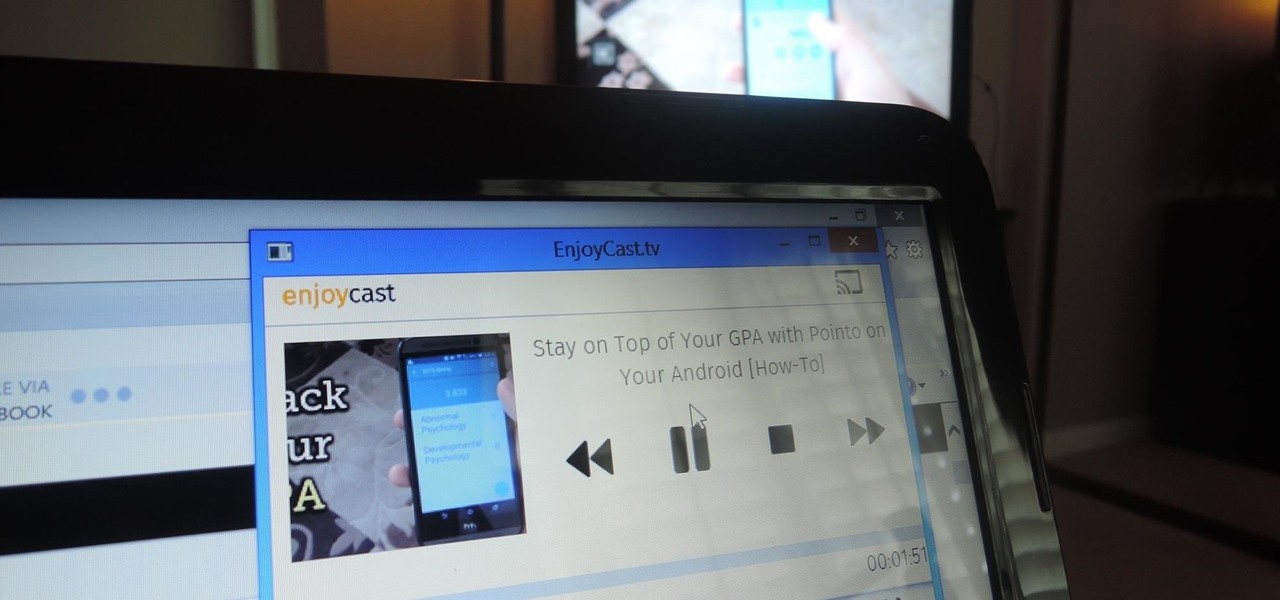
Google's Chromecast has been out for almost two years, and I can safely say it has changed the way I use my TV. At first it was a hassle to even get local media to play on it, but now casting has branched out to torrent streaming, which was a real game changer. Unfortunately, most apps only let you stream one video or song at a time, or you can't add magnet links or torrents to a playlist of local content.

Sometimes just drinking your alcohol can feel a little dull and boring. Eating your alcohol, however, is always a party.

As you might know, there are a multitude of tools used to discover internal IP addresses. Many of these tools use ARP, address resolution protocol, in order to find live internal hosts. If we could write a script using this protocol, we would be able to scan for hosts on a given network. This is where scapy and python come in, scapy has modules we can import into python, enabling us to construct some tools of our own, which is exactly what we'll be doing here.

It's nice that most apps ship with multi-language support, but if you only need to utilize one, those extra language packs are doing nothing more than taking up space on your computer. And when you're getting close to filling up your hard drive, every little bit counts.

Let's say that we want to see what someone is doing on their computer? In this tutorial, we'll be hijacking cookie sessions to do just that!

Hello my fellow hackers, Welcome to my republished revision of the ruby programming language, Part 1.

Hello Hackers! Welcome to my 2nd Post: This is a tutorial explaining how to hack android phones with Kali.

