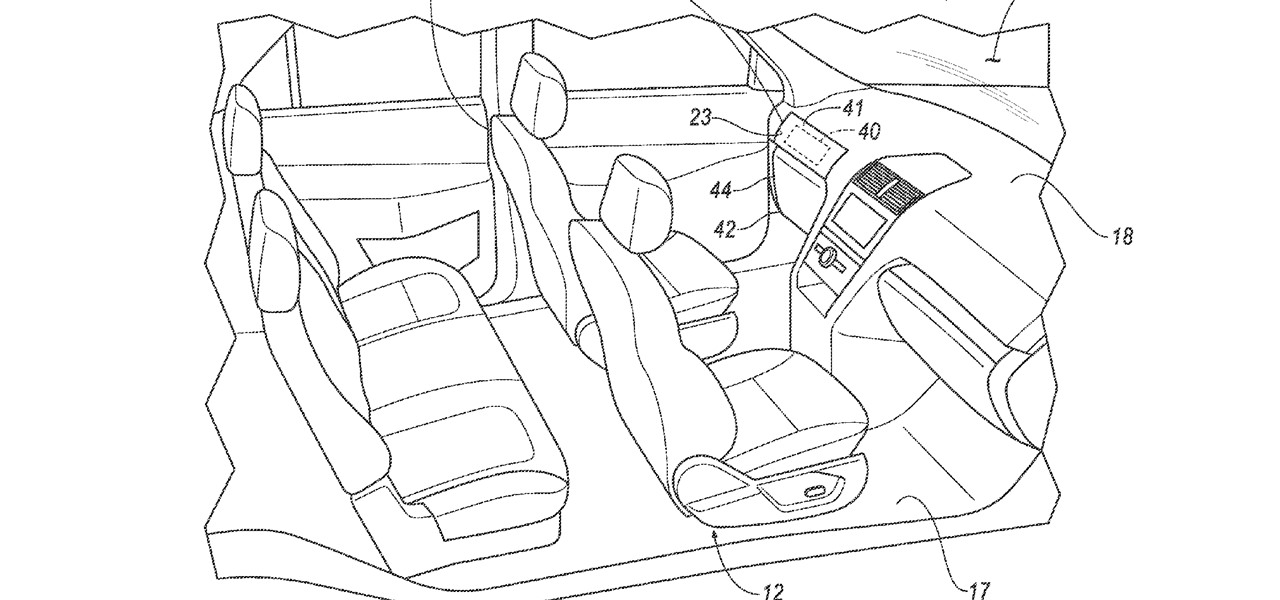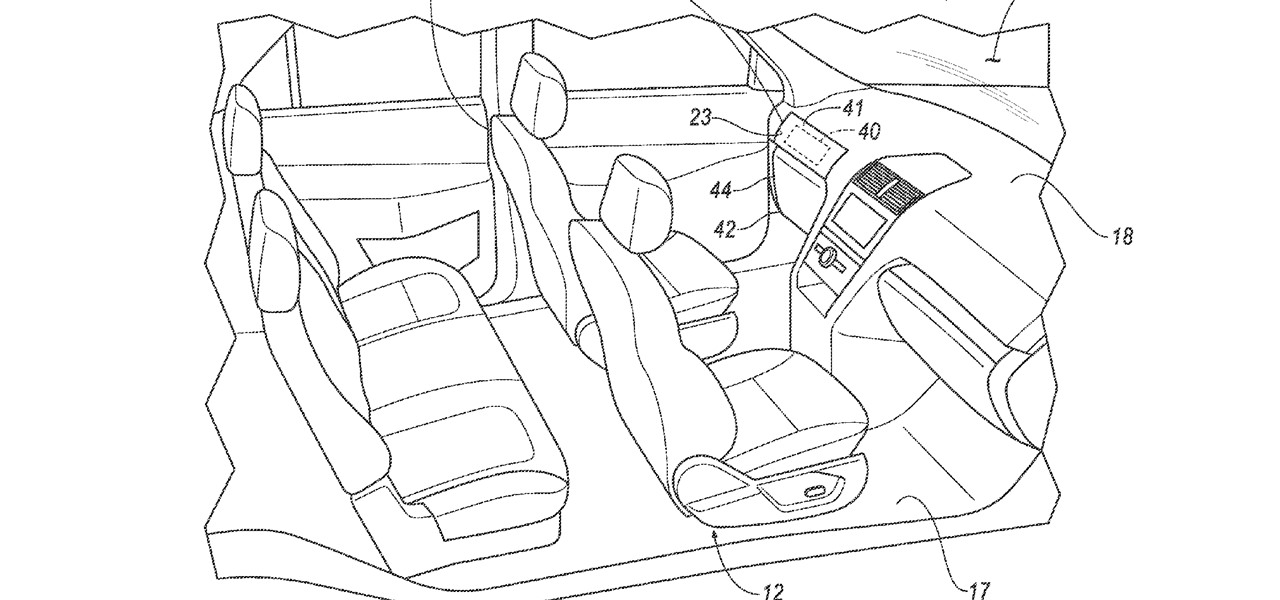
Google largely helped to pioneer the concept of a steering wheel- and pedal-free