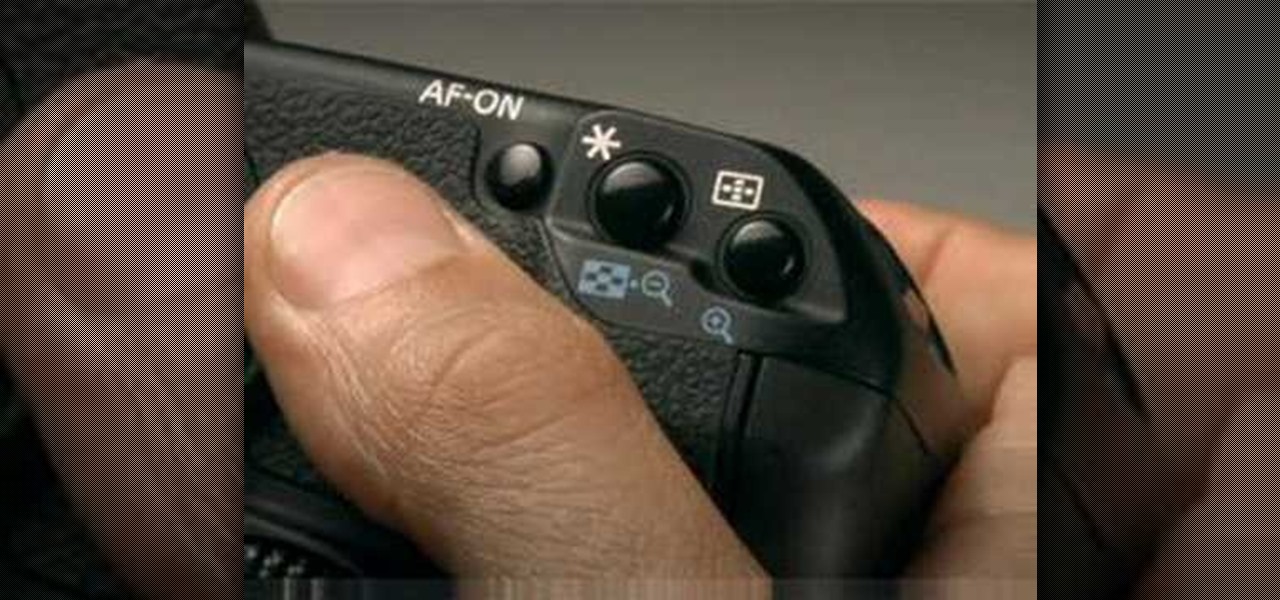
This online manual shows you all of the ins and outs of the Canon EOS 40D digital SLR camera. The guide covers: handling the camera, shooting modes, ISO speed, AF modes, Drive modes, image quality, highlight tone priority, picture styles, white balance, and live view mode

In this online video series you will learn basic floor aerobics from fitness specialist Mandy Muenzer.
In this tutorial, we learn how to play the red and black system in roulette with an online casino. First, do not accept the bonus from an online casino, because you won't be able to use this on roulette and you have to spend 10x that throughout the site. While playing, you're playing against software, not against a casino. You will bet three times, and look to see what you get each time, so you know what to bet when you get towards the end. Based on the system, you will know where to place ea...

Crossword puzzles are great way to exercise you mind and have something fun to do with breakfast. Don’t just do a puzzle, but make one yourself. You can do it by hand or try out the help of a crossword building software.

Flickr is the most known and dependable photo sharing website to date, so if you haven't made an account yet, you better now, if you want to share your precious photos with family, friends, and even the whole world! Flickr allows you to store digital photographs online and share them with other people.

Tracing any IP hostname or web address free online is demonstrated in this video. To trace any IP, website and hostname free online firstly go to the websiteGeoLocationWhen the webpage appears you will get a find option. Enter your IP address, website or hostname here. Then click the find option. Your IP hostname or web address is traced. So easy. Quick and simple to use. Your IP address, city, country, continent and time zone will be displayed in a rectangular box in your location in the wor...

