Build an old static electricity capacitor which will shock the electricity of your TV or computer screen. The full discharge of this Leyden jar can be deadly. Make it smaller if you want to try with your kids.

Use this knot to attach the fly to your tippet when you want a loop that allows the fly to move freely. It gives streamers, nymphs, and popping bugs a deadly action. Don't use the nonslip loop knot on dry flies or on hooks smaller than a #12.

The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

You may have heard of a signal jammer before, which usually refers to a device that blasts out a strong enough radio signal to drown out the reception of nearby devices like cell phones. Purpose-built jammer hardware is outright illegal in many countries. Still, Wi-Fi is vulnerable to several different jamming attacks that can be done with Kali Linux and a wireless network adapter.

While the security behind WEP networks was broken in 2005, modern tools have made cracking them incredibly simple. In densely populated areas, WEP networks can be found in surprising and important places to this day, and they can be cracked in a matter of minutes. We'll show you how a hacker would do so and explain why they should be careful to avoid hacking into a honeypot.

Null Byte users have often requested video content, but the question has always been what format would best serve our community. This week, we partnered with Null Space Labs, a hackerspace in Los Angeles, to test the waters by hosting a series of talks on ethical hacking for students in Pasadena Computer Science Club. We invited students and Null Byte writers to deliver talks on Wi-Fi hacking, MITM attacks, and rogue devices like the USB Rubber Ducky.

What happens if you unknowingly connect a malicious USB drive and it starts infecting your entire office network? Instead of having a panic attack and working all night to find a fix, you can just put on a mixed reality headset like Microsoft's HoloLens and point.

Welcome back, my rookie hackers!

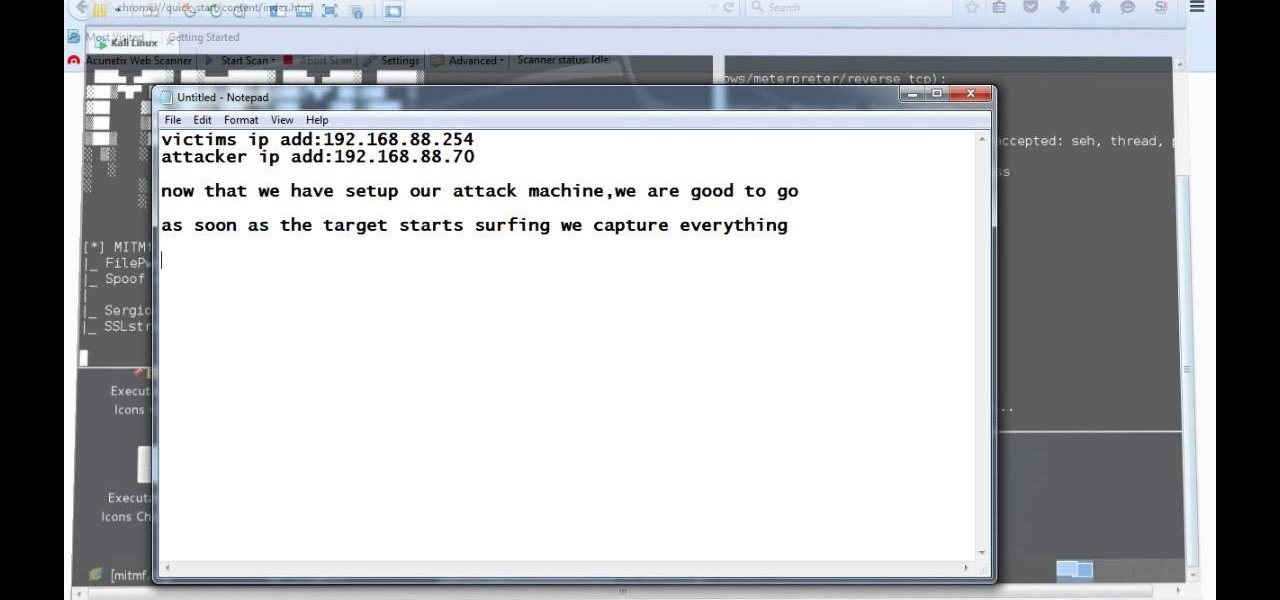
Video: . Hi, this is a quick demo about how to backdoor executables (software) sent over HTTP using MITMF, backdoor factory