self-driving experience when it began testing its Firefly pod-like vehicles a few years ago.
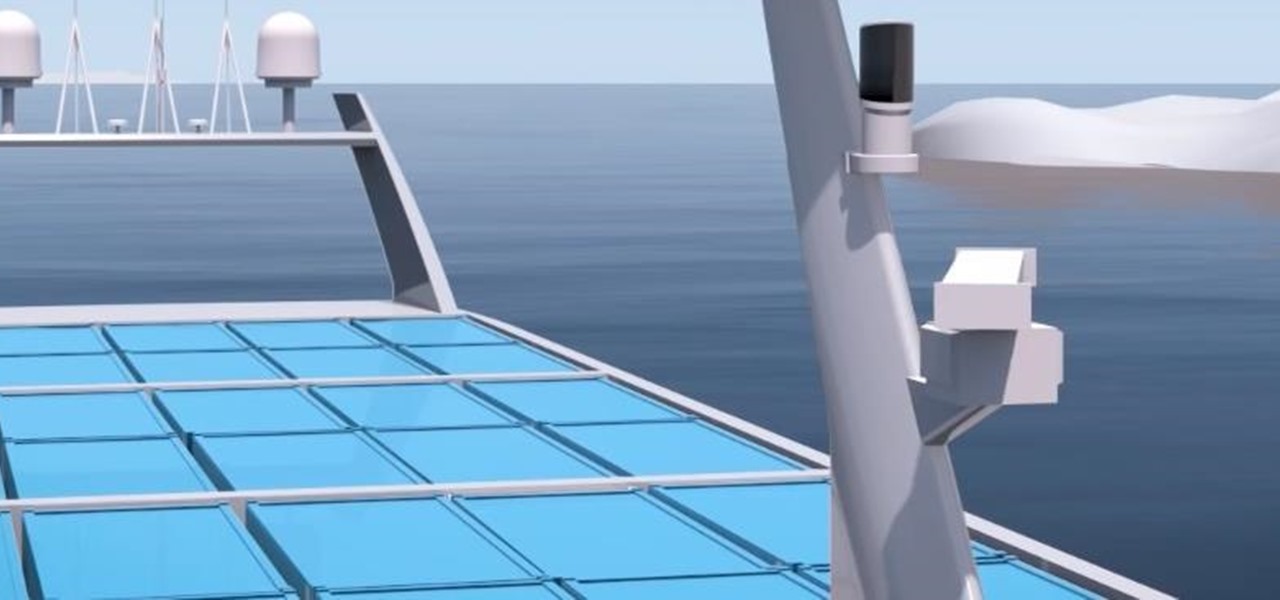
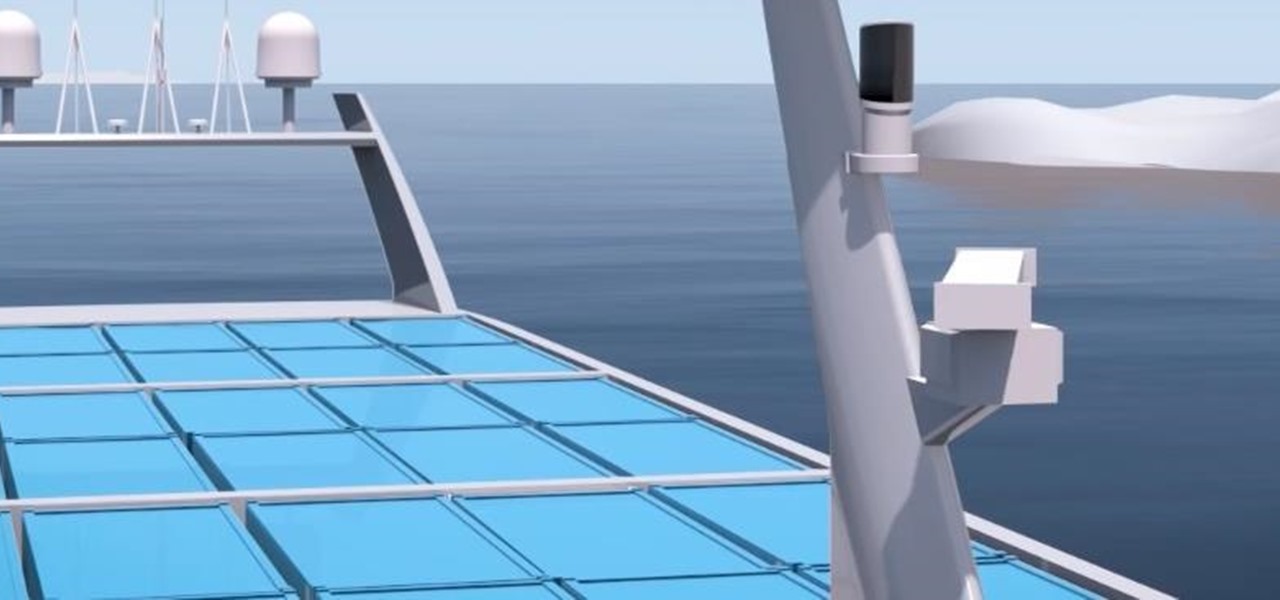
A Norwegian carrier's launch of a pilotless container ship next year could lead the way to a new era in sea transportation and shipping if successful.

