
How To: Make Play-Doh Roses for a Cute Gift Idea
Love making gifts for your loved ones? Here is a tutorial that shows you how to make a play doh rose. It's really easy and fun to make.


Love making gifts for your loved ones? Here is a tutorial that shows you how to make a play doh rose. It's really easy and fun to make.

Welcome back, my greenhorn hackers! Lately, much of the discussion here on Null Byte has revolved around evading detection and not getting caught hacking. Several of you have written me asking for a series on evading detection and forensics, and while I began a series 5 months ago on just that, we have changed hacking platforms from BackTrack to Kali, which has a much more highly developed forensic toolset.

If mainstream media has taught us anything, it's that being beautiful can get you ahead in life. The notion isn't necessarily correct, but it's what the general consensus accepts and it seems to hold quite a bit of weight (no pun intended) in the western world.
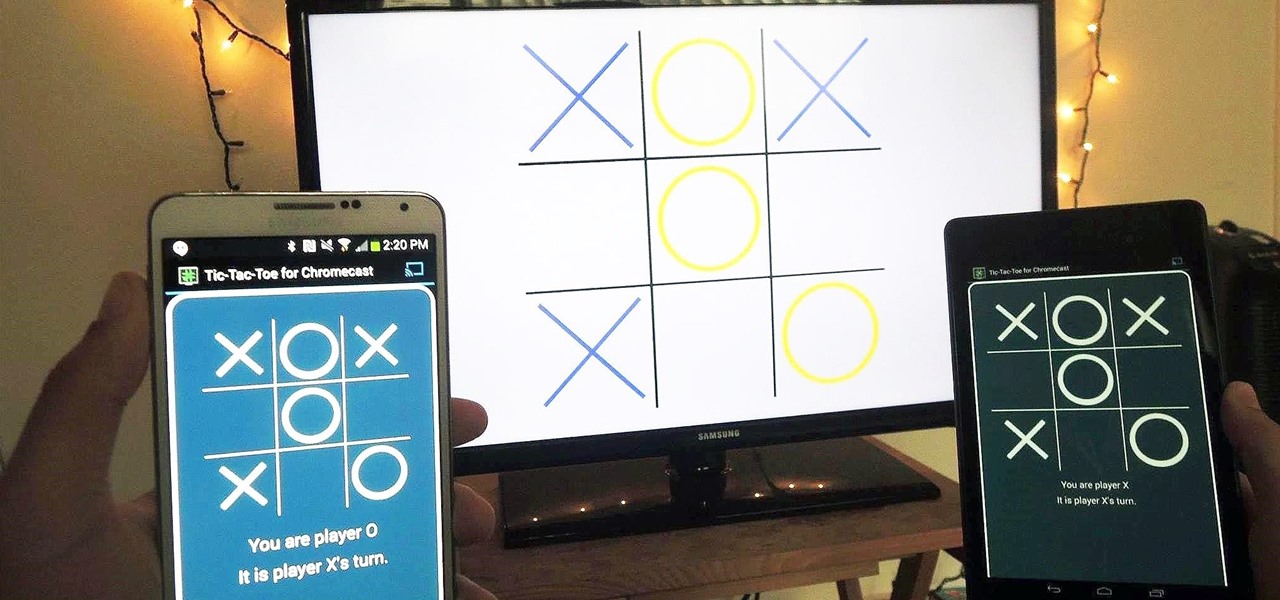
With the emergence of rumors that Amazon, Google, and Samsung are all making their foray into the gaming console market, it's a possibility that our Android-powered mobile devices might become tools that play a central role.

Facebook makes it easy to show how much you appreciate a funny status, great picture, or cool news article using their iconic "thumbs up" button, but what about those terrible jokes and annoying baby pictures? Where's the "thumbs down" for that crap?

My friends can be pretty shitty sometimes, but they're my friends nonetheless. On various occasions, they've secretly taken my device and made me look foolish by posting crude and embarrassing posts to Facebook, Instagram, or Twitter. With friends like these, who needs enemies, right? And it's because of these types of friends that we need to substantially upgrade the app security on our devices.

While browsing the internet on your Samsung Galaxy S4, you've probably scrolled to the bottom of a very long webpage, Twitter feed, or down into the abyss of some other app. Depending just how far down you've scrolled, it can be a test of your patience (and fingertips) scrolling back up to the top.

Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

The Google Play Store exists so you can download as many apps as your heart desires (and as your memory can hold). Sure, you may only use them once, but it's your choice—and isn't that what life is really about? With that said, the Samsung Galaxy Note 2 already comes with a ton of preloaded apps from Google, Samsung, and your device carrier, like Yellow Pages and Google Earth—both of which I never use. So why is it that Android won't let me remove or uninstall them?!

No matter what device you have, Android lag will get you down. It's our little green robot's only major downside, and you've probably noticed it quite a bit on your Nexus 7 tablet. Apps open slowly, actions stutter or pause, and loading files takes forever.

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

As you may have noticed, many of our tutorials cover topics that require you to have root access. When your phone is rooted, backing up apps doesn't require you to connect to your computer, and installing custom ROMs lets you get more useful settings. Rooting also lets you get rid of the Sense-style menus and status bar, and even upgrade to a newer version of Android.

As we all know, our attention spans are much shorter now that we're accustomed to getting information and news in tiny snippets via text messages, tweets, instagrams, and other constant updates.

Social media is where we post our thoughts for the world to see, but sometimes a little more exclusivity is needed. And that's where Scrambls comes in.
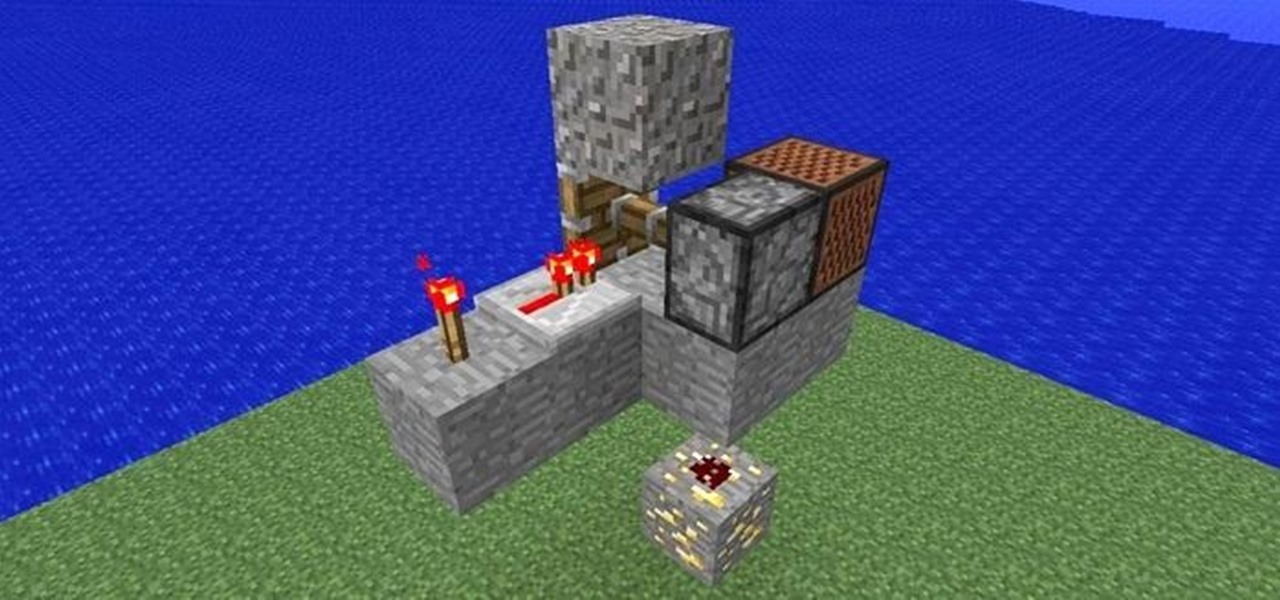
I saw Maro post about a trap on YouTube today, so I thought I'd post one here that I just invented. Since we are friendly at WonderHowTo, the TNT has been replaced with a note block. Step 1: Bait

3D printing has been around for a while, but until recently it was used mostly for prototyping and research. Now, with technological advancements, it seems like everyone is using 3D printers, from crime scene investigators to garage hobbyists and hackers. Below are some of the most innovative uses people have come up with so far.
An amazing amount of news this week; new proposals and new agreements have sprung up. But so has our "need" to spread our presence. The military warns of another war, while 26 congressmen decry the use of drone strikes. Read on:

The Library of Congress video archives brings this late nineteenth century dance lesson demonstration. Follow along with the performers as they show off their traditional moves, dancing a Washington post two step dance. It might take a bit of dance practice, but grab your partner, put on some music, and follow the steps. Watch this video traditional dance tutorial and learn how to do a late nineteenth century Washington post two step dance.

