I recently posted a Tutorial about setting up Dendroid: http://null-byte.wonderhowto.com/how-to/setup-dendroid-android-rat-0167299/. I have worked the last 5 days on getting the Dendroid Binder, given with the Dendroid Source, working. This solution only works on Windows systems!

In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

Hey readers! This tutorial will be the entry point for the introduction of buffer overflows. Something like requesting user input is a very common place for vulnerabilities to pop up and we will definitely have fun while trying to make programs crash. But for now, let's start with how we can get input from a user.

Welcome back, my novice hackers! More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not only using smartphones for voice communication, but also web services, email, SMS, chatting, social networking, photography, payment services, and so on.

Hi , Today i will show you how to do HID Keyboard Attacks With Android BUT without using Kali NetHunter BUT You will need to install custom kernel to your Android device, that will add keyboard+mouse functions to it's USB port,So Lets Get Started
I wrote a python script that allows you to easily ask what service runs on a specific port and vice-versa. Now, I am sure that such a program already exists on our lovely linux OS's, but... I didn't think of that before I started, and haven't found it yet. So if you haven't found it yet either, maybe you'll find this of some use. It's just called getport. If I have a port number, and want to know what services run on that port, I do:

Welcome back, my tenderfoot hackers! As you know, DNS, or Domain Name System, is critical to the operation of the Internet. It provides us with the ability to type in domain names such as www.wonderhowto.com rather than the IP address. This simple service saves us from having to memorize thousands of our favorite website IP addresses. Instead, we simply type in a domain name to retrieve the website.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!

If you pre-ordered your Samsung Galaxy S4, it might very well be possible that you're reading this on your brand spanking new Android device. As is commonplace with the release of popular smartphones, rooting instructions are usually released simultaneously. I mean, what's the point of paying so much for an expensive phone if you can't have a little fun? Android developer Dan Rosenberg (aka djrbliss) recently announced that you can root your Samsung Galaxy S4 using the root exploit he origina...

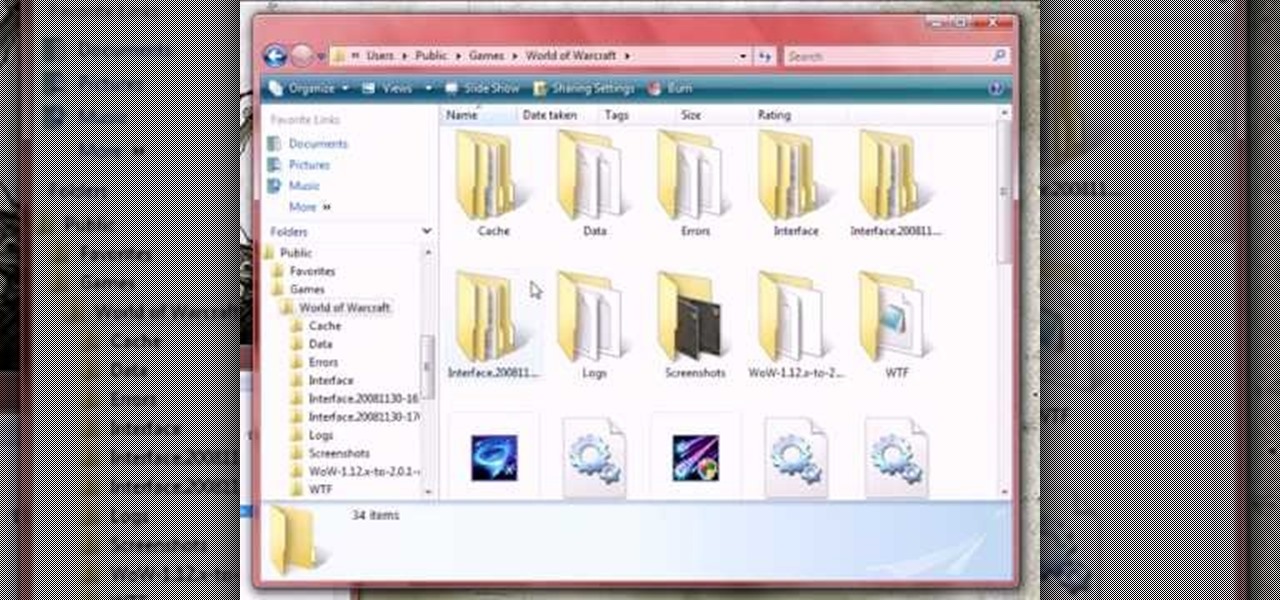
In this tutorial, we learn how to clear your World of Warcraft cache. First, you will go to your computer, then the local disk (C:), then users. From here, go to the public folder, then click on 'games', and then 'Word of Warcraft'. Once here, you will need to delete the 'cache' and 'wtf' folders. Next, you can exit out of this and continue to play your game as normal. This will clear out history from your game and make it load faster than before. If you aren't a Vista user, you will be able ...

