This video shows a quick and easy way to create a drum loop using "MIDI MERGE". A stereo instrument track with expand 2 is used here. First, select a track, expand 2, and select session drums (you can take any other track) for the patch and also create a "click track" which will be available in the track menu. Open the transport window and select "loop playback". In order to create a looped playback, right click on the "play" button and select "loop". This is a loop, so make sure that you do ...
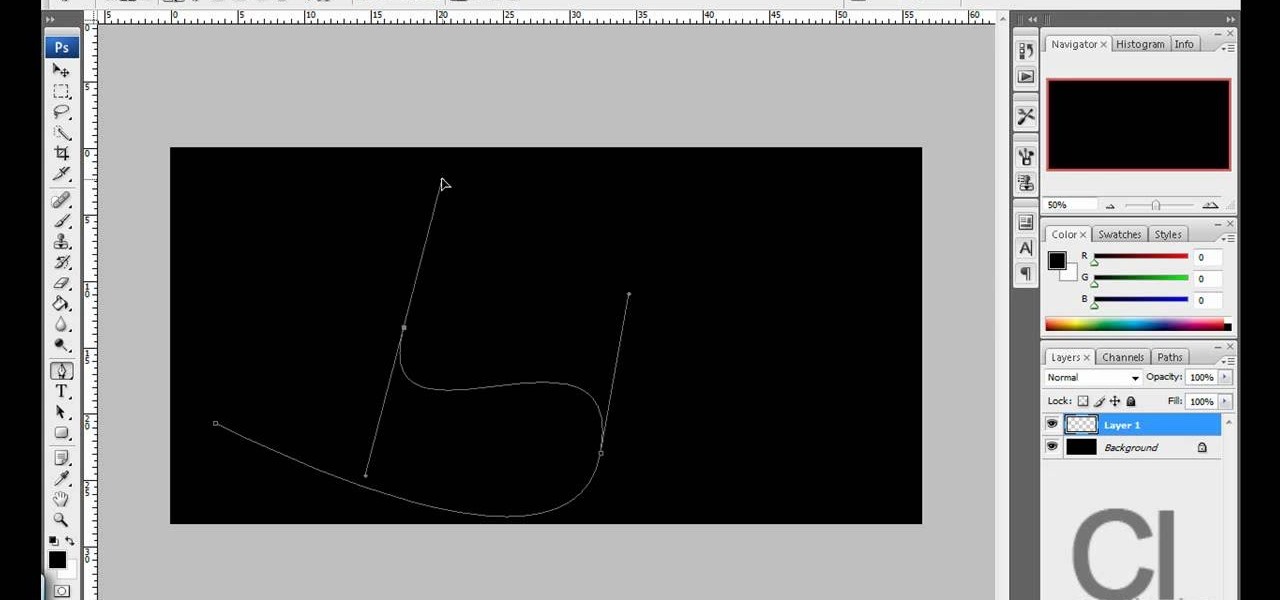
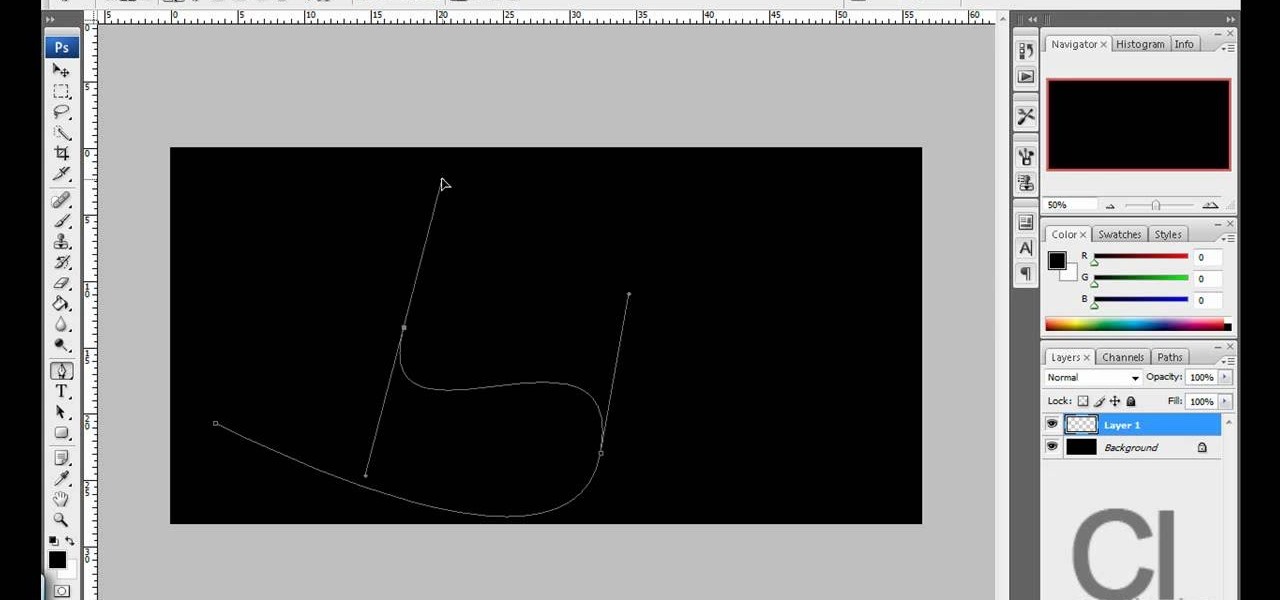
This is really cool, you can make these awesome neon glowing lines using your Adobe Photoshop. This is a fun way to make creative and colorful designs and it looks really neat without spending time working on detailed shapes.

