How To: VIM, as Ugly as It Is Fast
Hello there Nullbyte users! This will be my first article here.

Hello there Nullbyte users! This will be my first article here.

What's up, peeps? In this quick tutorial, we will be looking at structs, a special kind of data type.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Hello Everyone! I wanted to share a free and open source note taking tool that I've been using for quite some time now.

In Minecraft 1.9 New Command Blocks can be used to make elevators. You types different commands to achieve controlling the elevator for movement you like. This tutorial tells in Minecraft 1.9 how to use command blocks to make elevator. Lets just have a look at it!

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them

Ruby is a dynamic, general-purpose programming language created by Yukihiro "Matz" Matsumoto in Japan around the mid-90's. It has many uses but with it's flexibility, it makes a great language to write exploits in. In fact, the entire Metasploit Framework is written in Ruby! The sole purpose of this series is to teach hackers the basics of Ruby, along with some more advanced concepts that are important in hacking.

From laptops to tablets, technology is taking over classrooms. Elementary schools offer kids tablets, and college students are bringing laptops into lecture halls, leaving their notebooks behind. Today, many students prefer putting their fingers to a keyboard rather than pen to paper, but are these helpful devices truly beneficial?

What Is IPython? IPython is a richly featured replacement for the standard python interpreter. It offers a wider range of functionality, that the standard

If you're one of those people that would rather make a Valentine's Day gifts than buy them, then this fun little project is right for you. Impress your special someone with this homemade bear. All you really need is a large lemon or orange. There's not much instructions to make this project because the results will vary, but use the example in the image to guide you, and watch the video below.

When it comes to passwords, the longer and more complex they are, the better the security. Even professional hackers say so. But if you've ever tried to type in such a password, you've surely noticed that it can be a bit of a pain. Mistype one character, and you're probably going to have to clear the field and start all over again.

This is the best how-to's website that I've ever seen, and I wanted to join it. It taught me a lot, but, because I'm here to learn too, please correct me if I'm wrong.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.
Android has had predictive text for a while now, both with stock and third-party keyboards such as Fleksy, SwiftKey, TouchPal, et al. Apple is even getting on board, with stock predictive text and third-party keyboards for iOS 8, slated for public release later this year.

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

How to make a Lego key holder with note board. Tired of loosing your keys? Well keep them safe and in one place with this fun Lego key holder.

How to make 3 different Christmas trees. Brighten up your home this Christmas with a beautiful homemade Christmas tree or three!

Holidays can be challenging, especially around Christmastime—but not if you invoke your inner MacGyver spirit. In my latest "life hacks" guide, I show you 10 amazing tips and tricks that'll hopefully make your holiday season a little more merry.
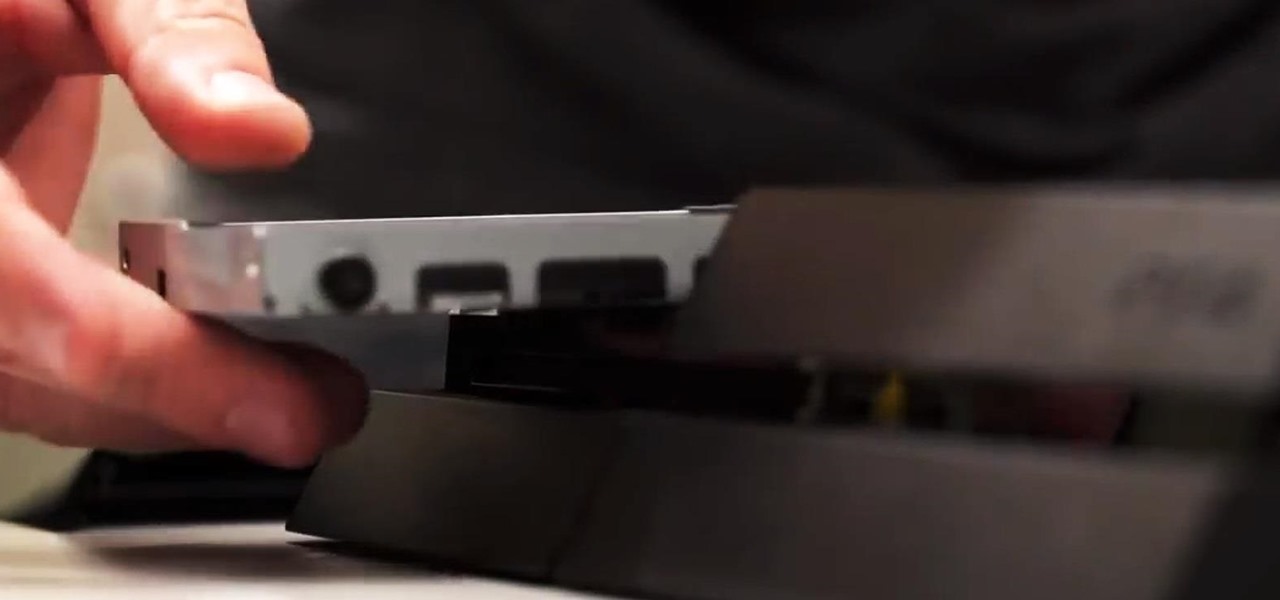
Bigger and faster. Two words that are pretty much always wanted no matter what the scenario is. The new PlayStation 4 has been out for only a few hours now and people are already looking for ways to one-up their friends and upgrade their already awesome systems.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

