No, the Kamehameha is not the famous Hawaiian king who united all the islands under his rule from 1795 to 1819. Nope. However, it is named after him. But in this case, Kamehameha is an energy blast attack shown in the Dragon Ball Z series. And with this After Effects tutorial, you're going to learn how to recreate this energy attack.

Jarret Waldman explains why Imi the founder of Krav Maga uses a single handed defense instead two in other systems for gun from the front attack.

What makes you better than your opponent in Jiu Jitsu? The ability to chain attacks, one right after the other.

How to attack from someone's guard (you in the mount position) in Jiu Jitsu using the heel hook technique.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.

An outbreak of anthrax from contaminated meat in Tanzania sickened dozens of people and moves the danger of this deadly bacteria back into focus.

Hi, dear co-apprentices and wise masters. I've been recently trying to learn the basics to hacking here, and I've read all guides on Wi-Fi hacking and noticed no word is dedicated to this awesome script that comes bundled with Kali!

Welcome back my social engineers/hackarians! Today we'll be looking into a fantastic piece of software, The Social-Engineer Toolkit or just SET for short. SET is designed, Developed and used by several Social-engineers. So... Let's get started!

ARP spoofing is an attack against an Ethernet or Wi-Fi network to get between the router and the target user. In an ARP-spoofing attack, messages meant for the target are sent to the attacker instead, allowing the attacker to spy on, deny service to, or man-in-the-middle a target. One of the most popular tools for performing this attack is Ettercap, which comes preinstalled on Kali Linux.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

Welcome back, my fledgling hackers! Over the years, we have examined multiple ways to own, exploit, or compromise a system. On the other hand, we have not spent a lot of time on denial-of-service (DoS) attacks.

In Fallout New Vegas, Obsidian decided to spread and equal amount of unique weapons all across the Mojave wasteland! Ranging from deadly axes, rifles, pistols, submachine guns and more! In this video you'll learn the three ways of acquiring the Cram Opener weapon, a unique version of the Bladed Gauntlet, from Little Buster!

What's better than a paper ninja star, or shuriken? A shiny paper ninja star, of course! Leave those blase plain white paper stars in the recycling bin or toss them to a frenemy.

In this video Reggie Bennett from the Mountain Shepherd Survival School teaches us a lot about finding edible plants in the wild. If you find yourself forced to survive in the woods, picking the wrong berry to eat could be deadly. Bennett goes over common misconceptions about foraging for food, and shows us the right way to do it.

Heart disease is the leading cause of death of men and women in the US. Over half a million Americans die from it annually. Atherosclerosis — a build up of plaque in the arteries — is a common feature of heart disease and can be caused by smoking, fats and cholesterol in the blood, diabetes, and high blood pressure.

While the USB Rubber Ducky is well known by hackers as a tool for quick in-person keystroke injection attacks, one of the original uses for it was automation. In this guide, I'll be going the latter, explaining how we can use it to automate Wi-Fi handshake harvesting on the Raspberry Pi without using a screen or any other input.

Sophisticated hackers have been exploiting vulnerabilities in Chrome and Firefox to trick even the most careful internet users into logging into fake domains for sites like Apple, Google, and Amazon.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

The thunder gun is one of the new deadly weapons in Call of Duty: Black Ops, and this quick little guide from IGN will get you up and gunning. Learn how to use the awesome power of this death stick, to clap some serious hurt down on your enemies.

Finding all of the rare trade objects in Assassin's Creed: Brotherhood can be infuriating, what with random item drops and quests to juggle. Watch this video for a guide to farming trade objects by killing bandits along a particular route.

Your job is to defeat Sapientia in this fight on the Xbox 360 game Bayonetta. In Chapter 13 - The Cardinal Virtue of Prudence, attack the red sphere over Sapientia's head. This fight starts with Bayonetta on the ocean, on a surfboard-like object. Sapientia will use two attacks. The first attack starts with his fin sticking out of the water, like a shark. He will then jump into the air and dive at you. Just keep moving in a straight line to avoid this attack. For the second attack the camera w...

Street Fighter IV : Blanka, the Brazilian Beast unleashes havoc upon the World Warriors once again. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

Street Fighter IV : Vega, the beautiful Spaniard delivers gruesome damage. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

Tired of being attacked by the goblin army in Terraria? Here's a sure-fire, or rather sure-lava, method for defeating them. Watch this video to learn how to design a lava trap that will make the goblin army vulnerable to your attacks.

