This small but very powerful electrolyzer produces gas that increases the fuel mileage of your car. The elctrolyzer runs on baking soda (4 volts/cell) and produces hydrogen. Electrolyzers in general are machines that uses a direct electric current to drive a chemical reaction that would otherwise not occur on its own.

If you are stuck in the wild and run out of matches, dip into your food supply and start a fire that way. This handy tutorial will show you how to stay warm with nothing but a can and a chocolate bar.

Check out this video tutorial to see how to use the BD Genie Safety Lancet blood sampler device. BD Genie Lancets are high quality, safety-engineered, single-use capillary blood sampling devices. They offer a permanently retractable blade or needle feature that minimizes the possibility of injury or reuse. BD offers a full range of blade depth and needle gauges for sufficient blood volume in multiple sample requirements. All Genie's can be used in conjunction with BD Microtainer Tubes.

Despite Samsung's long running support for Wi-Fi Direct, most users still struggle to transfer files between their devices. Whereas Apple has AirDrop, Samsung's previous solution wasn't so obvious. With the Galaxy S20 and Galaxy Z Flip, Samsung hopes to correct this with "Quick Share," a file transfer system that still uses Wi-Fi Direct but makes it easier to use.

QR codes are supposed to make life easier, but having to install potentially shady third-party apps just to scan one is more trouble than it's worth. Thankfully, there's a QR code reader built into all Google Pixels, but you wouldn't know it unless you stumbled across the feature.

Augmented objects in the classroom are closer than they appear. Within celebrated the close of summer with Wonderscope's unveiling of a fourth installment in its iOS app, titled Clio's Cosmic Quest.

Ever since the introduction of Google's SafetyNet feature, it's been an ongoing battle with apps trying to detect root access. For a while, there was a lot of back and forth between Magisk and certain apps. Pokémon GO was a high profile example of an app aggressively checking for anything related to root. Luckily, Magisk has made great strides to keep apps from detecting root for good.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

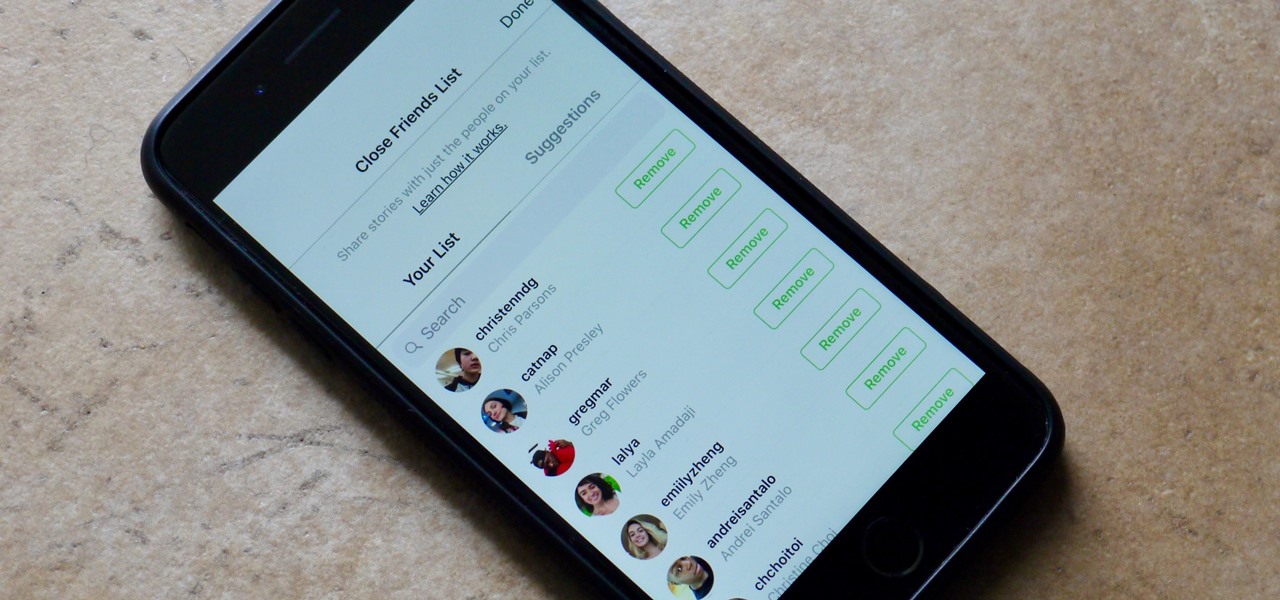
Stories make sharing your day-to-day highlights fun on Instagram. However, other than choosing who to hide stories from, by default, stories don't have much privacy control, especially if your Instagram account happens to be public. Instagram recognizes this flaw, which is what its "Close Friends List" is all about.