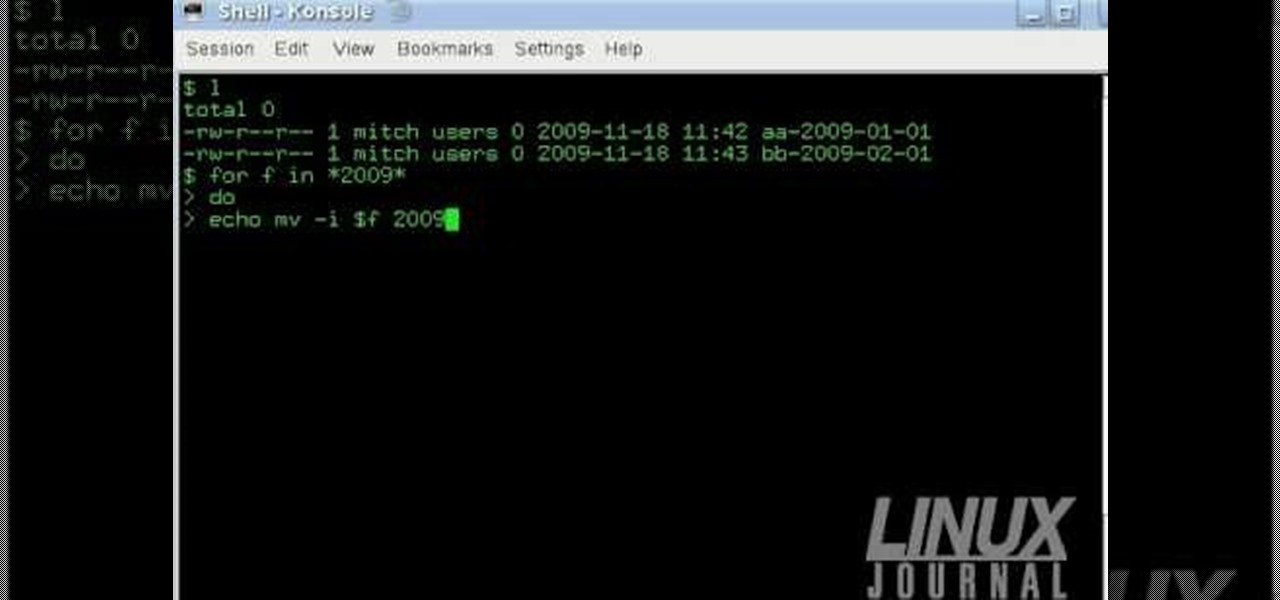
The Linux command shell provides a very powerful interface for doing various system tasks. This video explains with an example, how to use a bit of programming techniques to batch rename files with similar naming conventions.

In order to build Google Chrome extensions, you will need to familiar with scripting and codes. These are small programs that add additional functions for programmers. It is a compressed directory. These files must have a particular name: i.e. "manifest" (manifest.json). An extension will have at least one of the following: browser actions, page actions, content scripts, and utility web files.

