
How To: DDos a Website Like a Pro (Windows Only)
Welcome to this short and easy tutorial on hacking and DDosing (is that even a word I don't know) anyways lets get started


Welcome to this short and easy tutorial on hacking and DDosing (is that even a word I don't know) anyways lets get started

In this tutorial, we learn how to understand rheumatoid arthritis. This concentrates by attacking the joint spaces and causing a reaction. This doesn't happen for an exact reason, but it usually occurs in older individuals between 40-60 years old. This also occurs in young children rarely. The symptoms are when the joints become inflamed and painful. This happens around the knees, ankles, neck, and more. This attacks both sides of the body and the same body parts at once. Fatigue, fevers, mor...
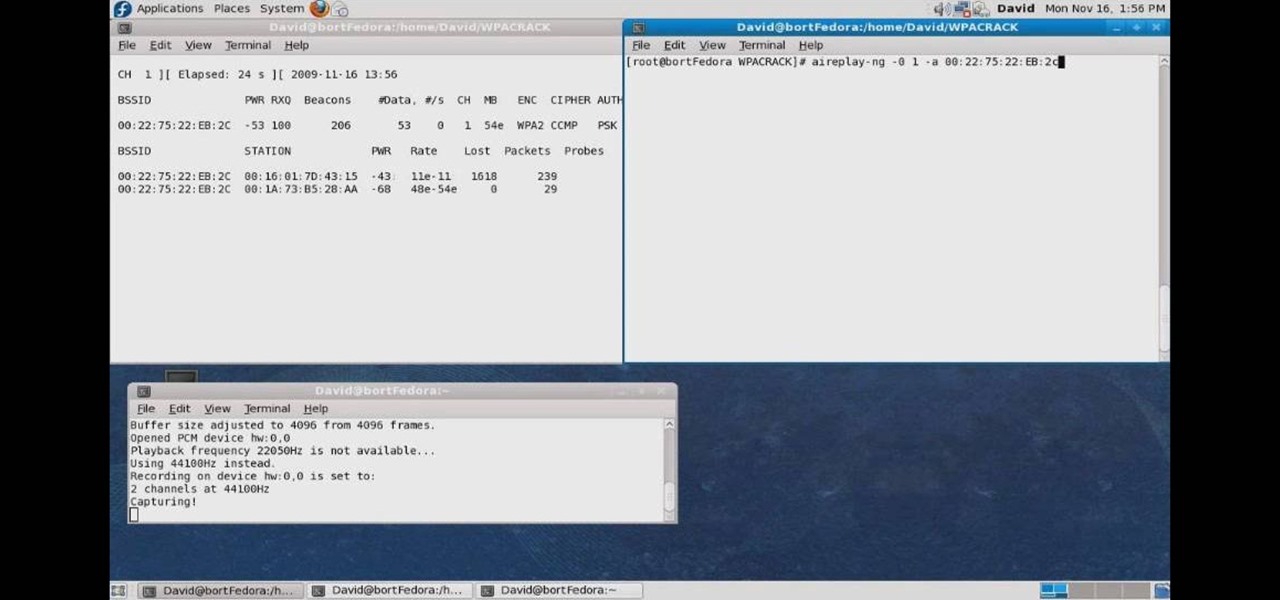
In this how to video, you will learn how to crack a WPA encrypted wireless network. To do this, you will need the Air Crack package for Linux. First, disable the wireless adapter and enable monitor mode. Next, identify the channel in the wireless network and Mac address. Once you have this, you can listen to the traffic coming to and from this point. Wait for the handshake or disconnect something in order to force it to reconnect. From here, you are ready to perform the attack. With any encry...

Learn how to maintain your heart health at any age! Great advice for all women because the younger you are the better chance you have at protecting your heart and preventing heart disease. Starting at age 30 you should start getting cholesterol test just to keep yourself in check. Once you hit 40 you should start scheduling stress echo cardiograms which can indicate if there are problems with your heart. Once you reach 50 you really need to be aware of the signs and symptoms of a heart attack...