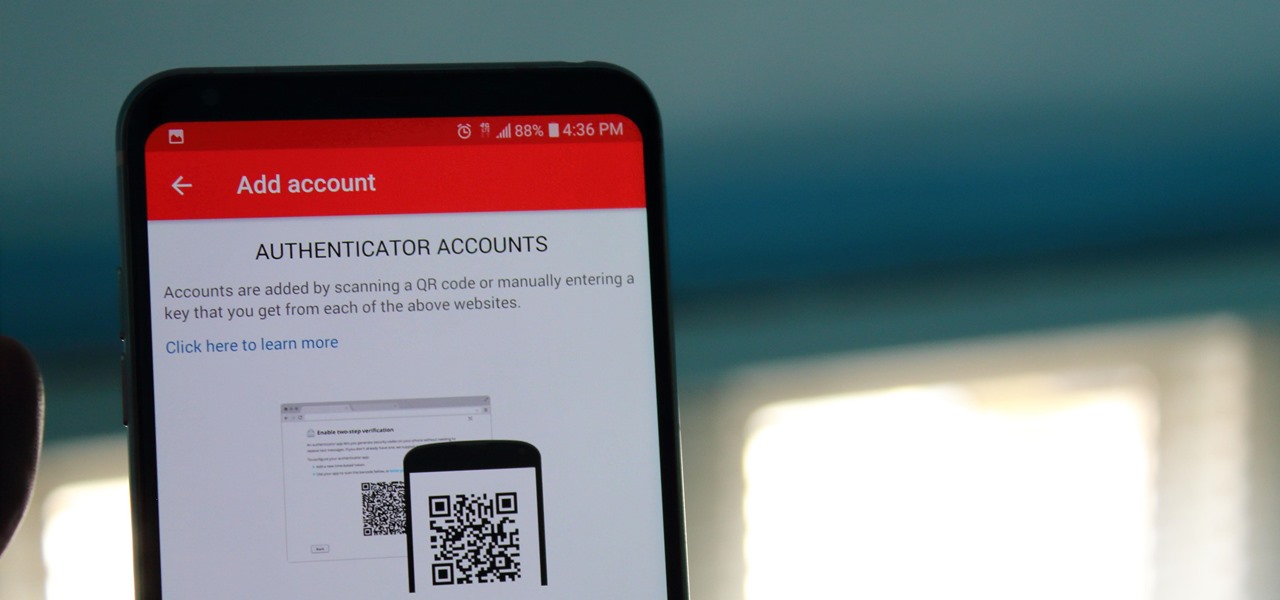
If you didn't get the memo, passwords aren't enough protection for your online accounts. Even a long and complex password offers only one line of defense which can falter. Two-factor authentication adds an additional layer, bolsters your defense, and decreases the risk of your account becoming compromised.

Consumers are chomping at the bit for augmented reality smartglasses from Cupertino's finest, but one market analyst is saying not so fast, Apple fans. Meanwhile, automotive AR is gaining speed, with the latest milestone coming courtesy of a major investment in waveguides by Continental. And although mobile AR apps have already arrived, retailer Target is taking a different approach. So why is Target tinkering with web-based AR? Answers below...

Noted analyst Gene Munster is predicting that Apple's initial entry into the augmented reality wearables category will be a year later than previous reports have estimated.