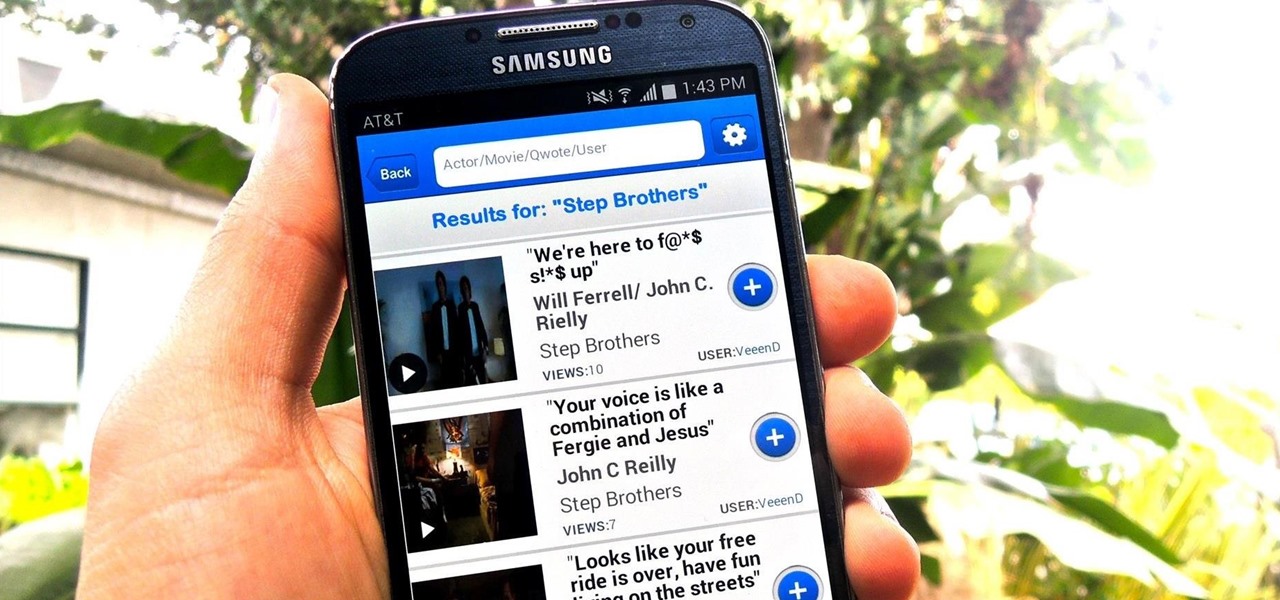
The Oscars are just around the corner, so it's the perfect time to remind people of your favorite movie moments, even if they're not exactly Oscar-worthy. But don't just settle on sending GIFs that don't include any of the fun audio, or resort to scouring YouTube for that one specific movie clip. Instead, take a look at Qwotes, a new mobile app from developer StudyUp.

Welcome back my fellow hackers. Today I'm going to teach you how to preform an Idle Scan. You may be asking what is an Idle Scan. Its a very stealthy scan because you don't use your own ip you use a zombie (in computer terms).

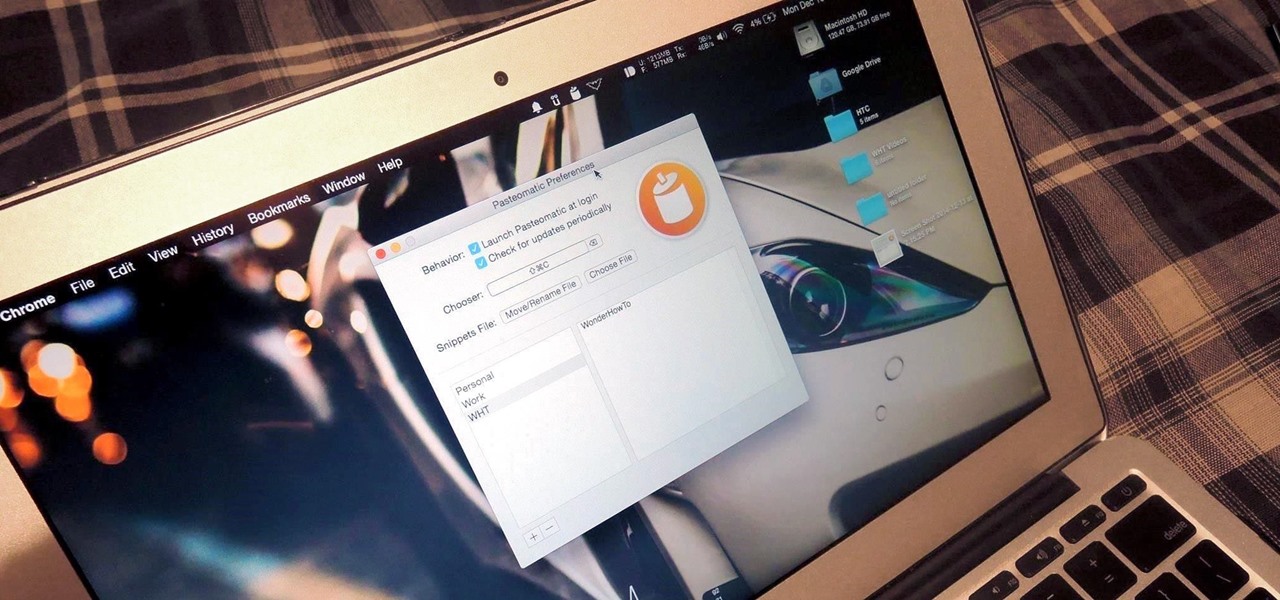
Your Mac's clipboard is great when you are just copying and pasting a phone number or address, but sometimes you end up having to re-copy the same thing over and over every day. To make those phrases a lot more easily accessible, the people over at Tiny Robot Software have released Pasteomatic. With this app, you will be able to use a hotkey to bring up a collection of your most commonly used text snippets and paste them into any text field or document.

