Secure Shell is one of the most common network protocols, typically used to manage remote machines through an encrypted connection. However, SSH is prone to password brute-forcing. Key-based authentication is much more secure, and private keys can even be encrypted for additional security. But even that isn't bulletproof since SSH private key passwords can be cracked using John the Ripper.
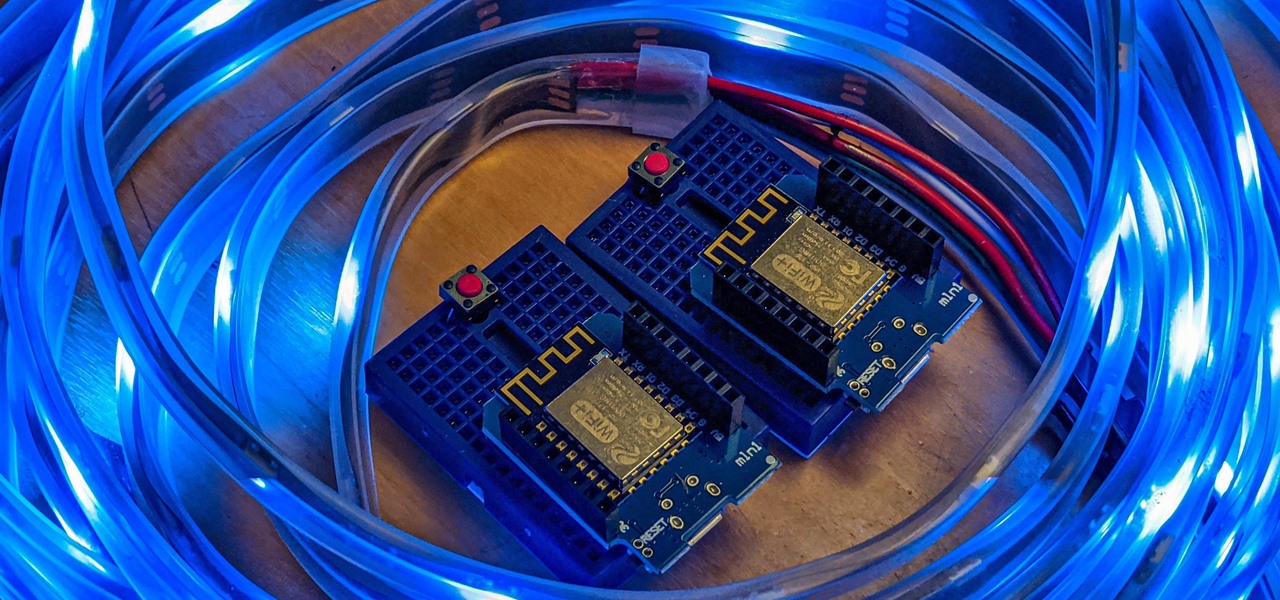
Individually addressable LEDs, also commonly called "NeoPixels" after the popular Adafruit product, are a bright and colorful way to get started with basic Python programming. With an inexpensive ESP8266 or ESP32 