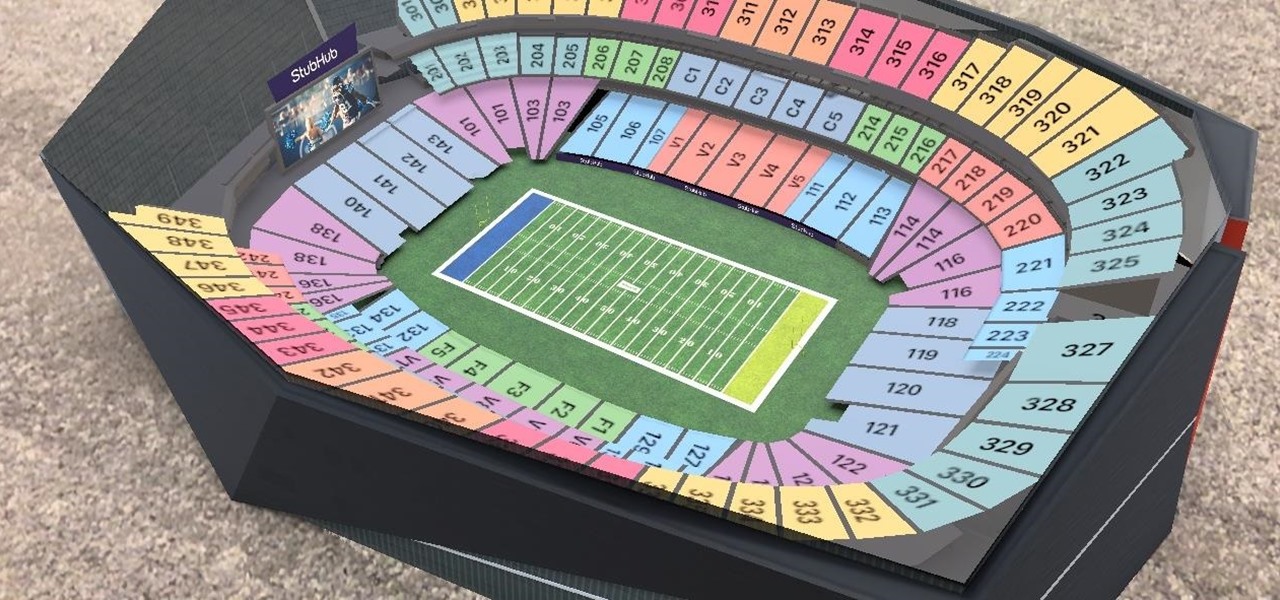
While the Minnesota Vikings have a realistic chance to become the first team to play in a Super Bowl on their home field, there will still be fans attending Super Bowl LII who will be in unfamiliar surroundings.

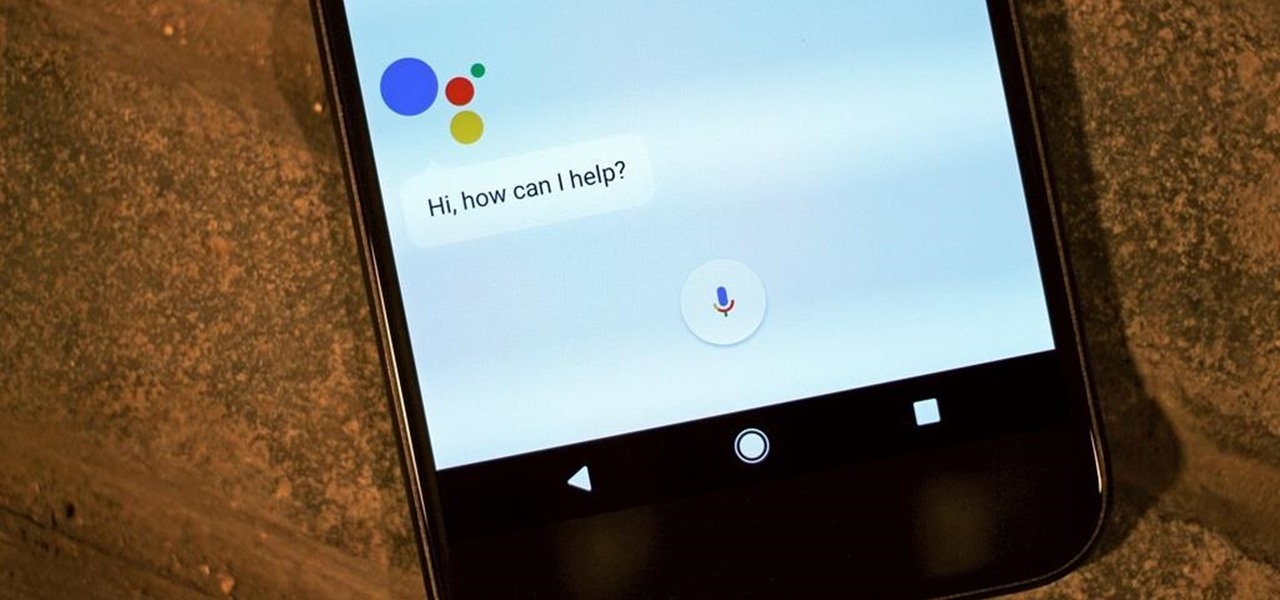
Rumor has it that Google Assistant will be coming to an iPhone near you. A "trusted source" broke the news of GA's arrival on iOS to Android Police ahead of Google's I/O conference this week.

