
Exclusive: Meta Patent Infringement Case Moves Step Closer to Resolution, New Asset Owner Revealed
The story of Meta and its Meta 2 augmented reality headset isn't over, there's a new development that could impact its ultimate fate.


The story of Meta and its Meta 2 augmented reality headset isn't over, there's a new development that could impact its ultimate fate.

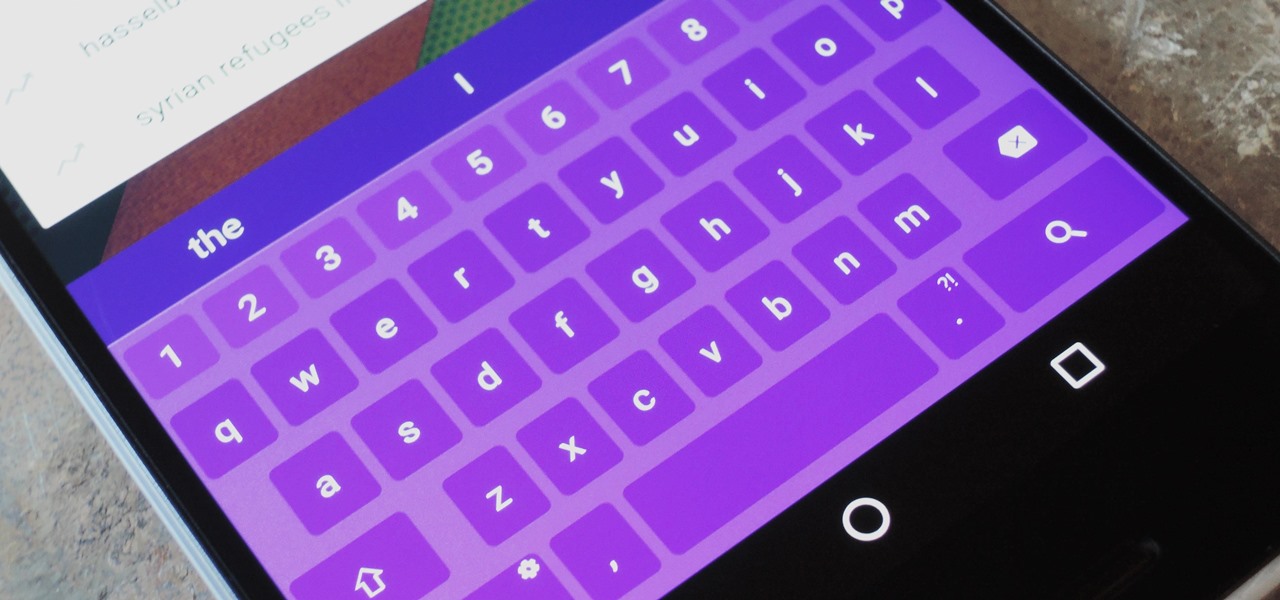
As highlighted in our article on how to enable Google Now in Action Launcher, doing so takes away the Quickdrawer. This effectively ruins one of the more beneficial features of Action Launcher, making it a tough choice between the two options. So I looked for a solution and found one that works.

The OnePlus 5 doesn't have too many weak spots, at least not when you consider the price. But you might feel that the company with the slogan, "Never Settle," might have actually settled a bit with its camera. The OnePlus 5 and 5T don't have bad imaging specs, but they could use a pick-me-up, which is what we're about to provide. There's a bit of a catch, though.

