Worried about a zombie apocalypse? Of course you are, we all are! This tongue in cheek video divulges the steps you'll need to take should zombies begin roaming the earth. Using clips from horror movies, this video shows you the right way to hide from zombies and even explains who you can trust. Learn what weapons work on zombies and how to cripple them and most importantly, destroy their brain! Nobody wants to get bitten by a zombie, learn how to escape, travel and even how to recognize if o...
It's nearly impossible not to be at least somewhat familiar with Microsoft Excel. While it's needed for many office jobs and data analysis fields, hackers could also benefit from improving their spreadsheet skills. Many white hats already know some of the essential Excel hacks, such as cracking password-protected spreadsheets, but there's so much more to know from an attack standpoint.

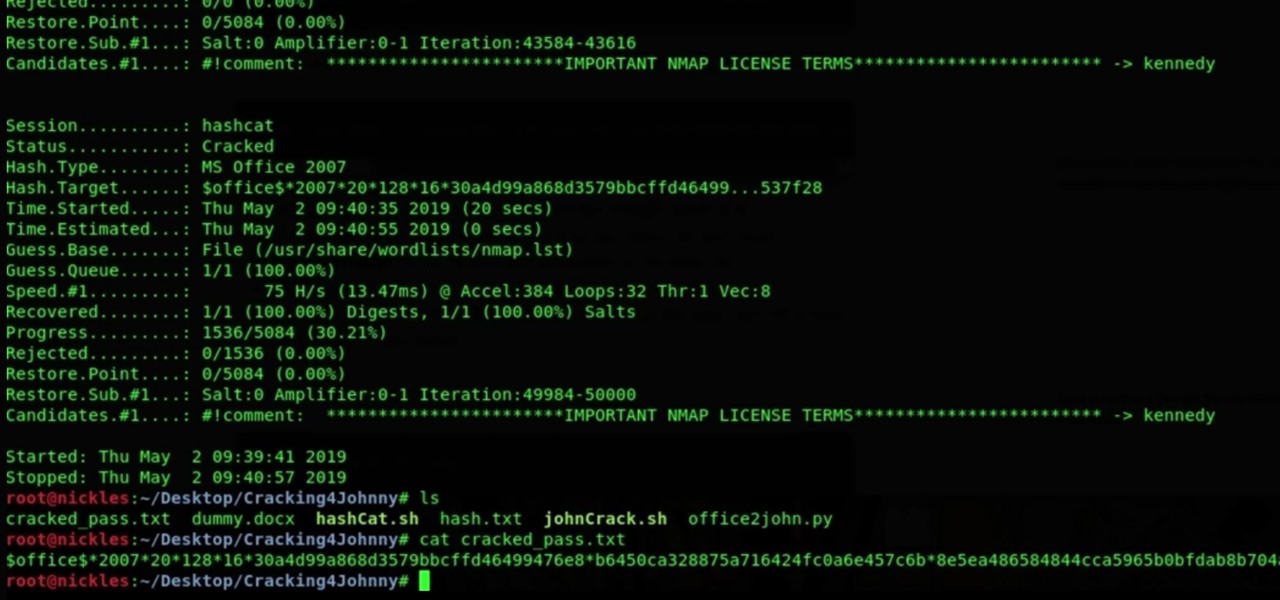
A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

Due to weaknesses in the way Wi-Fi works, it's extremely easy to disrupt most Wi-Fi networks using tools that forge deauthentication packets. The ease with which these common tools can jam networks is only matched by how simple they are to detect for anyone listening for them. We'll use Wireshark to discover a Wi-Fi attack in progress and determine which tool the attacker is using.