How can bacteria that lives in the throat of 10%–35% of people—without causing an infection—cause life-threatening meningitis and sepsis in others?

An advance in the race to stop birth defects caused by Zika-infected mothers has been made by a team of researchers from Rensselaer Polytechnic Institute in Troy, New York. They have identified the process Zika uses to gain entry into the placenta, and published their findings in the journal Biochemistry.

This is a whole new level of "Paleo," guys. Seriously: there's nothing more primal than a giant hunk of meat cooked in direct flame. Fancy grills and grill masters be damned—this method of cooking your meat is both the past and the future.

Google has an intriguing feature called Nearby that lets users share content without being on the same Wi-Fi network, or without even exchanging contact info first. Instead, the function uses an array of standard smartphone features, as well as subsonic sound, to identify other devices that are in the room, then makes a secure connection to transfer any data.

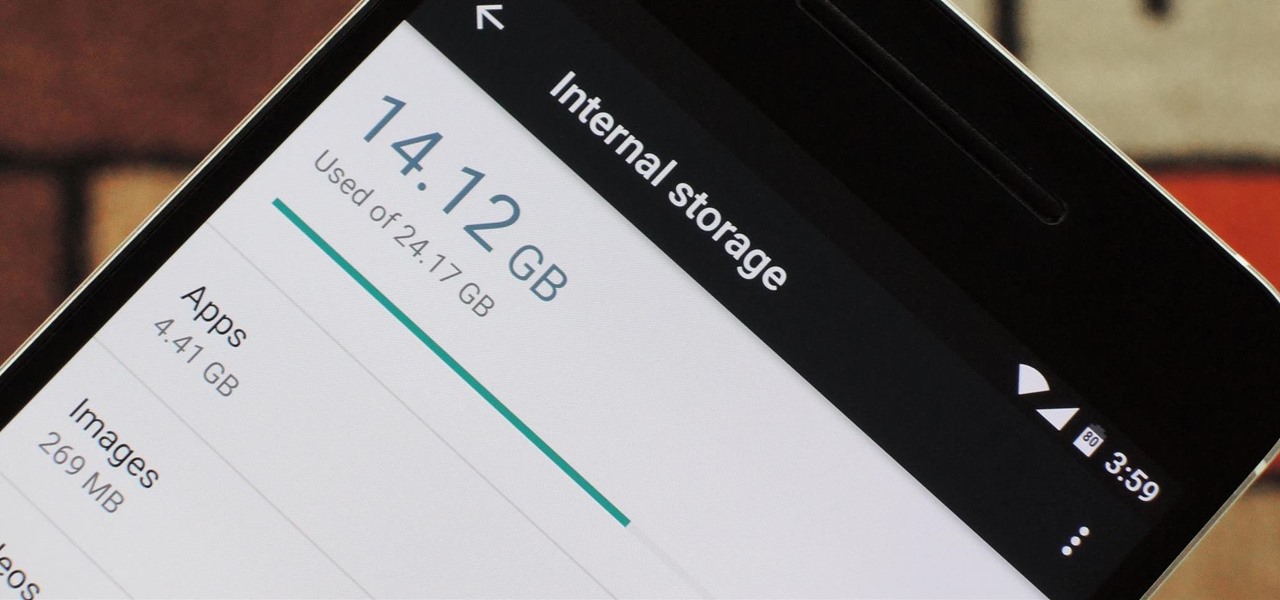
Fewer and fewer Android phones are being released with SD card slots, so it's always a struggle to make sure you have enough free storage space for your photos, videos, and music. Things like app data and cache slowly build up as you use your device, which means your available storage number gradually decreases over time.

