The road to becoming a skilled white hat is paved with many milestones, one of those being learning how to perform a simple Nmap scan. A little further down that road lies more advanced scanning, along with utilizing a powerful feature of Nmap called the Nmap Scripting Engine. Even further down the road is learning how to modify and write scripts for NSE, which is what we'll be doing today.

Confirming a previous report from last week, Qualcomm announced its Snapdragon X1 platform designed for augmented and virtual reality devices during an event at the Augmented World Expo in Santa Clara on Tuesday, with Meta and Vuzix among the first manufacturers to adopt it.
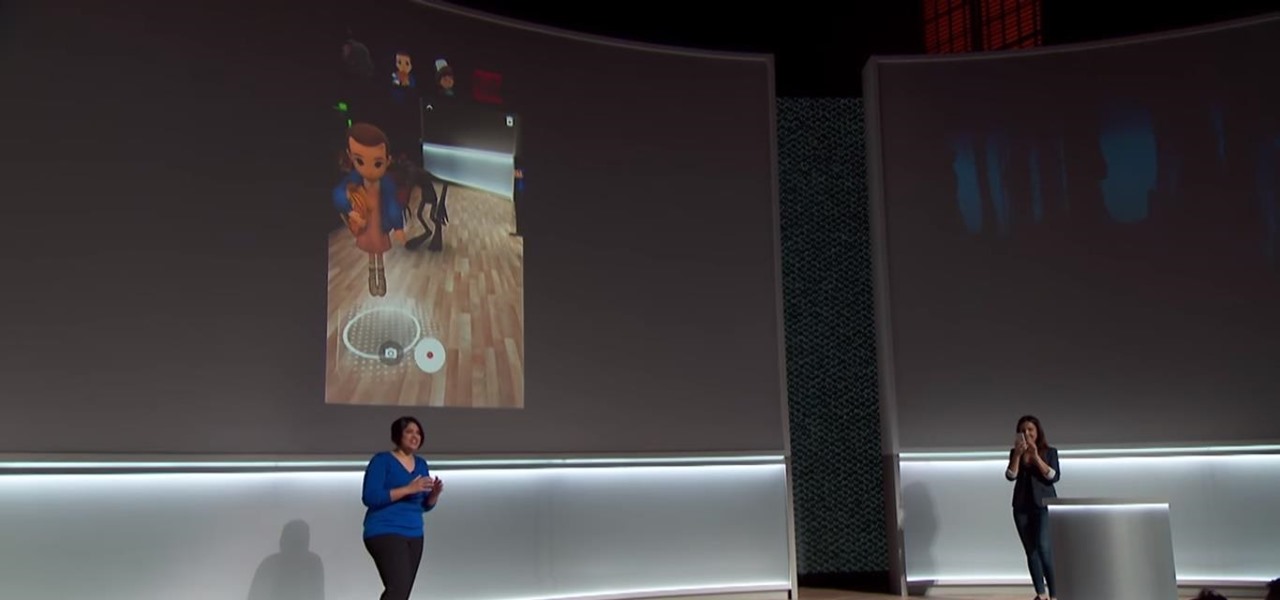
Clearly, the next big battlefield for tech gamesmanship between Apple and Google will be augmented reality.

Avegant Corporation has begun shipping display development kits based on its light field technology that other companies can use in their augmented and mixed reality devices.

Delphi Automotive PLC has announced it is partnering with Transdev Group to develop on-demand driverless transportation systems, a deal that shows promise for autonomous development on a global scale.

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.

Chinese search engine giant, Baidu, has just announced its own autonomous car platform which is intended to speed up the development of driverless vehicles.