Work is commonly composed as a Microsoft Word document but if you would like to convert that document into a PDF file that any operating system can ready you will need to follow a few simple steps.

In this how-to video, you will learn how to tune a guitar with the help of an online tuner. You will need a guitar. Listen to the low e string note being played and tune your guitar's low e to that tuning. Listen to the a note being played and tune the a string accordingly. Listen to the d string open note being played and tune the d string. Listen to the g string open note being played and tune your g string accordingly. Listen to the b note being played and tune the b string accordingly. La...

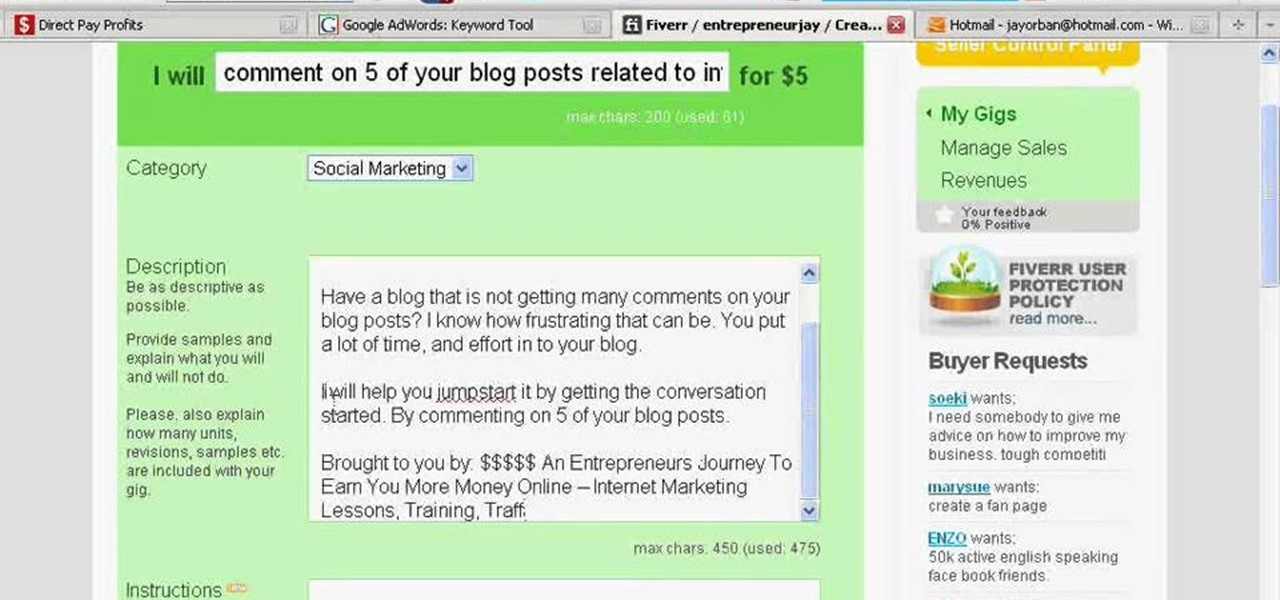
Fiverr.com is a website that allows people to offer different services for $5. If you are interested in making some of your unique skills or talents available online for $5, this video explains how to take advantage of Fiverr.com and start earning money online.

So your friend started humming "Who Let the Dogs Out" and now you CAN'T get it out of your head. Oh yes you can! This helpful little video shows you what unhearit.com can do for you. This website generates random catchy tunes, so you can dump what's in your head and move on to something fresh. Here comes Lady Gaga!

Get tons of money to spend in the free online game Ninja Saga! This tutorial is easy - all you need is the latest version of Cheat Engine. Open Ninja Saga, scan it with Cheat Engine and then enter in however much money you want!

