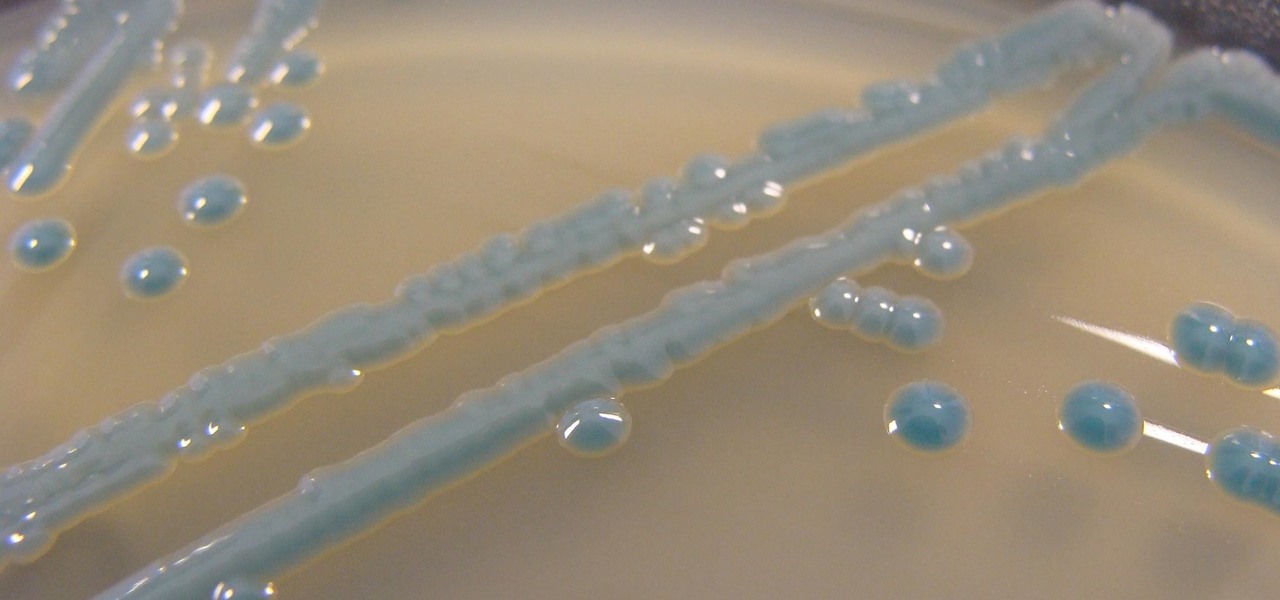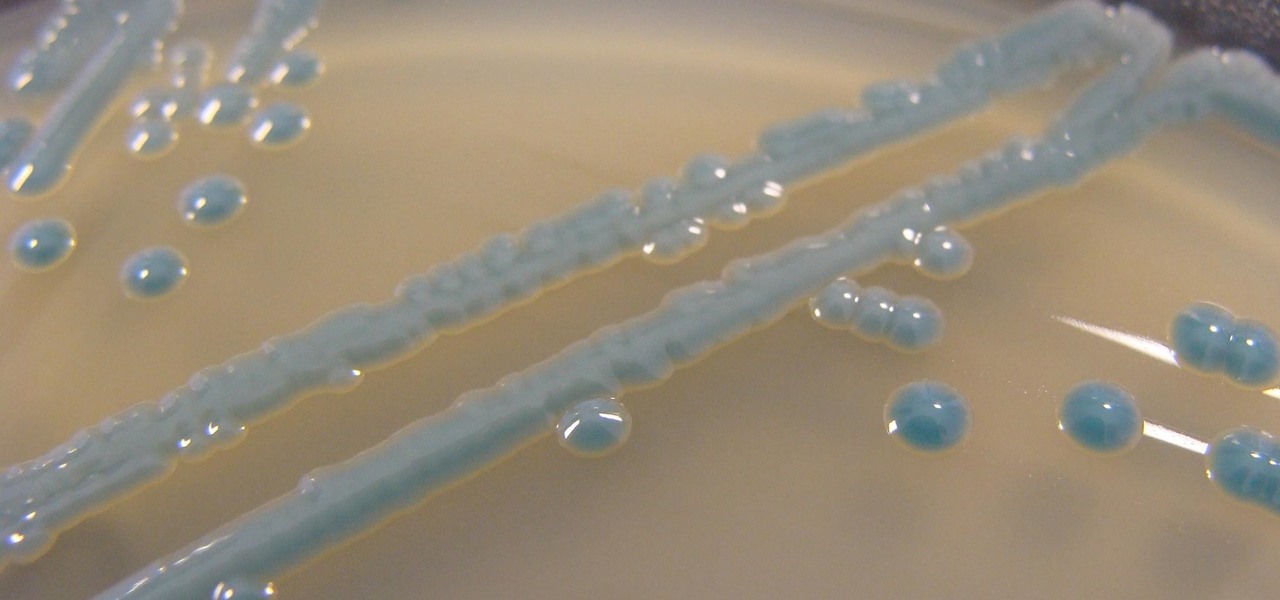
The growing list of dangerous antibiotic resistant organisms has just acquired three new members. Researchers have discovered three new species of Klebsiella bacteria, all of which can cause life-threatening infections and have genes that make them resistant to commonly used antibiotics.