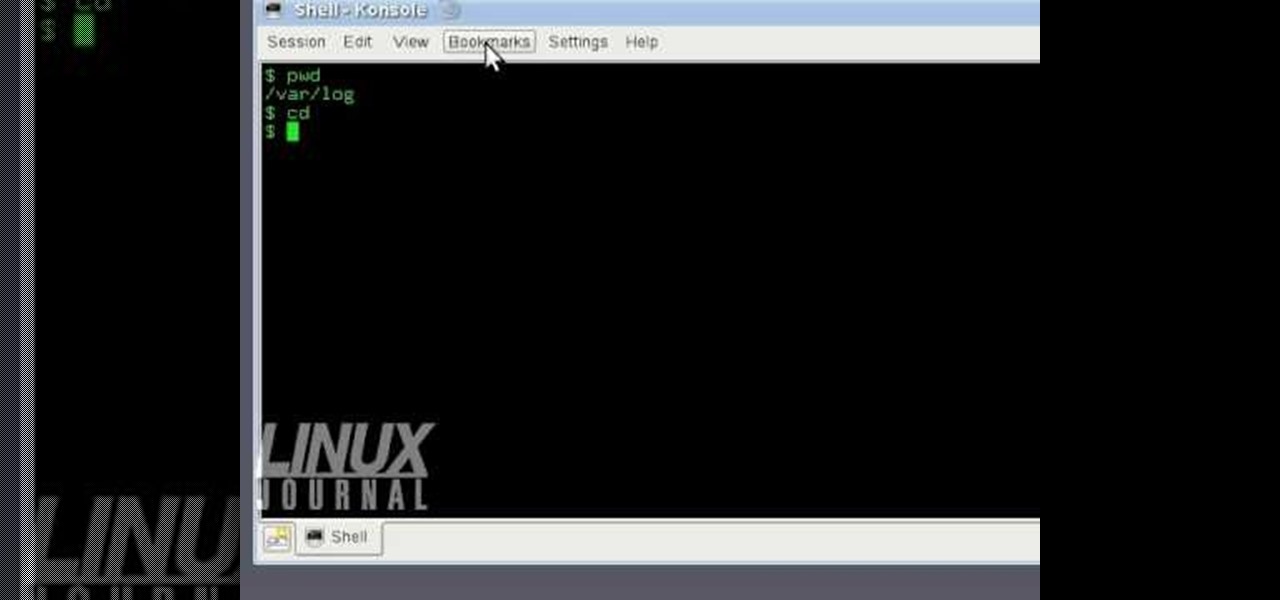
In this tutorial, we learn how to use KDE konsole bookmarks. You can add a bookmark, then go to the home directory and then you will be able to go back to where you previously were. To do this, save the bookmark of the entry that you are in. Do this by clicking the bookmark tab, then add bookmark. After this, go back to the home entry and then click on your bookmarks tab again. Once you click this, you will see your new bookmark on the bottom, when you click that it will bring you back to you...