Research group OpenAI, a research institute co-founded by Tesla CEO Elon Musk, says it is possible to trick driverless cars' neural networks into mistaking images for something else.

The Operative Framework is a powerful Python-based open-source intelligence (OSINT) tool that can be used to find domains registered by the same email address, as well as many other investigative functions. This reconnaissance tool provides insight about your target through examining relationships in the domains they own.

A Norwegian shipping company says it will launch an unmanned container ship within four years, as the shipping industry begins to apply driverless technology to commercial sea transportation.
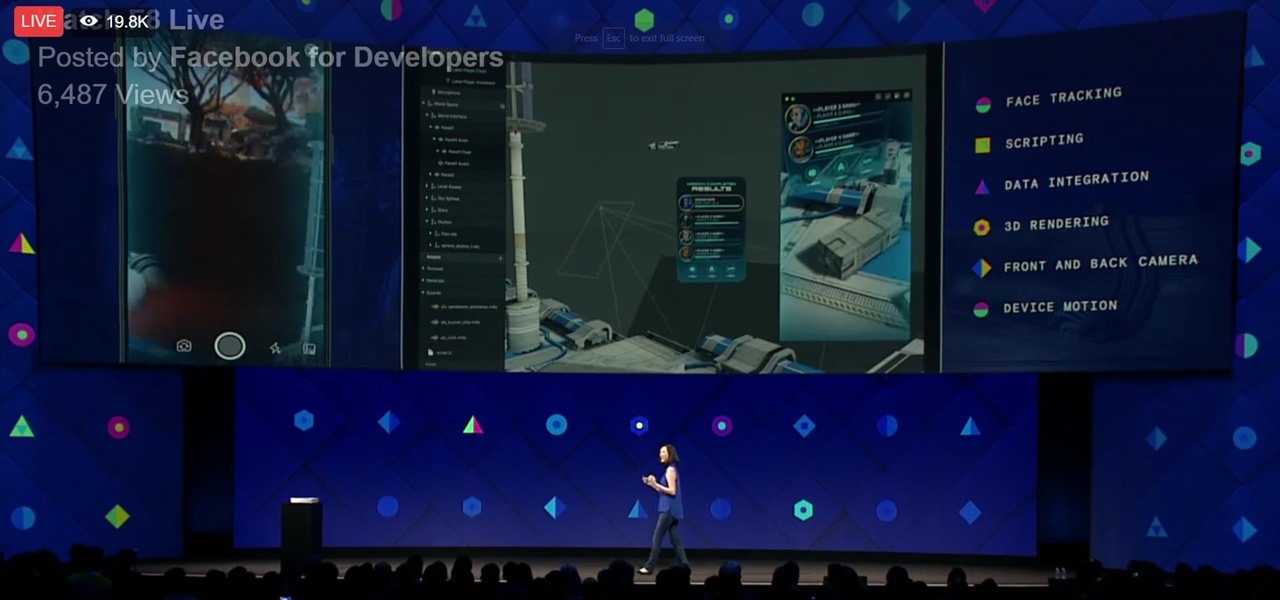
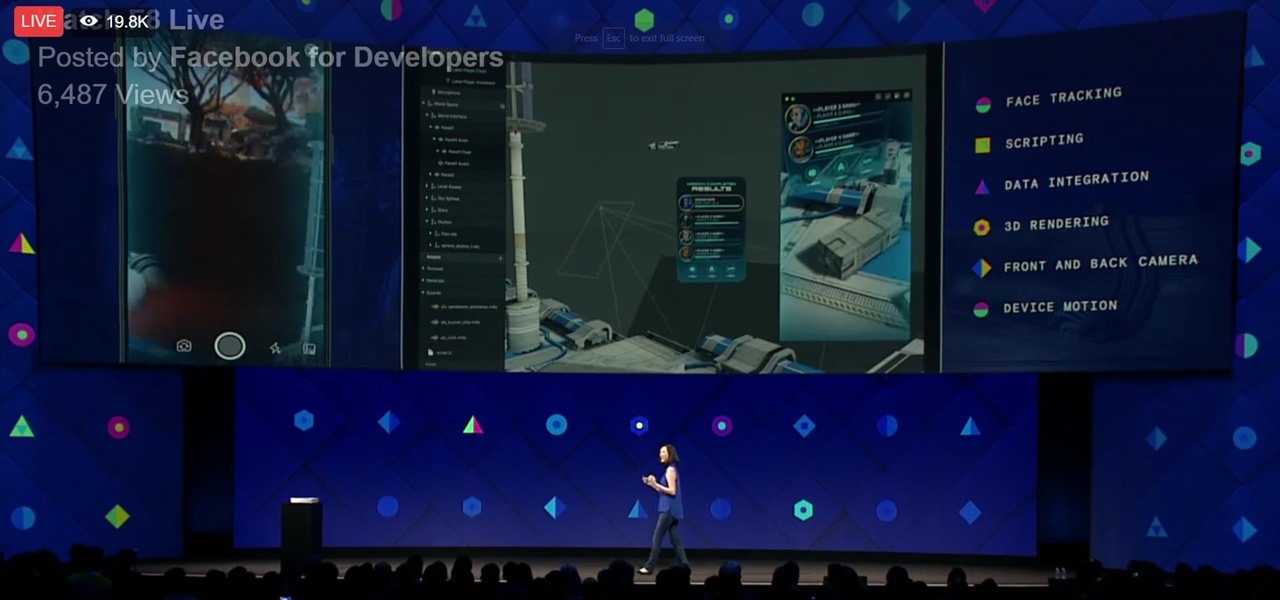
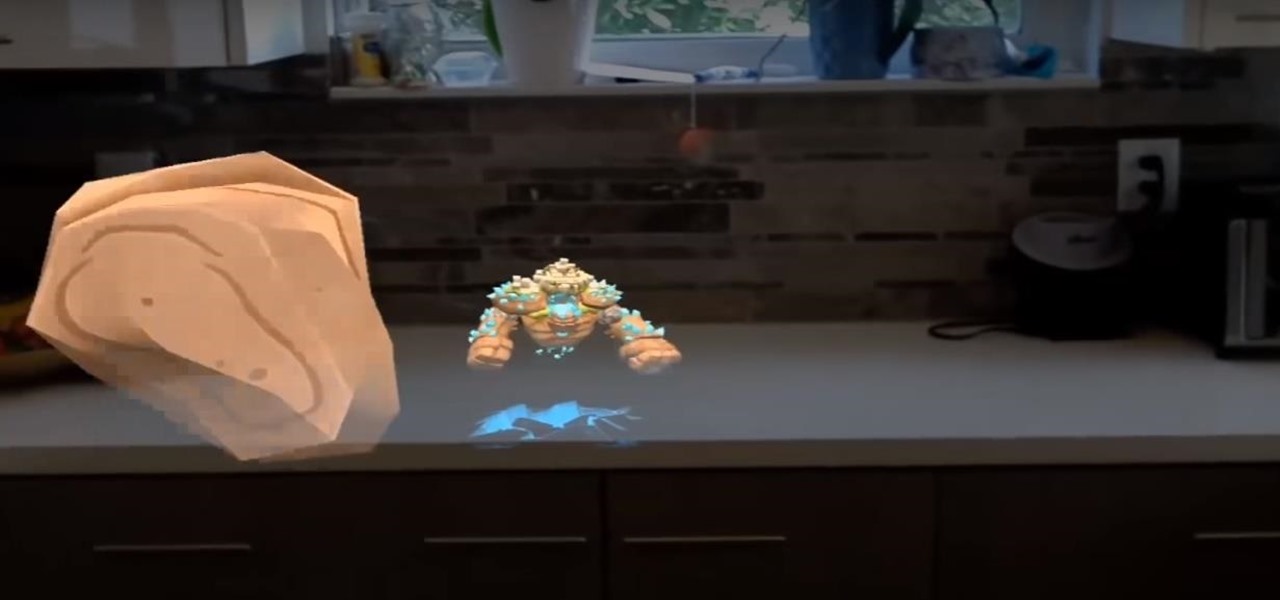
During his opening address on April 18 at F8, Facebook's developer conference, CEO Mark Zuckerberg launched the company's augmented reality platform centered on artificial intelligence-powered cameras.