The video shows us how to use audacity to record audio. Firstly you need to have the software audacity installed in your system and for that Google and search for 'audacity' and after that you get a link to save and install the software. Once the installation is done, open audacity and on the drop down menu the default is set to microphone, change that to stereo mix and copy my settings. Once this is done we will be recording the audio. Go to a site like youtube and press the record button in...
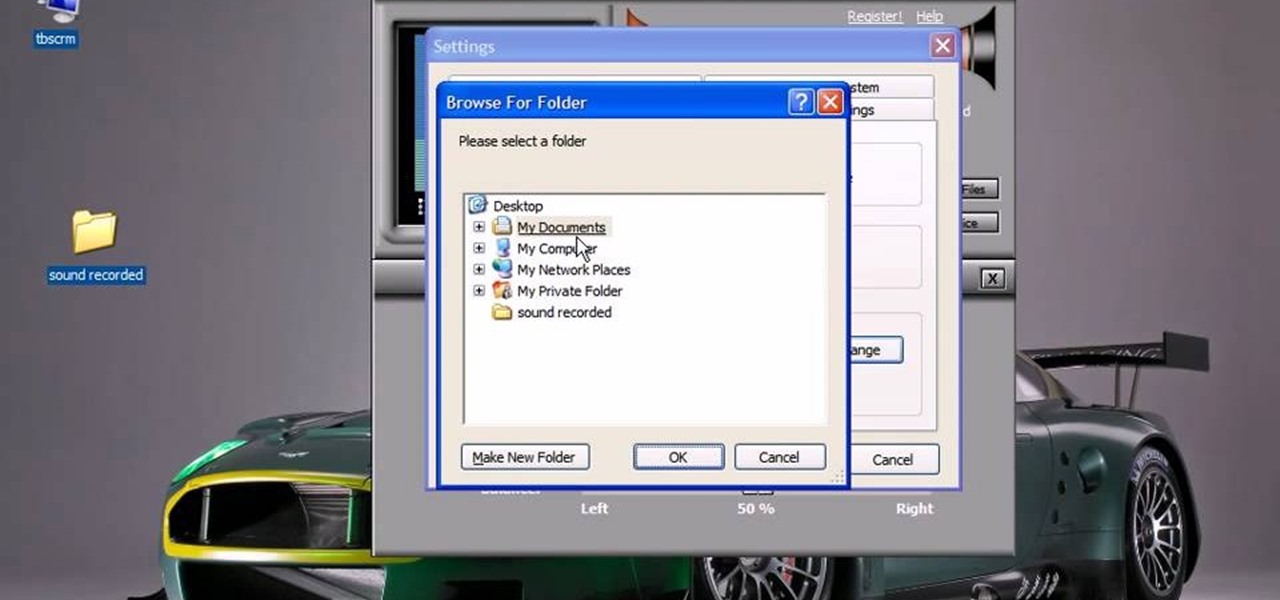
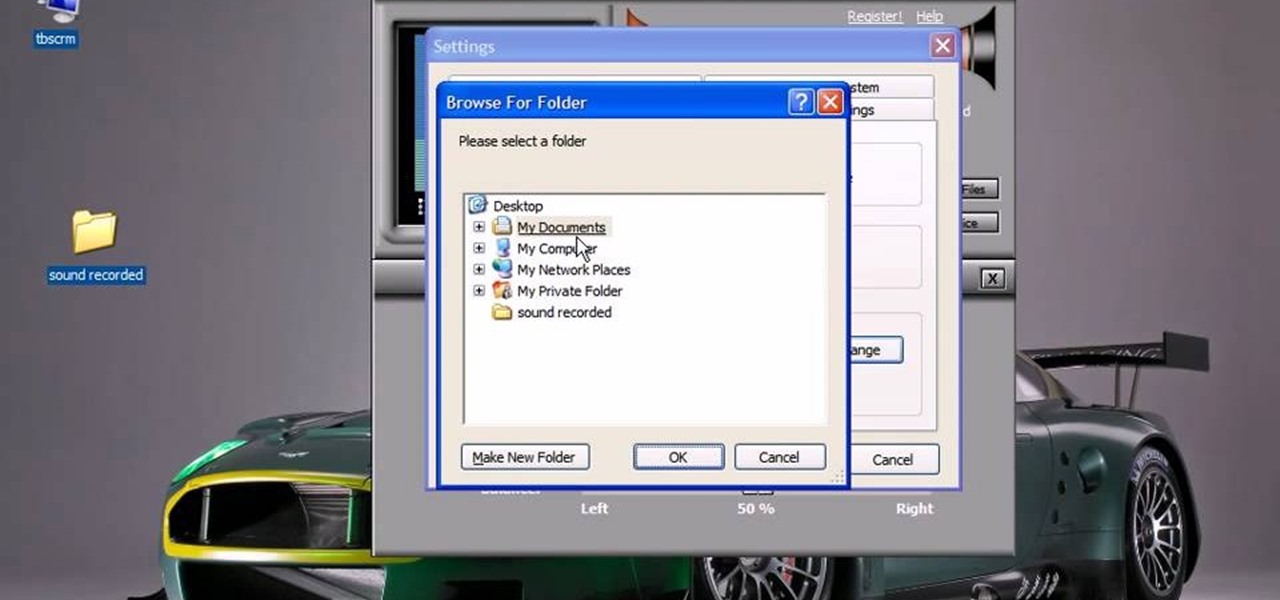
This video will show you how to record audio from the internet. Once you install this program, the video goes on to give you step by step instructions on all of the bells & whistles within the Free Sound Recorder. It will teach you how to work it according to your computer settings, and show you how to personalize and change the settings within the program. It gives you recommendations on the best options for the best audio. It also gives suggestions like choosing which folder to default all ...
This video will show you how to play free ISO / CSO games on your PSP 3000 using ChickHen. The steps performed are as follows:

Got a digital camera, but no idea how to share pictures with friends and family? Try the photo-sharing site Flickr.

In this video series, you will take a look a the new Houdini 9 interface and learn how it will make your work faster and easier.

WordPress is a hugely popular blogging content management system, or CMS. This video offers a walkthrough of designing for WordPress. In part one, you will be downloading and installing WordPress. Then you will install the "Starkers" theme by Elliot Jay Stocks to start with a completely fresh slate for our new design. No sense starting with the default theme; it's more trouble than it's worth! In part two, you will go over the theory behind designing for WordPress and how it's much like "work...

Want to control a friend's cell phone remotely and make "free" calls from it? In this hack how-to video, you'll learn how to hack Bluetooth-enabled cell phones with your Sony Ericsson or Nokia phone and the Super Bluetooth Hack—or "BT Info"—, a free program easily found through Google. Once installed, Super Bluetooth Hack will enable you to control your friends' cell phones remotely.

Even though most phones don't have Oreo yet, Google has released Android 9.0 Pie. It's available on Google's own Pixel devices, and updates should soon be available to partnered devices from Essential, Nokia, Oppo, Sony, Vivo, and Xiaomi. We're already digging into it to highlight all of the features and changes.

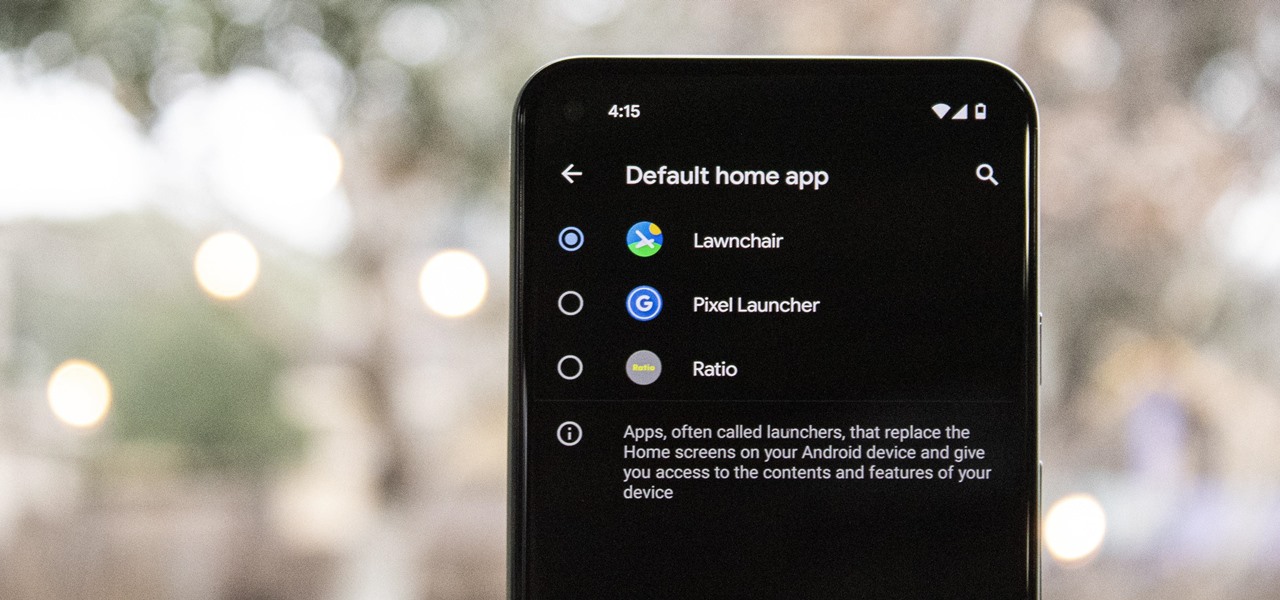
