
How To: Make a homemade teabox
With tips from this video, learn how to make a homemade teabox. Use scrapbooking, dictionary print, and dried violets for the top. This is a great gift for a friend who likes to drink tea.


With tips from this video, learn how to make a homemade teabox. Use scrapbooking, dictionary print, and dried violets for the top. This is a great gift for a friend who likes to drink tea.

This episode of Full Disclosure demonstrates how to hack/crack MD5 password hashes. MD5 (Message-Digest algorithm 5) is a hash function commonly used by websites to encrypt passwords. MD5 is a one-way hash; therefore, to crack the password you most try every possible dictionary word and if that does not work, every possible letter/number/symbol combination. The programs used to crack the passwords are Cain and MDCrack-NG.

Typing on a mobile device has come a long way since the days of flip phones. Today, there are awesome keyboard apps like Gboard, which integrates Google search features and makes typing a breeze. But the whole experience still stands to improve if you take some time to learn a few useful tips.
Google is a powerful search engine, but if you don't know all of the tricks to searching, you're not getting the best results possible. This video demonstrates all of the quick tricks to maximize your Google Search experience.

In a previous post, I wrote about how controversy changed SCRABBLE, about how the SCRABBLE Dictionary evolved thanks to Judith Grad and her crusade to rid the world of derogatory and racist words. She won, at least in some manner, but the fact still remains, racist or not—words are words, and they're here to stay.

If you have any mexican blood in you, you may already know what a cholita is defined as. If you don't know the urban dictionary defines a cholita as, "pretty much a tough girl.Usually a female version of a vato. They draw their eyebrows on and wear chuck taylors and carry a glock." There you go! Now if you're interested in drawing a cholita, this video will show you how to draw one crazy looking cholita. So good luck and enjoy!

In this video tutorial, viewers learn how to secure a home wireless network. There are 3 types of security protocols for connecting devices. The 3 types of security protocols are: OPEN, WEP and WPA. Users should use passwords that are secure but no so obscure that they are unusable. The password should not be dictionary words. They should be mixed with casing and contain the user's phone number. Go to your router's website and log into the website. Find the setting for wireless security and e...

The video starts out with a man wearing sunglasses, stating that he has a hangover. He gives a dictionary definition of a hangover. He then presents an example of the alcohol he drank the night before, which was the cause of his hangover. He gives some tips on how to cure a hangover. Step 1. Drink a can of beer while taking a shower. Step 2. Drink a bottle of tropical citrus flavored vitamin water. His reason for the vitamin water is that it will rehydrate the body, replace vitamin B and has ...
Learn Arabic words using the Learn Arabic with Pictures series from ArabicPod101.com. Beautiful images clearly show Arabic vocabulary divided into units by topic.
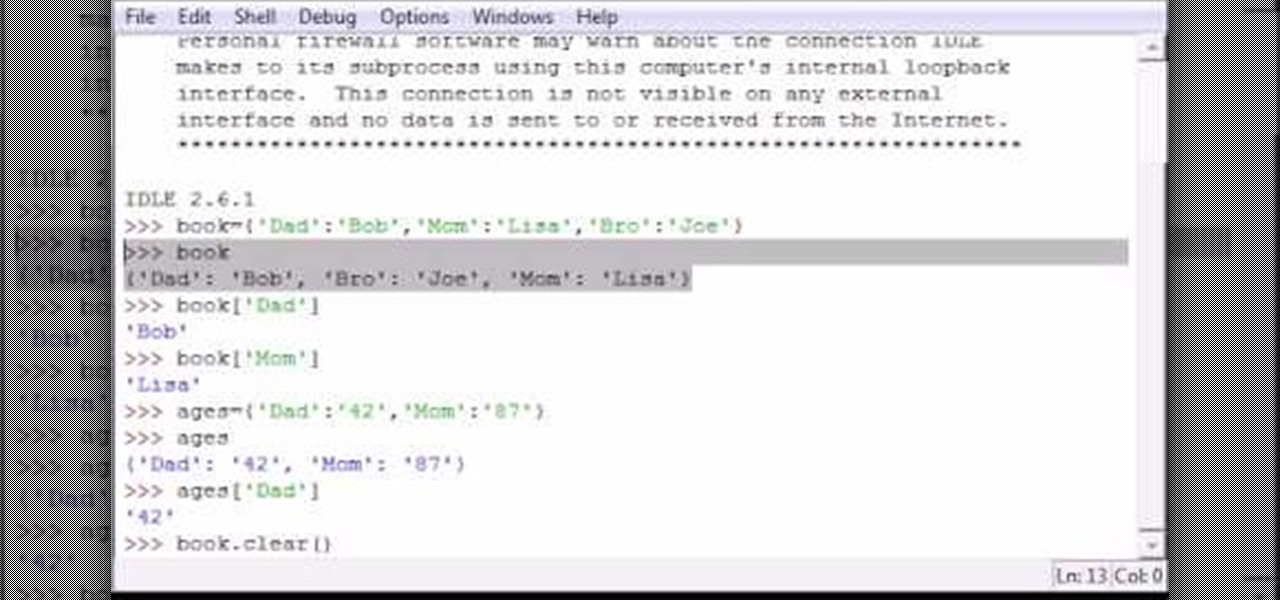
Bucky from The New Boston serves up this Python video tutorial on how to use dictionaries in Python. This is the program you use to write all of your Python code down. Dictionary!