Social Engineering was mentioned a few times here on Null Byte, but not very many explained what it is, or how to do it. I love this quote because it's true: Social Engineering is the key to carrying out client side attacks, and all you need is a little creativity!

Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.

Unfortunately, there are plenty of situations where having a can of pepper spray could come in handy. Even worse, in most of those situations your state of mind isn't really conducive to remembering important details like the facial features of the person who's trying to mug you, which means the police will have a harder time catching the culprit.

In this video tutorial, viewers learn how to checkmate an opponent in four moves in Chess. This task is very easy, simple and fast to do. Begin by moving your pawn to E4. Then on your next turn move the bishop to C4 to attack F7. Now move the queen to A5, which also attacks F7. Finish by moving the queen to F7. This is an automatic checkmate because the opponent will lose the king in either way. This video will benefit those viewers who enjoy playing board games such as Chess, and would like ...

The video describes an easy way to survive an attack from someone in the street. When the assailant grabs your, your first reaction should be to guard against their initial blow. Then, punch them in the groin, grab them around there neck in a sleeper hold type move using your arm to wrap around the back of their head and/or neck. Proceed to knee them hard either in the stomach or groin, and then simply push them off of you presumably giving you enough time to run and escape.

This video details how to survive a knife threat from behind. When threatened from behind with a knife, do not attempt to move the body first, this will result in the attacker maintaining the capability to thrust the knife into the body. When threatened, place arms out and low in a submissive position, this is to be followed by moving the left arm backward in a sweeping motion to push aside the arm which is holding the knife. Once the arm is moved, turn the body and bring the elbow up into an...

Trevor4Ever595 teaches you how to hack the game Space Attack using Cheat Engine. You start the game, select a level and pause it using P. Open up Cheat Engine, open the process list, select Firefox or whatever internet browser you are using. Then you will want to use the search box to search for the amount of money you have in the game. A lot of values will come up to the left of the search box. Go back to the game, earn more money and then search for that new amount. Cheat Engine will only r...

Machinima.com holds your hand through the 5th and final Prince of Persia Walkthru.

Street Fighter IV: Ryu, An old favorite returns, stronger than ever. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

Street Fighter IV: Quick, cunning, and flashy, Ken Masters brings his A game to the latest Street Fighter.

Street Fighter IV : Rufus may be portly, but his size obviously doesn't slow him down. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

Minecraft 1.8 has introduced Enderman to tons of blocky servers all over the world. If you're looking for ways to fight against Enderman or just avoid Enderman all together, take a look at this walkthrough on how to do both. Be sure to grab an Ender Pearl so that you can half their attack range!

Wolverine in the most well-known X-Man and arguably the most famous face in Marvel comics. Of course he kicks ass in Marvel vs. Capcom 3! This video will teach you the basics of fighting with Wolverine, including his basic attacks, special moves, and some combos.

Okami was one of the best games of the last decade, perhaps Capcom's finest, and it's heroine Amaterasu makes a much-deserved appearance in Marvel vs. Capcom 3. She isn't quite as powerful as you'd expect the God of Everything to be, but she kicks serious butt and this video will teach you the basics of fighting with her, including tips on all her normal attacks and special moves.

Marvel vs. Capcom has been the flagship series for frenetic 2D fighting games for years, and Marvel vs. Capcom 3 hit store shelves in February. This video tutorial will teach you the basics of the game, including basic combos, hyper combos, team combos, special attacks, and more. Everything you need to start off your MvC3 career right.