The de Blasio Administration of New York City has announced that the NYU Tandon School of Engineering will be hosting the country's first publicly funded VR/AR facility.

Citrus greening disease — caused by a bacteria spread by psyllid insects — is threatening to wipe out Florida's citrus crop. Researchers have identified a small protein found in a second bacteria living in the insects that helps bacteria causing citrus greening disease survive and spread. They believe the discovery could result in a spray that could potentially help save the trees from the bacterial invasion.

A disease called "citrus greening" has devastated and permanently altered citrus production in the United States, but a vaccine that could protect orange trees may be part of a winning strategy to beat the bacteria that is killing the trees.

General Motors Co. (GM) is set to expand their fleet of driverless cars in San Francisco, Detroit, and Scottsdale, according to documents filed by the company.

Growing populations and higher temperatures put pressure on world food supplies. Naturally occurring soil bacteria may save crops in drought-stressed areas, put more land into crop production, and produce more food.

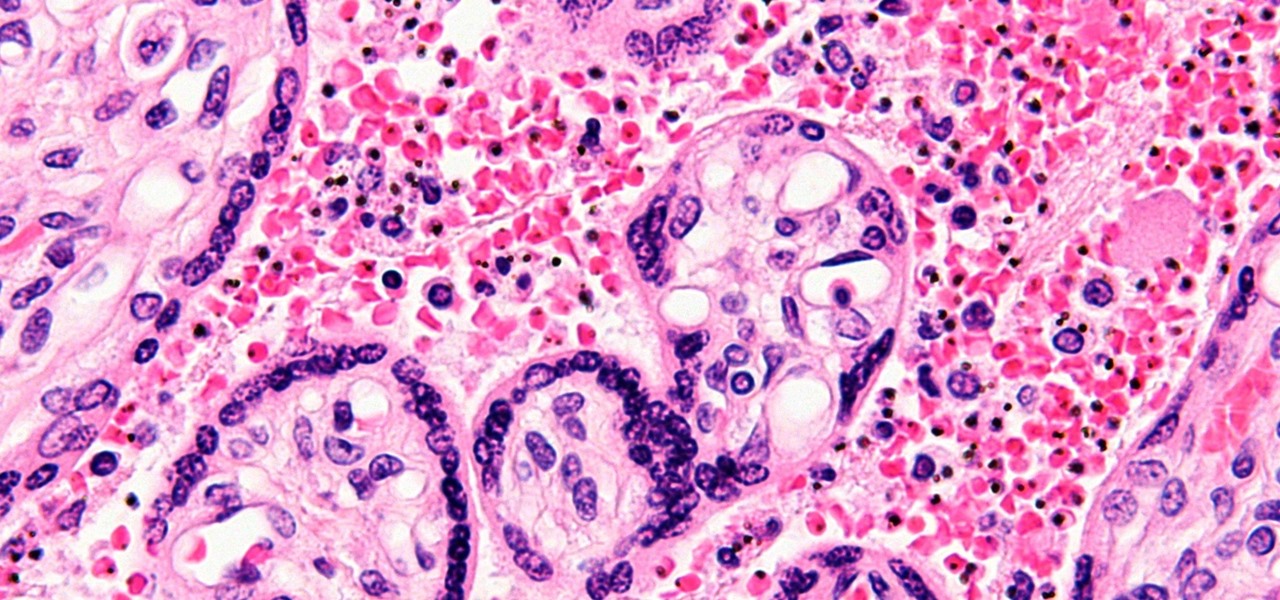
You might feel the bite, you might not, but an infected mosquito has injected you with a parasite named Plasmodium falciparum, a single-cell protozoa that quickly takes up residence in your body.