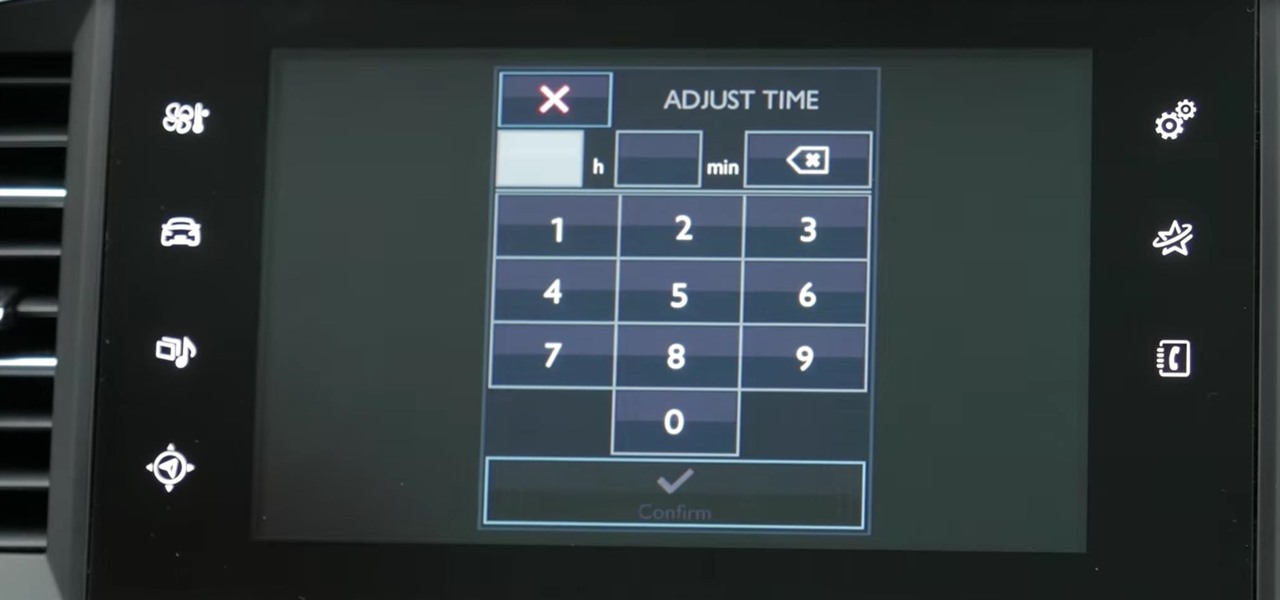
My Next Car how to video series - how to set up the date and time in Peugeot 308 iCockpit (2015, 2016 and 2017 Europe model). This function is accessible in the touch screen i-Cockpit.

Greetings my fellow hackers, In the previous article, I discussed briefly about ransomwares and their devastating capabilities. Devastating in a way that ransomwares are not only known to encrypt files but to also lockout some specific functions of the system and hold it up for a ransom.

Greetings, fellow NBers! Welcome to my sixth iteration of my sorting series. Today, we'll be discussing a personal favorite: Quicksort, or Quick Sort.

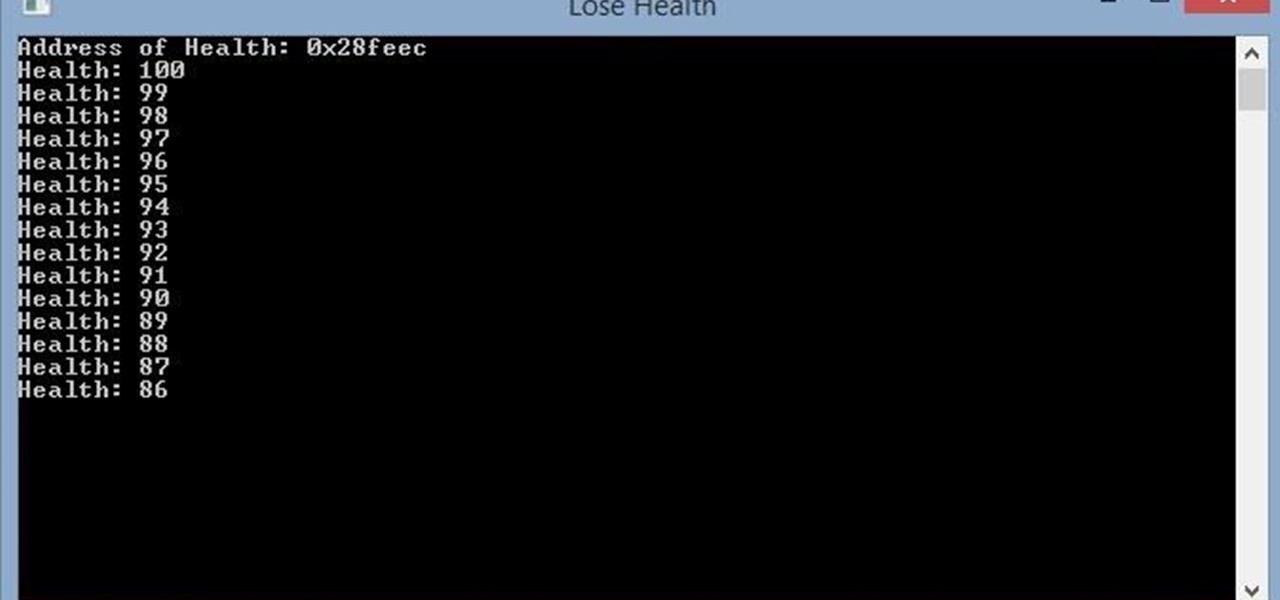
Hello, this is my first post on Null-Byte. This is made for those who have an interest in writing into another processes memory. Why would you want to do this? Who knows, personally I just wanted to mess around with games on my computer(have unlimited health).