The two-step is a step found in many folk dances, and in various other dances. The Washington Post Two Step is a 19th Century name originating in the USA. It is similar to the traditional two-step dance but slowed down and a bit jumpier. This video is only a demonstration, and unfortunately it does not give step by step instructions.

Learn the correct position for playing defense on the low post as a basketball player.

How to grow pineapple inside your home

Did you know that you can zoom in on your Mac laptop just as easily as you can on the iPhone? All you need is your fingers, your mouse and to activate the zoom function on your computer. Check it out!

In this video, you will be walked through the game Foreign Creature. There are human characters in this one, with word clouds, in an office setting with bulletin board, desks, rolling shelves, and tack boards. In another scene of the game, you will see a hospital setting with nurses, surgery table, patient, medical equipment, and doctors. In this setting, the patient is a foreign creature who blacks out the medical staff and proceeds to stalk the hospital. Police try to capture the humanoid-l...

The best way to win friends over in a foreign country is by breaking the ice and showing your enthusiasm with your best effort at their language. Practice your Gaelic for travel or just for fun with friends.

Roughly half of all Americans believe in extra sensory perception... Are you part of that statistic? Ever get the feeling you have a paranormal ability? You can investigate your psychic abilities and hone your skills with these tips.

Make your own custom characters for Icy Tower! It's as easy as drawing stick figures, believe it or not. Only stickman don't look as cool, unless of course it's a stickman that you want to use as your Icy Tower character.

This guide is all about hacking Icy Tower. You will need to download Cheat Engine 5.5 before you can try this hack. See what you can do.
Find a way to get a combo achievement in Icy Tower… by cheating. With Cheat Engine, it's easy to hack Icy Towers. See for yourself.
If you've ever been asked to find the GCF, or Greatest Common Factor, of a series of numbers or algebraic expressions, check out this video to learn how.

Do you ever feel as if your mind is running away from you? What if you could map out all of those thoughts into a coherent map that helps you make sense of your reality? Well, now you can.

We all know how volatile the stock market is, especially during times of crisis. That does not mean that the market is impossible to gauge, however. Day traders are trained to read charts in order to recognize market trends and price patterns, giving them the insight they need to make their trades as profitable as possible.

Apple just released the second iOS 13.4.5 developer beta today, Wednesday, April 15. The update comes just over two weeks after the release of 13.4.5 dev beta 1, which introduced a new way to share Apple Music songs to Instagram and Facebook stories.

The augmented reality team at USA Today closed out a prolific year of immersive storytelling with a hard-hitting companion piece exploring the controversial conflict in Afghanistan.
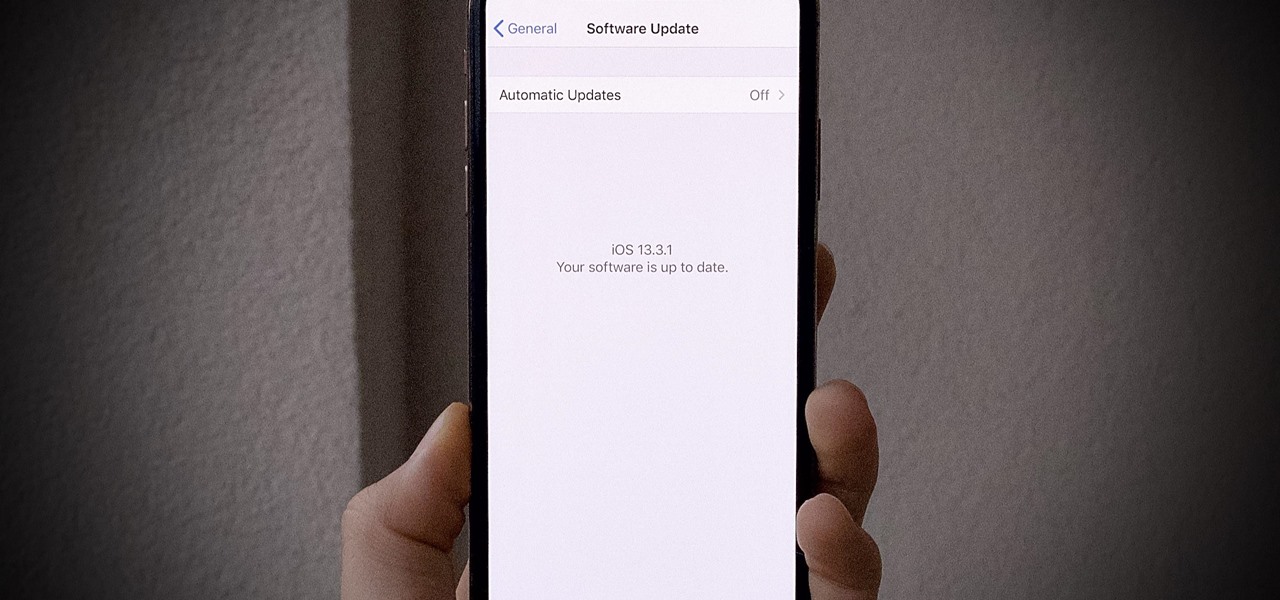
Yesterday, Dec. 17, Apple released the first developer beta for iOS 13.3.1. The update marked the first new beta in almost a month since iOS 13.3's fourth beta dropped on Nov. 20. Now, one day later, Apple has pushed out iOS 13.3.1 public beta 1 to everyone who wants to try out new features first.

