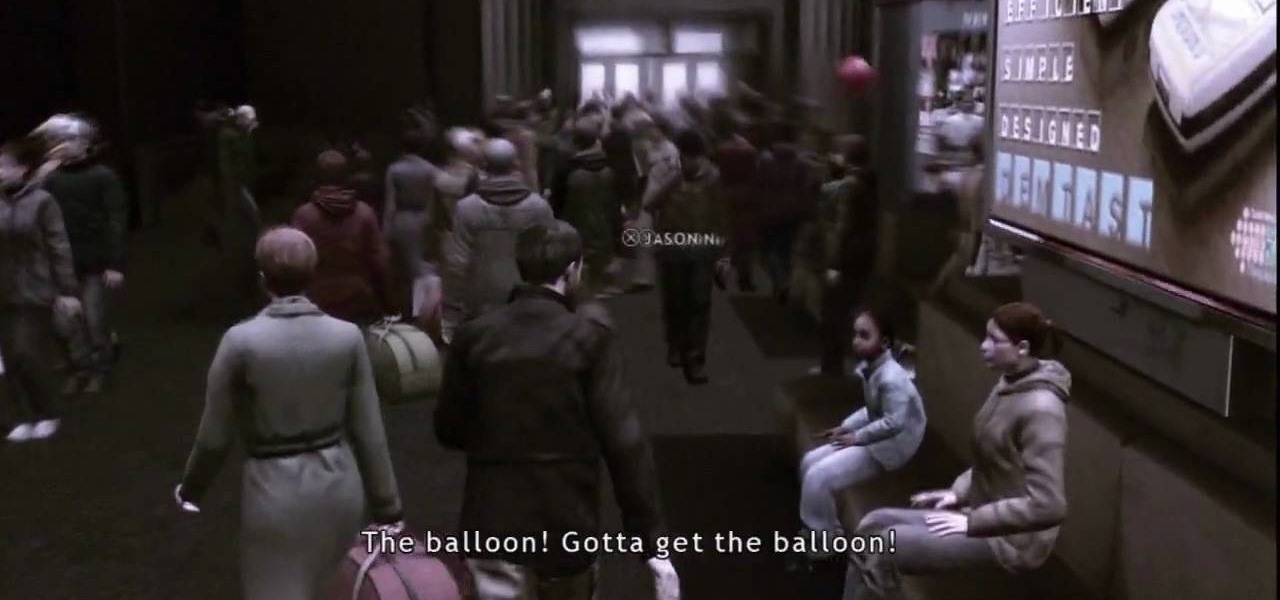
This level of Heavy Rain has you in the Lexington Station, where hopefully you can make it through the crowd without embarrassing yourself. Watch the full video walkthrough to see what happens, and how to continue on. See how to beat Chapter 2 - Lexington Station.

Nothing can beat a father and son. Check out this Heavy Rain video walkthrough for the PS3 on "Father and Son". Do you think you're getting closer to catching the murderous Origami Killer in this level? See how to beat Chapter 1 - Father and Son.

This video tutorial from Magix presents how to burn (S)VCDs and DVDs using Magix Movie Edit Pro 15 application.First you need to group videos you want to burn.If you want to play movies using remote control you have to place chapter markers. You can set markers manually or choose automatic? marker setting which places markers before each new scene.Once all chapter markers are placed, click Burn button.Here you can choose Start Menu Templates. To change movie titles and chapter headings double...

Look at the money you are receiving. Carefully inspect it for any strange colors, marks, or texture. Do not assume that a different color, texture, or design is simply a mistake made at the treasury. The bills there are all made the same based on the denomination.

Superman is one of the greatest and most known superheroes out there. Developed by DC Comics, Superman has seen the world… as in comics, television, newspaper strips, video games, movies, radio serials, etc. See how to make a Superman costume in this video from GiannyL.