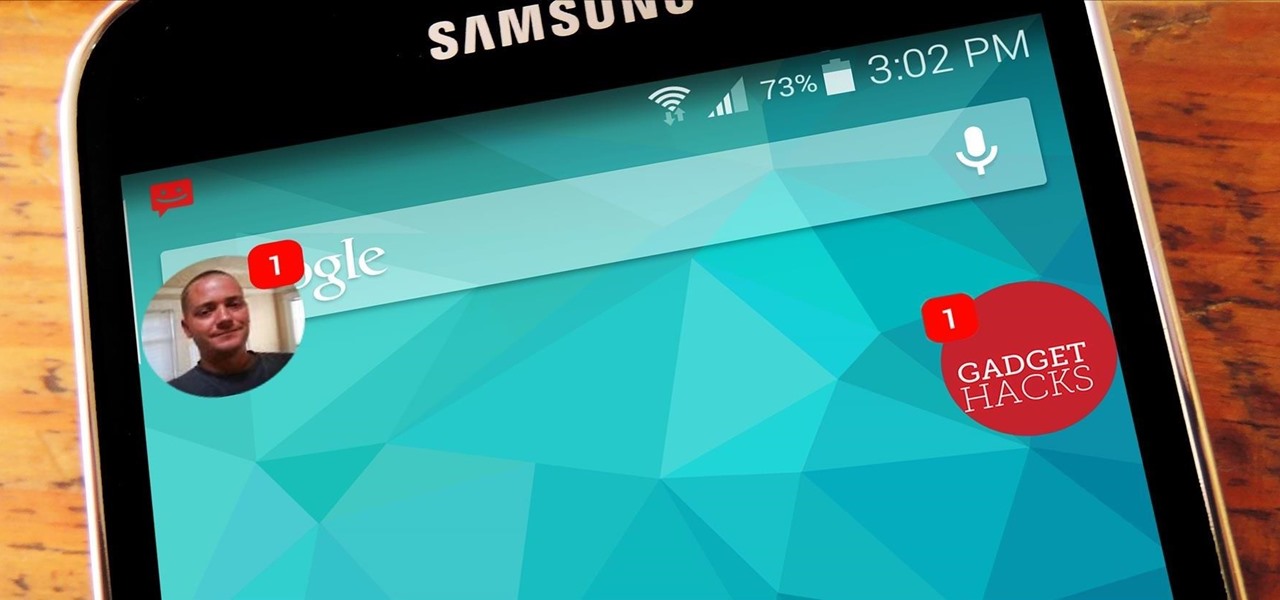
One of the easiest ways to change up your Android experience is by swapping out the stock launcher with a new one. The word "launcher" is Android lingo for "home screen app," and it's a common term because of how easy it is to switch to a new one. So if you're looking to revamp your home screen, this guide's for you.

Though more well known for their OLED displays and advanced cameras, Galaxy phones like the S8, Note 10 & 10+ and S10 series are a force to be reckoned with when it comes to audio. In fact, flagships from the S9 on up feature AKG-tuned stereo speakers, along with a slew of software enhancements that make listening to music a truly pleasurable experience.

No matter how good a display is, the idea of perfect color calibration is subjective — some prefer warmer more saturated colors, while others prefer the calmer cooler side of the color spectrum. It is almost impossible to create a single color calibration that everyone can agree on out of the box. The display on the Pixel 2 XL was specifically calibrated with a more realistic color profile in mind.

In 2013, Offensive Security released Kali Linux, a rebuild of BackTrack Linux derived from Debian. Since then, Kali has gone on to become somewhat of a standard for penetration testing. It comes preconfigured with a collection of tools accessible by a menu system, tied together with the Gnome desktop environment. However, Kali Linux isn't the only penetration-testing distribution available.