Beyblade is a fun game from Japan that is very similar to Spinjas but much more complex. If you're new to the game or just ant some expert advice watch this video to learn about the four mains types of Beyblade (attack, defense, stamina, balance) and how they can each be used to play better Beyblade.

The SAW lead is the most recognizable sound in hardstyle and hardcore electronic music, sounding like a swarm of bees attacking with the precision of an honor guard. Watch this video to learn how to program a patch for a SAW (or sawtooth) lead on a MicroKorg.

Having a successful rushing attack is the key to good offense both in real football and virtual. If you play Madden NFL 11 and are having trouble running the ball, this video will give you all sorts of great tips and tricks to help you out getting your offense moving and scoring touchdowns.

If you recently purchased Castlevania: Harmony of Despair on your Xbox 360, this next tutorial will help save your life. In this strategy how to tutorial, you'll find out how to defeat the game's most difficult enemies, the stage bosses. Each one has unique powers and attacks, but they also have some different weaknesses as well. They're easy to follow and should be easy to follow. Good luck and enjoy!

Life on the frontier was hard, and it still is in the Zynga Facebook game FrontierVille. If your homestead has been attacked by foxes or wolves, this video will teach you how to beat them, clobbering their little furry butts clear of your homestead for good!

In this excellent informative yet entertaining video Sara from petside.com invites you to join here in the war to end flea and tick infestation. You'll learn why they love to attack your pet and how exactly to combat these pesky little parasite. So gear up for battle and make sure you end up on top and not defeated by these annoying little blood suckers.

Getting back to nature can be an incredibly rewarding experience – unless critters come along and ruin it! Here's how to keep your food from being plundered. To keep your food protected while camping out in the great outdoors, try bringing along a cooler, a cloth or nylon sack, a sock, some rope, and sealable, waterproof plastic bags. Keeping your provisions safe will decrease the risk of animal attack, and make your journey out into nature a fun experience.

Learn the proper method of striking a flint, how to hold the flint, and the angle of attack. Use a slow, downward scrape--make a spark even on a dull edge!

Here are 2 pins for arresting techniques in jiu itsu. One attacks the elbow the other the shoulder.

AntiPolygraph.org's George Maschke speaks with Nick Frost about how to fool a polygraph (lie detector) test in episode 5 of the tongue-in-cheek 2003 television series Danger: Incoming Attack. Note that the anal sphincter contraction, discussed as a polygraph countermeasure, while effective, is no longer recommended by AntiPolygraph.org, and alternative techniques such as mental countermeasures or tongue-biting are to be preferred.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.

While not cuddly to most, bats are shy, skilled flyers that fill an important role in their environments. A new study reveals a deadly disease decimating North American bat populations has stepped up its attack on vulnerable bat populations in the summer months.

Last week, the U.S. Justice Department issued criminal indictments against seven Iranian hackers. These hackers, working for private companies in Iran, are accused of orchestrating DDoS attacks against U.S. financial institutions from 2011-2013 as well as intruding into the control panel of a small dam in Rye, New York. It is thought that these attacks were a response to the U.S. tightening financial restrictions on Iran during those years and the NSA-based Stuxnet attack on their uranium enr...

While password cracking and WPS setup PIN attacks get a lot of attention, social engineering attacks are by far the fastest way of obtaining a Wi-Fi password. One of the most potent Wi-Fi social engineering attacks is Wifiphisher, a tool that blocks the internet until desperate users enter the Wi-Fi password to enable a fake router firmware update.

Welcome back, my budding hackers! As I have mentioned many times throughout this series, knowing a bit of digital forensics might keep you out of a lot of trouble. In addition, digital forensics is a burgeoning and high paying career. Some knowledge and certifications in this field will likely help you land a Security Engineer position or put you on the Incident Response Team at your employer.

Welcome back, my budding hackers! With this article, I am initiating a new series that so many of you have been asking for: Hacking Web Applications.