When a new jailbreak method comes out, Apple is quick to patch the vulnerability it exploits by issuing a new iOS update. If you were to accept such an update, you'd no longer be able to jailbreak your iPad, iPhone, or iPod touch unless you could roll back your firmware to a version that could be jailbroken. But Apple even takes things a step further and stops signing older iOS firmware versions, which makes downgrading next to impossible. This is where your SHSH2 blobs come into play.

In this tutorial the author shows how to find out a Cool XP Easter Egg hidden in the XP which comes by downloading the latest update of widows update. The author now opens Internet Explorer and visits the windows site. Now he quits the explorer and holds down both the Control key and alt key and right clicks on the desktop seven times. Now keeping the control key pressed, he releases the alt key and right clicks the desktop and chooses the option 'Create ShortCut'. Now he releases all the key...

Mac users know why they love Apple. Of course, there are limitations. An entire universe of shortcuts is unavailable to the average user.

For a hacker, there are a lot of advantages to creating a fake network. One advantage forces nearby devices to use their real MAC address if you happen upon a network that's stored in their preferred network list.

Although there has been much speculation about how much damage could be done if hackers were to take control of a country's SCADA systems, there have been few examples - until a few months ago, with the power outage in Ukraine caused by hackers.

Apple will release tvOS 9.2 for the latest Apple TV today, bringing some major features to the streaming device. The software update, announced at today's Apple event, comes with Siri voice dictation, full iCloud photo viewing, and support for Bluetooth keyboards. Since Apple has already been beta-testing tvOS 9.2 for months, it's ready for a public rollout.

Before you purchased your smartphone or tablet, the device had already embarked on quite a long journey. From product development to manufacturing, your Samsung Galaxy device had already developed a rich history prior to your ownership.

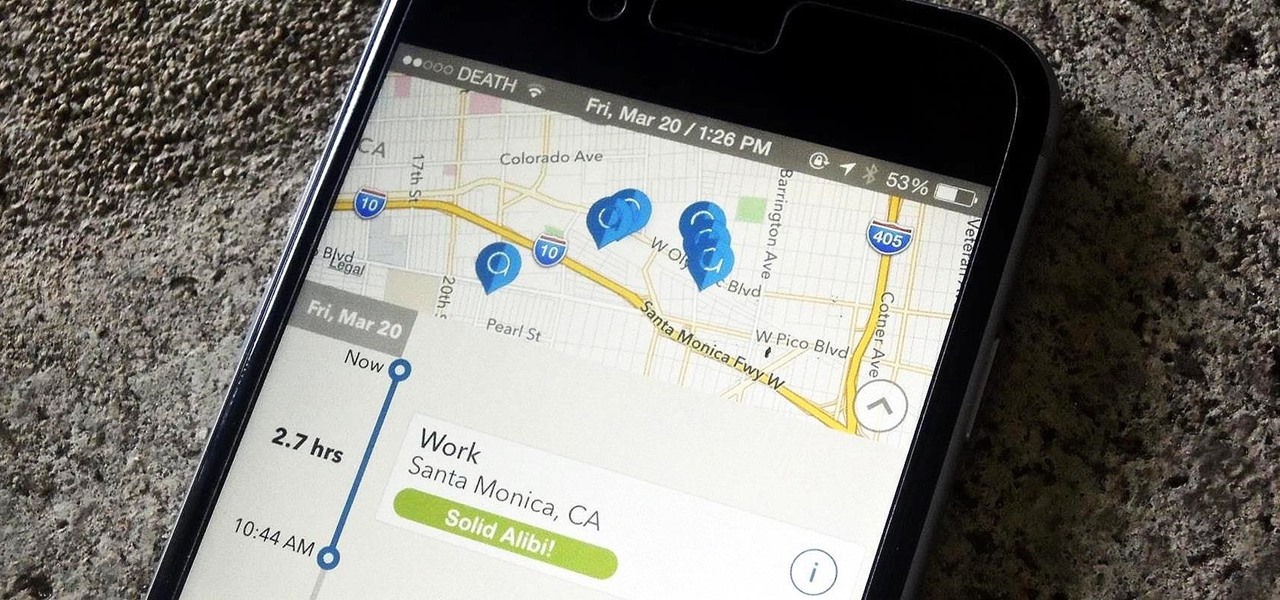
One of the biggest hits this past fall wasn't a movie, television show, or book—it was an unassuming podcast called Serial, which centered around an unsolved murder from 1999 of a high school student in Maryland.