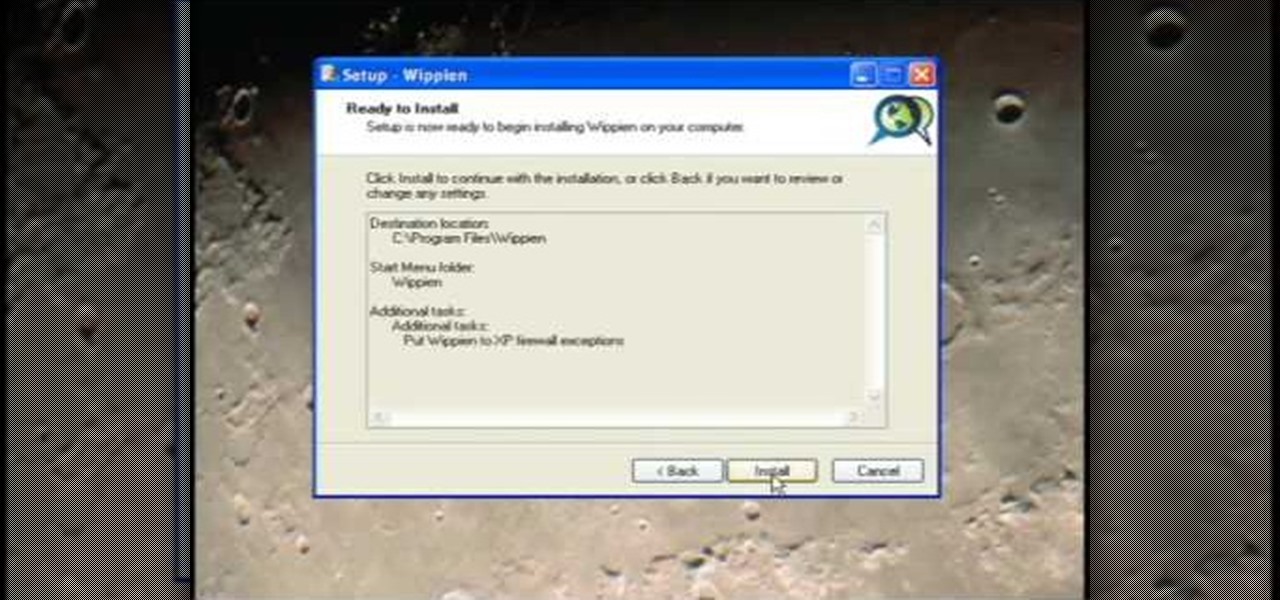
This video tutorial from ruralgeek shows how to set up and use Wippien VPN on Windows XP. First, download Wippien client from here: www.wippien.com.

how to create an Ocean in 3DS Max

If you get looks of exasperation whenever you stammer out a drink order, take this crash course in bar-speak.

Things tend to get noisy when you're in a big group chat, which is why the notification sound for that thread shouldn't be your standard, attention-grabbing ringtone. But you don't want to set the default notification sound to something too subtle, otherwise you'd miss messages that actually matter.

While SSH is a powerful tool for controlling a computer remotely, not all applications can be run over the command line. Some apps (like Firefox) and hacking tools (like Airgeddon) require opening multiple X windows to function, which can be accomplished by taking advantage of built-in graphical X forwarding for SSH.

Safari has always done a great job at letting you browse the web, but it has never so much as offered a way to download files locally. Other apps have stepped in to help fill the gap, but they never felt as integrated into the iPhone as a native downloads manager would. They aren't needed anymore though, because Apple added one in iOS 13, pushing Safari on the iPhone closer to its sibling on the Mac.

All of the new iPhones from 2018 were released with dual-SIM support, but none of them were capable of actually using the eSIM in iOS 12, only the physical nano-SIM. But on iOS 12.1 and later, you can finally take advantage of eSIM so you can have, say, a business and personal plan on your iPhone XS, XS Max, or XR at the same time.

As a longtime Android user, one of the changes I was most excited about with Android Pie was the fact that the volume rocker finally controls media volume by default. However, the new way isn't ideal for everyone, but thankfully, there's an app that can change it back.

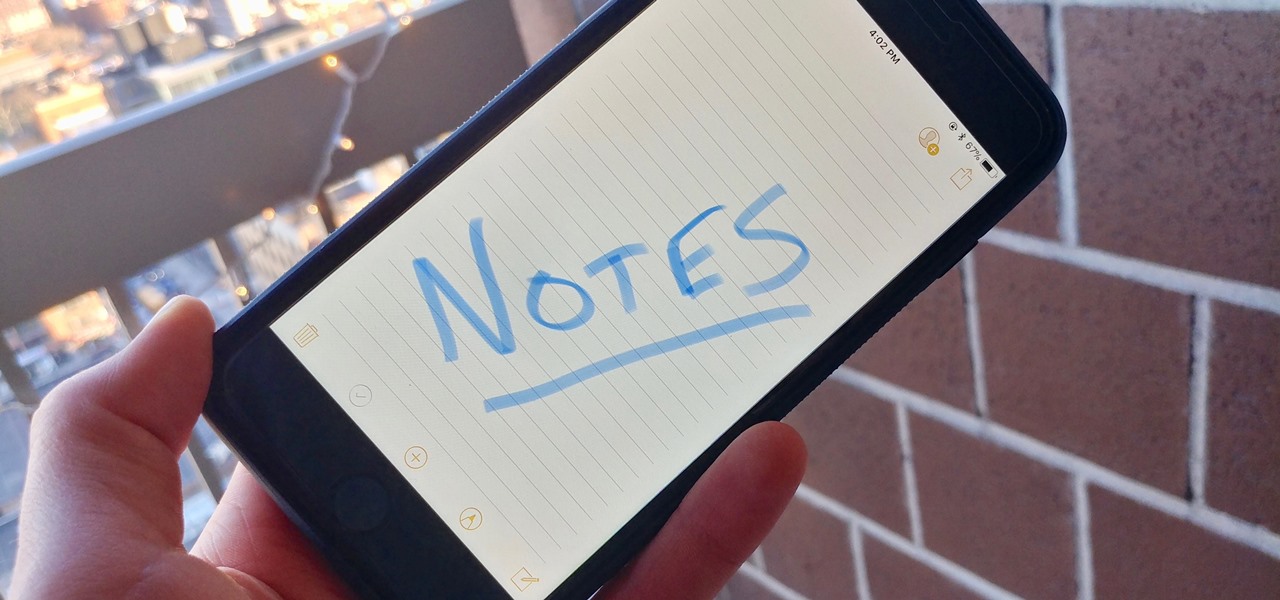
When you have an idea you want to jot down or a quick list to make, the Notes app on your iPhone is a great place to do it. However, by default, Notes use a blank canvas, which doesn't match the physical lined notebooks we're used to. If you've always use unlined or gridless sheets of paper, a blank canvas is probably fine, but you can actually customize your digital stationary with lines or grids.