Welcome back, my greenhorn hackers! Congratulations on your successful hack that saved the world from nuclear annihilation from our little, bellicose, Twinkie-eating dictator. The rest of world may not know what you did, but I do. Good job! Now that we hacked into the malevolent dictator's computer and temporarily disabled his nuclear launch capability, we have to think about covering our tracks so that he and his minions can't track our good works back to us.

Step 1: Making a Pear Leek & Curry Soup Is Easy and Perfect for Spring. Step 2: 1 Tablespoon of Butter

Video: . Step 1: Ingredients:
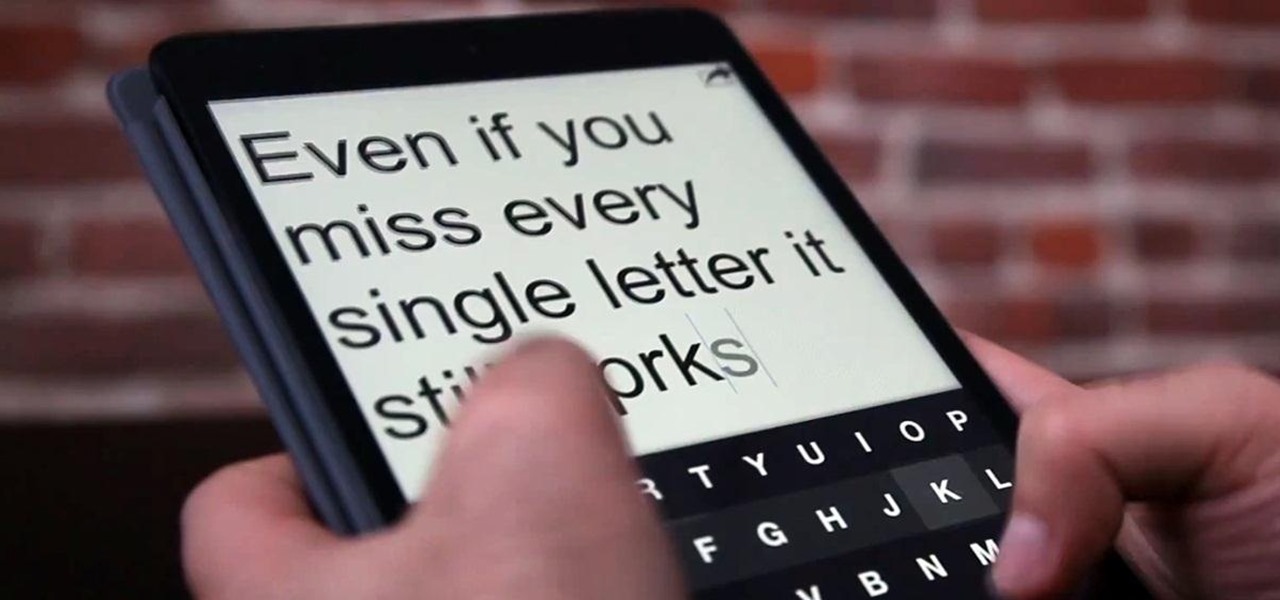
Who doesn't hate Auto Correct? There's nothing worse than hitting 'Send' only to realize that your phone betrayed you by changing a word so that your message doesn't even mean the same thing anymore—especially when it's going to someone like your boss or parents.
With the use of Terminal, anyone can run multiple instances of the same application on a Mac. When you have multiple windows open in a web browser, the windows are all running under the same Process ID (PID). But, with multiple instances, each has its own unique PID. So why would you want to run multiple instances of the same app? There are several reasons a person may run clones of the same application, but the most popular would be so that the user could multitask. Some applications, like t...