Like most iPhone users, I place my most essential apps in my dock as it allows for easier access to them from the home screen. Unfortunately, iOS restricts the dock to just four measly apps, but there may be five or six that I really want to place in it.

Apple has been one of the biggest trolls when it comes to adding new features to their software. Whether its adding a new boot screen and not letting all devices use it, or adding Dark Mode and making it a hassle to toggle on and off, there is always to be a caveat attached to each new addition.

Coffee shops are great places to unwind and get some free Wi-Fi, but all the bandwidth in the world can be ruined by someone being a noisy jerk. I usually start blasting music through my headphones whenever that happens, but that isn't always the most ideal situation, especially if I'm trying to study or work.

Yosemite brought a new, Alfred-like Spotlight search to our Macs, but at times I still find myself wanting more out of it. However, after stumbling upon Flashlight by developer Nate Parrot, I am now able to perform Google searches, look up weather, and even enter Terminal commands straight from Spotlight's search bar.

Linux may not be the most popular consumer operating system out there, but what it lacks in consumer app variety, it definitely makes up for in flexibility and security. And if you've ever tinkered with a Linux distro, you know how easy they are to install—most of the time, I skip standard installation and boot directly from a CD.

Video: . Extraterrestrial life is life that does not originate from Earth. It is also called alien life, or, if it is a sentient and/or relatively complex individual, an "extraterrestrial" or "alien" (or, to avoid confusion with the legal sense of "alien," a "space alien"). These as yet hypothetical forms of life range from simple bacteria-like organisms to beings far more complex than humans. The possibility that viruses might exist extraterrestrially has also been proposed.

Google's Chromecast streaming device is a marvel of functionality and form. Even with powerful features such as screen mirroring and collaborative party playlists, it's the device's idle screen that first catches the eyes of most folks.

Despite being one of the largest and most feature driven companies on the planet, Google can sometimes come up short. I have my Chromecast running 24/7, and while I use my phone to cast most of my content, I sometimes find a video while browsing Reddit or LiveLeak on my laptop and I'd rather just cast it from there.

I spend an ungodly amount of time on Reddit, and while I do enjoy scrolling through memes and scandalous confessions, I must admit that I spend the majority of my time watching an endless stream of YouTube videos.

Remember when MITMing people to pentest webapps and log-ins you had to fire Ettercap,Arpspoof, SSLstrip, then look for credentials in the captured packets?

A security analyst has discovered a flaw in Chromecast's initial setup process that allows would-be hackers to assume full control over the online streaming device.

Welcome back, my novice hackers! In a recent tutorial, I showed how the SNMP protocol can be a gold mine of information for reconnaissance on a potential target. If you haven't already, I strongly suggest that you read it before progressing here, as little of this will make much sense without that background.