The Galaxy S9's Super Slow-mo feature comes packed with tools that help you tweak your slow motion clips like a pro. Among these is the ability to convert your slow motion videos into GIFs with a user-friendly interface. As a result, it's incredibly easy to go from recording to GIF conversion and on to sharing in a few taps.
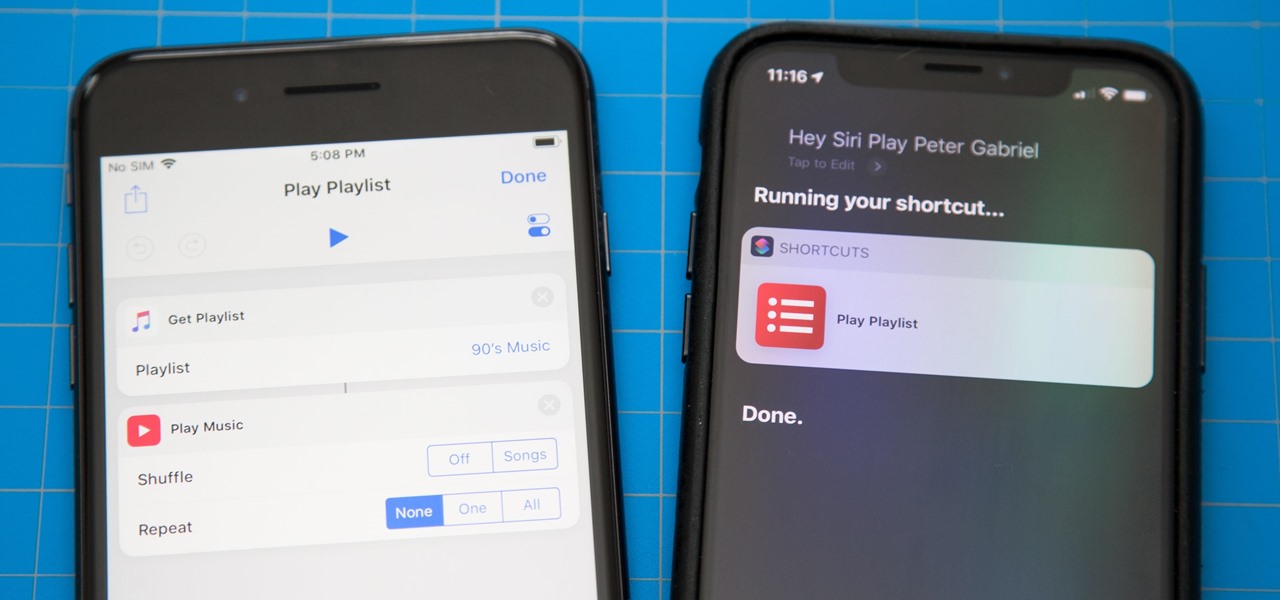
One of the most exciting additions to iOS 12 for iPhones is called Shortcuts, a tool integrated with Siri to help you get things done faster. While there are a few recommended shortcuts available to you in Siri's settings in iOS 12, the Shortcuts app brings the functionality of Workflow to Siri so you can build your own custom actions or select from the gallery of available shortcuts.
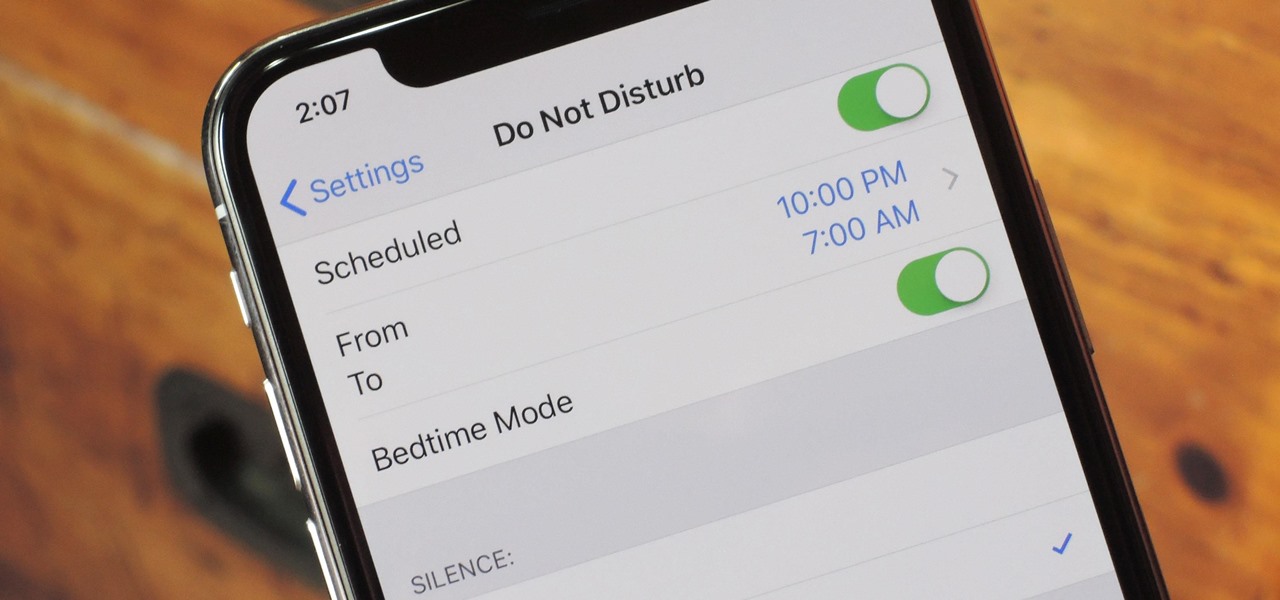
Apple knows their products can be addicting, and with iOS 12, they are doing something about it. With the help of Screen Time and few other new tools, it should now be a lot easier to get off your phone and enjoy life in the real world.

Over the years, we've seen security breach after security breach, as well as high-profile data scandals where collected personal information was misused by companies. Apple makes customer privacy a priority, so there have been few issues to worry about when it comes to its services on your iPhone. However, there are still plenty of privacy settings to explore and change, especially within Safari.

If you want to follow Null Byte tutorials and try out Kali Linux, the Raspberry Pi is a perfect way to start. In 2018, the Raspberry Pi 3 Model B+ was released featuring a better CPU, Wi-Fi, Bluetooth, and Ethernet built in. Our recommended Kali Pi kit for beginners learning ethical hacking on a budget runs the "Re4son" Kali kernel and includes a compatible wireless network adapter and a USB Rubber Ducky.

Between the Cambridge Analytica scandal and the revelation that Facebook logs your calls and text history on Android, many are considering joining the #DeleteFacebook movement. But it can be difficult to leave the site, because so much of its content is only available to active users. If you want to keep in the loop without sacrificing your privacy, you'll want to follow the steps below.

While TouchWiz as an Android skin isn't a favorite among many, Samsung Internet is a fantastic web browser that S9 owners should be happy to have preinstalled out of the box. But you don't need to buy Samsung's latest flagship to try their browser — Samsung Internet is available to all compatible Android phones.

