Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.

Each day, we read about another security breach somewhere in our digital world. It has become so commonplace that we hardly react anymore. Target, J.P. Morgan, iCloud, Home Depot, and the list goes on and on.

I spend an ungodly amount of time on Reddit, and while I do enjoy scrolling through memes and scandalous confessions, I must admit that I spend the majority of my time watching an endless stream of YouTube videos.

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.

Although your friends might roll their eyes every time you talk about playing Clash of Clans, Call of Duty, or Candy Crush Saga, your excessive gaming habits might actually be making you healthier than everyone else.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.

Airports are terrible germ-infested purgatories where people sit around for hours without Wi-Fi while they anxiously await to get wherever they really want to go. Unfortunately, there isn't much we can do about waiting, but this little Wi-Fi hack could help make the waiting a little less boring.

Parties are a great way to celebrate and have fun with your good friends, so to make sure your next party rocks, I've assembled some of the biggest life-hackers on YouTube to bring you 10 outrageous party tricks your guests will not forget.

Automated tattoos are now a reality, with 3D printers being hacked into tattoo machines. Multiple people have posted videos of their 3D printer that can "print" tattoos, with one of the more impressive ones shown in the two videos below.

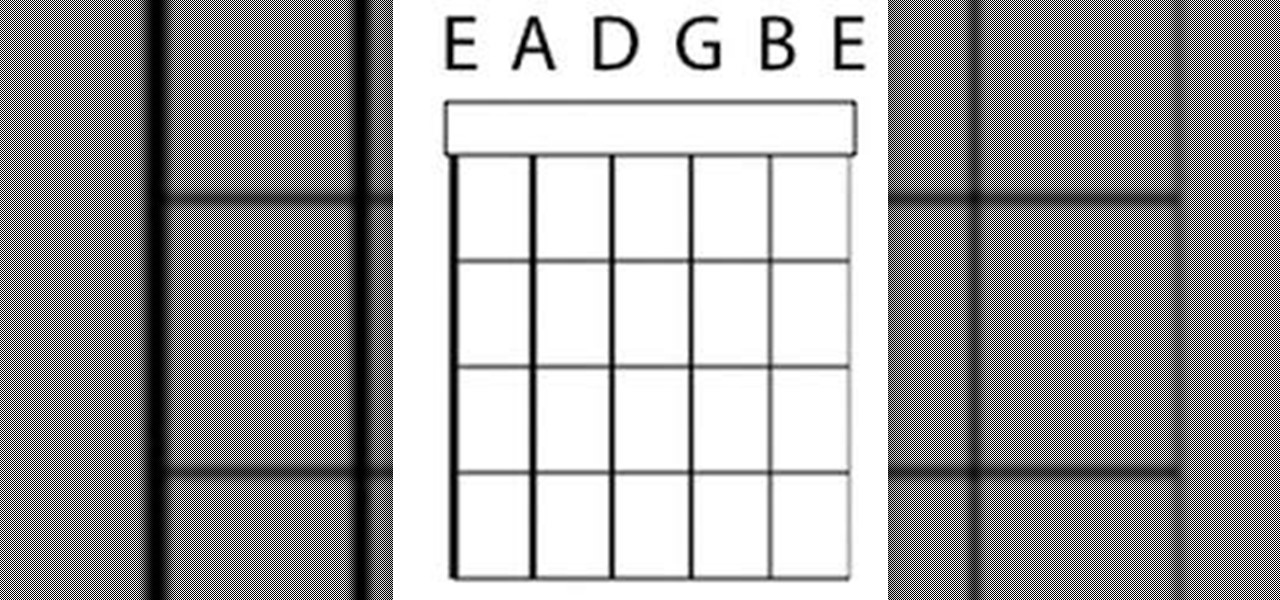
The daily-problem of guitarists is very simple. It is to 'tune a guitar'. This post is for the most of the beginners who want to but couldn't tune their guitar. Here is a very short and easy process to tune a guitar.

Update: June 2nd, 2014 Over the weekend, someone snuck in to Apple's presentation dry run, and grabbed a quick video of the new iPhone will look like.

Last night, I was reading a riveting National Geographic article on the green-eyed tree frog, until I was quickly interrupted by an annoying popup asking me to "create a free account" or "sign in." Really, I'd like to do neither. I just want to read about tree frogs.