Welcome back to a tutorial on malware. We'll be discovering a method to beef up our little trooper. Without further ado, let's jump right in!

Hello readers, in this tutorial, we will be discussing how to perform file operations such as reading and writing.

If your Android device wasn't manufactured by Samsung, chances are it uses on-screen navigation buttons. Colloquially referred to as "Soft keys," these have become commonplace due to their flexibility, as well as the fact that manufacturers don't have to include extra hardware buttons with a propensity to fail.

Hello Hackers/Viewers, It is a new day, and you might be thinking, It is so boring, why not try to be cool with computers in front of my friends? That is why, I have made this tutorial to make fake viruses using notepad to look cool!

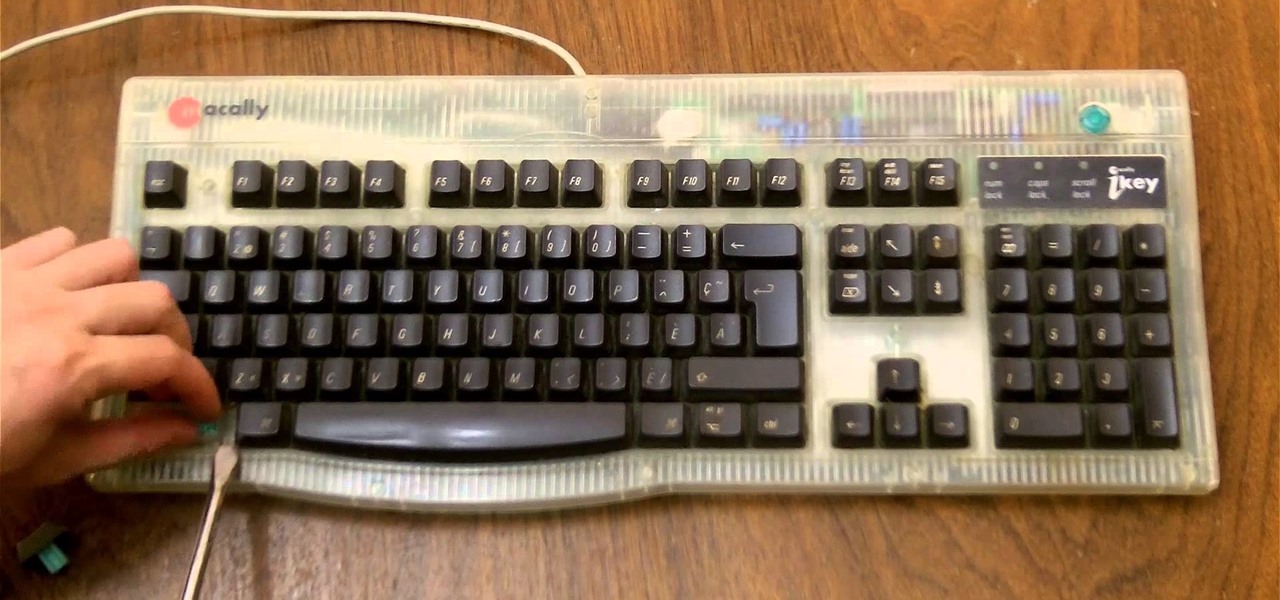
If you need to control a software like Ableton Live while you play guitar then you need a foot switch. In that video I will show you how it is easy to build a foot switch with an old keyboard. Then you will need to configure your software to map the keys to specifics functions like Play, Next, Pause, etc. Enjoy !

What Is IPython? IPython is a richly featured replacement for the standard python interpreter. It offers a wider range of functionality, that the standard

Due to their large size and added screen real estate, Apple included a new feature for the iPhone 6 and 6 Plus known as "Reachability." Essentially, this function makes reaching the top part of the display easier by double-tapping the home key to shift the screen down closer to your thumb.

