The Last Supper, or L'Ultima Cena, is a mural painted by Leonardo da Vinci in 1498. It is considered one of the greatest paintings of all time, and if you live in the San Antonio, Texas area, or are willing to travel, you can get it shaved into the back of your head.

The winter holidays are right around the corner and that can only mean one thing—dessert. Leave it to the French pastry chefs to come up with something totally unique, like this glittery, chocolate Slinky by Amaury Guichon of Jean Philippe Patisserie inside the ARIA Resort and Casino in Las Vegas.

If you want to become a food Instagram star, you may want to consider having babies. Well, to be more specific, you might need Mike Chau's two adorable children, Matthew and Samantha.
Hello Strangers, This is my first article for null-byte and its about staying anonymous on the Internet. But the question is why would you want to stay anonymous online?

UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - at my blog, here - https://techkernel.org/2015/12/11/embed-metasploit-payload-in-apk-easily/

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Welcome back, my fledgling hackers! Over the years, we have examined multiple ways to own, exploit, or compromise a system. On the other hand, we have not spent a lot of time on denial-of-service (DoS) attacks.

Hello, my web huggers! In today's tutorial we will learn how to use the Google Hacking Database (GHDB) developed by Exploit Database, to find vulnerable web servers and "juicy" information.

Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.

Welcome back, my greenhorn hackers! As hackers, we often take for granted that nearly all of our hacking tools and operating system are free and open source. I think it's important to examine a bit of background on how we arrived at this intriguing juncture in the history of computer software. After all, we pay for nearly all of our other software (Microsoft, Adobe, etc.) and nearly everything else we use in life, so how is it that Linux and all our hacking tools are free?

With over a billion monthly active users, it seems that Facebook is nowhere close to being dethroned as the most popular social media service in the world (sorry, Ello). While their stats may be impressive, it doesn't mean that Facebook is as good as it can be.

Hello Hackers! Welcome to my 2nd Post: This is a tutorial explaining how to hack android phones with Kali.

Welcome back, my hacker novitiates! As you know by now, the Metasploit Framework is one of my favorite hacking tools. It is capable of embedding code into a remote system and controlling it, scanning systems for recon, and fuzzing systems to find buffer overflows. Plus, all of this can be integrated into Rapid7's excellent vulnerability scanner Nexpose.

Spotlight is awesome for finding items in the stock Apple apps, but what if you want to search through the rest of the apps on your iPhone?

There will always be a time when you're not entirely sure what you're doing with a certain subject. But the days of weighing the pros and cons yourself are coming to an end. Whether it's a common quandary like "Where should we eat?", or a more specific question along the lines of "Should I buy this shirt or not?", you can now simply AskInternets.

OK as you all know i was the won who loved ships on the old server, well though they all looked weird this may be the best I've ever made. I made a small replica of the Titanic but its bigger than any other ship i made on the server.

I know that after seeing 8 Mile for the first time, you and your friends tried a few freestyles yourself. Nothing to be embarrassed about. As one person dropped the beat, you started your stuttering flow, and everyone else nodded their head. And for a second you probably thought you sounded pretty good, until the beat maker started coughing and threw you off.

The new Samsung Galaxy S4 may be the only phone to include temperature and humidity sensors, but your Galaxy Note 2 has a few weather-detecting features of its own.