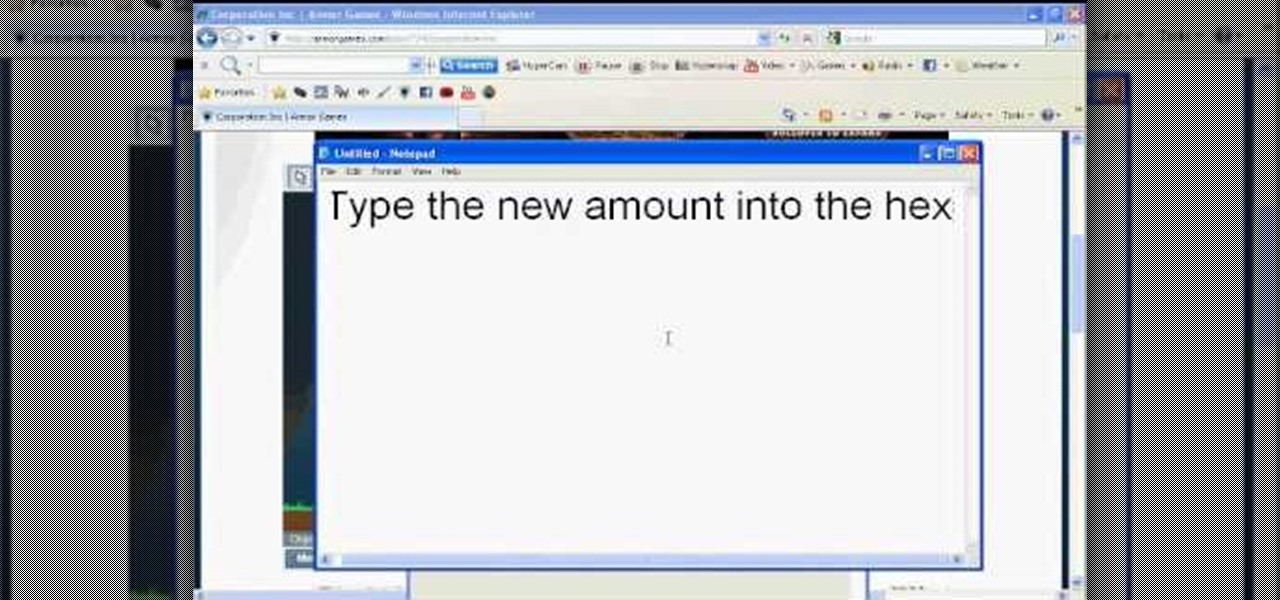
Corporation, Inc., is a fun game you can get from Armor Games. Like most CEOs, you'll want to be as cutthroat and ruthless in pursuit of profits, and that sometimes means cheating. This tutorial shows you how to hack the game using Cheat Engine.

Want to give yourself extra points or resources in the online game Wild Ones? All your friends will be asking you how you passed them up so quickly! Make sure you have the most recent version of Cheat Engine downloaded, first!

An online English teacher explains to English-language learners how to correctly use the word "make" as a causative verb in this instructional video. As usual, he provides many examples to in order to make the contextual usage of this important verb more clear to those attempting to learn American English for work or pleasure.

Explore functions and capabilities of the Rhapsody online music player through your iPod and iPhone with this helpful video guide.

This is a simple blackjack tutorial using Betfair Zero Lounge for gameplay example.

If you are thinking of playing online roulette, here's why you should always choose European roulette instead of the American version.

In this video tutorial you will learn to use Photoshop to create text that resembles what you often find in video games. Learn to use the different options on Layer Style to achieve the effect you want. This example uses "Battlefield" font, a freeware font which you could find online.

The legal battle between Epic Games and augmented reality startup Nreal isn't cooling off anytime soon.

Improving your experience online is getting easier every year. Browsing can be safe, easy, and boundary-less with the right VPN, and gaming online is working better than ever to connect and compete with other players.

Even as the world continues to grapple with the pandemic, the tech industry continues to chug along, with some looking for ways to present new products, and in some cases continue major conferences that reveal the latest in augmented reality developments.

Everyone needs a great website. Whether you want to launch the new business you've been dreaming about in 2021, increase your brand's web presence and bring it into the digital realm, or promote yourself and your portfolio, a fully optimized website is the way to do it — and the results can be life-changing.