Wouldn’t it be great if your baby could just tell you when he was hungry, thirsty, or getting tired? He can, if you teach him to sign. You will need a sign language dictionary, time, and patience. Research shows that a six month or older baby has the ability to use and understand language, although it will be months after that before a baby can learn to speak. Sign language will allow mothers and fathers to communicate with their young baby. Watch this video parenting tutorial and learn how t...

The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.
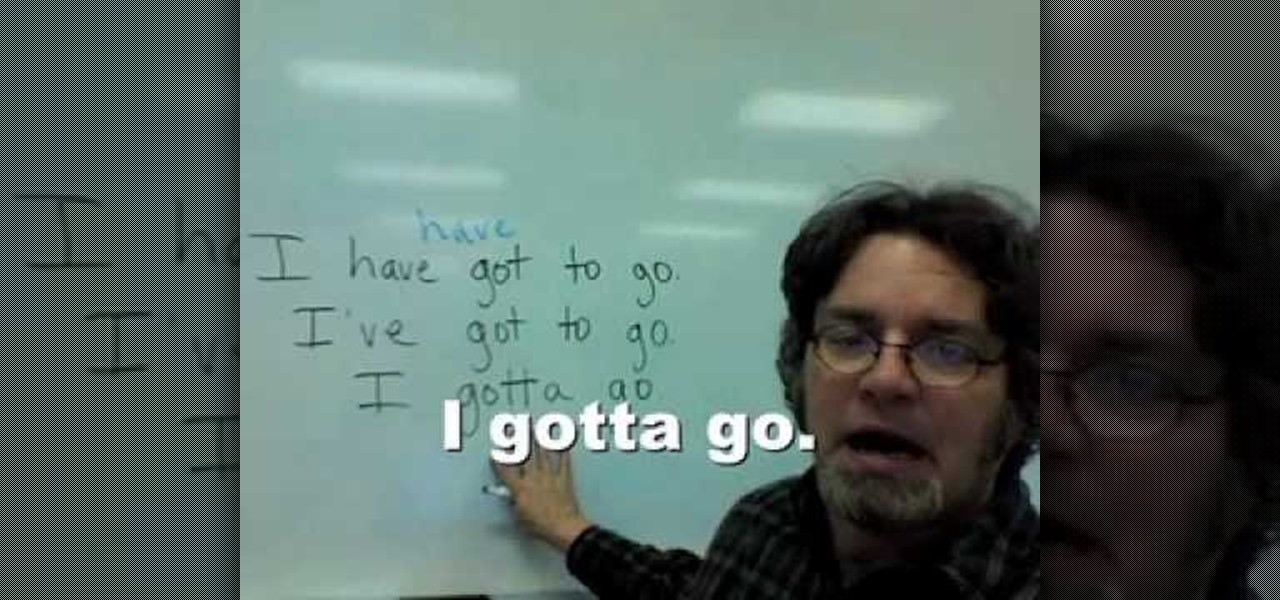
In this video it is explained how to use the words "got" "got to" and "gotta'". "Got" is the past tense of the word " get". Sometimes Americans say "have got" in place of "have" or "got" in place of "have". For example there is a sentence "I've got my wallet". Some Americans say "I have my wallet" and some may say "I got my wallet". All of them are correct. "Gotta'" is used in place of "have got to". For example there is a sentence" I have got to go". Some Americans may say