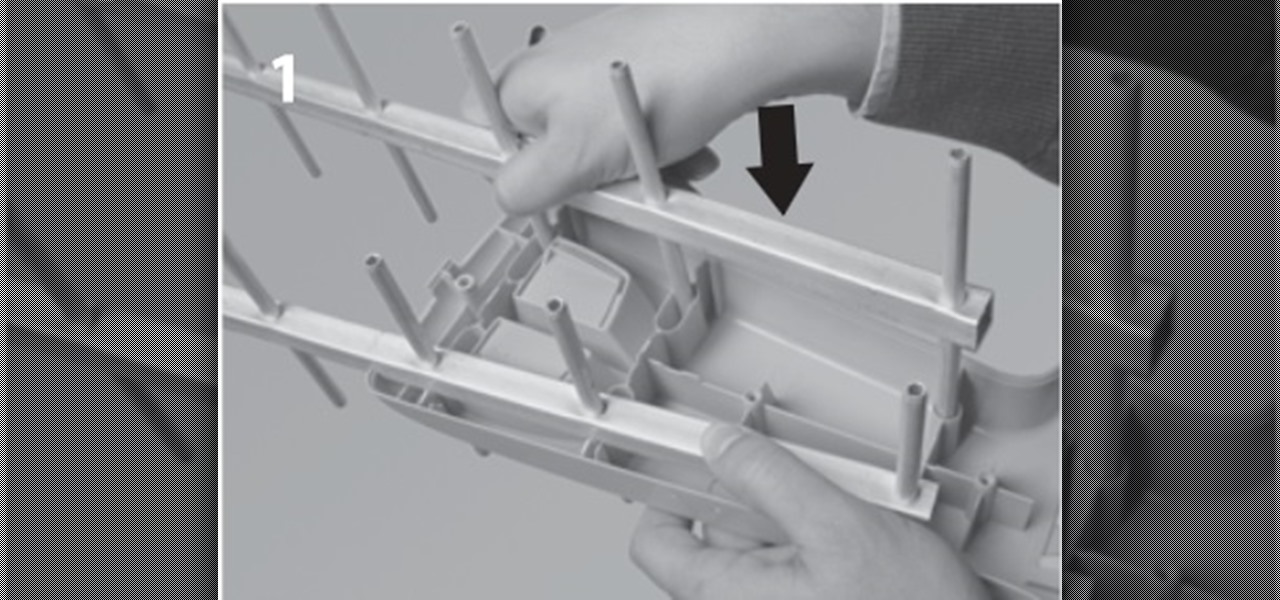
In this post I'm going to explain the assembly of an UHF antenna, step by step. Assembly of v HD Antenna of TELEVÉS We will need a Screwdriver and wrench.

As enjoyable as Facebook can be at times, it can also be a great distraction and even better deterrent of getting work done. A quick "Oh, let me check my notifications" can turn into hours and hours of Facebooking, and before you know it, you're already on your 7th Wikipedia page, all thanks to that status your friend posted. The reason I mention this is because Firefox's new 17.0 update includes many features, but the one that's been making the rounds online is the integration of Facebook Me...

Zombies. That's the first thing that comes to mind when I see footage of a once heavily populated area turned completely desolate. Either that or you stumbled across a Ke$ha concert...BURN.

Robert Templeman from the Naval Surface Warfare Center in Crane, Indiana and several of his friends from Indiana University recently developed an Android application that is capable of gathering pictures and videos from mobile devices in order to reconstruct a user's environment in 3D. The malware would come coded inside of a camera application that the user would download. The malware, called PlaceRaider, would then randomly take pictures throughout the day and carefully piece them together ...

Everything is documented these days, thanks to the Internet and mobile devices. Most people who own a smartphone use it to take lots of pictures. If you're one of those people, an app called Scoopshot can help you turn some of those photos into extra cash. Scoopshots lets you post your pics so that news organizations can pay you to use them. Companies can also post tasks, so if someone is looking for a particular photo in your area, you can accept the task, go take the photo, and earn money f...

Unless you're living in some weird parallel universe where plug-in light bulbs are the norm for household lighting, chances are you've had to unscrew a light bulb every now and then.

WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the communities.

Asphalt5 is a racing game for the WebOS phone operating system, originally developed by Palm. If you want to play it (and you should) on your Nokia N900 handset there are some complications you're going to have to get through, and this video will show you how step-by-step.

Rust protection doesn't have to cost a fortune. With a little zinc and some electricity, you can protect your precious metals from rust by galvanization. When you galvanize something, you're giving it a protective coating, and in this case, it's a zinc coating.

November 11th isn't just Veterans Day— it's Origami Day in Japan, where they celebrate the traditional art of paper folding. November 11th is also the last day of World Origami Days, a 2-1/2 week celebration held internationally.

Acne develops when pores become blocked with dead skin cells and oil. They usually disappear over time but sometimes they leave a scar. When those blemishes form white blood cells rush to the surface to help heal the area. But occasionally a scar forms. Popping and picking can send bacteria further into the skin and increase the blemish and it greatly increases the likelihood that a scar will appear. Nodules and cysts are more severe blemishes and have an increased likelihood of leaving scars...

Want more gold? How about more skill points? You may need them in the game Acruz. But how do you get more, more, more? Well, with Cheat Engine, you can get more gold and skill points, with no real hassle.