Researchers at the cyber security firm Zimperium have recently uncovered a vulnerability in roughly 95% of Android devices that has the potential to allow hackers to take total control over your phone with a simple picture message (MMS). The gritty details of this exploit have not been made public yet, but hackers now know the general framework for this type of attack, so you can be certain that they'll hammer out the details in no time.

When it comes to smartphones, the biggest complaint voiced by most users is battery life. Sure, it's unrealistic to expect your Android device to run for weeks without a recharge, but many folks struggle to even make it through the day without having to top off their battery.

If you're a fan of double-tap to wake gestures, you're going to love the newest app from ElementalX developer Aaron Segaert. On supported kernels, it allows you to associate custom apps and activities with each of the wake gestures you've set up, which will immediately be launched even with the screen off.

When you're actively using your phone, a certain amount of battery drain is to be expected. But, if your device is just sitting in your pocket draining its battery, that's when you need to take action.

Welcome back, my aspiring hackers! Many of you have installed Kali Linux as a virtual machine (VM) using VMware or VirtualBox, while others have installed Kali (or BackTrack) in a dual-boot system. The drawback to installing these hacking systems as a VM is that it then requires an external wireless adapter (your wireless adapter is piped through the VM as a wired device, eth0), but it makes for a great place to test your hacks while honing your skills.

When the Nexus 5 debuted, one of its coolest features was the fact that you could say "OK Google" any time you were on the home screen to launch a Google Voice Search. This feature was ultimately made available for other devices by way of the Google Now Launcher.

Multitasking has always been one of Android's strengths relative to other mobile operating systems. As the first cell phone OS with "true" multitasking, Android's been ahead of the game in this department for quite some time.

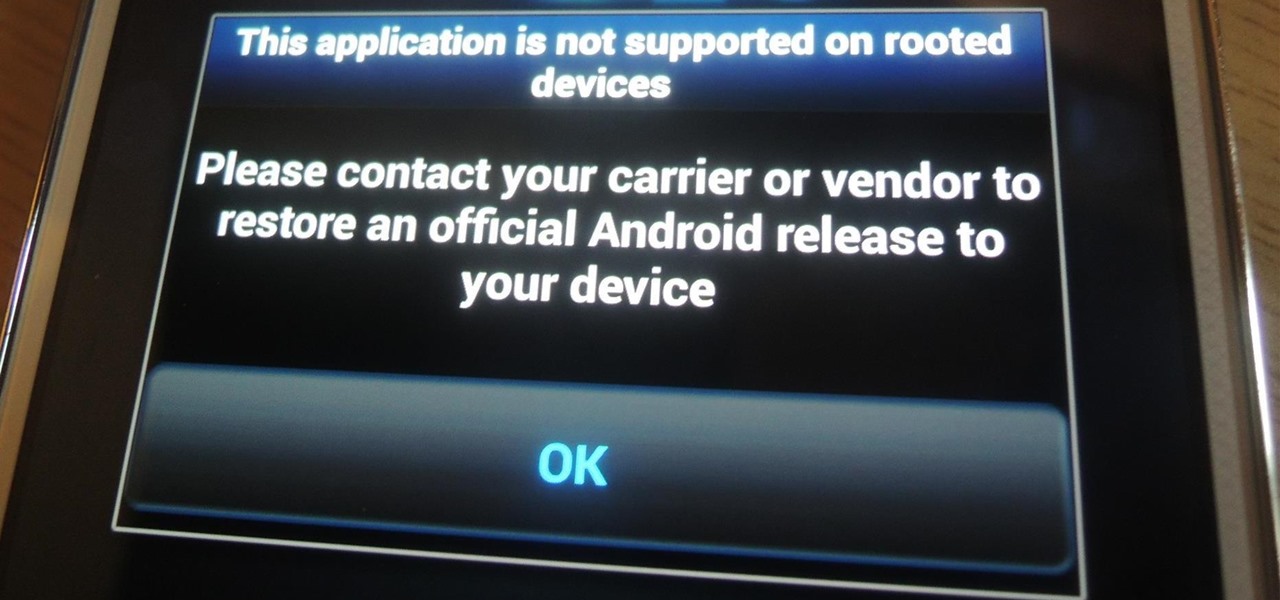
As a preventative measure against exploitation, certain Android applications won't work if your device is rooted. Opening one of these apps that detects root will typically end up with a warning and an inability to access its features, like in the picture below. AS IF!