The autocorrect feature in Apple's default iOS keyboard is anything but perfect. Sometimes it can't autocorrect things on your iPhone to want you want, while other times there's a software bug that just flat out gets it wrong. These autocorrect issues can get even worse thanks to Apple's predictive text feature, QuickType, and the inability to edit your custom dictionary.

To some, SCRABBLE is just a board game to play during family game night or during a casual get-together. Others think of SCRABBLE as a mere hobby. But with any activity, there will always be fanatics—the ones who would rather sell their soul than stop—the ones with a constant yearning for self-improvement—the merciless.

Word games can expand your vocabulary skills in all sorts of exciting and creative ways. Because of this, both the iOS App Store and the Google Play Store are awash with word games, making it hard to differentiate between good and bad titles. This is especially troublesome if you're looking to purchase a game, as everyone hates to waste hard-earned cash.
Welcome back, my novice hackers! This is the third installment of my Python scripting series. If you haven't read the previous two articles, take some time now to go back and read Part 1 and Part 2 before you proceed here.

To share a song or album to family and friends, it's as easy as copying its link in the app and pasting that into a message. However, not everyone uses the same music streaming service, so a link to an Apple Music song won't do a Spotify, Tidal, Pandora, Deezer, or YouTube Music subscriber any good. If you're on an iPhone, though, there's an easy way to convert links from one service to another.

Despite its name, the Frequently Used section on your iPhone's emoji keyboard features both frequently and recently used emoji, and it may contain emoji you've never even touched. If you want to remove all of those recommendations, there's an easy way to reset what you in Frequently Used to the defaults.

Sometimes you need a password to gain access to an older running Windows system. Maybe it's a machine in your basement you forgot about or a locked machine that belonged to a disgruntled employee. Maybe you just want to try out your pentesting skills.

Chrome apps and extensions are powerful tools for students: they can help optimize your web browsing experience by helping you take notes, check your grammar as you compose documents and emails, and even help you squeeze a little more juice out of your laptop's battery by freezing unused tabs and optimizing YouTube streams.

In this article, we will build a parallel password cracker using the techniques explained in the previous part. As SHA-512 is the digest function that Kali (and most modern Linux distributions) use to store our passwords, we will make a SHA-512 password cracker.

People who know that I am a professional hacker often ask me what they can do to make their computers and personal information safe from people like me. The answer, of course, is that nothing will make you completely safe, but there are a number of measures any computer user can take to reduce the chances of being a victim of a hacker.

Welcome back, my hacker apprentices! Last week, I started off my password cracking series with an introduction on the principles and technologies involved in the art of cracking passwords. In past guides, I showed some specific tools and techniques for cracking Windows, online, Wi-Fi, Linux, and even SNMP passwords. This series is intended to help you hone your skills in each of these areas and expand into some, as yet, untouched areas.
In the midst of furious finger typing on a small non-tactile screen, you're sure to make mistakes—so the majority of keyboards have autocorrect. Generally it works pretty well and is a welcomed feature.

If you're serious about keeping your diary for your eyes only then you might have to take some drastic steps. There are some very clever ways to distract from, encrypt, hide, or disguise a diary if you're willing to put in the work.