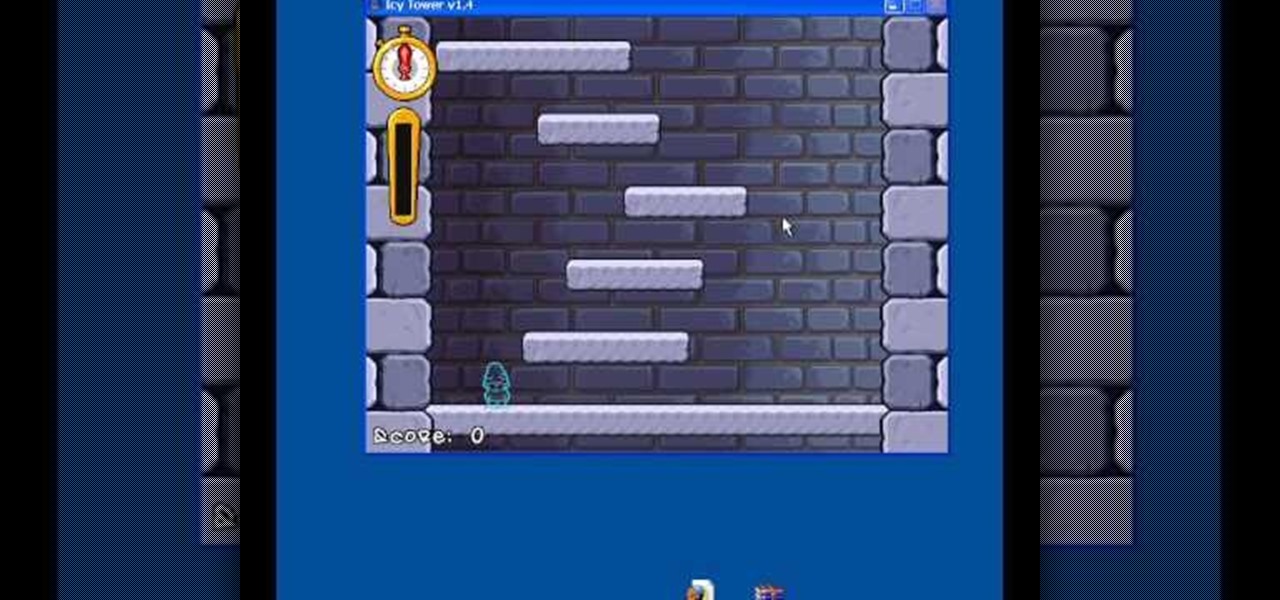
The cold time of Christmas is upon us, and Icy Town is a winter-ific game you can play… and hack. With Cheat Engine and a little patience, you can hack and unlock floors in the game easily.

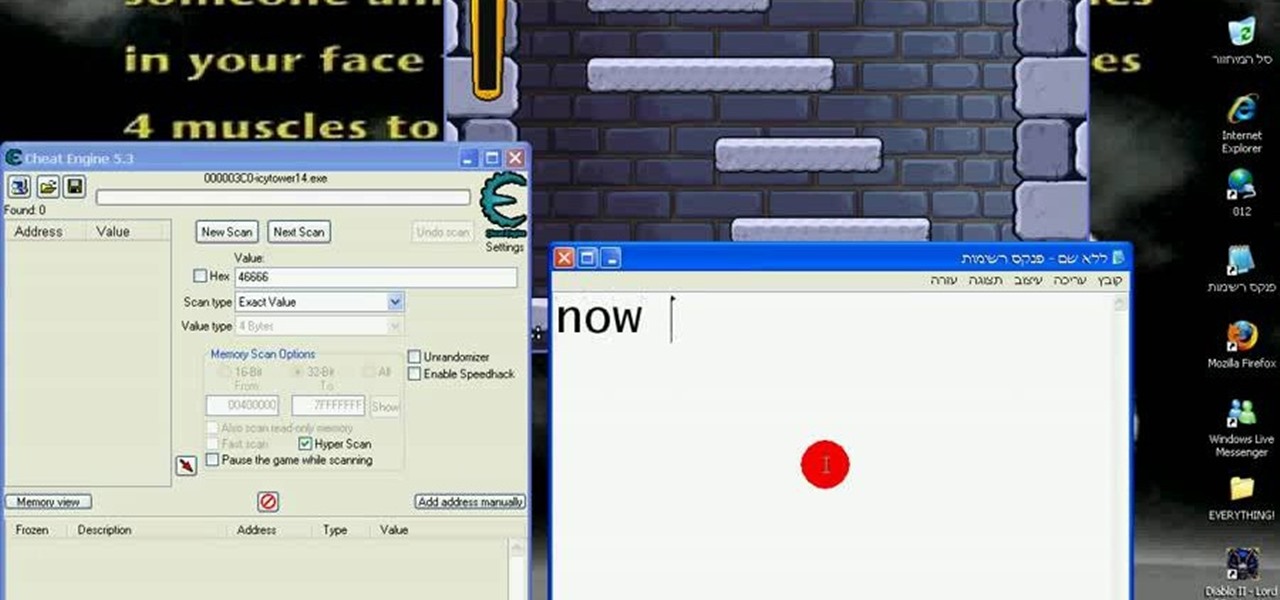
It's Christmastime, so what better of a game to play than the winterized Icy Tower? And what better game to hack with Cheat Engine?