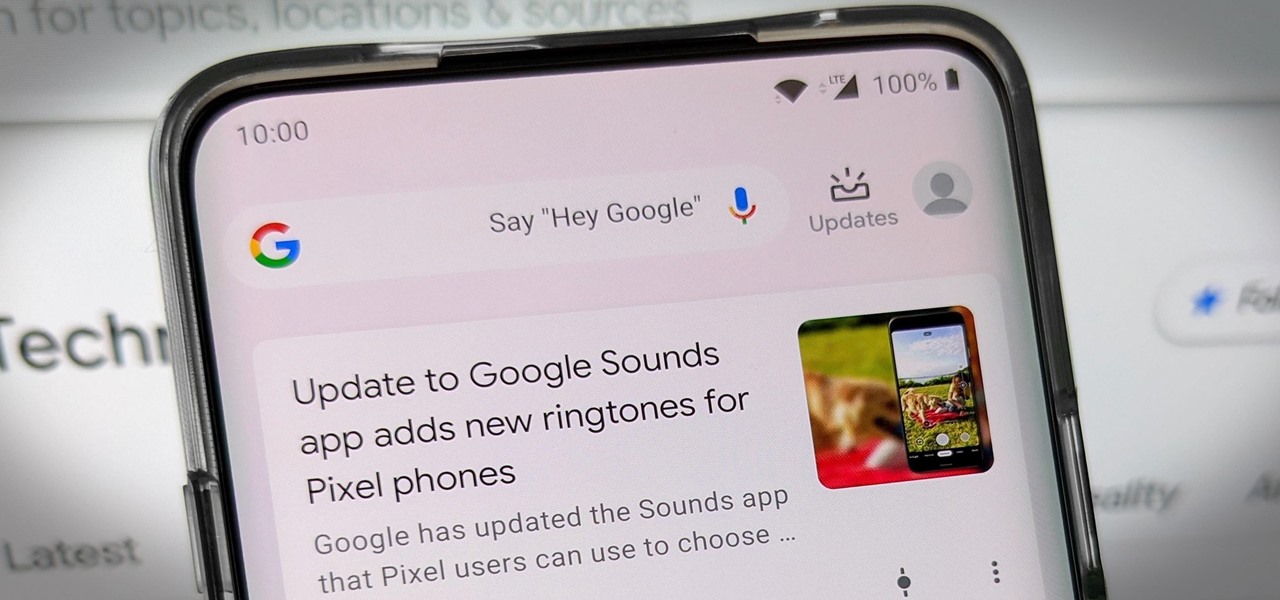
Pixels and other near-stock Android phones have the Google Feed baked into their home screen, but sadly, the default OnePlus Launcher doesn't. Even more disappointing is the fact that the OnePlus Launcher actually has the Google Feed code built into it, but it's not activated. Let's change that.

When Android 4.4 was released, the massive changelog led to some awesome new features getting lost in the virtually endless list of new tweaks. One such change was the ability to set a default text messaging app, which streamlined the existing process of installing a third-party SMS client.

We all know Google keeps a history of everything we do on our phones unless we say otherwise. However, you might not realize just how detailed it is until you check it for yourself — even the actions you do in each app are tracked by default.

The newer HTC One is arguably the best smartphone yet in terms of hardware, but its software moves considerably farther away from the stock Android experience. Even more so from HTC's own Sense.