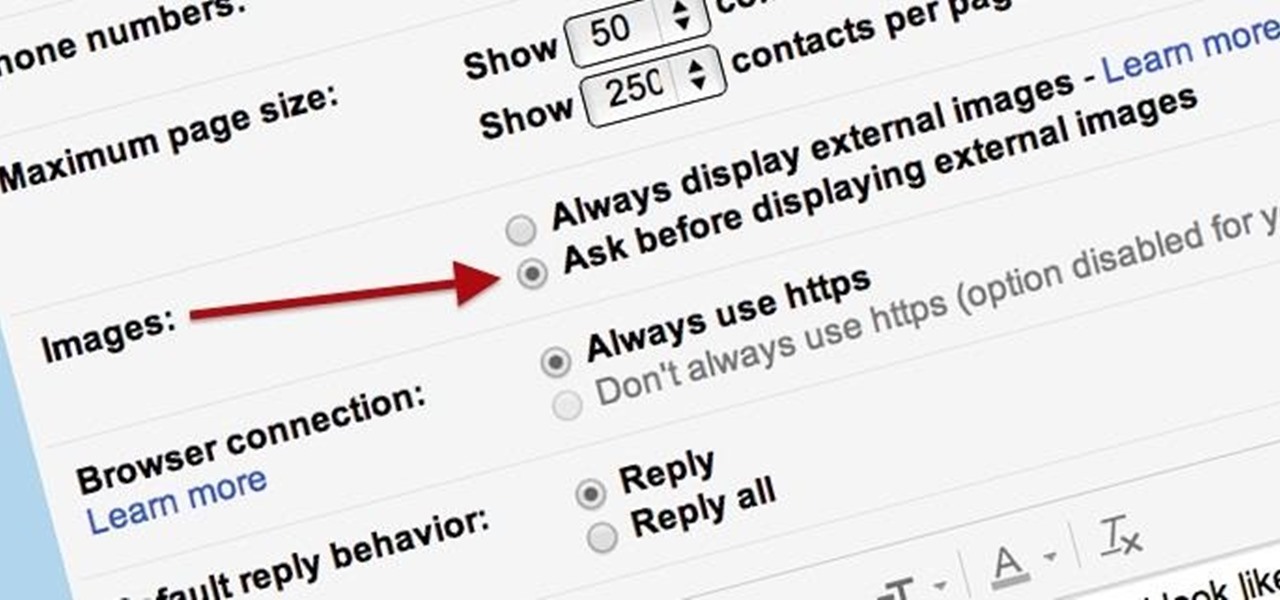
Securing your email address is one of the most important things you can do on the internet. Hackers, spammers, and overly aggressive marketers can turn your Gmail inbox into a heap trash if you're not careful.

There are hundreds of sites that host high-res wallpapers for your Android's home screen, but most of us stick with the same old drab stock wallpaper because we're too lazy to go hunt for new ones.

In my last hack blog on crashing your roommates Win7 system, we started looking at client- side attacks. As promised, we will be looking at some more client-side attacks.

In the Windows 8 Enterprise edition, you can use the Windows to Go feature to travel with Windows 8 OS, personal files, documents, settings and many more. All you need is an external hard drive or USB drive of 32 GB space or more and USB 3.0 support or more for fast Windows 8 booting. We need the storage media of above specification to create bootable USB to access the data anytime by plugging the media into different PC running latest version of Windows 8 PRO or Windows 7.

Early last month, Sony released PlayStation Mobile, bringing PlayStation games to the PS Vita and other certified phones and tablets. The list of certified phones isn't as extensive as it should have been, consisting of only Sony devices (a few tablets and Xperia) and a couple of HTC ones. For anyone with a supported device, you can head over to the PS Store for the download and installation instructions.

Anything free is cool, but getting a fully upgraded operating system for the great price of nothing is downright awesome. A recent exploit was uncovered that allows users to get a free copy of Windows 8 Pro directly from Microsoft's own website. Seriously.