So you like card games, huh? Don't we all. Well, have you ever heard of Heart Attack? I didn't think so.

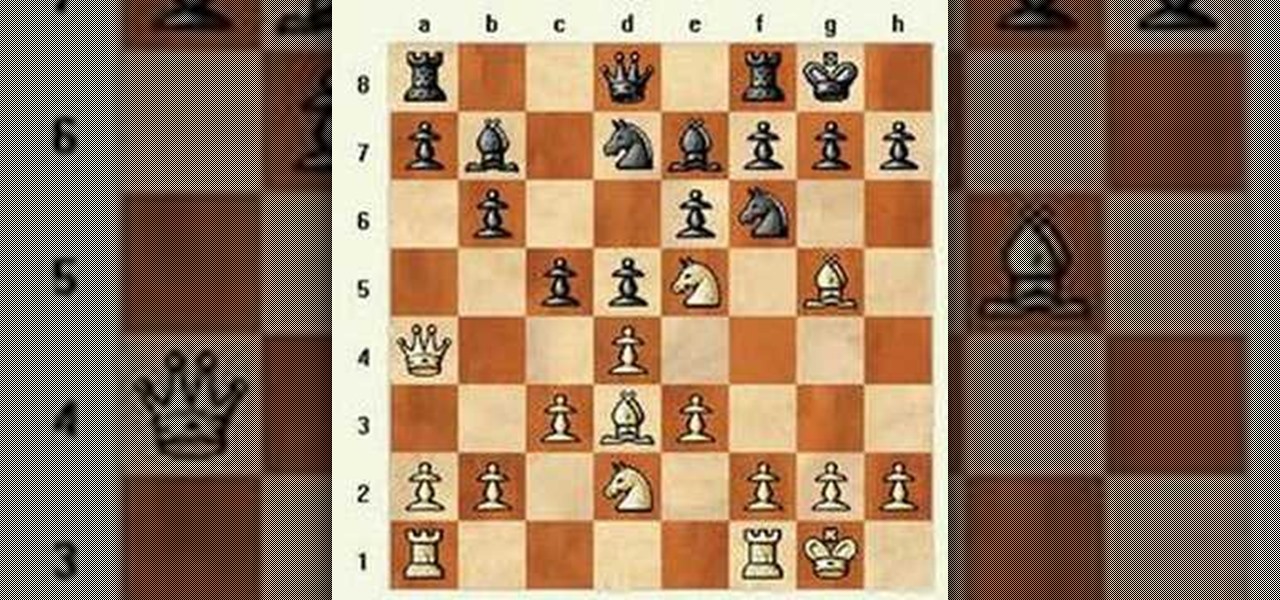
Here is a match with a Reti Opening transposing to a King's Indian Attack. See how to do it, and see why to do it.

This is an introduction to the Veresov Attack 1.d4 Nf6 2.Nc3. It features a game in which Matt crushes a reasonably strong guest who only makes 2 very natural looking errors (...O-O and ...c4). Try it out for yourself.

In this series, Matt will examine the Stonewall Attack for White and display defenses which he thinks are challenging and/or interesting. Here's a prototypical Stonewall game where everything goes right for White.

This video demonstrate a system against the King's Indian Attack. Enjoy! And don't get too good, because if we ever play, I don't want to lose.

This is a trap in the Torre Attack (1.d4 2.Nf3 3.Bg5). It's a favorite in opening traps, so watch and learn. You'll need it someday.

The Spear Master's two greatest abilities are camoflauge and close combat, which can make him a deadly opponent on any battlefield. He is ideal for hit and run tactics, and this video shows you the best way to use Spear Master in your Bloodline Champions game.

Here's how you can fight against a shield wall if you're wielding a spear when playing in a boffer larp (live action roleplay). And after those strategy tips, here is some advice on how you can team up with a shield fighter for a deadly tag team.

Lightning storms are beautiful to watch but deadly to be out in. If you find yourself caught out in a thunderstorm there are several easy guidelines you can use to stay safe, and this video will teach them to you.

When programming in Visual Studio, you may find yourself creating any number of all-but-identical windows. This can be tedious and time consuming. This tutorial discusses the deadly and dangerous task of using a form as a parent for the development of other forms in Visual Studio, using C# in this particular example. For more information on designating a form as a parent, take a look.

West Nile virus is rare but can be deadly. To avoid getting it, you’ve got to avoid mosquito bites.

This video shows you how to prevent from getting the deadly disease and if you already have it, how to treat it.