Is "Last Resort" Steampunk? Well, no. I mean, how could it be?

Emilie Autumn is a fun, unique singer who dresses up like the hybrid of a doll and pin up girl. Slightly kooky yet adorable at the same time, the singer is truly one who doesn't care what others think of her personal style.

The first step in this video is to draw a rectangle on a piece of paper to gauge the length of the hair stokes. The artist then makes long pencil marks along the inside of the rectangle that are much less defined towards the middle. It is explained that you need to go in one direct with your pencil strokes as going back and forth gives an unrealistic final product. It is shown that you must begin at the beginning of the hair source and bring the strokes downwards for more realism. Four exampl...

In this tutorial, we learn how to know when a girl is interested. First, always look for eye contact with women. This is a girl showing that she wants you to come over and talk to her and that she is interested in you. For the most part, a girl will not come over and talk to you, she will give you signs for you to come talk to her. Also check out her body language to see if she is interested in you. Focus on the direction and interest of her body, make sure she is directed towards you and lea...

In this video, we learn how to bring your Cuban spouse to Canada. First, you need to have the correct documents which prove your identity and marriage status. You will also need marriage certificates from previous marriages stating that they are dissolved. After this, you will need to have them notarized, then travel to Cuba to obtain new documents for you and your future spouse. The authorities will direct you to the appropriate offices, then you will need to pay the fee for filing these pap...

In this Language video tutorial you will learn how to report another person's words. In other words how to restate what someone else said. This video focuses on two aspects. #1. What's the difference between quoted and reported speech? #2. When can we use say and tell? In quoted speech you quote the exact words spoken by a person within inverted commas or quotation marks. It is also called direct speech. Here is an example. Jennifer said, "I like birthdays." Whereas, reported speech does not ...