Venmo makes it incredibly convenient to send money to friends and family, and it all happens instantly from the comfort of your smartphone. Even better, if you have an iPhone, Venmo lets you conduct transactions straight from the default Messages app, giving you more flexibility and convenience over Android users.

An incorrectly scaled object in your HoloLens app can make or break your project, so it's important to get scaling in Unity down, such as working with uniform and non-uniform factors, before moving onto to other aspects of your app.
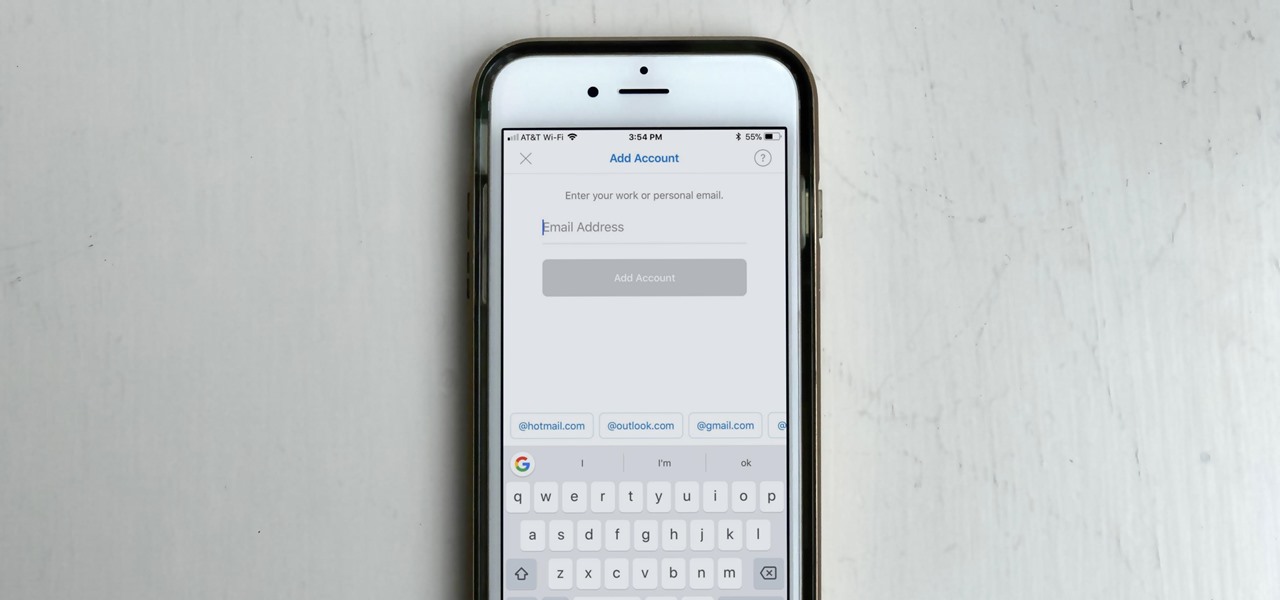
If you work with multiple email addresses, you need an app that can organize and declutter your day-to-day messages. Outlook is a great choice, but if you only have one account attached, it somewhat defeats the purpose. Lucky for you, adding additional email accounts is both quick and simple.

Configuring onion services for the first time can be tricky. A surprising number of system administrators make seemingly trivial mistakes that ultimately lead to catastrophic cases of de-anonymizing supposedly anonymous sites on the dark web. OnionScan is a tool designed to identify common misconfigurations in onion services and aid us in understanding how to fix them.
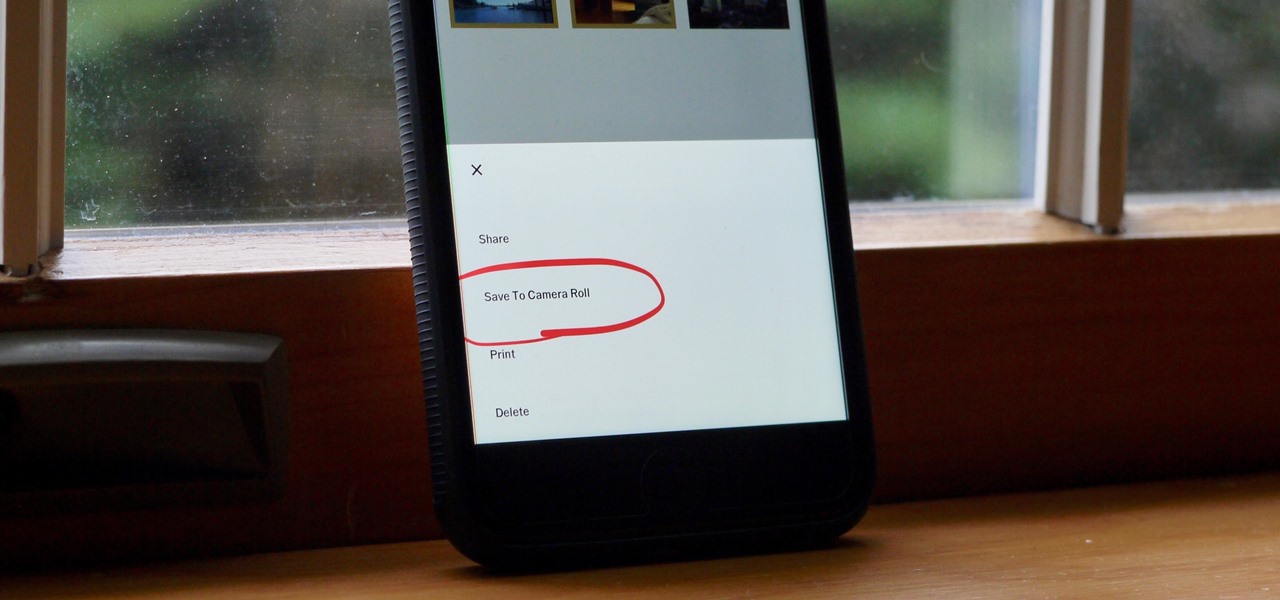
Whether you use VSCO to take all of your photos or you use it primarily to edit photos you take with others apps on your iOS or Android phone, you're at some point going to want your VSCO pics to end up in your Camera Roll or Gallery. VSCO doesn't add them there by default, but there's a couple of ways to get them there.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