New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to share files between Ubuntu (Host) & XP (Guest).

This series of ping pong / table tennis videos demonstrate how to master the backhand drive. Jim Clegg, a Level 4 Coach with the English Table Tennis Association and Head Coach of the Preston Table Tennis Association, explains and demonstrates how you play a backhand drive correctly.

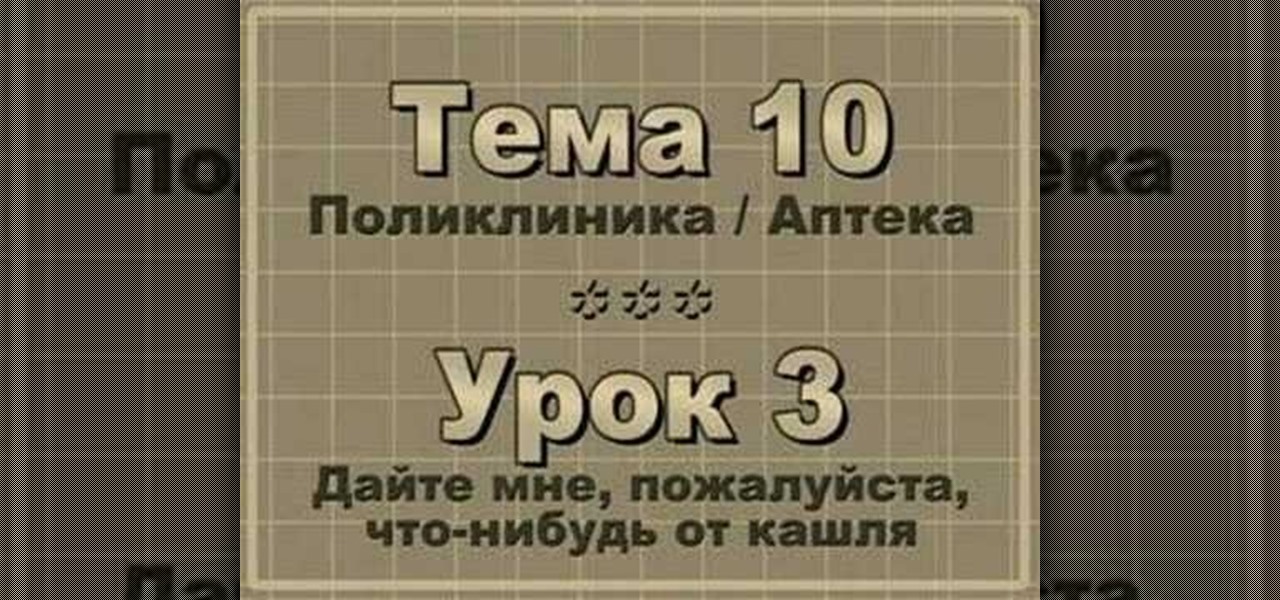
Check out this instructional Russian language video to learn Russian as Russians speak it. This is Theme 10, Lesson 3 in the series. Practice your Russian listening skills by listening to the dialogue presented in this language video. Learn words related to your health, being sick, and visiting a doctor or hospital clinic.

Check out this instructional Russian language video to learn Russian as Russians speak it. This is Theme 11, Lesson 1 in the series. Practice your Russian listening skills by listening to the dialogue presented in this language video. Learn words related to meeting your friends in public.

Check out this instructional Russian language video to learn Russian as Russians speak it. This is Theme 10, Lesson 2 in the series. Practice your Russian listening skills by listening to the dialogue presented in this language video. Learn words related to being sick and conversing with a doctor.

Check out this instructional Russian language video to learn Russian as Russians speak it. This is Theme 8, Lesson 1 in the series. Practice your Russian listening skills by listening to the dialogue presented in this language video. Learn how to have a conversation with someone about their upcoming and previous travels.

Check out this instructional Russian language video to learn Russian as Russians speak it. This is Theme 7, Lesson 3 in the series. Practice your Russian listening skills by listening to the dialogue presented in this language video. Learn words related to inviting your friends out.