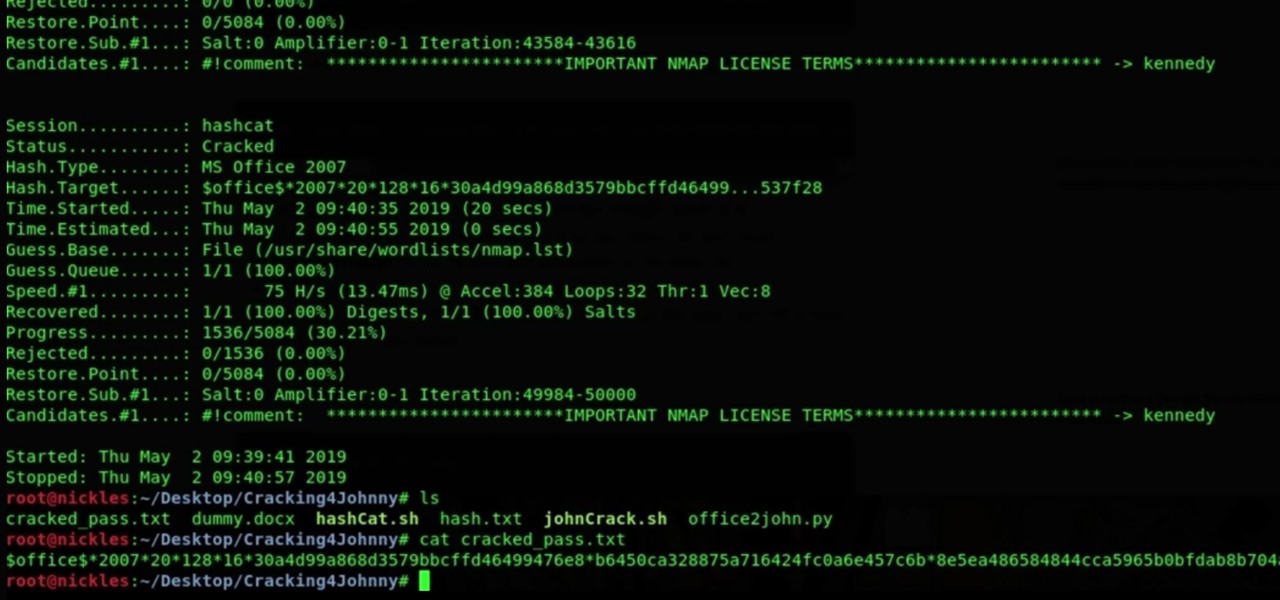
Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

Barrow's article on Pupy made me wish for a RAT that could target an OS frequently used by gatekeepers at startups, tech companies, and creative firms: macOS. Once run, a RAT can do severe damage by dumping a user's stored credentials for many accounts. The best loot lives in the Chrome Password cache, and EvilOSX, an OS X RAT, infiltrates macOS and dumps these credentials.

A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwarding legitimate traffic to and from the unsuspecting target.

Maybe you thought sitting behind a Mac gives you special protection when it comes to getting hacked. Thanks to a a new report from Check Point, you can kiss that theory goodbye. The cyber security company just uncovered the latest strain of malware — OSX/Dok — infecting all versions of macOS (previously Mac OS X).

Welcome back, my tenderfoot hackers! Web apps are often the best vector to an organization's server/database, an entry point to their entire internal network. By definition, the web app is designed to take an input from the user and send that input back to the server or database. In this way, the attacker can send their malicious input back to the servers and network if the web app is not properly secured.

infosecinstitute posted a handy article about what to expect in the new year for cyber security, along with highlighting major game changers from 2015; 2016 Cyber Security Predictions: From Extortion to Nation-state Attacks - InfoSec Resources.

Hi , Today i will show you how to do HID Keyboard Attacks With Android BUT without using Kali NetHunter BUT You will need to install custom kernel to your Android device, that will add keyboard+mouse functions to it's USB port,So Lets Get Started

If you've been watching the latest USA TV Series Mr Robot, you will have seen the Raspberry Pi used by Fsoeciety to control the HVAC system. OTW covers this very well here with his take on setup they may of used.

Hello, ladies and gents! Today I will be discussing the fun and excitement of backdoor on an OSX system.

With each day that dawns, there is a new, major hack that makes the news headlines. If you are paying attention, there are usually numerous hacks each day and far more that never make the news or are kept private by the victims. Every so often, a hack is so important that I feel compelled to comment on it here to help us learn something about the nature of hacking and IT security. This is one of those cases. Last week, the U.S. Office of Personnel Management (OPM) revealed that they had been ...

Hi everyone! In the previous part of this series we introduced remote code arbitrary execution via buffer overflows using all of our past experiences.