This how-to video explains the names behind the rubber guard (why they are called what they are) and a step by step method behind the basic rubber guard set up. There are many variations and attack positions, but this video covers the basics: mission control, zombie, New York, chill dog, and kung fu move into jiu claw. There are more advanced attacks and sweeps from anyone of those positions like: invisible collar, asylum, straight jacket, double bagger, reaper, gogoplata, locoplata, Croc, sw...

Are you serious about becoming a bonafide hacker? Then you simply must learn how to hack SSL passwords using ARP poisoning. ARP poisoning, also known as ARP spoofing, involves attacking an ethernet wireless network by looking at the data frames on a LAN (local area network). Resultingly, you can sniff plaintext passwords, SSL passwords, and even manufacture denial-of-service attacks.
'Wayward Son' is a main story quest about halfway through Act 1 of Dragon Age 2, in which you are called upon to, big surprise, help a mother and son in need. This video series will give you a walkthrough of the entire quest, allowing you to complete it yourself and also making a compelling viewing experience in it's own right.
In order to play the game Risk, begin by setting up. Name a banker. Players choose a color. The number of players determines the number of armies. Remove the jokers from the country card packs. Shuffle the cards. Deal them face down. Players may not get an equal number.

This is a tutorial for controlling the Pine tip moth. Identifying and controlling the pine tip moth consists of studying the small plants of pine. The attacks on pine trees is caused by Nantucket pine tree moth found along the Rio Grande Valley as far north as Espanola, it has spread to South Arizona and California by importing grafts from Mexico. The moths are 3/8 inch long reddish brown to grey in color. They attack the main stem of the baby plant and the pines instead of growing vertical g...

As a Boy Scout, when the First Class rank is attained, a scout has learned all the basic camping and outdoors skills of a scout. He can fend for himself in the wild, lead others on a hike or campout, set up a camp site, plan and properly prepare meals, and provide first aid for most situations he may encounter. A First Class scout is prepared.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

Last week, NowSecure security researchers revealed that nearly 600m Samsung mobile devices are vulnerable to a type of MitM attack.

Are you ready for the last boss fight in the Xbox 360 game Darksiders? Once you fight Abaddon in the Destroyer, you win, unless you lose. You'll now have to face Abaddon in his "normal" form. He is a powerful swordsman so you'll want to take the defensive route as he can block most of your basic attacks. Instead of attacking him, be patient and stand near him. You'll need to perform a Block Counter but simple tapping the Dash button (without hitting the directional stick) the moment before Ab...

Get ready for the boss fight of your lifetime in the Xbox 360 game Darksiders. In the boss fight in Twilight Cathedral, spar against Tiamat. When you reach the bat queen Tiamat she will take offf into the air immediately. Quickly dash to the Inert Bomb Growth around the edge of the arena closest to the flying and then throw it at Tiamat. Now you need to use your Crossblade and target a flaming urn then the bomb you stuck onto Tiamat to light the bomb on fire. Once you detonate the bomb on her...
Battle Temperantia is this episode of the Xbox 360 game Bayonetta. In Chapter 7 - The Cardinal Virtue of Temperance, prepare for a fight. This chapter consists of a boss fight. You'll start on a platform. Temperantia will punch the platform with his fists and they will stick in the platform. Attack the lighted area of his wrist. While you are attacking he will shoot at you with his other hand. He slowing sweeps his guns, so you can attack until his bullets get close to you, then jump as his l...

There's 14 verses in this chapter in the Xbox 360 game Bayonetta. In Chapter 5 - The Lost Holy Grounds, combat Grace and Glory, Durga, and Alfheim. Near where you start you'll find the book "Crescent and Sunrise Valleys." Walk along the path and it will crumble as you go.

Defeat the Templars in Mission 8 on the Sony PSP and stop the attacks on the safe house. Altair doesn't really catch a break, although the Safe House assault squad comprises only six Templars. Slay them all. For more info, watch the whole gameplay.

Aproaching a cute girl in any sort of setting is intimidating. If she's with her friends, then you're probably nervous about making a good impression in front of all of them and probably freaked about how they'll judge you as a potential suitor, and if she's alone it's a deadly one-on-one confrontation.