Now that iOS 13 is in the wild, developers are starting to show off the magical augmented reality powers ARKit 3 can deliver.

Apple's annual iPhone launch is set for Sept. 10 and iOS 13 is expected to be released soon thereafter, but it appears that the likelihood of a "one more thing" reveal just got a big boost.
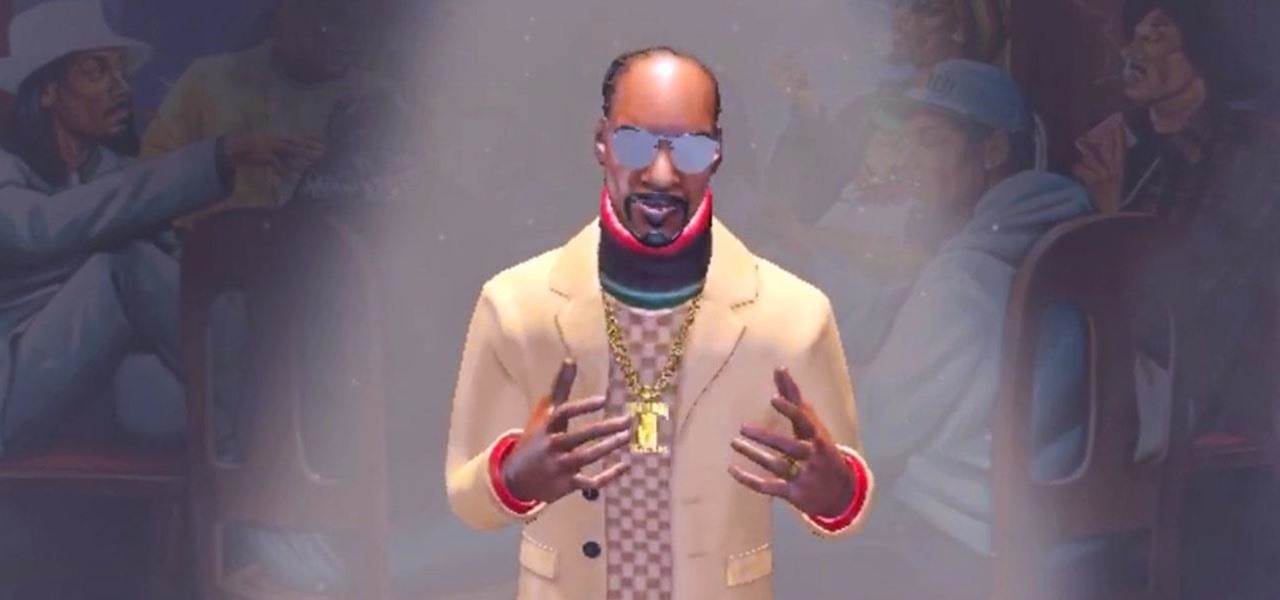
He might be an O.G. rapper, but Snoop Dogg has officially entered the cutting-edge of technology via a hidden feature included with his newest music release.

With all the talk about returning to the moon via SpaceX, NASA, and international agencies, some have forgotten some of the magic surrounding the original Apollo 11 mission.