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

It's pretty logical for your MacBook to sleep when you close its lid, but under certain circumstances, you may not necessarily want this feature to kick in.

Coffee shops are a relaxing place to get work done on your laptop; there's free Wi-Fi, fresh coffee, and people generally leave you alone. Inevitably, those cups of coffee will go straight through you, resulting in a much-needed bathroom break. But while you're attending to your bodily functions, who's attending to your MacBook?

With over 20 million songs, Spotify has become my go-to source for music. I can stream tunes to my desktop or phone, without ever having to worry about storage space being eaten up.

The Samsung Galaxy S4 is a great smartphone, but do you know all the tips and tricks within the handset?

Samsung catches a lot of flak for all of the "bloatware" it preinstalls on its Galaxy line of devices. Many users complain that "TouchWiz," Samsung's custom Android skin, causes lag with its overabundance of features. But some of these features can actually be pretty handy, like Multi-Window Mode or Milk Music.

Silence can therapeutic at times, but unsettling at others. When I'm in bed at night, I need some sort of background or white noise to help me fall asleep. Pure silence just does not do it for me. Whether it's a fan oscillating left to right, or the TV playing, I need background noise to soothe me to sleep.

I regularly listen to music on my Nexus 7 while working or playing my Xbox. It's light and easy to carry around, and has basically become an extension of my body. The only thing that bugs me is having to constantly turn the screen on to pause or change music tracks. Even if I can do it from my lock screen instead of the actual music player app—I don't want to.

No matter how careful or decent you are, there will always be pictures or videos that you want to keep private. They say a picture is worth a thousand words, but if someone were to go through my photo gallery, only one word would be coming out of my mouth—"%@&#!!"

This year in Android has seen a myriad of visual improvements among various apps' user interfaces. From the card swipes of Google Now to the article fade-ins of Circa News, developers have shown that they can strike a beautiful balance between form and function. Check out the following video, complied by redditor hinesh, for some examples.

Get noticed at your next social function or at work with a different and new way to tie your tie. I will be covering amazing and unique knots as well as traditional knots. If you're a man, and you probably are if you're reading this, the odds that you will one day have to ironically wrap a tie around your neck are really high. Like, sky high. It might be for a job interview or for your own wedding, and you'd do well to put one on at the funeral of anyone over the age of 60.

Most of us have some sort of malware scanner or antivirus program on our computers, but what about our smartphones? A lot of people don't realize that computers aren't the only devices that are susceptible to malicious software and apps—they can follow you on your smartphone or tablet, too.

Small studio apartment decorating can be challenging, especially when it comes to creating separate zones and keeping clutter at bay. In this video, you'll see how to create an entryway using Ikea Billy bookcases and natural jute grasscloth. This bookcase room divider serves many functions, including separating the bedroom from the rest of the space, and providing extra storage, crucial to organizing small spaces. And best of all, you can take your bookcase wall with you when you move out!