No matter how advanced technology gets, there will always be room for classic video games in the hearts of nerds everywhere. Mini arcades became very popular, as they allowed users to take arcade games on the go. As Game Boys and other mobile gaming devices appeared, the mini arcade slowly disappeared. Well, believe it or not you can combine the best of both worlds! Metku user Japala wanted to make his old Game Boy Advance SP "look cool again," so he turned it into a mini arcade cabinet.

Texting is a godsend to mobile devices, but it also has its caveats. Sending a text to someone requires visual, manual, and cognitive attention—looking at what you're typing, holding the phone steady, and thinking about what you're trying to say. So, texting while doing pretty much anything else is not a wise move.

At one time or another, we've all enjoyed the visualizations that came stock in Windows Media Player. I remember spending hours listening to my favorite album, putting the graphic equalizer on full screen, and getting lost in the flurry of colors that would dance across the screen. Well, now thanks to the imaginative mind of Instructables user yardleydobon, you can now recreate this rainbow-colored music visualizer right on top of your freaking head—with these trippy EL wire headphones, which...

Fluorescent dye can be a great addition for decorating around the house for Halloween, especially for a haunted one. Creating your own fluorescent dye is a simple experiment, as long as you've got the proper chemicals and safety gear. Nurd Rage details the chemical process of creating your own fluorescein below.

There are a lot of ways you can use pumpkins to decorate for Halloween. Of course, there's always the traditional jack-o'-lantern, but if you want to step it up a bit, you can make them glow in the dark, or put them to work for you by turning them into surveillance pumpkins to catch pranksters who prefer the 'trick' in 'trick-or-treat.'

Halloween is less than a couple weeks away, so it's about that time you start thinking of cool ways to decorate your house (if you haven't already), and pumpkins are an obvious choice. Pumpkins are one of the cornerstones of Halloween celebrations, dating all the way back to the early 19th century. Carved jack-o'-lanterns are a great way to add some spookiness around the house, but that takes time, skill, and effort. Creating cool glow-in-the-dark pumpkins requires no carving at all—and looks...

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

This method is quick, easy, looks beautiful and does not require any equipment beyond a plastic bag and a pair of scissors.

Small containers are useful for many things. They're good for storing snacks if you have children, as well as holding coins or odds and ends. But those regular store-bought containers are lame—who wants to keep their stuff in a Tupperware dish or old butter container?

Learn how to frost a cupcake using a 1M tip or large tip. The supplies you'll need are cupcakes and a bag with the frosting and the tip. First, squeeze the bag to remove any air bubbles. Take your cupcake in your hand and start at the outside and work your way in. Then, in one motion, go over the first layer to create a stacked second layer of icing. This method gives you a pretty ice cream cone type effect on your cupcakes. Next, you'll learn how to make your cupcakes look like roses. Using ...

How to hack Pet Society! Pet Society cheats, tricks, hacks. Watch this video tutorial to learn how to poop in Pet Society (09/05/09).
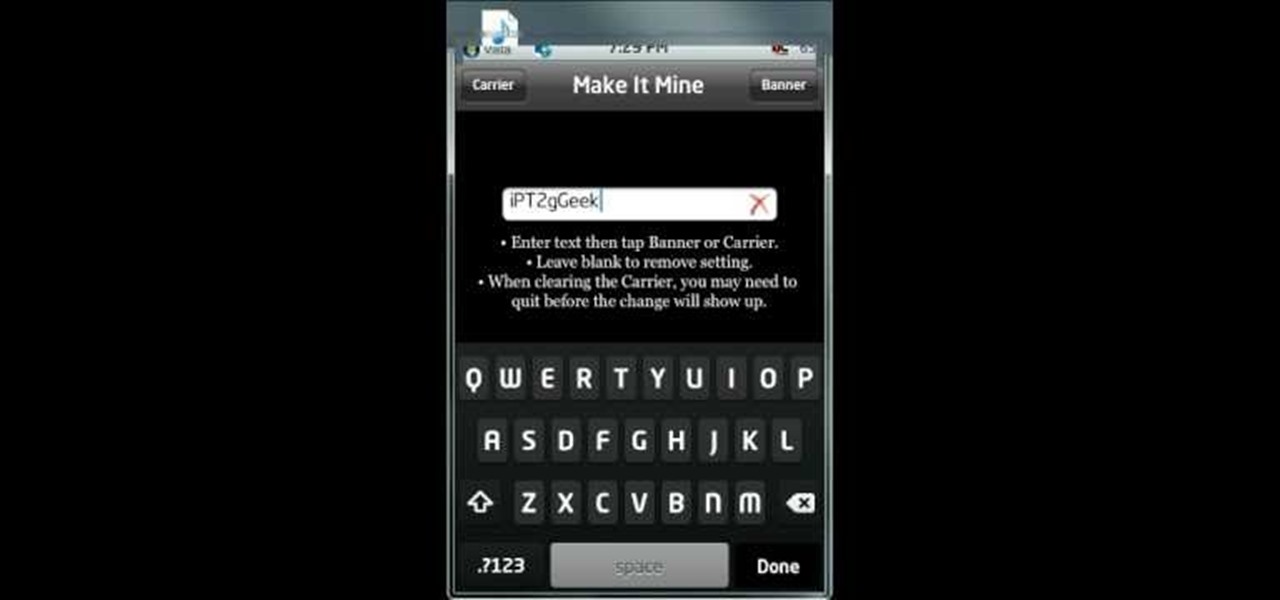
In this video from iPT2gGeec we learn how to change the carrier name on your iPhone. You can make it say anything you want. You need a jailbroken iPhone. Open up Cydia and select the search tab. Type in MakeItMine. Click on it and install and confirm. Now press the home button and click on the app for it. Now you'll get a very simple dialog box. In that box, type in whatever you'd like to change your carrier name to. You can select it to change the carrier or the banner which would replace th...