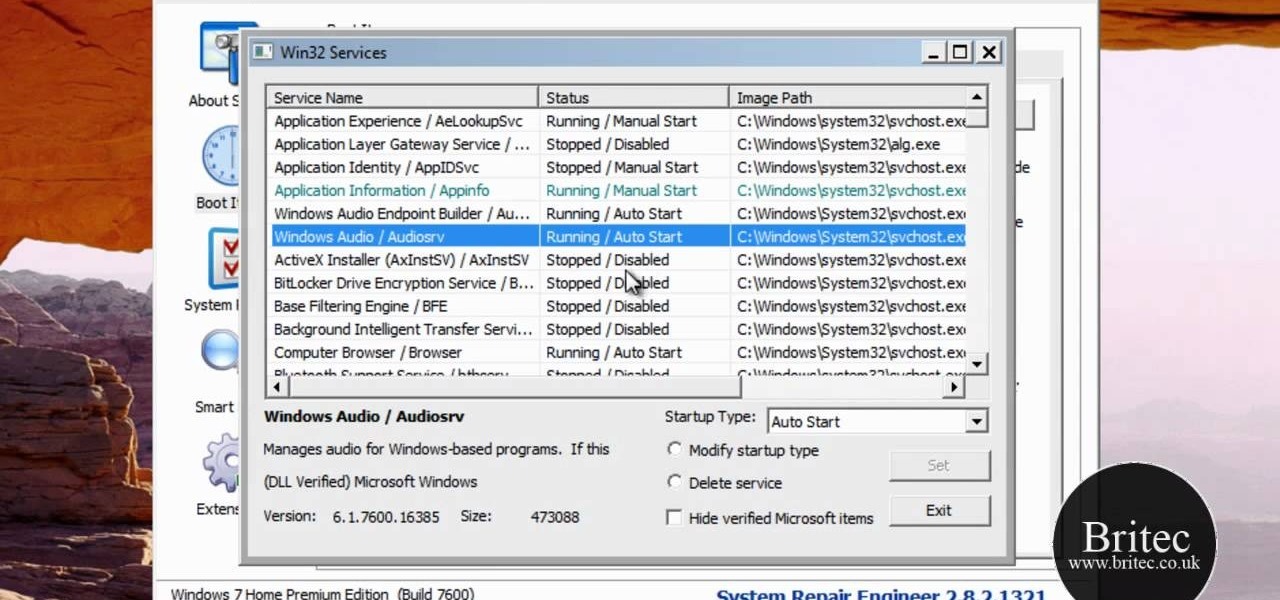
Your Windows computer may be experiencing some issues, and those issues may be a direct result of computer viruses and malicious software from the internet. One of the simplest ways to find these issues and repair them is by using a freeware program called System Repair Engineer (SREng). But that's not all it can do… check out the video to see a basic overview for using SREng.

In this tutorial, we learn how to stream web content to your PS3. If you want to do this for free, you will go to PS3 Media Server. Once on this site, you will download their player, then you will be able to stream content from your computer straight to your PS3. This will give you real time audio and direct streaming of movies. You can do this one other way, which will cost you $49.99, the website you will visit is PlayOn. When you download this, you will be able to stream advanced content t...

In this tutorial, we learn how to set a passcode for your iPhone or iPod touch. First, go to your main menu and then find the "settings" button. Then, click on "general" and find "passcode lock". You will now be prompted to enter a passcode into your phone, then re-enter it. Now, you will be directed to a menu where you can decide how often you will have to enter your password, and if you want your password to be turned on or off. Now, when you turn on your phone you will be prompted to enter...

Learning English may seem like fun, but it's not. It's one of the hardest languages to learn, because there are so many different ways that sentences can be created. So it's important when learning the language, to understand the grammar behind it.

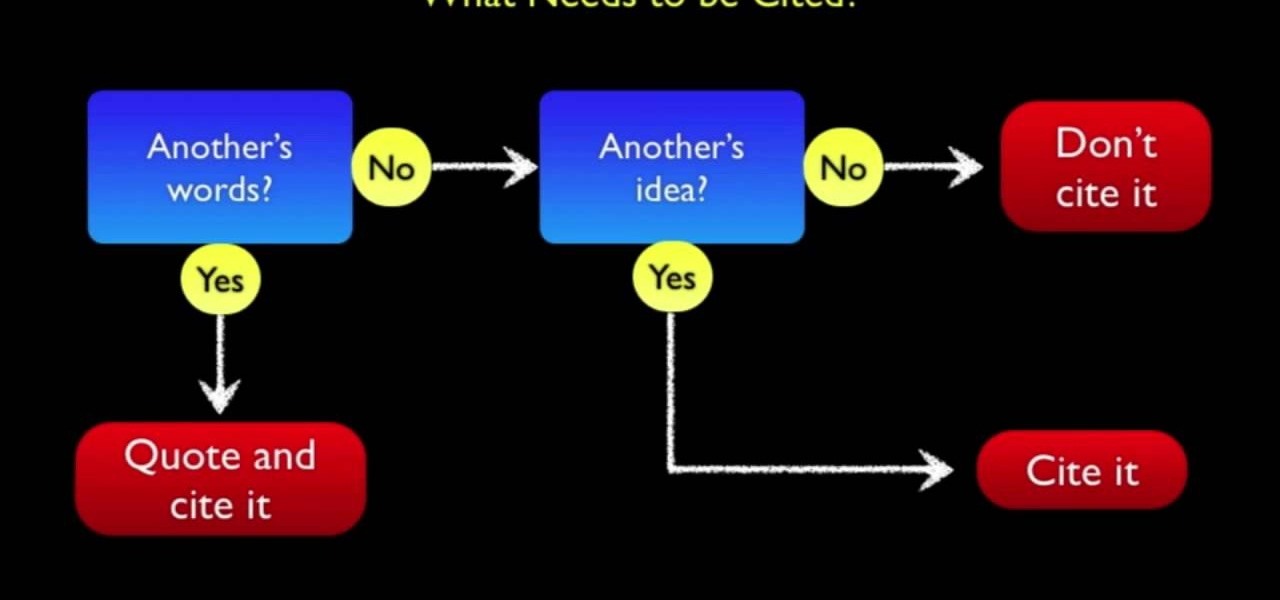
Writing papers can be a long, difficult process that can take up any sutdent's Friday night or worse: weekend. It's a common fact that most students need to cit a source when using a direct quote or piece of information obtained from any magazine, book, or even film. But a big problem is that there are some who do not undrstand the basic need to cite correctly in order to avoid plagiarism. Not doing so can result in some bad things happening for that pupil. So sit back, pay attention, and fin...