Hate answering the door, but don't trust your friends with a set of keys? This RFID front door lock made by Steve Pomeroy will solve all your party-hosting problems. It reads the RFID tags in his friends' public transit cards and decides who's allowed in based on "groups" that Steve defines. And I have to say, it's also rather stylish. It's controlled by an Arduino serial console and a custom Android app to add and remove cards. The reader can store 50 or 100 tags at a time and allows 7 diffe...

If you want to get started sniffing Wi-Fi networks, you usually need to start with a wireless network adapter. But thanks to a Wi-Fi sniffing library written in Arduino and the ultra-cheap ESP8266 chip, you might not need one. For less than $10 in electronics, you can build a tiny Arduino Wi-Fi sniffer that saves Wireshark-compatible PCAP files and fits anywhere.

A macOS computer can reveal a lot of information about the owner, including which Wi-Fi network they have permission to access. With an Arduino-based attack, we'll use a five-dollar setup to inject a rogue Wi-Fi network and steal the list of trusted Wi-Fi networks, allowing us to see where the computer has been.

Deep down inside, Kindle Fires are actually Android tablets — the only trouble is, Amazon has layered so much of a skin on top of it all that you can't normally use Android's main app store, the Google Play Store. The Amazon Appstore, which comes bundled with Kindle Fire devices, only has about 600,000 apps, so it would be great if you could access Google Play's library, which boasts 2.8 million.

Ditch those namby-pamby clichés like skeleton decals and peeled-grape eyeballs. This year, give your guests a real scare.

Drive.ai (a startup founded by Stanford University graduates), Waymo, General Motors, and serial entrepreneur and author Vivek Wadhwa are featured in today's top news.

Bose Corp is the latest company trying to make another dollar off of you without your permission. Bose Connect, the companion app to the swag $350 Bose headphones, is not the Jane to your Jack that maybe we all hoped it to be.

Augmented reality allows for all kinds of experiences to happen just about anywhere, and that creates some incredible potential for entertainment. While games like Pokémon GO take you out into the world, one crowd-funded game wants to keep you inside—to scare the crap out of you in your own home.

A relay is an electrical component that works like a light switch, where it's turned on or off with an electrical signal. By connecting a relay to a Wi-Fi connected microcontroller like an ESP8266, you can build a connected switch that can be controlled from the web browser of any device connected to the same Wi-Fi network — all for just a couple of dollars.

It's easy to run Kali Linux from a live USB on nearly any available computer, but many publicly accessible laptops and desktops will be locked down to prevent such use. School, work, or library PCs can be secured with a BIOS password, which is often an easily recovered default password. Once you have access, though, you can use a USB flash drive to run Kali live on any PC you find.

We know Android 9.0 will have the formal designation of Pie, following Google's age-old tradition of naming their OS after items you'd normally find on a dessert menu. And thanks to a slew of new features that centers around your overall security, P could also stand for Privacy.

You might want to take apart your Xbox for a variety of reasons. This video will walk you through the process of opening up your controller from unscrewing to the trick of lifting of the cover. You can see the different part where you might need to replace or upgrade things. Step 1: Start out by making sure that the XBox 360 controller is not turned on. The green lights around the XBox button should not be lit. Take off the battery pack located on the back of the XBox 360 controller. Step 2: ...

If you've recently built a Wi-Fi spy camera out of an ESP32-CAM, you can use it for a variety of things. A baby monitor at night, a security camera for catching package thieves, a hidden video streamer to catch someone going somewhere they shouldn't be — you could use it for pretty much anything. Best of all, this inexpensive camera module can perform facial detection and facial recognition!

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.