When I was younger, my best friend's dad would always give us a lollipop on long car rides. I remember three things about those lollipops: they were bright green, tasted delicious, and had a cricket in the center. You know, like a Tootsie Roll Pop... only instead of a Tootsie Roll, a cricket.

Bud Brown explains how to know when to use a voltage adapter in the Philippines. The United States and the Philippines have different voltage systems. In the United States 110 volts are used, and in the Philippines 220 volts are used. If you plug something from one system into the other system, it will not work correctly and may ruin your equipment. Consider that computers and phone chargers are equipped to handle both systems. Check the labels on your electrical equipment to determine if it ...

In bar routine work refers to high bar exercises that are close to the hips. Learn how to perform in bar routines from a professional coach in this gymnastics video tutorial.

If you're looking for an easy way to determine if a number is divisible by 3, then look no further than the divisibility rule. It's a shorthand way to tell if any given number can be divided by 3, without actually performing the division. Take the number in question, and if the sum off all the digits is divisible by 3, then the original number will be, too. There are four examples in this math video.

In this Sports video tutorial you will learn how to compute skins in a golf game. Kevin in this video illustrates how to calculate skins in your golf game. Skins are determined by the winner of each hole. A clear winner gets a skin for that hole. If there is no clear winner, the skin is carried over to the next hole. And the next clear winner of any hole will also get the skins for the previous holes where there was no clear winner. In the video Kevin wins the 1st hole and he gets the skin fo...

Use a simple mathematical formula to find the circumference of a circle. The circumference of a circle can be determined by using the formula 2 times pi times the circle's radius. Pi is equal to 3.14. If a circle's radius is 10 centimeters, first multiply pi times 2. Pi, or 3.14, times 2 is 6.28. The next step then is to multiply 6.28 times the circle's radius. Since the circle's radius is 10 centimeters, multiply it by 6.28. This gives you 60.28. 60.28 inches, then, is the circumference of t...

Let's try the Ken Burns effect. First Google photo story 3 and download the second link and install it. Now open photo story 3, select a new story and import pictures. Then click customize motion under preview and determine the start and end position. When done customizing, click next and select the music required with the desired genre and then save the story with a appropriate name. This will help in creating presentations, good memories as well as slide shows.

This video is pretty fast paced. There is no audio. It explains with video and text how to install Linux in a virtual drive from SUN. It includes the various needed steps including to First install the Linux or Windows CD into your CD/DVD Drive in your PC. Creating your new drive partition and then determining how much ram you want to add to the installation. It shows you how to work with Debian GNU/Linux and passwords and touches on installing Kubuntu.

This video is about a particular pool or snooker game shot technique called "Shooting or Going around the Angles." The presenter, with a alias name of 'Forcefollow', first describes a particular 9-ball pool game situation that would require this technique, using a computer generated picture image to show an overhead view of the pool table, with the pool balls in question placed at certain locations within the table and showing the various angle trajectories paths of the desired ball to be str...

Do some niche research for your eBay affiliate site in these video tutorials, and see how to build an eBay affiliate partner site from scratch. Learn how to drill down into eBay Pulse and search for untapped niches. Finding a niche for your eBay affiliate site might seem daunting, but it's not. Also, learn about the Google Keyword tool and Wordtracker keyword tool along with a basic Google search to determine traffic levels and how easy it is to rank for a given keyword.

Before the calculator and even the abacus was invented, there was a little instrument called the human brain that we used to do math. Remember that? While most of us turn to our trusty Ti-84s to do calculus homework or whip out our cell phone calculators to determine how much we should tip at Johnny Rocket's, it can often be much faster to use our own brains, along with a piece of paper and pencil.

If left unattended, a hacker with a USB Rubber Ducky and physical access to the computer can infiltrate even the most secure computer. Such attacks often go undetected without the use of a tool like USBRip, which can provide you with assurance that your device hasn't been compromised.

A rainbow table can be thought of like a dictionary, except instead of words and their definitions, it holds combinations of characters on one side and their hashed form on the other. What is a hash and why would you want to know what random combinations of characters are hashed into?

Clumsiness is the great equalizer when it comes to smartphones — it makes no distinction between the most expensive flagship handset and cheaper mid-range models. A hard drop onto pavement will usually result in a shattered screen, regardless of how pricey your device is. And with a smartphone breaking every two seconds, we're truly our own handset's ultimate nemesis.