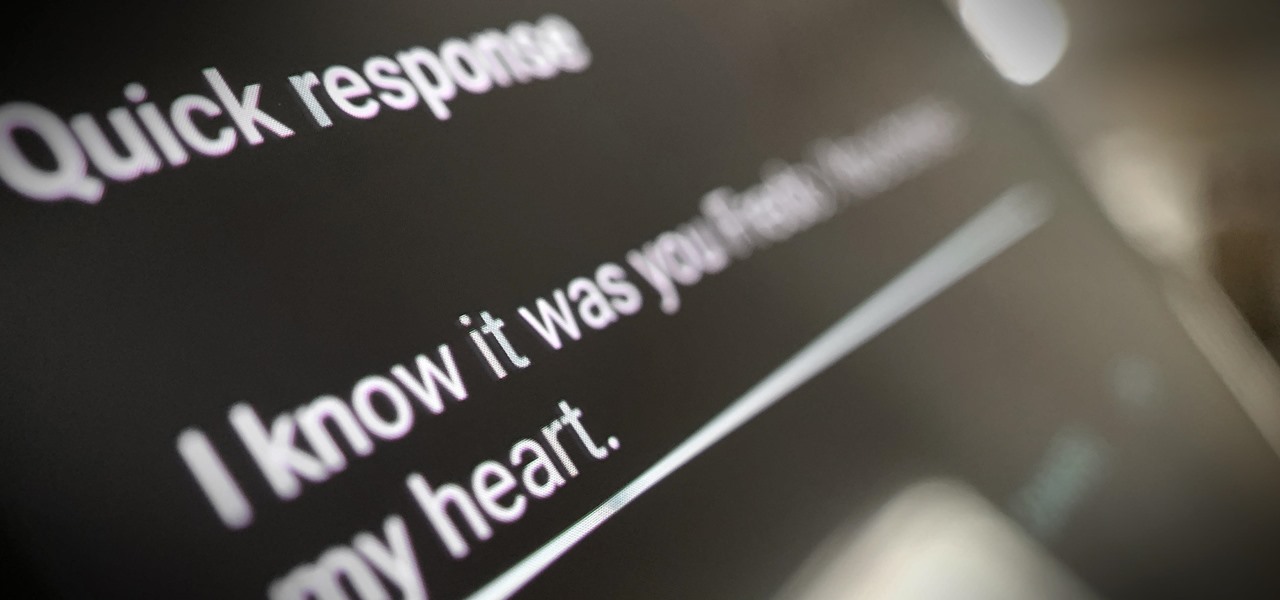
Google is making its Phone app, the default dialer for Pixel and Android One devices, available to many other smartphones via the Play Store. If you're enticed to replace your factory-installed dialer to take advantage of the spam-filtering capabilities, you don't want to miss out on other features like the ability to customize canned responses for declining calls.

To be honest, the Mail app for iPhone had always been somewhat forgettable. It lacked many of the features that made third-party clients like Spark and Edison better, but with iOS 13, the gap between Mail and its competitors is much smaller. Apple updated the layout and added many new features to its native emailing app, and that may be just enough to get you to switch back.

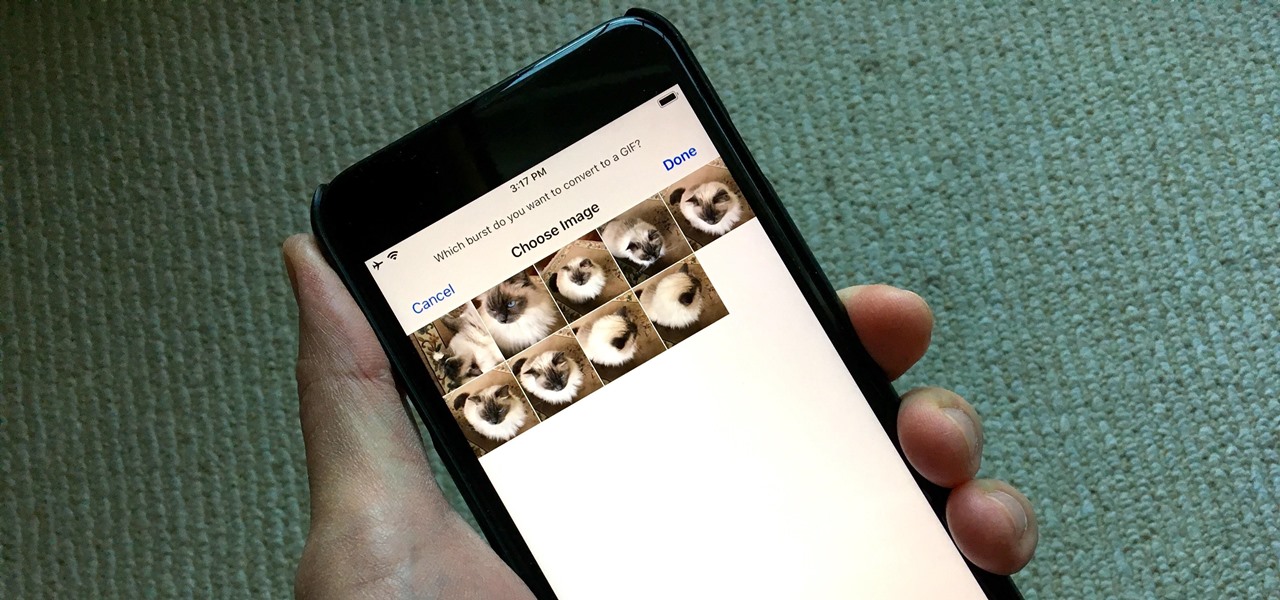
Creating GIFs of your own burst images has been possible for a while with third-party iOS apps, some of which cost money or include in-app purchases to utilize the full potential. Fortunately, with Shortcuts, Apple's automation workflow app, there's finally a native way to achieve this without spending any cash.