While fully closing apps on your iPhone can keep it running at peak efficiency since it frees up memory and stops background refreshing, it's most critical when dealing with unresponsive apps. If you have an issue with a certain app, you can just force-close it instead of rebooting.

By default, iMovie for iPhone adds a dissolve (also called a crossfade) in between all of the video clips in your movie project's timeline, which is an effect that transitions gradually from the end of one clip to the beginning of another. However, iMovie does not add any beginning transitions to your first video clip or ending transitions to your last video clip. But that doesn't mean you can't.
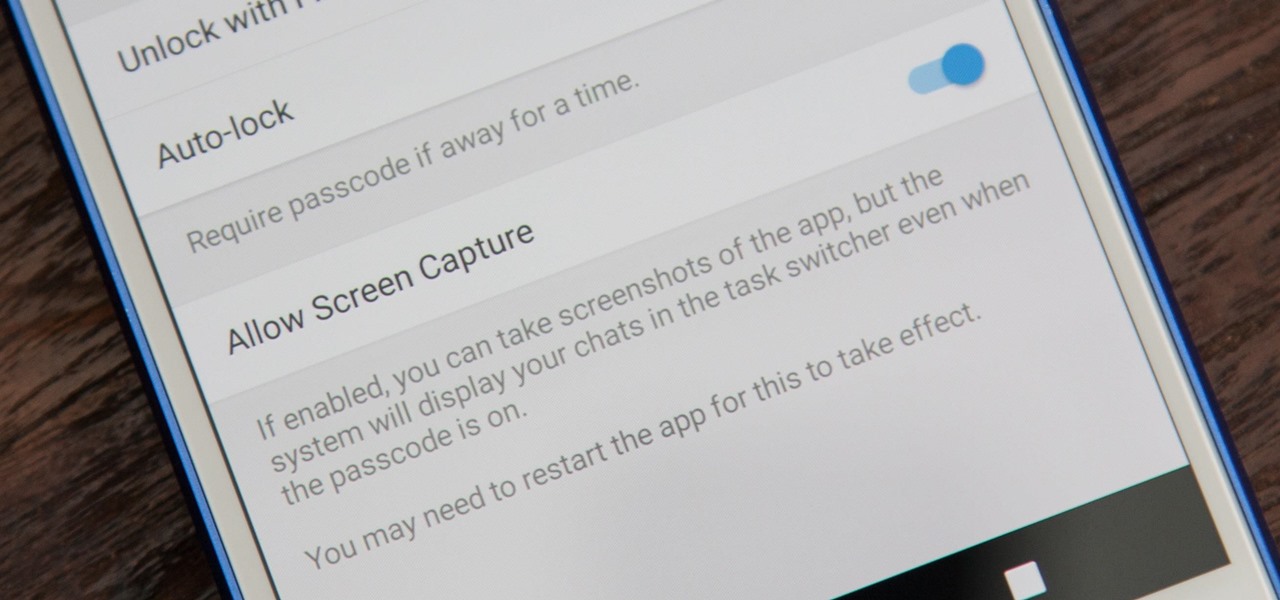
While it's easy enough to take a screenshot of an end-to-end encrypted Telegram chat thread using an iPhone, it's an entirely different story on Android phones. Telegram disables screenshots for Secret Chats by default on Android, and not everyone can turn it on.