microcontroller, it's easy to get started programming your own holiday lighting animations on a string of NeoPixels with beginner-friendly MicroPython!
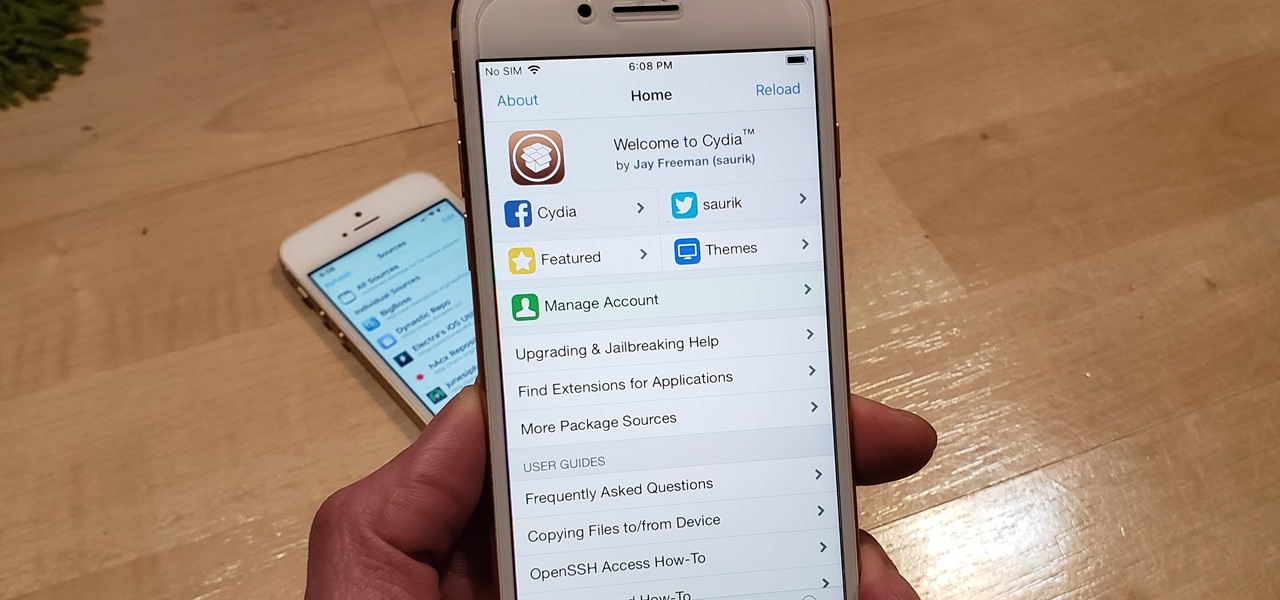
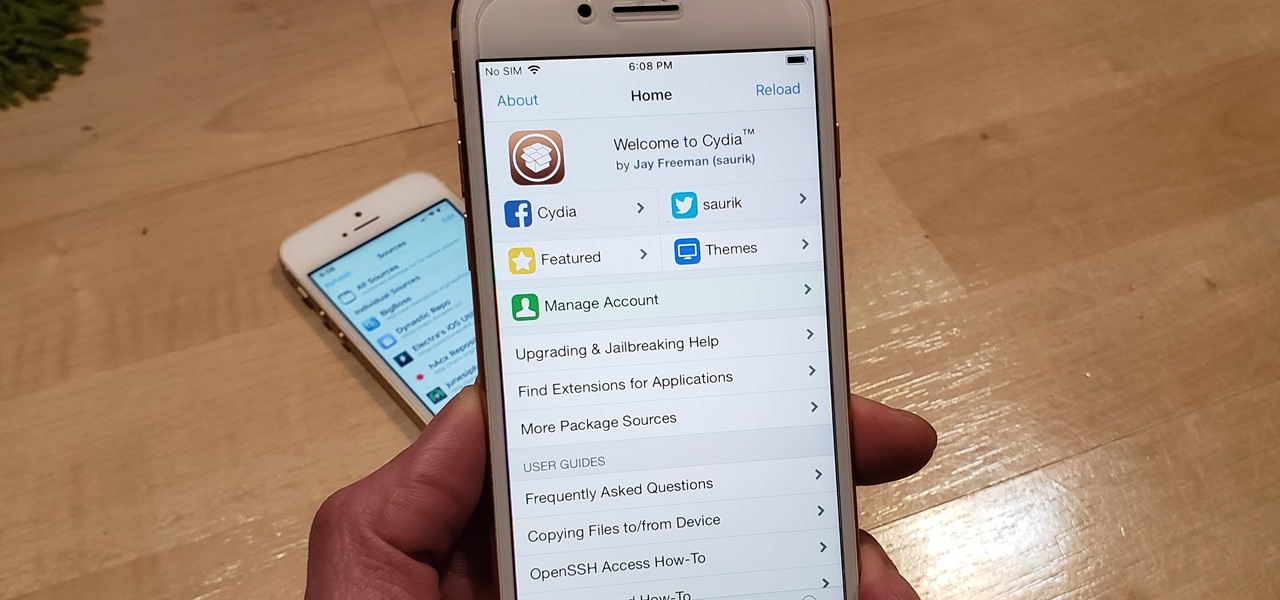
With Unc0ver, Pwn20wnd was the first to jailbreak an iPhone and iPad running iOS 12 versions. While it initially couldn't work on all devices, it's an entirely different story now. Unc0ver currently works up to iOS 13.5 for most A7 to A13-powered devices. Plus, Chimera, another jailbreak tool, supports a similar range of models on iOS 12 to 12.3 and iOS 12.4.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.