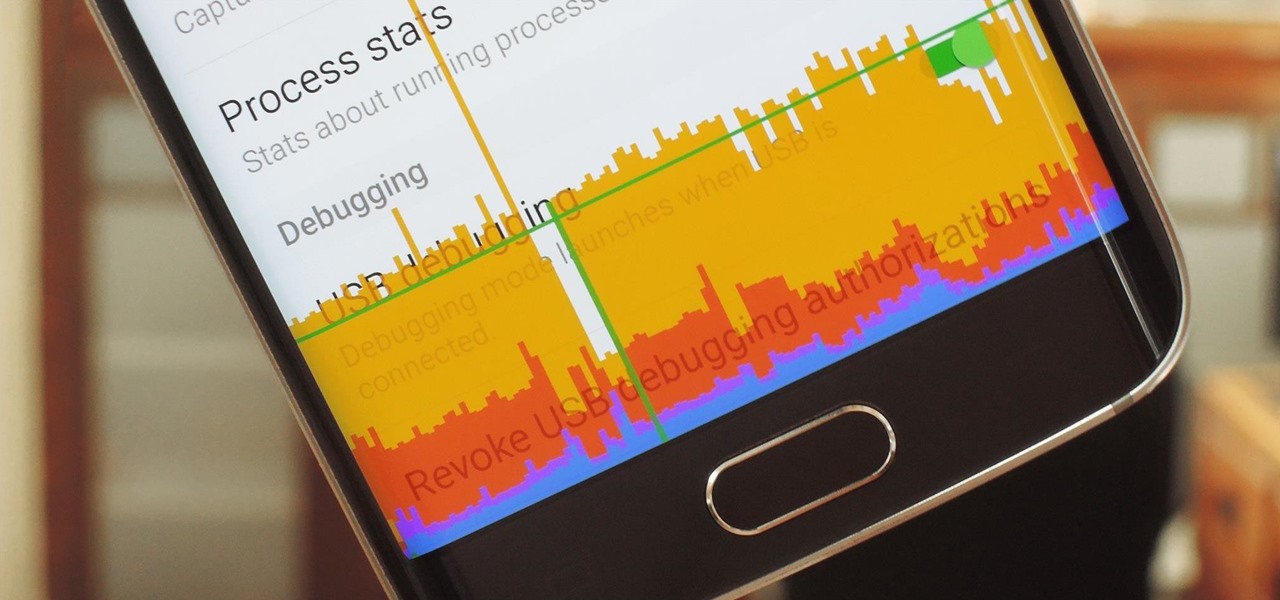
In case you didn't know, Android has an awesome hidden settings menu called "Developer options" that contains a lot of advanced and unique features. If you've ever come across this menu before, chances are you just dipped in for a minute so that you could enable USB debugging and use ADB features.

Probably SSH is not as clean and fast as other useful tools like netcat, but it has some features which are very useful, and when you'll need them, here's how to behave with that huge amount of computers all over your house.

Your iPhone's built-in Voice Memos app is a great way to record the audio around you, whether it be conversations, lectures, meetings, interviews, discussions, chitchat, gossip, or other kinds of talks. But if your goal is to record audio on the down-low without being noticed, you'll need to know the hidden shortcut.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

With much of the hype centered around its powerful cameras, it's easy to overlook the equally impressive audio capabilities of the Galaxy S9. After all, the S9 and S9+ are the first Samsung flagships to feature AKG-tuned stereo speakers, and that's not even mentioning all the software enhancements that help deliver rich, immersive sound in several different listening situations.

Welcome back, my hacker novitiates! In an earlier Linux Basics tutorial, I had demonstrated the basics of the Apache web server. Since Apache is the world's most widely used web server on the Internet (as of July 2015, Apache was 38%, IIS was 26%, and Nginx is 15%), the more you know about it and understand it, the more success you are likely to have hacking it.

Your phone's keyboard is one of the most commonly used apps. Whether you're typing out status updates, sending private messages, or just bombarding everyone in sight with as many emoji as you possibly can, you probably couldn't get by without a good keyboard app.

The Google Phone app is one of the best dialers for Android today, especially with all of the unique and exciting features it brings to the table. Unfortunately, without owning a Pixel phone, you are unable to officially download the app, making a modified version your only option. However, this version of Google Phone is missing a few key features, such as spam protection and business search.

When it comes to traveling from one location to another with the aide of your iPhone, ensuring your navigation app works as it should keeps you one step ahead of potential hassles. One feature often overlooked is audio settings, and while having no voice prompts is easy enough to ignore while walking or commuting, having no sound to guide you while driving can spell disaster.

Welcome back, my hackers apprentices! To own a network and retrieve the key data, we only need to find ONE weak link in the network. It makes little sense to beat our heads against heavily fortified systems like the file and database server when we can take advantage of the biggest weak link of all—humans.