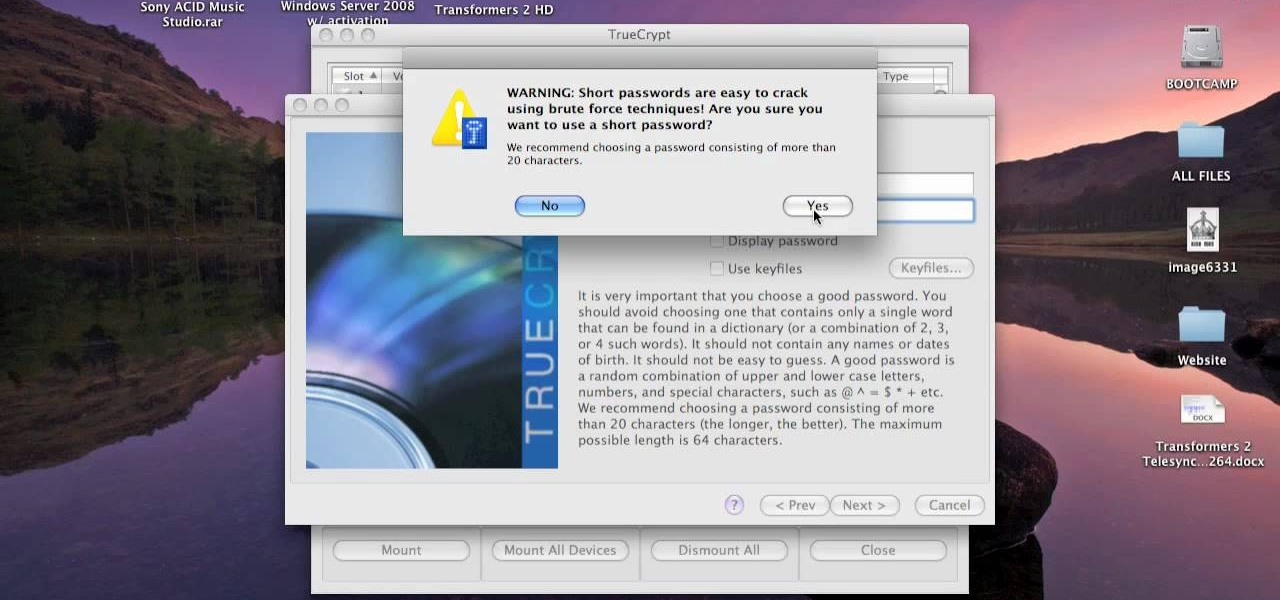
This video tutorial is in the Computers & Programming category where you will learn how to encrypt files & folders on a Mac with TrueCrypt. Open up TrueCrypt and click on create volume > create an encrypted file container > next > standard truecrypt volume > next. Here you name your file, choose the directory where you want to put the file and click 'save'. Choose the encryption type and click 'save'. Choose the volume size and click 'next'. Now type in a password and click 'next'. Then in th...

This video tutorial belongs to the software category which is going to show you how to set up a home server from behind a router using WAMP. You will need a free program called wampserver. Go to their website, download and install the program. Then click on the icon and click 'put online' and the local host comes online. To check it, open up your browser and type in local host in the search box and it will show you the default index.php file. Again click on the icon and click 'www directory'....

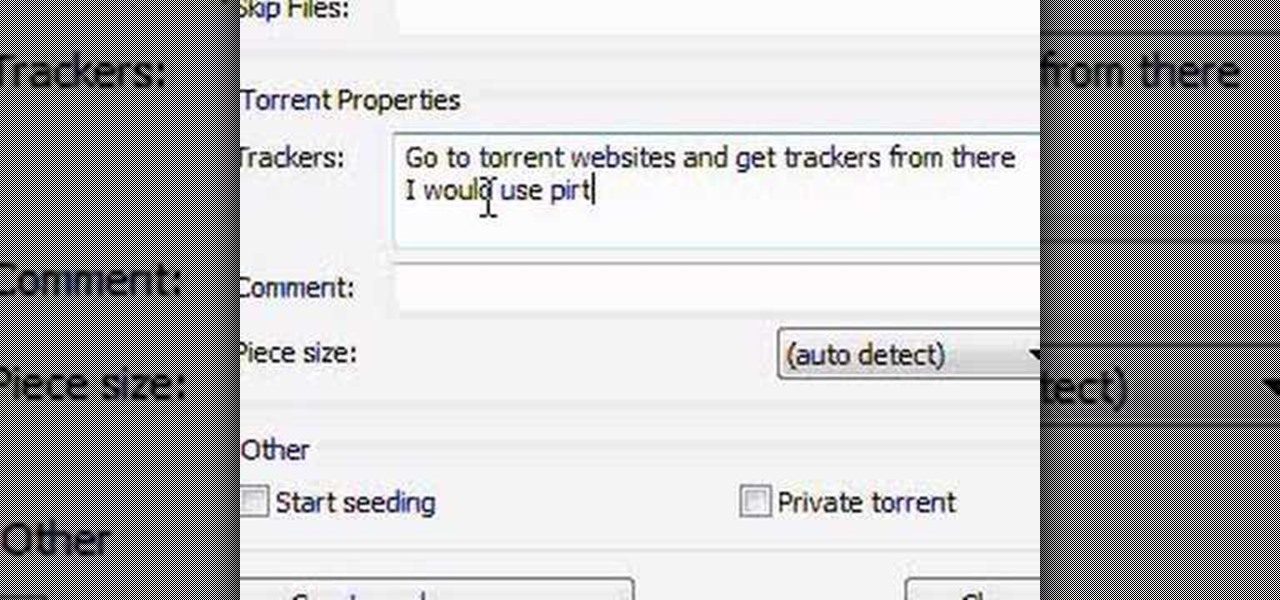
In this video tutorial, viewers learn how to create a .torrent file using u-Torrent. Begin by opening the program. Click on File and select Create New Torrent. Now select the file, select the directory and type in the tracker code. Then click on Create and save as. Once the file is created, click on File and select Add Torrent. Locate the .torrent file click OK. Now wait for the torrent file to finish downloading. This video will benefit those viewers who use u-Torrent and would like to learn...