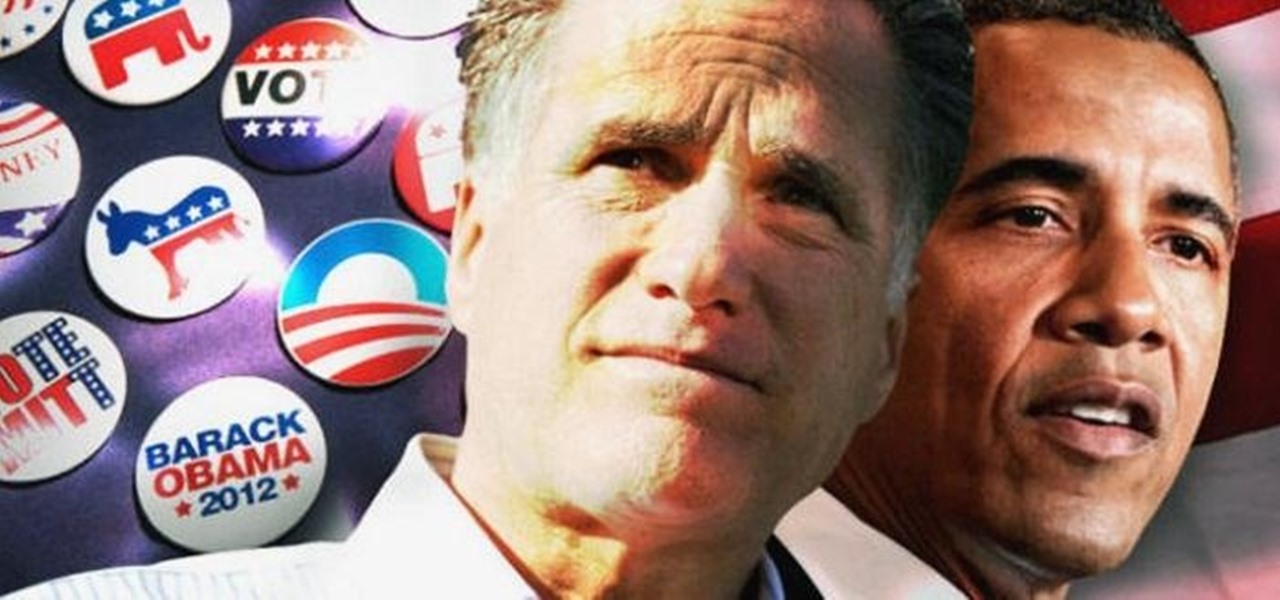
Believe it or not, the 2012 Presidential Election is (finally) almost over. While most of us are breathing a collective sigh of relief (no more political ads!), it still seems like it hasn't been that long since the last election results were announced. This time, though, one of the biggest differences is how people will watch. Since traditional cable is on its way out, and mobile devices are getting more popular every day, a lot of people will be watching this year's election results online ...
Are you scared that the RIAA is about to track you down for illegally downloading songs. Well, here is a method of obtaining many songs absolutely free that is virtually untrackable

Hate answering the door, but don't trust your friends with a set of keys? This RFID front door lock made by Steve Pomeroy will solve all your party-hosting problems. It reads the RFID tags in his friends' public transit cards and decides who's allowed in based on "groups" that Steve defines. And I have to say, it's also rather stylish. It's controlled by an Arduino serial console and a custom Android app to add and remove cards. The reader can store 50 or 100 tags at a time and allows 7 diffe...

In this eight minute video the host of the video conveys the methods and techniques that can be used for hacking the "Urban Rivals" video game. By use of Microsoft Word, the host types out the methods that are being used. This typing makes for a clear and easy to understand communication system to the viewers. The first step that is thoroughly explained by the host is simply to make and account. This makes it possible to play Urban Rivals in the first place. Throughout the rest of the video, ...

This is a tutorial video on how to play the ukulele, brought to you by gtut98. In this lesson, the host teaches you how to play a classic Hawaiian song called "Lovely Hula Hands", as performed by Junior Brown. You will learn all the chords you need to play the song as you follow along with the host. He does a good job of demonstrating the fingering of all the chords, as well as their progression through the song.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

In this tutorial, Jenny Jones invites you into her bedroom to show you how to give yourself an easy, 6 step at-home facial. Keep your skin young and bright with these fantastic tips from America's favorite talk show host.

Elvira, Mistress of the Dark, was created in 1981 by Cassandra Peterson. She was the hostess of a local Hollywood horror movie show that became nationally syndicated. Elvira was the first horror host to be nationally syndicated, first person to be broadcast in 3-D on TV, and first female celebrity to do a national beer campaign and market her own beer.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

While much of the world is currently in some form of quarantine due to the COVID-19 pandemic, augmented reality (AR) gives us all the opportunity to see virtual content while stuck in our homes.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.