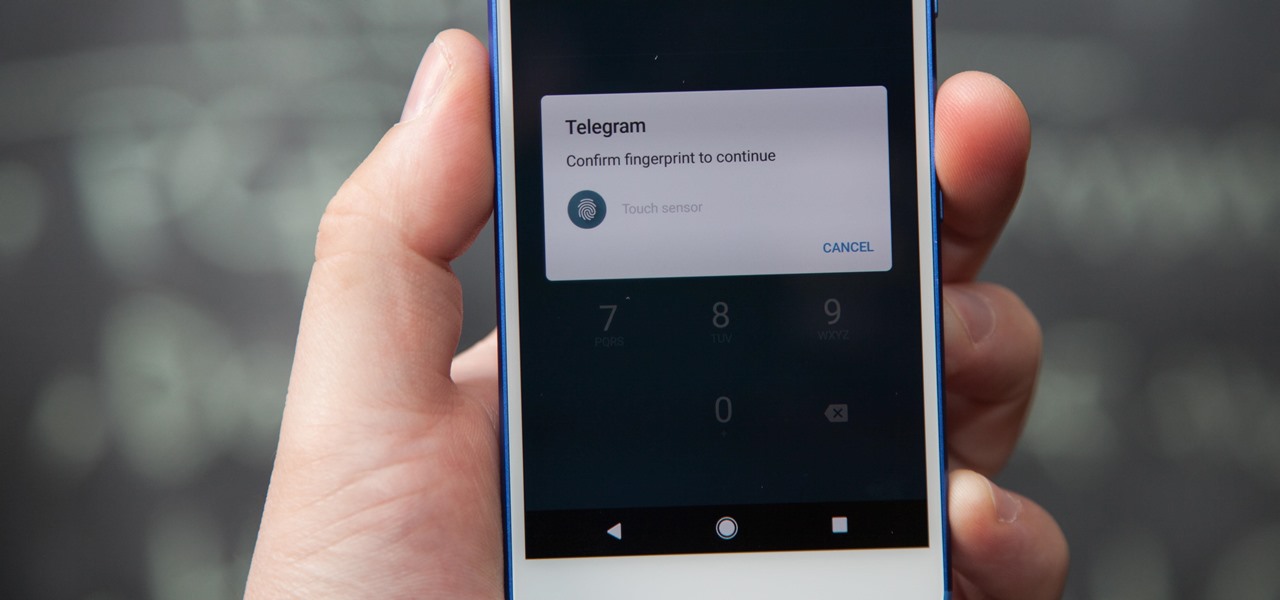
If you're using Telegram for its "Secret Chats" feature, which provides end-to-end encryption for your messages, then I'd highly recommend locking down the app itself with a passcode, PIN, or password. While your phone itself may have a secure lock screen already, if that gets compromised, you'll at least have an extra layer of security on your important conversations.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.
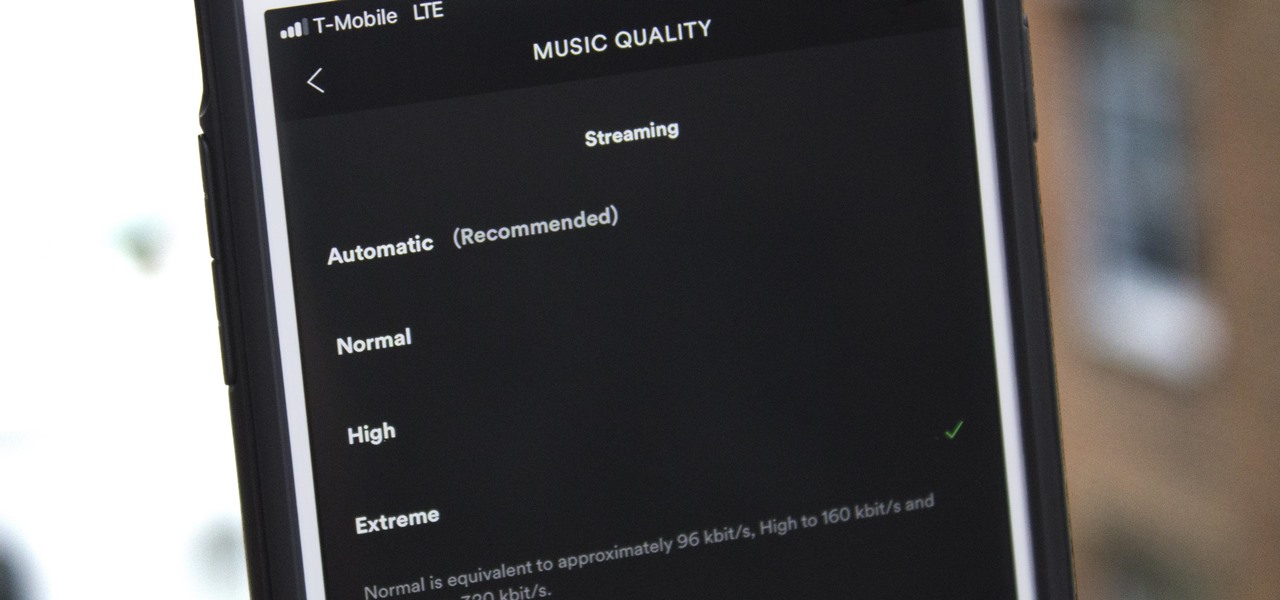
Spotify's massive song catalog can be streamed in decent quality on iPhone or Android without any tinkering. But if you're an audiophile, you've probably noticed that the sound quality can fluctuate from time to time.
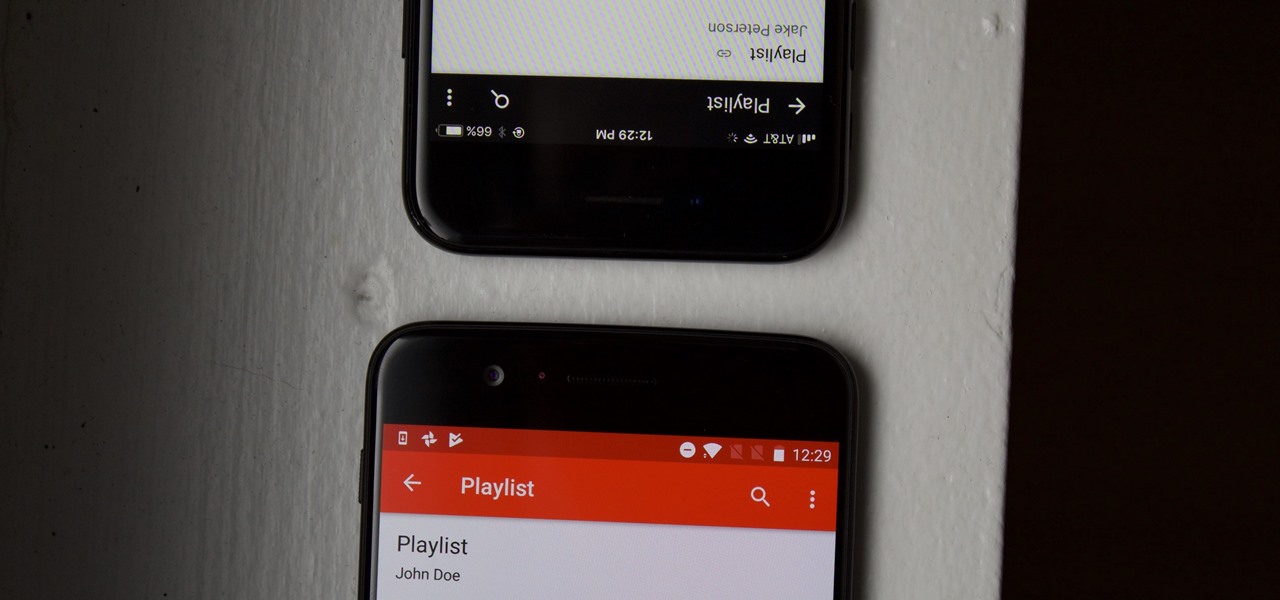