Welcome back, my apprentice hackers! In this series on password cracking, I have been attempting to develop your skills in the age-old art of password cracking. Although it might seem like a simple and straightforward exercise, those of you who have attempted password cracking know that there are many subtleties to this art.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.
Have you ever gotten into a taxi in a foreign country and had trouble expressing where you want to go? Or tried to ask a waiter what's in the dish you're eyeing on the menu? Perhaps you just want to know what's happening in another country, and the news outlets don't offer a translated edition.
The next big iOS version for iPad, iPhone, and iPod touch was revealed by Apple at WWDC 2018 and dropped for everyone on Sept. 17, 2018, less than a week after Apple revealed the new iPhone lineup. We've rounded up all the big picture items and secret features and changes we could find so you know exactly what to expect when updating to iOS 12 on your iPhone.
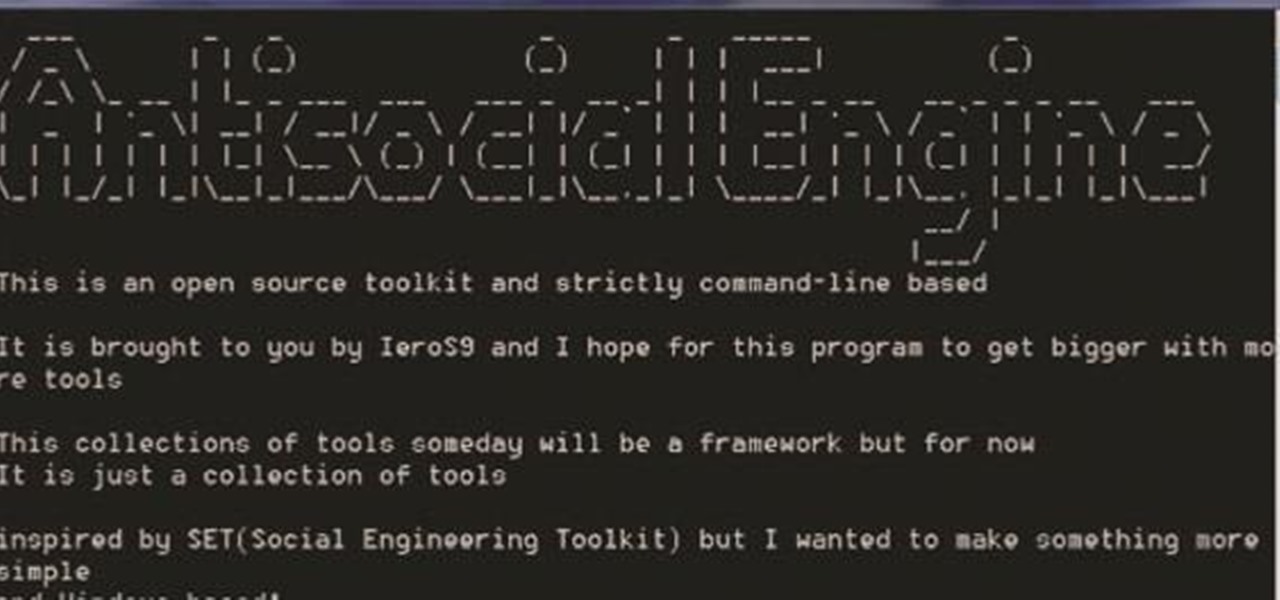
A.E Hi again this is my second post on nullbyte. The first one was on how to make a remote screenshot captor, now I will give you a presentation for a project of mine(I have named It Antisocial Engine) that It is not something extraordinary but will help many guys.

There are over 1.6 million apps on the Google Play Store, which makes it the largest collection of mobile apps on the planet. However, a large portion of this total is occupied by apps with overlapping functions—think social media, news, weather, music players, and various other categories where developers compete against one another to garner the largest user base.

Amazon is currently offering over $80 in free Android apps in the Amazon Appstore, but only for Friday and Saturday, so make sure to grab them quick before they all go back to normal price. Highlights include the Fleksy Keyboard (normally $3.99), Oxford Dictionary of English with Audio (normally $24.99), and EasyTether (normally $9.99).

Welcome back, my neophyte hackers! Several of you have written me asking how to crack passwords. The answer, in part, depends upon whether you have physical access to the computer, what operating system you are running, and how strong the passwords are.