It seems nowadays there's no limit to what type of companies are looking to invest in augmented reality. Given both the positive outlook on the future of AR, and its reported benefits for efficiency in employees, this makes sense. Safran, an international corporation with three main sectors—aerospace, defense, and security—is one such company taking the plunge into incorporating AR in their business.

You can get eggs and high-quality compost from backyard chickens—but you can also get Salmonella.

Ideally, wine would stay as perfect and delicious as the day it was first uncorked forever. But, thanks to a pesky process called oxidation, re-corked wine (no matter how you do it) pales in comparison to a fresh's bottles original magic.

This tutorial is one technique to use the full functionality of your Pi. The small size makes it ideal for inside hacks, but still has the capabilities of a average desktop or computer. I should mention that a tutorial that OTW has done, but I'm gonna take it a step further. OTW made a brilliant article, but only touched on the surface of the possibilities. I hope this article will both show you many the possibilities and also allow you to start causing havoc, but I'm planning on making this ...

I found this article a while back and I found it underneath a bunch of junk. Anyway, it's a article on 9 notorious hacker including Walter O'Brien (You know the T.V. show Scorpion? Well that's him). Not to mention the weird names:

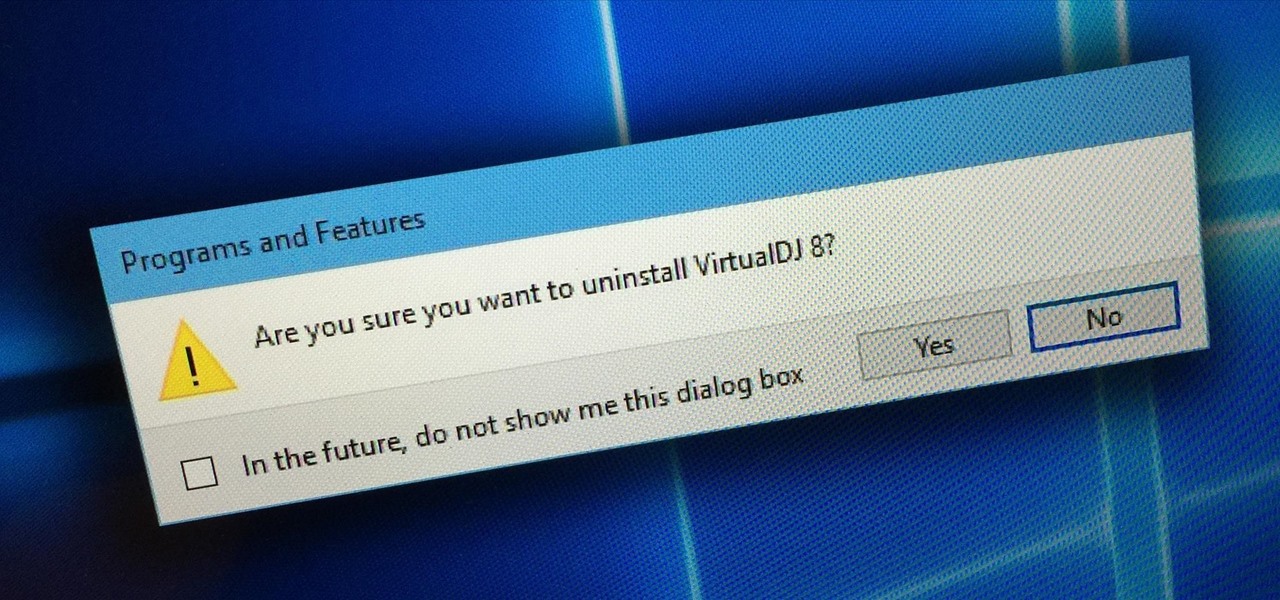
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

This past weekend, one of the most notorious hacker organizations in the world, Hacking Team, was hacked by some unknown organization. The Hacking Team is an Italian company that sells it software and services to companies and governments (yes, my rookie hackers, there are legitimate companies who sell their services to governments—Vupen, being one of the most famous and lucrative).

Throwing a party means making sure everyone has fun, but that pursuit can quickly get out-of-hand. Before you know it, you're once laid back get-together has received so many RSVPs that it becomes obvious you're throwing the party of the century. With an over-abundance of beer and an inflated guest list, your newly-formed epic reputation must live up to the hype.

Brought to you by Tomcat. Falling snow, warm fireplace, delicious hot cocoa, quiet reading time, mouse. Quick quiz - which one is not like the other? Nothing can ruin a perfectly cozy afternoon in your home like a pest on the loose. With dropping temperatures, you may have some unwelcome residents, like mice, looking for shelter from the cold.

Link shorteners like TinyURL and Bitly are great for Twitter (or anytime you're limited on space), but they're also great for hackers. It's easy to hide a malicious link in an innocent-looking shortened URL, which increases the chances that people will click on it.

Playing in the paint… what does it mean exactly? Inside the paint means close up to the rim, in the area below the hoop that is actually painted a different color than the rest of the basketball court. This video will show young players and coaches how to effectively play inside the paint, with drills for layups, rebounding and more. This is the roughest and most dangerous part of the game, so knowing the best defense and offense is key to winning.

In this sports how-to video, Farmington HS boys basketball coach Shane Wyandt and team demonstrate the shell 5 defense drill. The five man shell drill is an effective way to train defensively for basketball. Follow along with this video demonstration and learn the shell five drill.

Learn how to play "Now Or Never" from High School Musical 3, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:

The setter in volleyball is one of the most important positions because they set up the spike which, in many cases, ends in a point if the set is done right. Watch these setting tips in this sports video tutorial.

The volleyball middle hitter attacks from both in front of the setter and sliding behind the setter. Learn how to be a middle hitter in this volleyball video tutorial.

Perfect body position allows the volleyball player to execute effective techniques on both offense and defense. Learn how to get into perfect body position in this volleyball video tutorial.