YouTube is a giant platform — over 300 hours of video are uploaded every minute. It can be difficult to keep track of your favorite videos in such a chaotic sea of content. Difficult, but certainly not impossible.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.
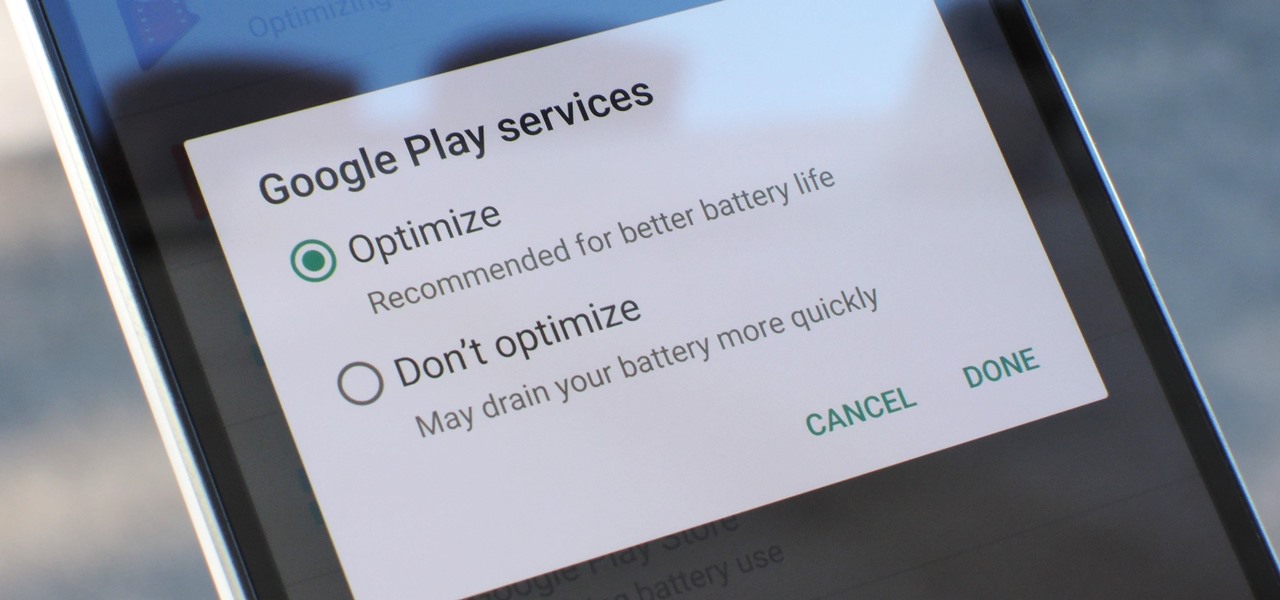
Google Play Services has been near the top of every Android user's list of battery-sucking apps for years now. It's a core system app, so you'd expect some battery drain, but for many folks, it runs rampant.
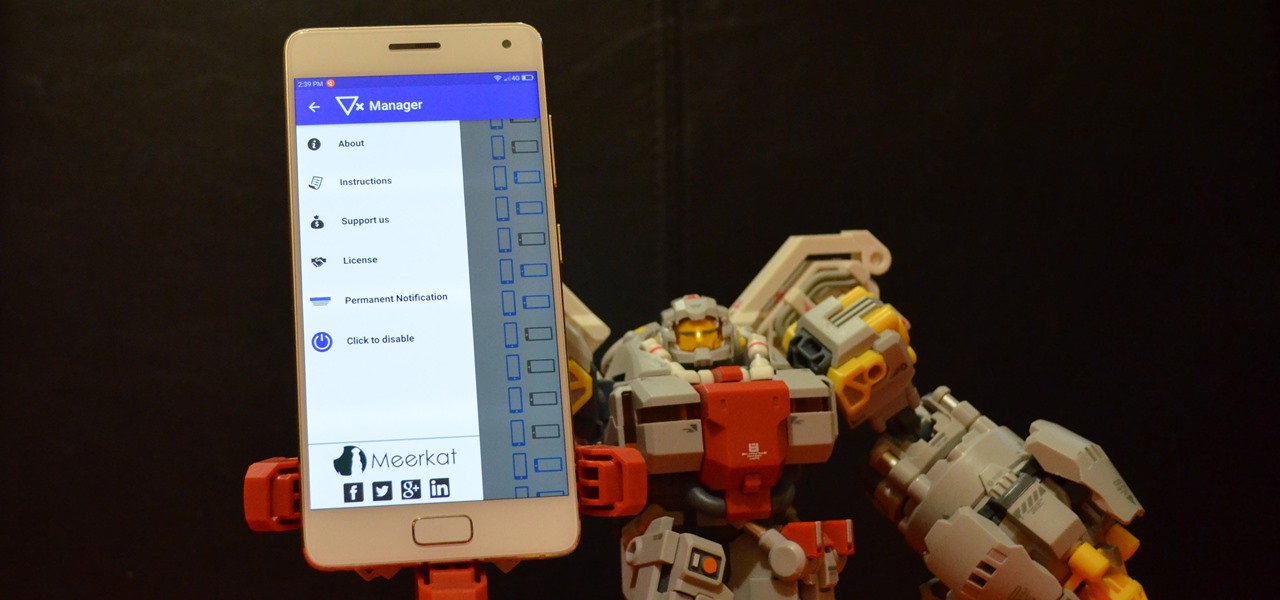
We've all been hit by inopportune screen rotations at some point or another. Having the display orientation suddenly go from portrait to landscape when reading an interesting article in bed is one of the biggest irritations that come with using a smartphone (at least, for me). Thankfully, there are apps out there for your Android to help alleviate this inconvenience.