A PirateBox creates a network that allows users to communicate wirelessly, connecting smartphones and laptops even when surrounding infrastructure has been disabled on purpose or destroyed in a disaster. Using a Raspberry Pi, we will make a wireless offline server that hosts files and a chat room as an educational database, a discreet local chat room, or a dead-drop file server.

Besside-ng is the hidden gem of the Aircrack-ng suite of Wi-Fi hacking tools. When run with a wireless network adapter capable of packet injection, Besside-ng can harvest WPA handshakes from any network with an active user — and crack WEP passwords outright. Unlike many tools, it requires no special dependencies and can be run via SSH, making it easy to deploy remotely.

Android comprises an entire ecosystem of apps, games, functions, and features, so it would only make sense that it has its own lexicon. Words, phrases, and acronyms that didn't exist ten years ago are now used in an off-the-cuff style by developers and support technicians across the web.

Double clutching was born out of necessity to help ease gear transitions and prevent clutch wear. They've since changed the transmission and the double clutch technique is now reserved for a more deliberate driver looking to add finesse to his acceleration.

The famed chessmaster Capablanca was once asked how many moves ahead he saw when playing a game of chess. His answer? "I see only one move ahead, but it is ALWAYS the right move."

Doing this workout from Men's Health will increase flexbility and strength in your rotator cuffs. Make sure to execute technical precision to avoid injury.

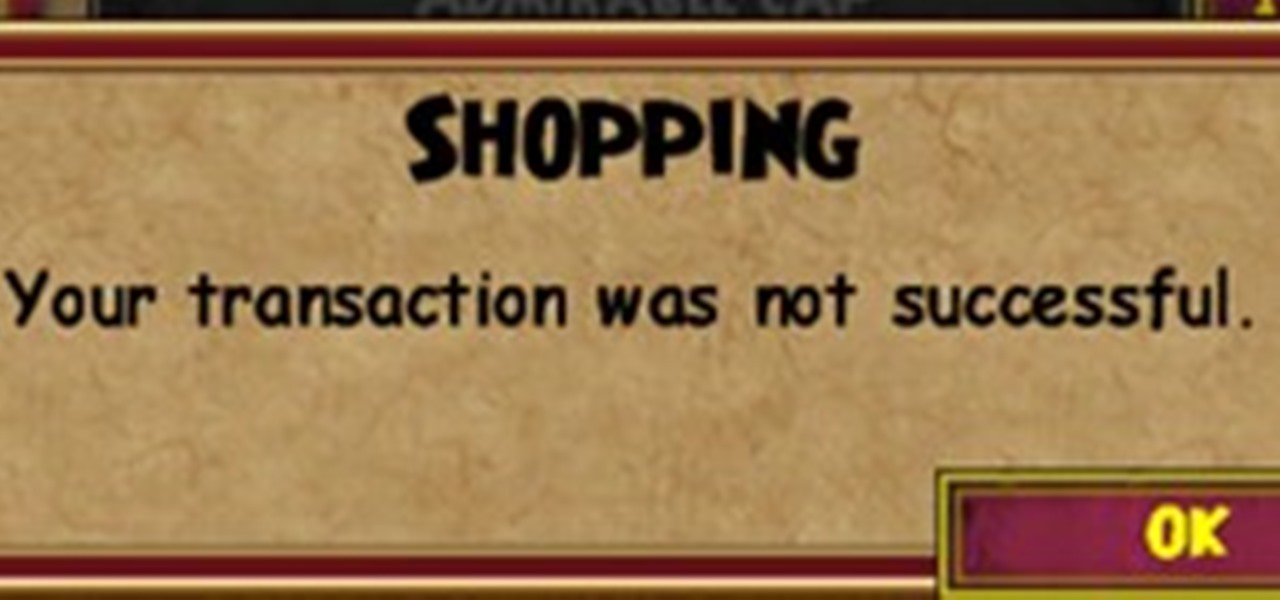
So many of you like to save up your gold coins to buy things like castles, treasure cards and clothing. But sometimes when you buy something, an error message pops up. One of them is this extremely annoying one: "Transaction was not successful."This error happens mostly when buying clothes. Let's say you want to buy a robe, but it is too expensive. You change the color of the robe to brown, yellow or white and try to buy it. When you click Buy, the error pops up. You switch realms. No differe...