In this how to video, you will learn how to convert a flash video to an AVI file. First, download the Pazera Converter program. Open the program. At the left hand corner, click add files and find your flv file. Next, select and open it. Once it is imported, go to output directory and choose which folder you want the new file to be placed. Go to output file format and click AVI. You can also choose MPG instead if you want. Now click the convert button at the top. You will see a progress bar. O...

In this how-to video, you will learn how to see high quality pictures of your own house. First, go to your web browser and click on Maps and Directions in the directory on the MSN website. Next, click on locations and type the address of your house or whatever place you want to see. Once this is done, click on bird's eye to get a closer photo of the area. Next, click zoom in until you get an even larger image. You can also click on the picture and drag to move around the image. This video sho...

In this video, our author, atomicinteractive, shows use how to use Fetch FTP to upload a temporary webpage. Please make sure your directory has the html file. Please find your email with ftplogin information. This will also show login information for the control panel and creating alternate email addresses.

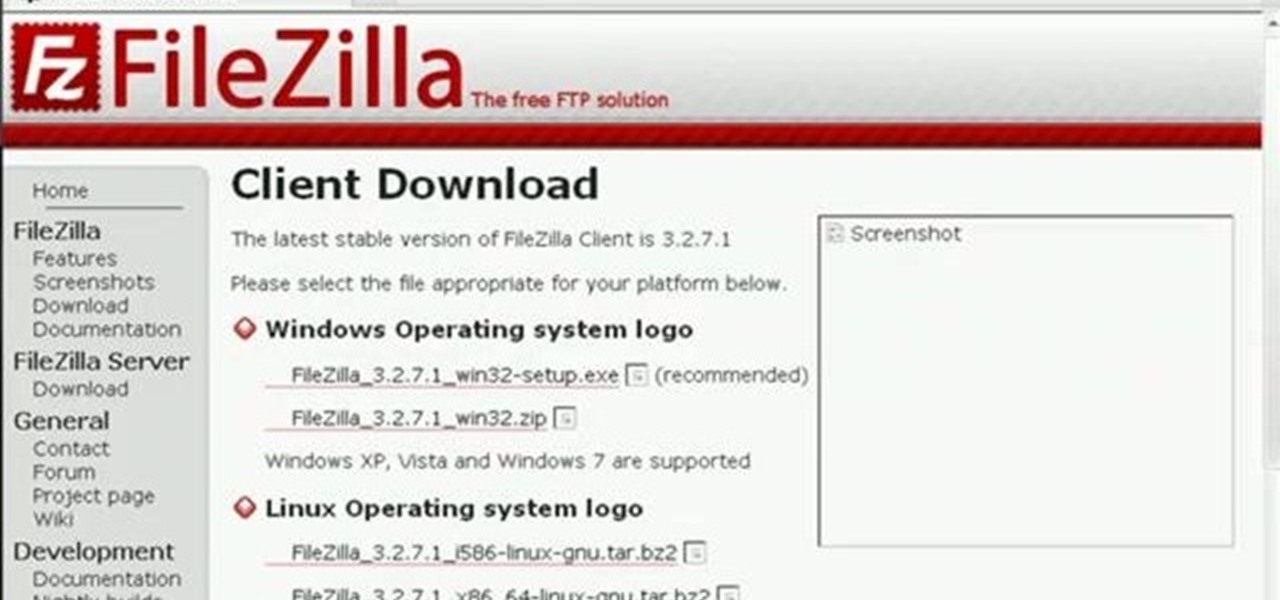
In this Computers & Programming video tutorial you will learn how to update a website with an FTP client (v† la FileZilla). Download FileZilla client from www.filezilla-project.org. Find your server IP address from your web host, which will be found in the hosting control center. In the video, it is GoDaddy.com. Open your filezilla client and put in the IP address of your web host and your username and password for your hosting account. Then click ‚Äòquickconnect‚Äô. This will connect you to ...