UPDATE: Entries are now closed. Thank you for participating! Next Reality is where we help you literally 'see' into the future of augmented reality, and to help with that mission we're offering three free pairs of Snap Spectacles 3 to three lucky readers who sign up for the Next Reality daily AR email newsletter.

It looks as though the novel coronavirus and social distancing guidelines are here to stay for a while. So companies of all sizes and industries are scrambling to adapt to a new reality in which everything from morning meetings to large-scale presentations are done entirely online. It looks like this is going to be the new normal for the foreseeable future.

Since it first launched in 2003, WordPress has dominated the internet. The free, open-source content management system (CMS) is used by over 60 million websites. Wordpress is undeniably one of the most popular CMS solutions in the world.

Every single photo you take carries with it a considerable amount of seemingly "invisible" yet important information known as metadata. Although metadata is usually helpful to sort your photographs by location and date, that same information could potentially be used against you, especially if the pictures are taken during a precarious situation.

With protests springing up across America, there's a chance you may have your first interaction with law enforcement. Many demonstrators will have their phones in-hand to film the action, which, sadly, could prompt an officer to demand the device and any self-incriminating data it may contain. Before this happens, you should know there are tools at your disposal to protect your data in such situations.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

When researching a person using open source intelligence, the goal is to find clues that tie information about a target into a bigger picture. Screen names are perfect for this because they are unique and link data together, as people often reuse them in accounts across the internet. With Sherlock, we can instantly hunt down social media accounts created with a unique screen name on many online platforms simultaneously.

If there's one strength of Apple's that iOS and Android fans can agree on, it's the company's dedication to user privacy. With each new iteration of iOS, Apple builds upon these foundations, enhancing and increasing each iPhone's ability to protect its user's data. In iOS 12, Apple has added many new features to Safari, most of which have their own unique way of keeping you safe online.

Russian cyber disinformation campaigns have many missions, but one of particular interest is using technology to monitor, influence, and disrupt online communications surrounding culturally sensitive topics or protests. The ability to watch these events, and even filter positive or negative tweets to amplify, gives rise to the ability to execute a number of disinformation campaigns.

It's easy to run Kali Linux from a live USB on nearly any available computer, but many publicly accessible laptops and desktops will be locked down to prevent such use. School, work, or library PCs can be secured with a BIOS password, which is often an easily recovered default password. Once you have access, though, you can use a USB flash drive to run Kali live on any PC you find.

Apple has introduced a special edition iPhone 8 and 8 Plus to bring attention to the ongoing worldwide battle against AIDS. As the second iPhones to carry the (PRODUCT)RED name, these rare iPhones may quickly sell out when preorders open up on Tuesday, April 10, at 5:30 a.m. (PDT), so we'll go over some tips to help you secure a red iPhone before it's gone.

For years, PuTTy has reigned supreme as the way to establish a Secure Shell (SSH) connection. However, those days are numbered with the addition of the OpenSSH server and client in the Windows 10 Fall Creators Update, which brings Windows up to par with macOS and Linux's ability to use SSH natively.

Coinbase is the primary go-to for many users when it comes to investing in Bitcoin (BTC), Ethereum (ETH), Litecoin (LTC), Ripple (XRP), and more, due to its user-friendly interface. But before you join them, know that the ease of use comes with a price. Coinbase charges fees for each transaction, and your bank might even add charges on top of that. Plus, there is some fine print to be aware of.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

The big day is nearly here... Super Bowl 50 kicks off this Sunday, February 7, at 3:30 p.m. PST (6:30 p.m. EST). And whether you're having a giant party or watching the game on your big-screen TV by yourself, there's one thing you probably won't be doing: cooking food in your kitchen.

Of course, if it were a perfect form of currency, it would have become the standard by now. But it hasn't. Wanna know why? The story begins with the advent of agriculture, when humans had settled down under groups as units called villages, over 10,000 years ago.

hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.