You may not have heard of visceral leishmaniasis, onchocerciasis, or lymphatic filariasis, and there is a reason for that. These diseases, part of a group of infections called neglected tropical diseases (NTDs), impact more than a billion people on the planet in countries other than ours. Despite the consolation that these often grotesque illnesses are "out of sight, out of mind," some of these infections are quietly taking their toll in some southern communities of the US.

Cryptography is the science of keeping secrets, or more specifically, the science of disguising them. As a point of fact, cryptography has progressed quite a bit farther and now encompasses file and message integrity, sender authentication, and pseudo-random number generators.

Wearing the correct size bra is the fasts way to improve your look. The correct size bra will make you look longer, leaner and younger, plus, it will help your clothes to hang better. If you can’t remember the last time you had a bra fitting then it’s time to bust out the measuring tape.

In this article, I'll be explaining the basics of how microcontrollers work, physically and virtually. First off, microcontrollers are no simple thing, so don't be discouraged if you find it mind-boggling! The world of microcontrollers is fascinating, engaging, and an awesome hobby; it never gets boring. I'll be focusing more on I/O and analog based microcontrollers, such as those running Arduino, and using Atmel chips as examples (these are most commonly available, and easy to program).
(Series designed to help explore whether your ideal employment ideas should be formalized into a business venture or as an employee or volunteer value added problem solver).

There are phones nowadays with 12 gigs of RAM, but they'll cost you well over a grand. The majority of Android devices have much less memory — I'd wager most have less than 4 GB. And with the system taking up around 2 GB, that leaves user-installed apps little room to breathe.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

Post-exploitation information gathering can be a long and drawn-out process, but it is an essential step when trying to pivot or establish advanced persistence. Every hacker should know how to enumerate a target manually, but sometimes it is worth it to automate the process. Metasploit contains post modules that can quickly gather valuable information about a target, saving both time and effort.

Web application firewalls are one of the strongest defenses a web app has, but they can be vulnerable if the firewall version used is known to an attacker. Understanding which firewall a target is using can be the first step to a hacker discovering how to get past it — and what defenses are in place on a target. And the tools Wafw00f and Nmap make fingerprinting firewalls easy.

While Magic Leap World gets its share of fun apps for playing with Porgs, watching TV, and exploring the ocean's depths, developers are making a strong business case for the Magic Leap One as well.

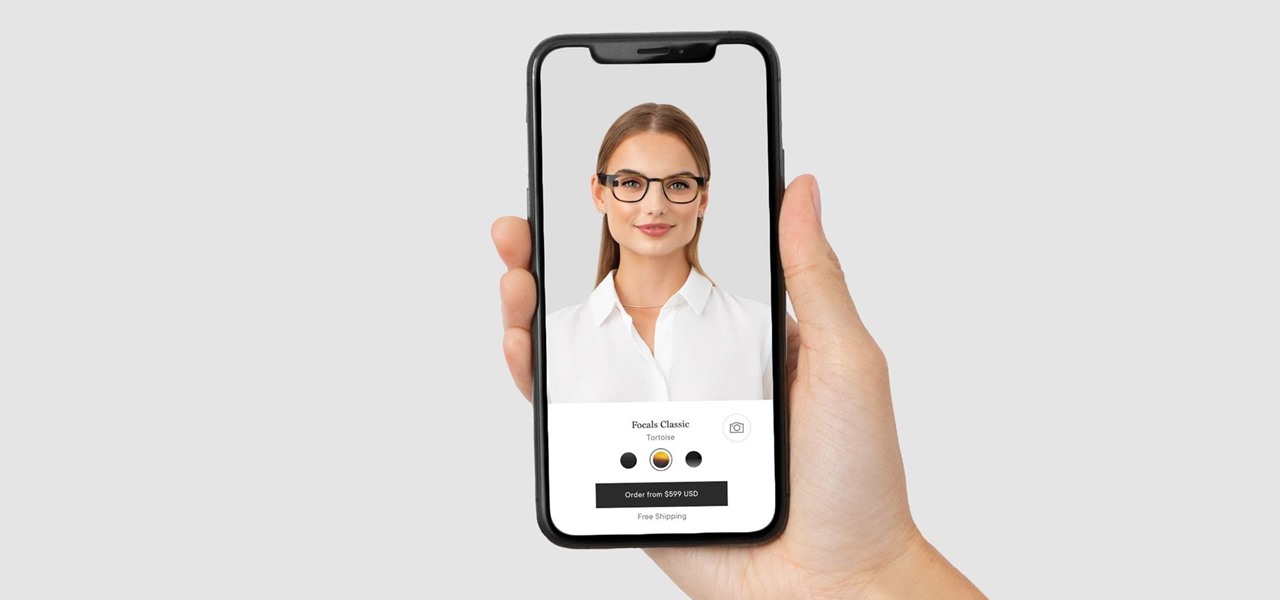
Wearables startup North has made a smart move to get its Focals smartglasses into the hands of more consumers.