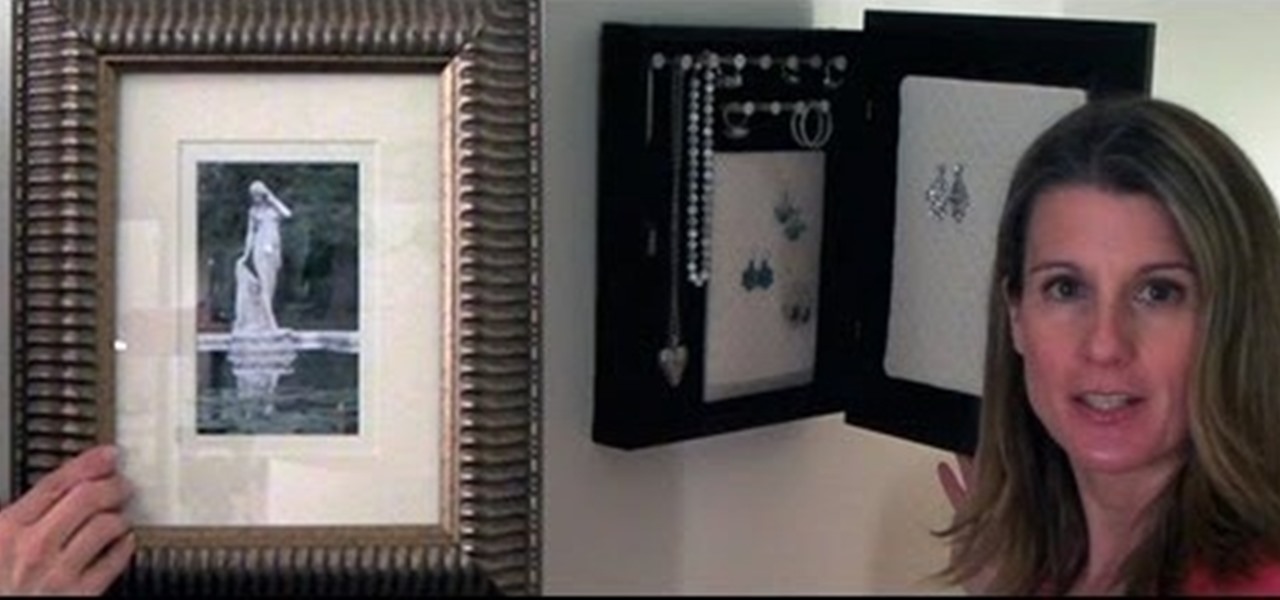
Frustrated with how to organize your jewelry? Why not make your own jewelry organizer! In this episode, learn how to make a frame to transform an ordinary picture frame into a DIY jewelry organizer, using easy to find materials and simple tools. You will be able to store your jewelry on the wall, out of sight, while at the same time displaying a beautiful photo. Having decorative items like this DIY jewelry holder that also function as storage is perfect for small space decorating.

There isn't as much use for old-school four-function calculators anymore since we all have them on our cell phones now. If you've still got one lying around, you can hack it to play recorded sounds, use it to make a metal detector, or turn it into a custom name plate that says anything you want...

With the new Samsung Galaxy Note II, there's a new Multi Window mode that allows users to run two different apps simultaneously on the tablet's screen. This feature works with Samsung and Google apps like Gmail, YouTube, Chrome and Talk.

Programs that run automatically every time you start your computer can slow down your boot time—or just be plain annoying. Many of these programs are rarely used and don't even need to be running for your computer to function properly. So, if you want to disable these auto-run programs and increase your computer's startup speed, here are a few ways you can do it in the new Windows 8.

Making little robots with a LEGO Mindstorms NXT set is already cool, but putting one underwater? Now that's just crazy. That didn't stop this engineer, who built a LEGO submarine that can not only maneuver around his fish tank, but can also be remotely controlled with his Xbox controller. The craft has a sealed battery compartment, exposed Power Functions motors, and features real-time communication between it and a laptop using a NXTbee wireless module.

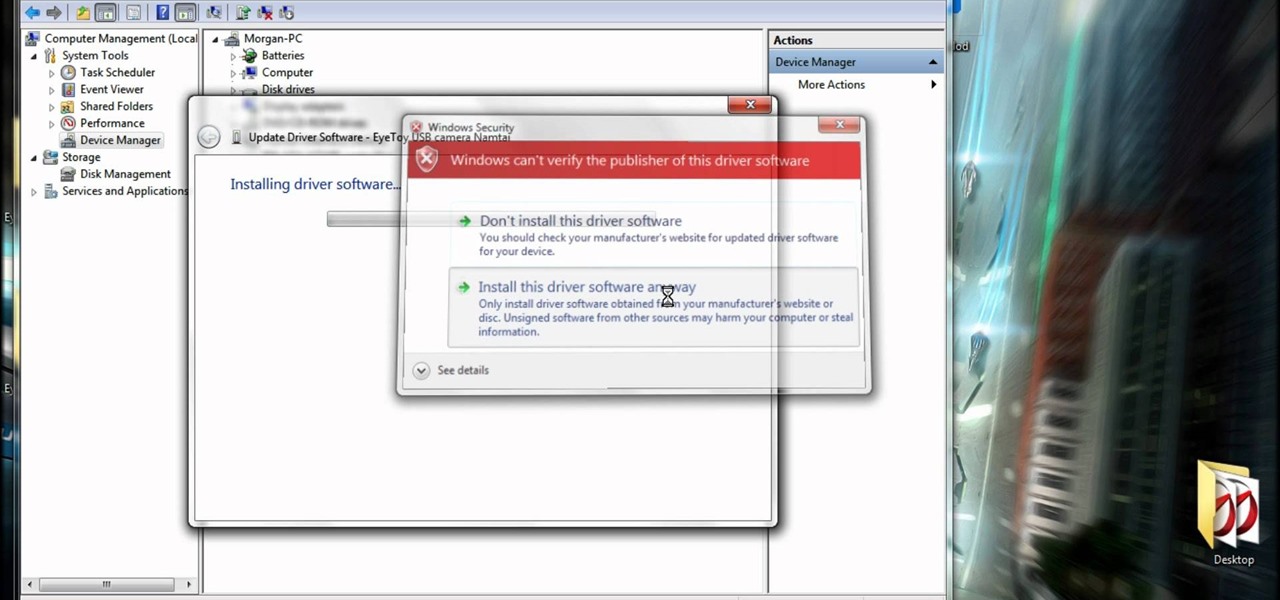
If you have a PS2/PS3 Eyetoy, but don't want to go and spend $30+ dollars on a new webcam, then this is for you.
An amazing amount of news this week; new proposals and new agreements have sprung up. But so has our "need" to spread our presence. The military warns of another war, while 26 congressmen decry the use of drone strikes. Read on:

As a doctor, sometimes it will be necessary to perform a neurological examination of your patient to rule out any neurological disorders. Your objective is to identify abnormalities in the nervous system, to differentiate peripheral from central nervous system lesions, and to establish internal consistency. This is a great video less that outlines the complete neurological exam procedure. It's great for medical students or doctors, and even nursing students can learn a thing or two.

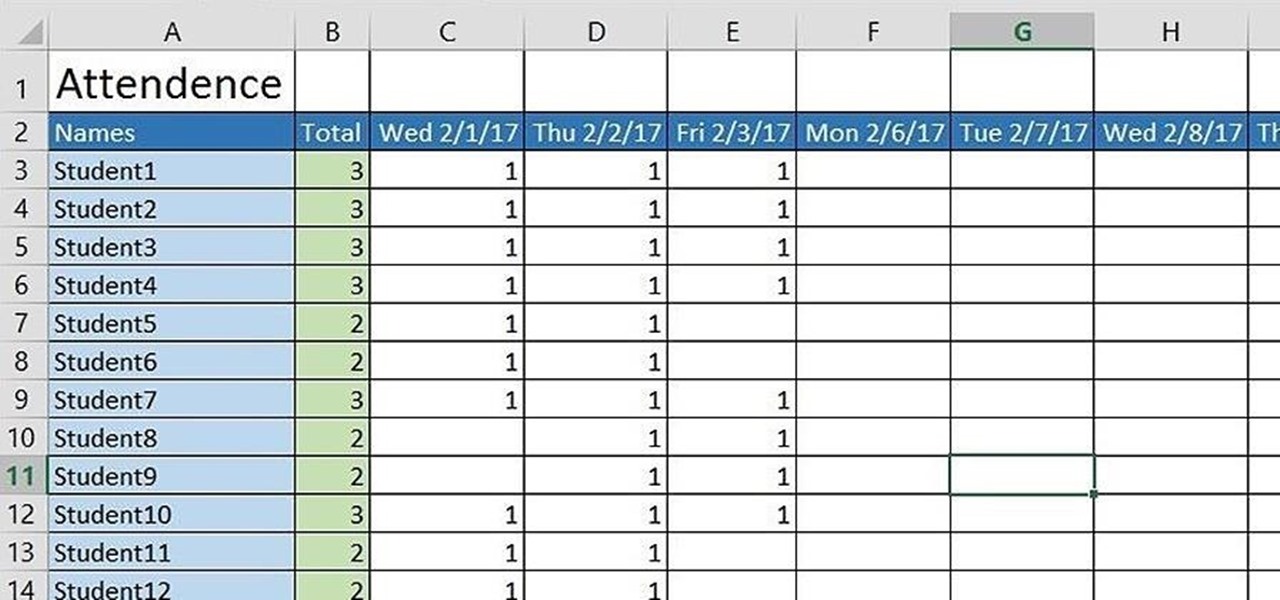
If you're a teacher in any type of school, whether it's high school, college, or middle school, it's imperative that you keep an attendance sheet. The paper and pen route can get pretty messy, and very disorganized, and that's where Microsoft Excel comes in. With this software, you can create a simple yet functional attendance sheet to keep track of your students.