Welcome back, my tenderfoot hackers! We have looked at a number of ways that we sniff traffic on the network with such tools as Wireshark, tcpdump, dnsiff, and others, but each of these tools is only capable of pulling packets off the wire.

April Fool's has come early, with an update for Google's Maps application for both Android and iOS that's geared towards finding their next big hire: Pokémon Master.

The new HTC One M8 has only been out for a few hours, but it's apparent that some people had their hands on the device before the announcement. And well, one them decided to drop the thing in water.

We've always been able to switch between running apps pretty easily, but iOS 7 beefed up the multitasking menu significantly by incorporating app previews in lieu of just icons.

With the Samsung Galaxy S5 all but assured to be showcased in a just a few weeks, we've got our hands on some fresh details of the upcoming flagship device.

If you look at the label on your favorite processed snack, there's a good chance you have no idea what half the ingredients are. It's nothing new, but with natural and organic foods becoming huge trends, we're hyper-aware of all the "chemicals" we eat.

Snapchat has had more than its fair share of security failures and mishaps. The photo-sharing company is looking to better address some of these security gaps by adding new features, and today its most recent addition is live: the Captcha. New users will be asked to verify their "humanness" by selecting the infamous Snapchat ghost out of a selection of images. The feature is supposed to help block hacker-made bots from creating fake accounts or accessing existing ones. But rather than using t...

Welcome back, my fledgling hackers! As nearly everyone has heard, Target Corporation, one of the largest retailers in the U.S. and Canada, was hacked late last year and potentially 100 million credit cards have been compromised. Happening just before Christmas, it severely dampened Target's Christmas sales, reputation, and stock price (the company's value has fallen by $5B).

Welcome back, my rookie hackers! The more we know about a system or network, the better our chances of owning it and not leaving a trace for investigators to follow. One of the often overlooked sources for information is the Simple Network Management Protocol (SNMP). Many rookie hackers are not even aware of it, but it can prove to be a treasure trove of information, if you understand how it works and how to hack it.

Some of my fondest memories from childhood was when I'd bust out my Moonwalker VHS and practice all of Michael Jackson's greatest moves. Needless to say, as I sit here typing this post, that my dancing career failed before it began. I have a few decent moves on the dance floor now, but don't expect to see me trying anything special unless tequila is involved.

Welcome back, my budding hackers! I've written several listener guides on creating a malicious PDF or malicious Word document that would carry in it a payload with the Meterpreter, or reverse shell enabling you to own the system. One of the hurdles to using these techniques is the antivirus (AV) software on the target system. For instance, if you try to email a malicious PDF or Word doc, it's likely that the victim system will alert the victim that it contains a virus or other malware.

Welcome back, my greenhorn hackers! Recently, I asked the Null Byte community what subject they would most like me to cover in future tutorials. Many of you cited scripting, and I decided it's best to cover this subject soon, so here goes.

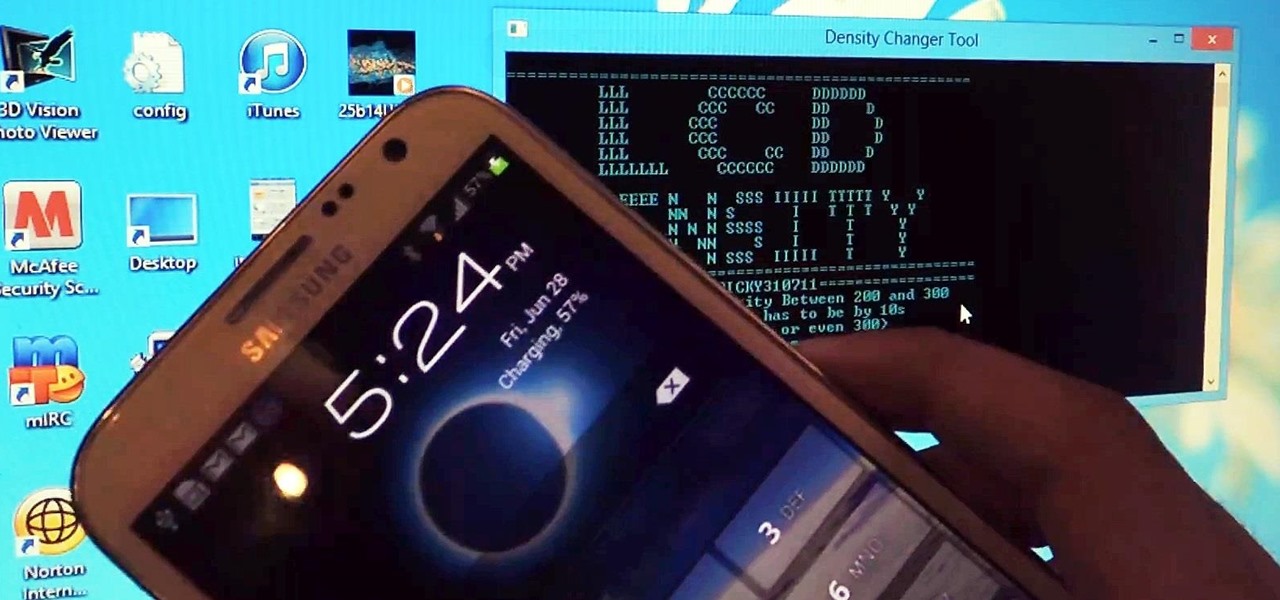
Xposed, by XDA developer rovo89, is a framework for your Samsung Galaxy S4 (or other Android device) that lets you add tweaks and customizations to your ROM (either stock or custom) without any real hassle.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!