Tackling in field hockey is essential to having a strong defense, and there are subtleties that a defender must know when attempting to tackle without being penalized. Learn how to tackle in field hockey in this video tutorial.

In these videos, you can see how 3 minute chess blitz games are for the greats, because if you're a beginner, you spend too much time analyzing the moves, when they should come almost as second nature. See some common follies in rushed games, and see some good defenses, here and there.

The still-unfolding story of China's Nreal augmented reality startup continues to develop, with each turn uncovering another unexpected wrinkle.

The legal drama surrounding Chinese startup Nreal and Magic Leap continues, and now we finally have an update.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

Months after Next Reality broke the story surrounding the financial troubles at Meta Company, there's a new update in the company's ongoing patent lawsuit.

Augmented reality gaming company Niantic Labs is now instigating conflicts between Pokémon GO players, but it's not as bad as it sounds.

The app that Lego demoed at this year's iPhone launch event is now available in the App Store, and it showcases several new capabilities available in ARKit 2.0.

There is no shortage of defenses against cross-site scripting (XSS) since it is so prevalent on the web today. Filters are one of the most common implementations used to prevent this type of attack, usually configured as a blacklist of known bad expressions or based on regex evaluation. But there is hope with a wide variety of techniques that can be used to defeat these filters.

Locating and abusing files containing unsafe permissions is an easy and surefire way to elevate shell privileges on a backdoored macOS device. This time around, we'll be more aggressive and attempt to phish a user's login password by prompting a convincing popup message merely asking the target for their password.

Recently, a user on Reddit complained that their Snapchat account had been temporarily banned because Snapchat noticed the user's account was going through a third-party service. In reality, the account in question was running on a jailbroken iPhone, and it was far from the first to be banned by the messaging app.

As it prepares to ship its first product by the end of the summer, Magic Leap has managed to impress yet another high-profile investor in telecommunications giant AT&T.

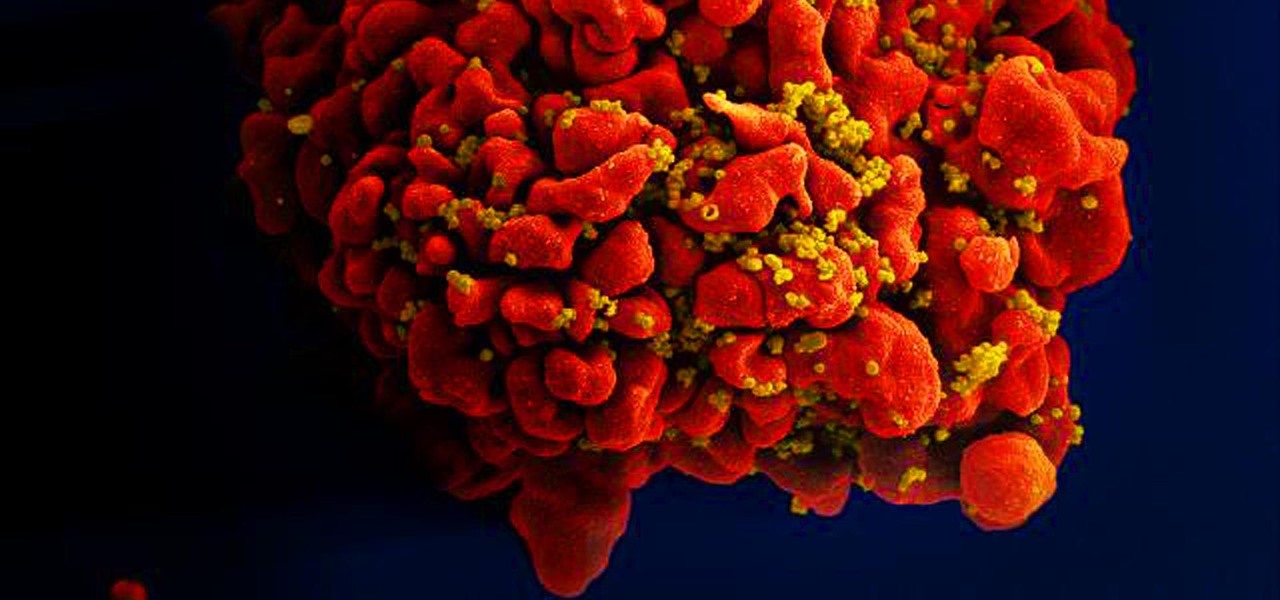
Results of an early-stage clinical trial of an HIV vaccine could mean a hoped-for breakthrough in the battle against AIDS.