Beginners learning brute-forcing attacks against WPA handshakes are often let down by the limitations of default wordlists like RockYou based on stolen passwords. The science of brute-forcing goes beyond using these default lists, allowing us to be more efficient by making customized wordlists. Using the Mentalist, we can generate millions of likely passwords based on details about the target.
Sure, emojis are all the rage, but there's not an emoji for every emotion or feeling just yet. That's where emoticons come into play, emoji's older typographical sibling. Unfortunately, emoticons can be hard to type out, easy to forget, and ASCII art, in general, can be pretty time-consuming to create from scratch — but there's an easy way to forgo all these issues — make keyboard shortcuts.
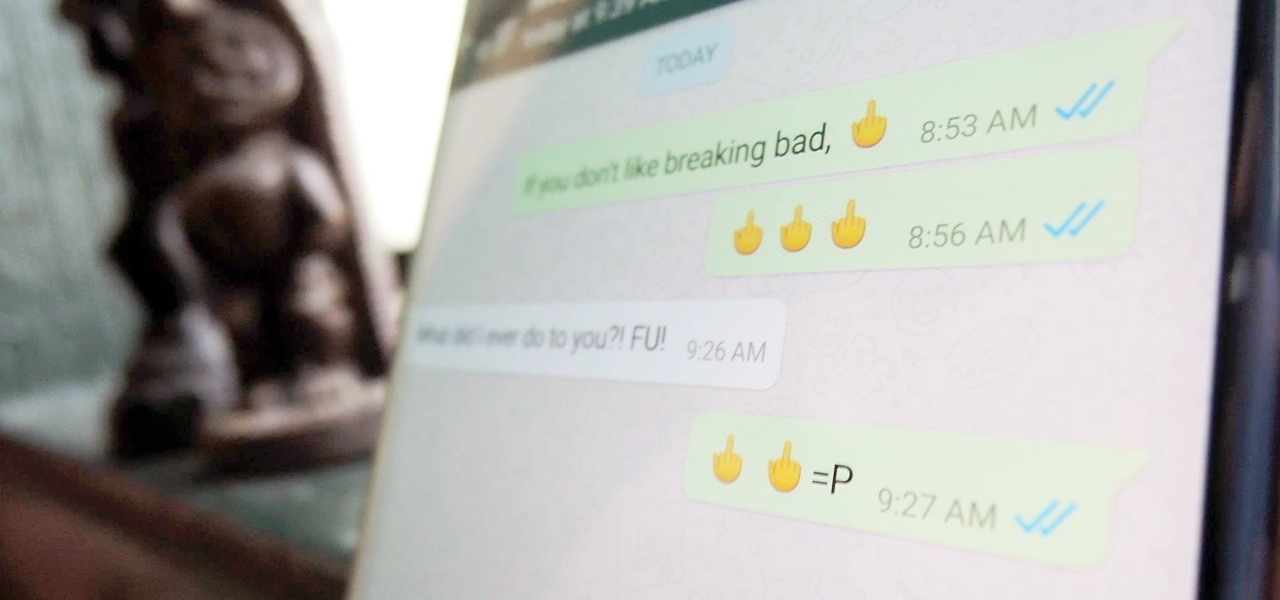
Hidden deep in WhatsApp's emoji database is a middle finger emoji, and there's a really easy way to use it. Much like Spock's "live long and proper" Vulcan salute, this one can be used simply by copying and pasting the emoji from our tweet. Note that the emoji, for now, does not display properly on iOS devices, but it can still be sent. So if you're in a conversation with an Android or computer user, they'll see it just fine.

Hello, multicolored-hat hackers!

SCRABBLE was invented by Alfred Mosher Butts, an architect in New York, in an attempt to make a word game that combined anagrams and crosswords, which involved chance, luck and a great degree of skill. Together, Butts and game-loving entrepreneur James Brunot, refined the game and made the games by hand, stamping letters on wooden tiles on at a time. They eventually came up with the name SCRABBLE, which means "to grope frantically."

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.