Yesterday, April 7th, it was revealed that the United States White House had been hacked by allegedly Russian hackers. According to reports, the Russian hackers used social engineering/phishing to get a foothold in the U.S. State Department and then pivoted from that system/network to the White House. Although the White House said no confidential information was compromised, the President's appointment calendar and other information were. Attribution or "blame" for the hack was made more diff...

Hello, hackers and engineers! Today we are going to dive a tiny bit deeper into the secrets of psychology, and how we can use them with hacking and social engineering attacks.

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).

Yesterday, we pointed out that hackers could remote-wipe certain Android-based Samsung smartphones like the Galaxy S III using a USSD exploit. All they have to do is hide a small code into any webpage or text—even barcodes—then once you click on it, the phone resets to factory settings in a matter of seconds. The video below shows just how easy it is.

Some of us use our smartphones for almost everything. Manufacturers know this, so they try to make their devices as convenient as possible to use, but sometimes that convenience comes with a cost to security. The very same technology that allows you to easily share music with friends and make purchases can also put you at risk. Photo by sam_churchill

If you like to carry your team by doing a ton of damage, and you like the idea of flying around in a flying machine, try out Corki, the Daring Bombadier in League of Legends. In this champion spotlight, Phreak from Riot Games builds Corki with a Trinity Force to do a ton of damage and attack quick. He also overviews what abilties, masteries, and runes to get on Corki.

If you play Elder Dragon Highlander, the awesome Magic: The Gathering variant, check out this video for a guide to building a cat-based deck that will ravage people. Cat attack! If you haven't played EDH, check out the link above and come back.

A bug out bag, or BOB, is a prepared bag, usually a backpack, designed to sustain you for up to 72 hours while your escape wherever you are in case of a natural disaster, terrorist attack, or other catastrophe. This video will teach you everything you need to know to prepare an effective BOB that will help ensure your survival.

In this tutorial, we learn how to apply a neck ring and plug on a reborn baby doll. First, attack the neck ring to the doll head by pulling the vinyl onto the lip using your fingers. You will need to use your hands to push the inside of the neck through the ring. This will take a lot of pushing and pulling. After this, you will need to attach your plug. First, place it into the neck of the head to make sure it fits. After this, stuff it with cotton and then push it back in. Now you will be ab...

In this video, you'll learn about the basics of using your military to defend your fortress, in this case against a dinosaur attack, in Dwarf Fortress.

Do you remember making the paper hat boats when you were a kid? Want to feel like a kid again? Or just looking for something to do with those old 2 liter bottles? Make a bottle boat! And heck, why not throw on a radio control feature while you're at it! Your childhood wasn't this cool! This video will show you all of the steps that you need to take to get your deadly vessel together and how to assemble the radio control feature as well!

If you want to have a character get attacked by a predatory land animal in your movie, you are probably going to need to put some claw marks on their body to make it look realistic and visceral. This three-part video will show you how to create a really realistic open claw mark wound on an actor's face, or any other body part. It looks really, really good, now try it yourself and scare your family and friends!

Football is a dangerous sport, but playing smart and safe is the key to making sure you're not being hauled of the football field on a stretcher or in a neck brace. It's not one-hundred percent preventable, but how do you minimize the risk of potential deadly injuries to young football players? This video will show coaches a few drills to teach their young athletes to minimize catastrophic neck injuries. And the key is staying low at the line.

Dr. Lin Morel discusses stress in an easy to follow format in this short OneMinuteU presentation from 2008. Her first suggestion is to breathe deeply. She follows that up with paying attention to your body and taking care of it. Then she discusses enlisting friends for support with the stress. Her second to last suggestion is to take time to be still and rest. Her final idea is to create a plan of attack for dealing with stress so that you are prepared when it comes up. These easy steps are g...

The powerhouse of space exploration, NASA (National Aeronautics and Space Administration), sheds light on Newton's laws of motion as pertaining to drag force on aircrafts. This is a great source for any aeronautics major. The infamous government agency breaks drag down for you.