Has your Lego arsenal grown stagnant relying on the supply of weapons offered it by the Lego corporation? Take matters into your own hands. This video features detailed instructions for building a sniper rifle out of Lego blocks that one of your Lego minifigures can hold. This will make this piece a deadly force on the Lego battlefield.

Give people some deadly goosebumps! Also tells you how! Learn how to prank your friends with a secret envelope. All you need is copper wire, a button, an envelope, a card and elastic. This prank is sure to scare your friends.

Are you a fly fishing enthusiast? Check out this instructional video and learn how to tie the "Rubber Leg Stonefly", TPO's fly of the month for June 2008. A favorite "anchor fly", this one is deadly out west but you will be surprised with your success at home as well.

You may have come across Chloe Bruce in the past, but we're betting it was on the web, because if it were in person, you probably wouldn't be reading this right now. Because in a blink of an eye, she'd have her foot smashed against your face using her world famous Scorpion Kick, a difficult move for any martial artist to perform.

Awww look, the piggies made a little train to pull other little piggies along. If only it would actually move, they might survive your attack. This video will show you how to beat level 3-6 of Angry Birds with three stars and stop the pigs dead in their tracks. Which they can't really make since they don't have feet... NEVER MIND!

This tutorial starts off by demonstrating the proper way to hold a boffer sword for greatest control. Once you've gotten that down, you're shown how you can go up against an opponent with a shield and still win, even if you only have a sword.

A shield isn't just for defensive maneuvers - you can also use a shield in several different ways to augment your weapon attacks. This tutorial shows you how you can use a shield effecitvely in boffer combat or at a fighter practice.

Combat is a fundamental part of many boffer larps, and you'll need to know how to fight well in order to have a successful PC for most games. This tutorial starts with the very basics of weapon grip, and shows you other important boffer combat techniques, like footwork and how to attack without leaving yourself open for a counterattack.

Heading to a potlock tomorrow but can't swallow the idea of slaving over the stove for hours in the kitchen making the perfect French onion soup and olive oil drizzled baguettes? Save yourself a panic attack as well as time by baking this apple crumble.

If you're playing as the Terran in StarCraft 2, then you need to know how to master the Thors, which are large and powerful Terran mechanical units (mech units) which are great for defense and late-game attack units. Watch and learn to see the best way to use your Thor army. They're especially good in StarCraft II: Wings of Liberty for sieging large groups of ground infantry units.
One achievement for you to earn in Starcraft 2: Wings of Liberty is the "My Precious" achievement, and you can get this in the Colonist mission of Save Haven. In order to obtain the achievement, you must successfully rescue two Colonist bases from the Protoss attack on HARD difficulty, i.e., destroy the Purifier while at least 2 Colony bases are left un-purified!
Breast cancer is one of the most deadly and tragic diseases afflicting women today. If you are interested in spreading breast cancer awareness and also in 3D modeling, then this video is a must-watch. It will teach you how to create a 3D model of the pink ribbon synonymous with breast cancer awareness, which you can then use on your website or in any other digital locale you wish.

Is your kitchen out of control cluttered? Do you have paper work, utensils, and junk mail scattered in the one room in your house that should act as your sustenance sanctuary? In this episode of Real Women Scrap, the hub of every household is attacked as well as other ways to unclutter your kitchen.

In this video, you'll see how and why wax can be a deadly. This is how it works,When the test tube is submerged in cold water, the glass forms tiny cracks. The Water enters gets into the tube and vaporizes causing a micro explosion. The hot wax is then ejected from the tube quickly as oxygen is displaced from the tube itself. Be careful, and make sure to be as safe as possible when trying this experiment at home.