Sometimes it's the smallest feature in your smartphone that makes the biggest difference in user experience. Take screen timeout, for instance. You can probably think of plenty of times when your handset's display blacked out while you were in the middle of something. You could have been cooking with a recipe on the screen or looking at chords while you learned a new riff on your guitar.

No matter which smartphone you buy, it will come with an internet browser preinstalled. Depending on your OEM, the default browser might be called Samsung Internet, HTC Internet, Silk Browser by Amazon, ASUS Browser, or Google Chrome—there's just so many stock browsers available.

Don't let the lack of owning a HoloLens stop you from joining in on the fun of creating software in this exciting new space. The HoloLens Emulator offers a solution for everyone that wants to explore Windows Holographic development.
Google's new Pixel phones are shaking things up in the world of Android, as the Nexus line is no more, and the Mountain View tech giant has now become a smartphone OEM. The long-term impact of these moves remains to be seen, but we already know that Google, the manufacturer, will be adding extra software and UI features to the version of Android that ships with its Pixels.

Wi-Fi signals have limited range, so if you live in a two-story house or work in a larger office, you may have set up multiple routers or repeaters to ensure full wireless coverage. Sadly, Android handles the transition between networks pretty poorly.
North American users get a raw deal when it comes to Sony devices. For some reason, the critically-acclaimed Xperia lineup of smartphones is hardly ever available here, whereas in Europe, the Sony Xperia Z series is one of the most popular flagship devices around.

A VPN service is almost an essential these days. Good ones can block ads, prevent tracking cookies, encrypt your internet traffic for better security, and even spoof your device's location to bypass geo-restrictions — all things you should be concerned about in the age of NSA snooping and Facebook data mining.
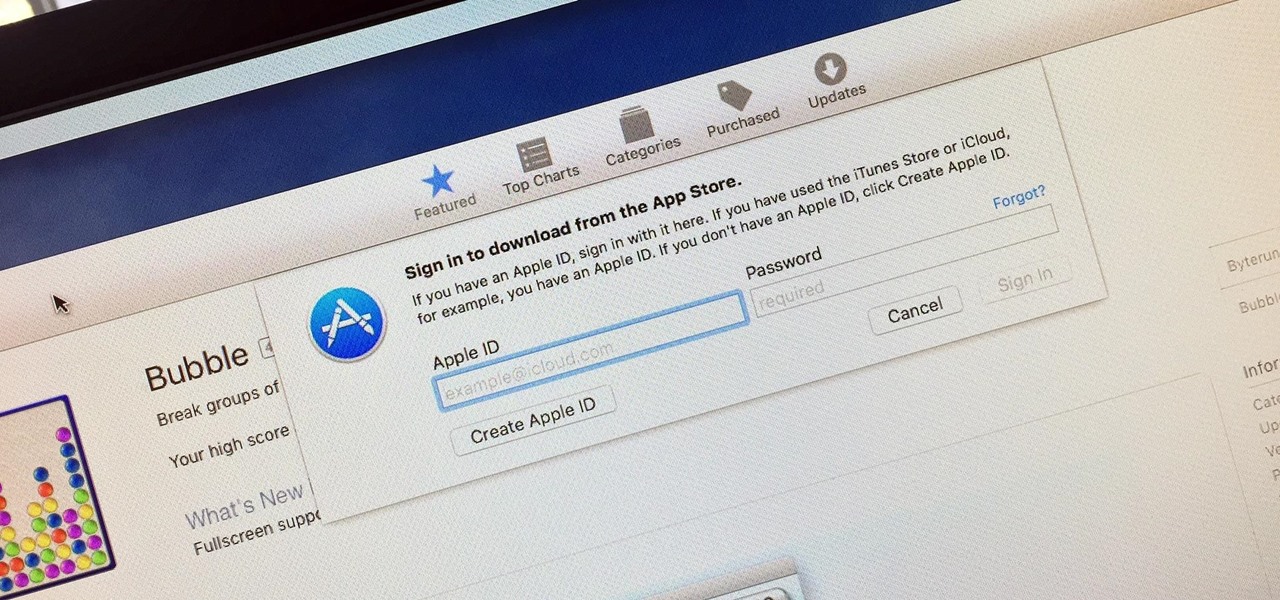
Whether you want to edit photos, compress files, play games, or DJ your next party, there's a free Mac app that can help you out. But things can get annoying real fast if you download a lot of free apps from the Mac App Store, since you have to type in your Apple ID password each time.
You can use the F1 key to notably dim your Mac's display, but sometimes that just isn't dark enough. If you're working in pitch black conditions, have a migraine or tired eyes, or just want a more comfortable environment, you might want your screen even darker—without making it pitch black.