This article will teach you how to make an error similar to this one (also by me). This error message though, is a yes or no question. Clicking yes and no will give different results. Like the previous error message, this is 100% harmless.

Apple's 9.3.2 update for iOS has been completely destroying some users' iPad Pros, and there's only one way to fix it.

i keep giving detailed descriptions but i cannot copy and paste on this website and it keeps having errors and kicks me out! about to pull some hair out because of this.to view my true description here is a link:http://i324.photobucket.com/albums/k337/sk8rhunter/descriptionjackass-1.png

This article will show how to make a simple, fake computer error message. These message boxes are 100% harmless, and make for funny pranks. They will display any text you want them to.

Learn how to tell your boss that you've made a major mistake. This narrated video with step-by-step subtitles discusses the most effective means of softening the consequences of a potentially fatal error. Also discussed are potential actions to use after the problem has been acknowledged. Suggestions include: acting quickly, confessing, and proposing viable solutions to the problem you caused. Tell your boss you made a major mistake.

I've come across a few very stubborn Xbox consoles in my day. A previous Null Byte demonstrated how to fix the Xbox with just eight pennies and some electrical tape. But if you've got one of those hell-born boxes that just refuses to be fixed in any way, shape, or form, there is always one last ditch approach. I'm talking about the infamous "towel trick". It works over 90% of the time, from my personal experience. Though, please note: This is only a temporary fix.

There are often requests for the Monkey’s Fist (or Paw) Knot so here it is! Watch this instructional knot tying video to learn how to tie your own perfect monkey's fist boating knot. The key to tying the monkey's fist knot successfully is to have a small ball or core to insert into the knot before tightening it up. The core must match the size of the knot - which is dependent on the size of the rope being used - for the knot to finish right. Some trial and error is to be expected when first t...

Microsoft has had a pretty bad wrap with their Xbox 360 gaming console. Right from the start, the console has suffered a multitude of different hardware failures and design flaws. These problems cause the parts to get too hot and become faulty. I'm sure everyone who's had an Xbox 360 has gotten at least one Red Ring of Death or E74 error.
In this tutorial we will be go over how we can make use of conditionals. In Perl the main conditional is the if statement. The if statement in
Back in Backtrack5 there was a nice GUI addon for the aircrack suite called feedingbottle. I liked it because it simplified easy tasks like fake auth with a click of a button. I was hunting for sources and it seems that all I could find was an ubuntu deb package from 2013. It was a little tricky installing it on a 64-bit system so I thought I would write a quick how to. Feedingbottle is an x86 package so you must install the corresponding libraries. If they are missing you will get a "bash:.....