In this Computers & Programming video tutorial you are going to learn how to add "Hide" & "Unhide File" to the right click menu. Go to reg.exe and type in ‘regedit’ and click ‘enter’. On the page that opens up, Navigate to ‘HKEY_CLASSES_ROOT’ > directory > shell. Right click on shell and select new > key. In the ‘key’ box type ‘Hide Folder’. Now right click on the right side box of the page and select new > string value. Type in ‘HasLUAShield’ in to the box that opens up. Now on the left side...

Fetch is an FTP program for Macs (Smart FTP can be used if you don't have a Mac). These can be downloaded from Download.com

This video teaches the secrets of partitioning a hard drive on a MAC in simple steps. First open the disk utility, select the root directory of your hard drive and click partition. Now select the required partitions under the volume scheme, adjust the drive space and name them. Select the format a MAC OS Extended (Journaled) and select GUID Partition table from option if you want to boot it. Click 'Apply' to start the partitioning and when its done start using it.

This instructional video shows you how to reboot your iPod Touch 2G after shut down. First shut down the device and plug it to a computer via USB. Use the links in the description if you have the newest version of OS X. Put the device in to DFU mode by holding the home and power key for 10 seconds, letting go of the power key keep holding the home key. Download the RSlite folder from the link in the description. Open the terminal, change the directory to the Rslite folder and type the code re...

It's possible to stream a MacBook's entire computer screen without using Apple's Screen Sharing application and without opening any ports on the target device. A hacker with low user privileges on the backdoored Mac may be able to view a victim's every move in real time no matter where they are.

Ransomware is software that encrypts a victim's entire hard drive, blocking access to their files unless they pay a ransom to the attacker to get the decryption key. In this tutorial, you'll learn how easy it is to use the USB Rubber Ducky, which is disguised as an ordinary flash drive, to deploy ransomware on a victim's computer within seconds. With an attack that only takes a moment, you'll need to know how to defend yourself.

Greetings my fellow hackers, In the previous article, I discussed briefly about ransomwares and their devastating capabilities. Devastating in a way that ransomwares are not only known to encrypt files but to also lockout some specific functions of the system and hold it up for a ransom.
Hello everyone! This is my first attempt at a tutorial here. There are a couple great assembly tutorials here, and I wanted to toss my coin in the fountain.

UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - https://techkernel.org/2015/12/19/embed-metasploit-payload-in-apk-manually/

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

Well now, that was interesting wasn't it? After mission 16 you may be concerned about the fate of our universe. Fear not! You've still got a bunch of StarCraft 2 missions left to play. This video will show you how to beat mission 17: Breakout.

Supernova is coming! Prepare yourself. This video will show you how to beat Mission 19: Supernova in the StarCraft 2 single-player campaign mode. It's a great walkthrough with expert commentary throughout. SPOILER ALERT: This video contains relevant cinematics, so if you want just gameplay skip it.

The campaign is really starting to get intense now isn't it? This video will show you how to beat one of StarCraft 2's later levels, mission 21: Media Blitz. It features great commentary to guide you through the tough parts.

Did you know that StarCraft 2 has a secret mission in it's campaign mode? It's called Piercing the Shroud, and if you've already played through the game and missed it or are playing through now and don't want to miss it, watch this video, which shows you how to unlock the mission, then this video which gives you a great walkthrough of it..

Does shattering the sky sound good to you, or possibly like something that you should prevent? Mission 23 of StarCraft 2 campaign mode offers you the chance to do it. This video will walk you through it with expert commentary.

Mission 24 is yet another one of the branching-off points in StarCraft 2's lovingly crafted campaign game. This video will show you how to beat the Shatter the Sky level with expert commentary to guide you.