If you're looking to customize your Android beyond its stock options, things can get confusing quickly. One of the best places to get into developer mode is the XDA forums.
Being able to customize the look and feel of your device is the main reason a lot of folks choose Android over iOS. And perhaps the single biggest way to visually overhaul your phone or tablet's UI is to apply an icon pack, which can liven up your home screen with bright colors or make things look a bit more classy with a sleek, minimalist style, for instance.
Hello fellow Nullbytiens, I'm Washu, a long time commenter but first time poster. Today we'll be making an IRC bot, if you haven't seen OTW's post about the new IRC channel I would encourage you to go check it out. He does a good job at explaining what IRC is and how to get set up.
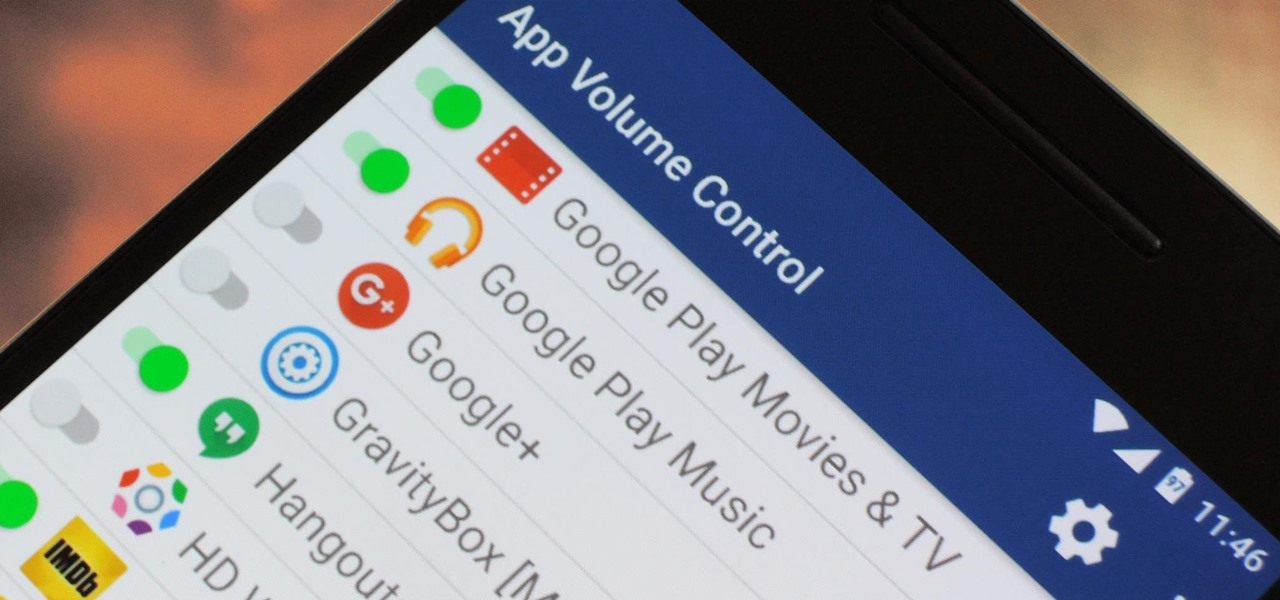
You can do practically anything with a modern smartphone or tablet, so it stands to reason that the apps you have installed may serve vastly different purposes. Picture a game and a video player sitting right next to each other in your app drawer—odds are, you want the sound turned up while you're watching videos, but would prefer that the game was muted or a little lower. As a result, we're constantly tweaking volume levels to get the best experience.

A lot of people think that TOR services are unhackable because they are on a "secure environment", but the truth is that those services are exactly the same that run on any normal server, and can be hacked with the same tools (metasploit,hydra,sqlmap...), the only thing you have to do is launch a transparent proxy that pass all your packets through the TOR network to the hidden service.