L.A. Lakers superstar Kobe Bryant shares some tips with TIME Magazine's Sean Gregory on how he puts his best foot forward everytime he steps onto the court. Areas gone over in this video include: The proper grip & shooting form, attack the foot & sell the fake, the pull-up jumpshot, the art of the foul shot, playing to the opponent's weaknesses, getting in character, and stretching.
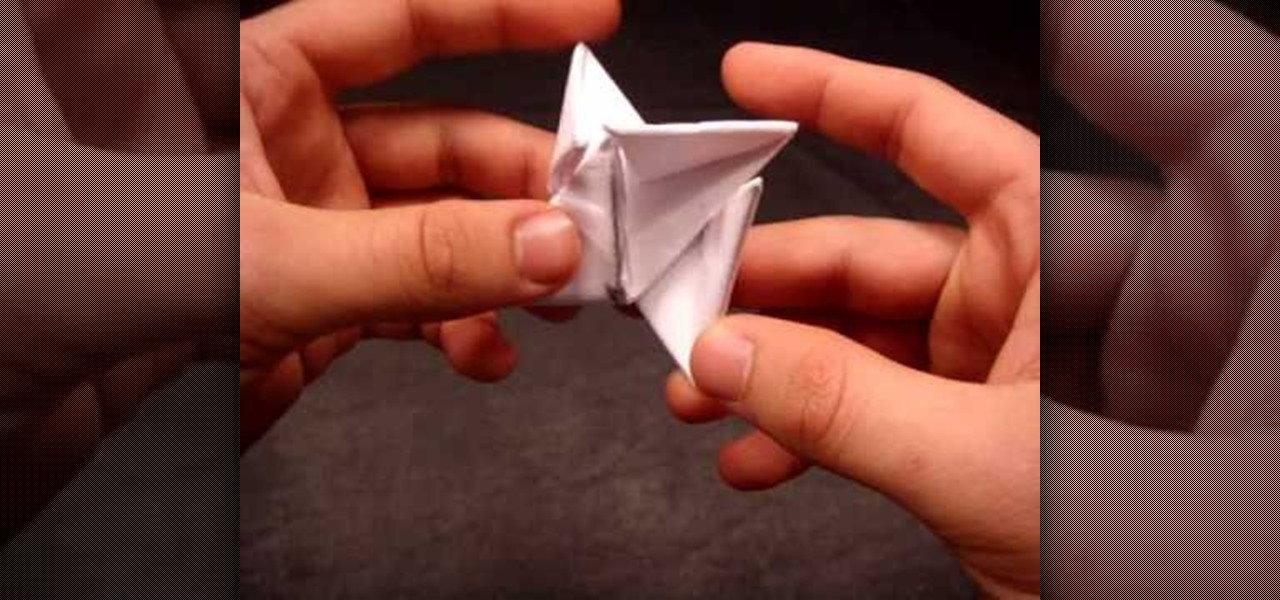
Shuriken are the ancient Japanese weapons you've seen ninja warriors use in the movies. Their name literally translates as "sword hidden in the hand". In this tutorial you'll learn how to make a shuriken out of paper in a few fairly simple steps. But while this throwing star isn't as deadly as a metal version, it has sharp edges and it is potentially dangerous. Be very careful about where you throw it, and never throw it at people or animals!

Are you using the Queen too much, or attacking with one piece at a time, or making mostly pawn moves, or that tricky Knight obsession, or "freeing" the Rook with a side pawn, or are you being a victim of a back row checkmate? Well, watch this video to to avoid these common chess mistakes.

This how-to video demonstrates Krav Maga Worldwide Sherman Oaks 3rd degree Dave Bluestein teaching defense against a basic choke from the front with a push. Follow along and improve your Krava Maga skills or just learn how to defend yourself from an attack. Watch this video martial arts tutorial and learn how to execute the Krav Maga choke with a push defense.

There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture handshakes from both attended and unattended Wi-Fi networks, we'll use two of Bettercap's modules to help us search for weak Wi-Fi passwords.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

The most common Wi-Fi jamming attacks leverage deauthentication and disassociation packets to attack networks. This allows a low-cost ESP8266-based device programmed in Arduino to detect and classify Wi-Fi denial-of-service attacks by lighting a different color LED for each type of packet. The pattern of these colors can also allow us to fingerprint the tool being used to attack the network.