Here you are. One more mission. Are you ready? Or have you already died on it seventeen times? If you answered no to the former or yes to the latter, watch this video. It will give you a walkthrough of the last level with expert commentary that should allow you to beat it no problem. You're done! Now get on Battle.Net.

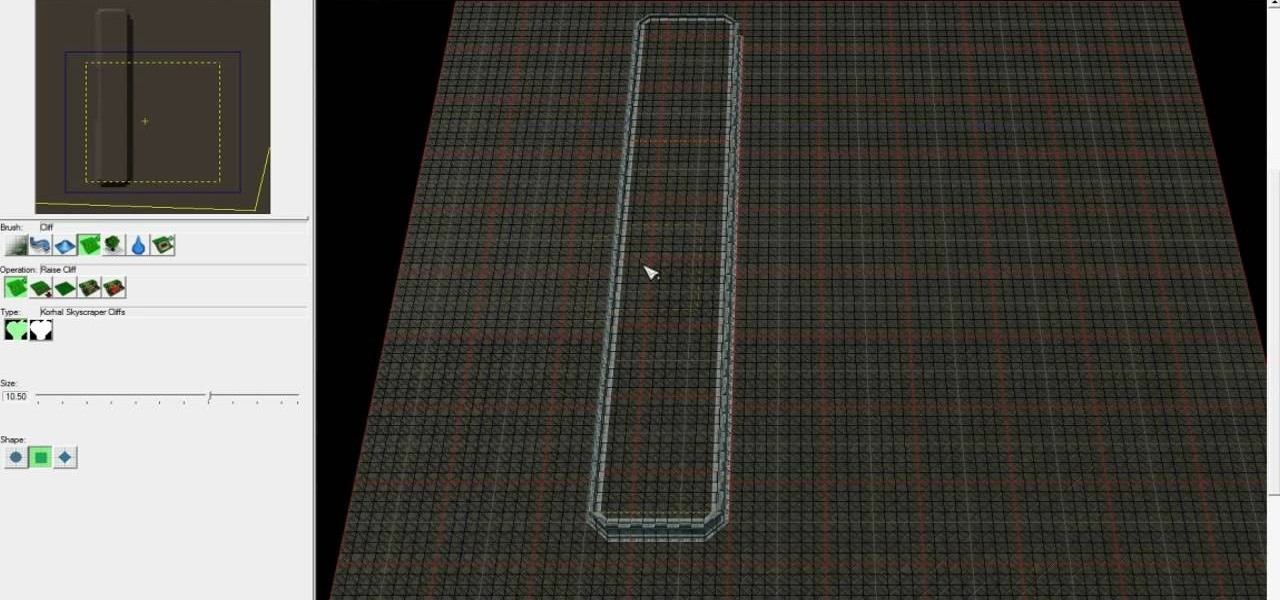
Starcraft 2, like it's predecessor before it, has a very robust level editor that allows you, the DIY modder, to create nearly any scenario within the bounds of the Starcraft 2 engine that you could imagine. We have compiled videos on how to do all sorts of fun things with it, from making RPG's and Tower Defense games to just making you dream Starcraft 2 level. This video will teach you how to create a complete and advanced Tower Defense game in the Starcraft 2 editor, allowing you to create ...

Starcraft 2 is finally upon us after 12 years of waiting, and it is just as majestic as you would hope it would be. If you're new to the series or just haven't played in five years, the barrier to entry for the unskilled can high, especially if you prefer playing online multiplayer. Fortunately for you, we've compiled videos on just about everything you need to know about the game, including strategies and tips for winning with different races in different modes and situations, and even how t...

Starcraft 2, like it's predecessor before it, has a very robust level editor that allows you, the DIY modder, to create nearly any scenario within the bounds of the Starcraft 2 engine that you could imagine. We have compiled videos on how to do all sorts of fun things with it, from making RPG's and Tower Defense games to just making you dream Starcraft 2 level. This video will teach you how to create a WoW-like camera and control scheme in the SC2 editor, allowing for WASD control of your uni...