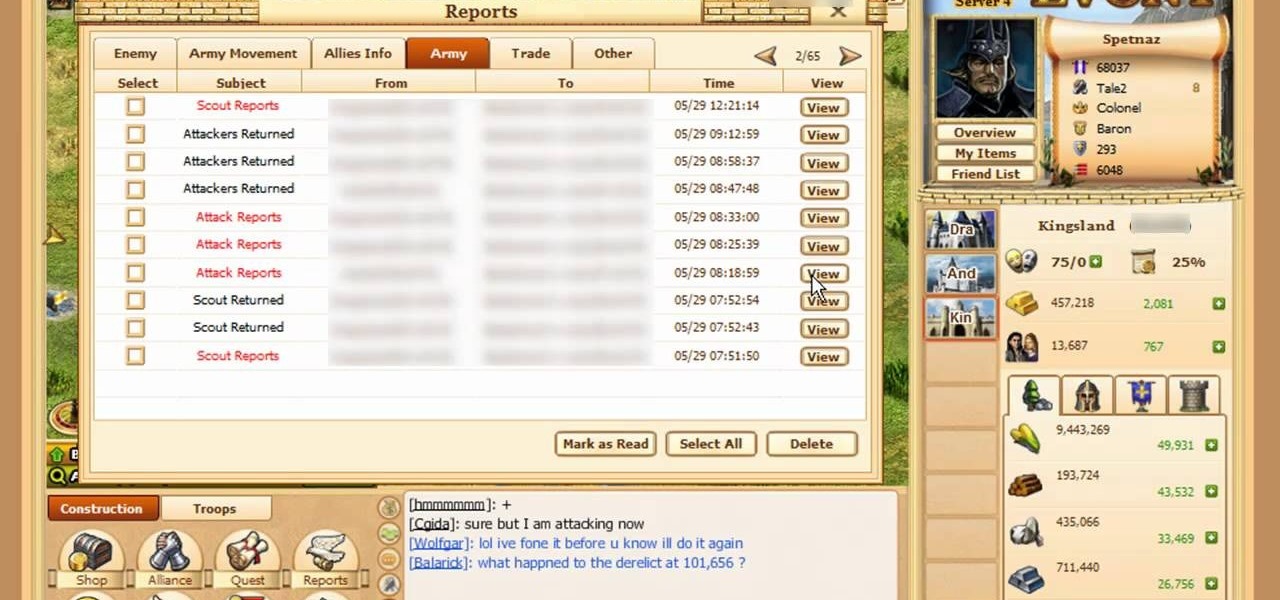
Learn everything you could possibly want to know about the internet, multiplayer game Evony with tutorials from EvonyTutorials. Watch this video tutorial to learn how to play Evony - promotions and medals. See exactly what the game Evony is!

Learn everything you could possibly want to know about the internet, multiplayer game Evony with tutorials from EvonyTutorials. Watch this video tutorial to learn how to play Evony - Ballistas vs NPC. See exactly what the game Evony is!

Lightning is quite simply sublime. Beautiful yet terrifying all at once, it is one of nature's great mysteries (we still don't fully know why it happens) and can be deadly if you get in its path.

The Knights of Gray are back, and they're are here to teach you some boffer sword fighting drills to practice with for your upcoming LARP events.

Face, meet table. Another great practical joke video by PrankVote where they attack Ernie in his sleep. Find your sleeping friend, place a small table over his sleeping face and blow an air horn in his ear. Be assured this will result in a very angry and delusional roommate. However this is a great way to pull a face smash practical joke on any sleeping roomate. Use this as inspiration for one of your April Fools Day pranks!

An opening strategy used by Black to have a strong attack against White queen/pawn openings. The Benoni Defence and variations have been used by the likes of Bobby Fischer and Kasparov, to name a few. Learn it!

The Danish Gambit opening allows for rapid attack development for White. This video explores the book line moves, along with possible counter-play by black.

Matt covers some lines with a black ...Bg4. He found the first game with analysis on the Kenilworth Chess Club site. Most of the analysis he gave for this game is taken verbatim, but he does mention a couple side variations that you should be curious about. So watch!

We look this time at 1.d4 d5 2.e3 e6 3.Bd3 Nc6, a move order I am calling the Teichmann Defense, after the player who first used it. It seems like a little-explored and reasonable approach against the Stonewall. So pay attention.

This is a discussion of a tricky line against the Stonewall, the Horowitz Defense (2...Nf6 3.Bd3 Nc6). White allows Black to spend three moves capturing the light squared Bishop and bringing White's pawn from c2 to d3, preventing a ...Ne4 invasion. This makes for very dynamic play.