Need to know how to use your Texas Instruments graphing calculator for your college math or statistics class? You're in luck... watch this video tutorial to see how to determine a regression equation with a TI-83 graphic calculator. That's not all...

Did you just sell your car? Do you know what the next step of your process should be? This video tutorial shows you all the steps you need to do to transfer the title of your car from you to the new owner. Beware of any missteps, or it could cause delays in the transfer of ownership. Make sure all information is accurate, because any errors that are erased on the title will void the document. Transfer the title of your car.
The US judge handling the Megaupload case noted today that it may never be tried due to a procedural error, a comment that has sparked the anger of Megaupload’s founder. Kim Dotcom is furious with the US Government for destroying his businesses and rendering hundreds of people unemployed. According to Dotcom the case is the result of “corruption on the highest political level, serving the interests of the copyright extremists in Hollywood.”

Don Williamson shared his real-time web-based code editor & interpreter for the DCPU-16 Virtual Machine. It makes nice use of the canvas tag for a beautiful blue console, features a real-time recompile as you type, and thanks to some custom DCPU-16 support for Marijn Haverbeke's wonderful CodeMirror syntax highlighting textarea library, it'll give you real-time error feedback as you type.

By now, most of you have updated to the new Xbox look. Just as expected, it's got some great new features. The dashboard looks great and Bing integration is awesome, but I'm very unhappy about the new Netflix interface. It's awkward, slow, and half of the items don't even load correctly. I can't even play some movies. And the instant play feature is kind of annoying. When I first chose a video, I was hoping when it instantly started playing that it was a trailer, à la Zune. Alas, no.

I spent the holiday weekend becoming fluent in the basics of modular origami. With practice, you can churn out the below models surprisingly quickly.
This place lets you post profiles WITH LINKS, images, shows, resources, all free. Best part...RANKS HIGH ON GOOGLE! worth the hassle of setting up a profile.

While a lot of internet threats are rather over-hyped, there are some serious things to be cautious of when going online. Probably the biggest risk to the average internet user is malicious software. Commonly knows as "malware," this term refers to any program that exists solely to do harm. This may include damaging your computer or accessing your data without you knowing. Viruses, trojans, and spyware are all forms of malware. Now, malware can seriously mess up your system, and the idea of s...

The monochrome layout on Samsung's default keyboard can make it a little hard to view keys. Fortunately, there's a setting you can enable that makes your keyboard significantly easier to view and type on.
While following a tutorial on python recon tools, I found a new way to access the command prompt on a school network. While there are other ways of bypassing security, it's nice to learn use Python's OS library.

Who hasn't gone mad trying to fix his/her computer, trying to delete all of the harmful software? It may not be funny with a real virus, but a fake one is. Or course, you can make a simple virus just with Notepad. There's no need to download applications to fool others; in less than 1 minute you will learn how to create a fake virus to scare friends, family or even teachers! Why not?

(Difficulty Level: from Newby to Expert) Digital cameras can produce freaky sharp images—it’s one thing that sets them apart from film cameras. A DSLR doesn’t have grain, it has noise—and that sounds a lot less charming for a reason. If you shoot at a low ISO, high f-stop and fast shutter speed, you can wind up with a super sharp image that might look great even on a billboard. But sometimes, sharp isn’t everything.

Building Material Request Links for Brick, Nail, Wooden Board Update: Watering Can Request

Free Tree Gift Request Links With the new orchards and tree mastery system everyone is looking for more trees! As wishlist requests often end up with errors, I've created this list that will provide links you can put your ID into allowing people to send you the item without getting the "gifterror=notfound" message.

Mac owners— life just got a little easier. No longer do you have to wait in line for the newest version of iLife. No more searching Amazon or eBay for the best price on Aperture. And no more Angry Birds on your mobile device's small touchscreen!

Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying various SQL injection vectors over and over. This is especially so if they are using an automated framework like sqlmap that can spam a ton of requests in a short time. More often than not, the access logs are what most amate...