During the millions of years they've been on earth horseshoe crabs have developed a trick that can save our lives even now — and may be especially useful in the fight against healthcare-associated infections.

Tesla founder and CEO Elon Musk offered some insight into how hackers might seek to turn driverless cars into zombie fleets, but remained upbeat about what can be done about it.

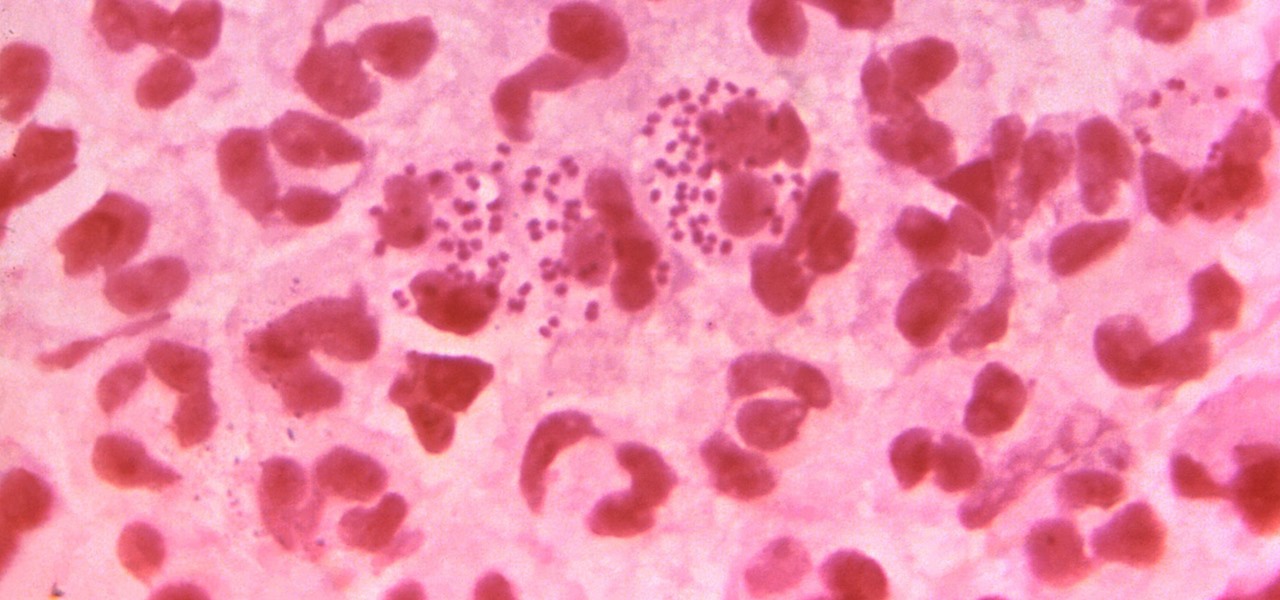
In the race to outsmart "untreatable" antibiotic-resistant gonorrhea, one of the three new treatments on the track is about to enter Phase 3 clinical trials. Hopefully, it'll be widely accessible sooner rather than later, for the 78 million people who are diagnosed with gonorrhea each year.

Tell the truth. The bat picture creeps you out. You are not alone. But in reality, bats truly are some of our best friends. They gobble thousands of disease-spreading bugs a night. But they also carry viruses that can be deadly to humans. So, bats — friend or foe?

Fans of rhythm tap games and traditional one-on-one fighters finally have something to bring them closer together. DuelBeats, a fighting game that lets you perform moves by tapping to the beat of a song, has been released as a soft launch for both iOS and Android in New Zealand, Australia, and Singapore. Just because the game is exclusive to those regions doesn't mean we can't try it out for ourselves, and with a little hackery, it's entirely possible to do so.