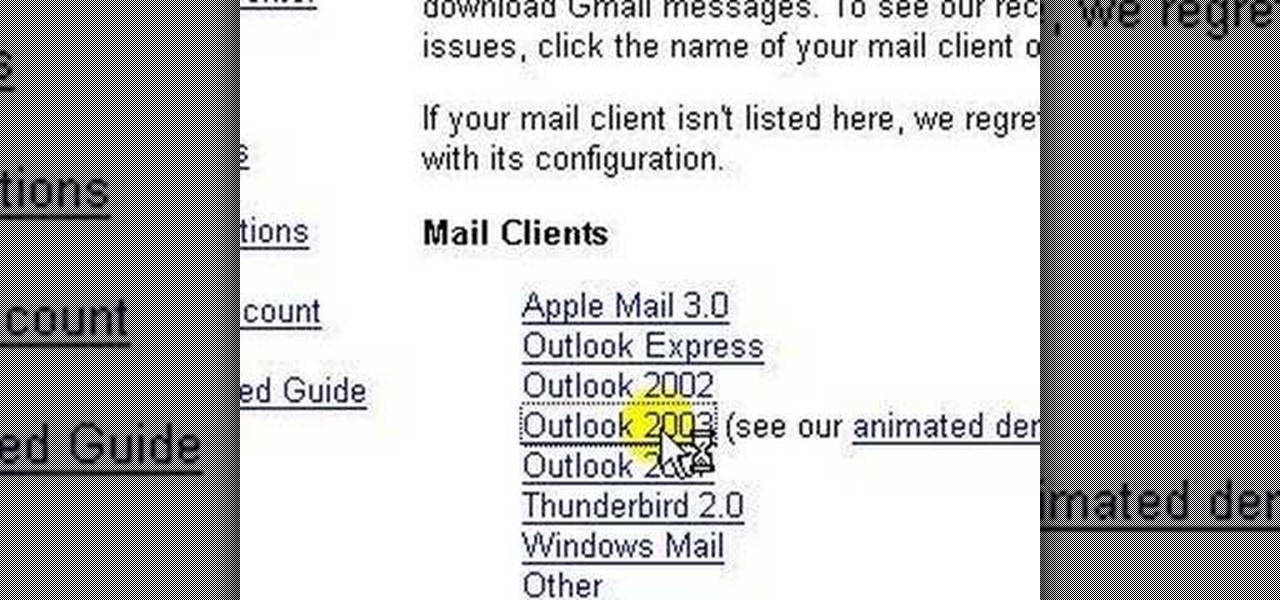
lakercoolman shows us how to set up our gmail account with this quick tutorial. Basically outlook express is a program that helps us to organize our email with added features such as contacts, to do lists and calender entries. Its an offline email client that allows us to work offline and also lets us set up exchange servers aswell. Ohter email servers such as hotmail and yahoo charge for thios service but the advantage of gmail is that IMAP or POP access is free. in ofer to set up, navigate ...