What's the difference between grilling on a pan in your kitchen and grilling outside with wood chips? It's definitely not just the surface you cook on that changes.
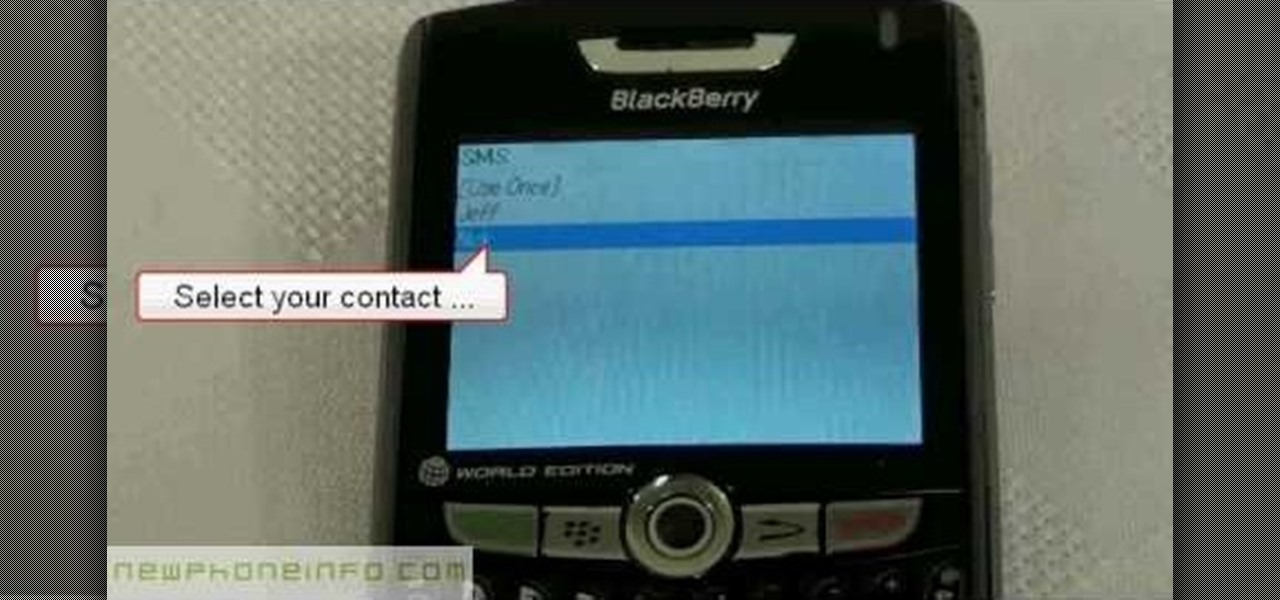
In this tutorial we learn how to text message with the Blackberry 8330. Start on the main menu and then click on the messages icon. From here, you will click on the menu key on your keyboard. From here, scroll down and choose the "compose sms" selection. Next, you will choose who you want to send the message to from your contacts, or choose a number you want to send it to just one time. After this, you will type in your message. Once you're done typing in your message, click on the menu key a...