When it comes to building luxury cars, Bentley certainly knows what it's doing. However, when it comes to building an AR app, Bentley is looking less Continental GT and more Geo Metro.

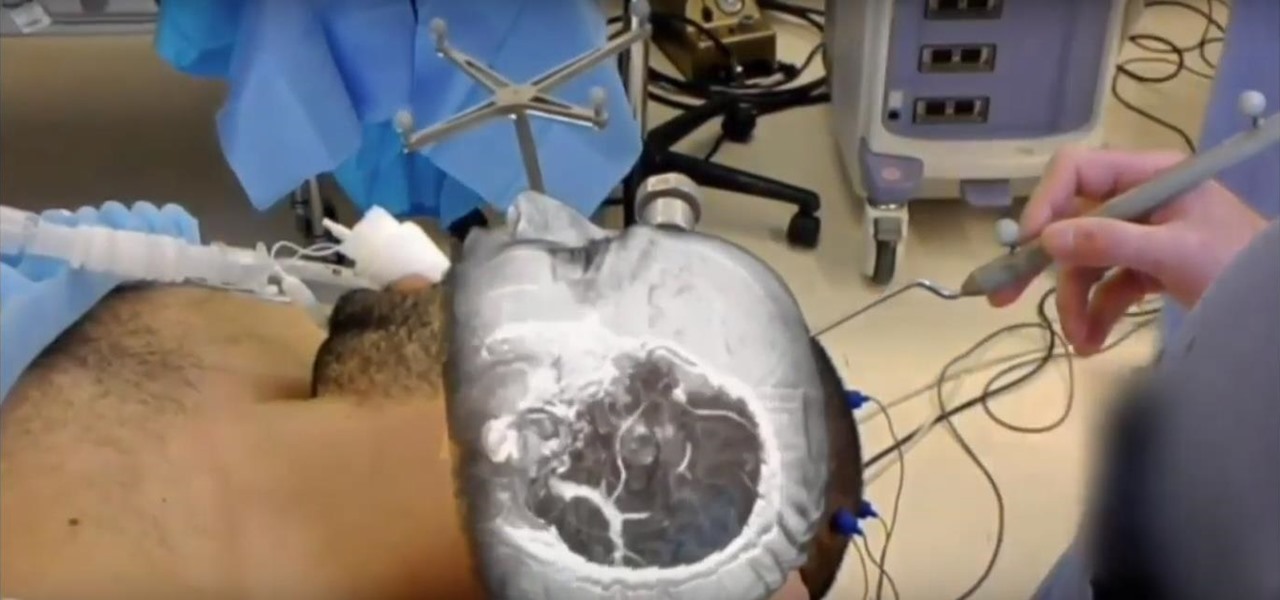
In the last few years, the HoloLens has become a popular tool for use in medical procedures and training. But recently, the Magic Leap One has gained momentum in the space as well when it comes to medical use cases.

Ratings and reviews apply everywhere, from a restaurant you want to try to a new camera you're thinking of buying and games you might want to play. Podcasts are no different. Reading reviews of shows can help determine which are worth listening to, and your opinion is valuable to other people too. In Apple Podcasts, there are a few different ways to read, rate, and review shows.

Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.

After applying augmented reality as a solution for the sale and marketing of sneakers, Nike is taking the next step in its adoption of AR to improve the customer experience.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

Picture this: You finally get that awesome angle, the perfect selfie. You can't wait to post it on your Instagram, except there's one problem — it looks a little flat and the colors just seem off. Maybe it's the lights? Or maybe your new smartphone camera isn't as good as you thought? How are your friends getting those beautiful photos they've been posting on social media?

The HoloLens has made enough of an impact on the healthcare industry for Microsoft technology partner Medivis to convince investors to pledge $2.3 million in funding for its surgical platform.