Guacamole is one of those things that tastes far better than it looks. To someone who isn't a huge fan of avocados, guacamole's texture can appear slimy, and on top of that, its chunky green appearance brings up visions of Nickelodeon-style slime. What's even worse is the browning that occurs in just a few minutes of being exposed to air, and it's even worse if there's salt in it. I love guacamole, but that brown is enough to turn off even the most enthusiastic connoisseur. Few things are mor...

Hey dolls! I love my new infrared hair straightening iron by MUK. I thought it was a gimmick but really, the technology makes sense. I love that you can adjust the temperature unlike GHD straighteners. So if you if have fine hair you can turn it down and if you have thick crazy hair like me you can turn the bad boy up!

Yellowed or hazed headlights don't only make your car look tacky, it also reduces the amount of light that can shine through at night. This results in poor visibility and may result in an unnecessary accident.

There are a ton of cool features available on your Samsung Galaxy Note 2, but if you're a softModder, you can make your phone do just about anything.

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.

If you're studying human anatomy (or have ever visited a doctor's office), you're no doubt familiar with those plastic anatomical models with removable pieces meant to teach the different parts of the body. Before those, there were illustrated pop-up books. If you need to know the difference between the latissimus dorsi and the multifidus, you're probably better off sticking with your textbook diagrams. But if you prefer a more artful approach (and have a lot of time one your hands), this pap...

Welcome back, my rookie hackers! Several of you have written me asking about where they can find the latest hacks, exploits, and vulnerabilities. In response, I offer you this first in a series of tutorials on finding hacks, exploits, and vulnerabilities. First up: Microsoft Security Bulletins.

Who doesn't love a good prank? Taking advantage of unwilling and gullible bystanders is an obvious recipe for success—and some hilarious amusement.

If you can think of a piece of junk, someone has probably found a way to turn it into a lamp. Granted, sometimes the result is more functional than beautiful, but DIY lighting is probably one of the most versatile projects you can take on.

One of the best aspects of Android is its customization options. You can change launchers and icons, add widgets, and replace standard apps with others that allow full customization. Android allows your device to really take on your personality, from the inside and out.

This is a very easy nail design that I did quite a long time back, and I decided to post it here today because I thought it really deserved to be shared !

This is a very adorable looking nail design that I tried a few days back on my valentines day list of 'nails to do' ! It worked out exactly as I had planned , though during the execution it looked as if it may not, and I was happy enough to post this design online and share it with my viewers!

Who doesn't hate Auto Correct? There's nothing worse than hitting 'Send' only to realize that your phone betrayed you by changing a word so that your message doesn't even mean the same thing anymore—especially when it's going to someone like your boss or parents.

If you've never heard of cookie butter, it must be because you live in a town where there's no Trader Joe's. It was their most popular item in 2012, and when it started to become popular, the Internet promptly went nuts, posting recipe after recipe using it as an ingredient. For those of you who don't live near a Trader Joe's but still want to see what all the fuss is about, there's good news—you can make it at home—and you don't need spiced Speculoos shortcrust biscuits either!