
News: Bloodsucking Flies Act as 'Flying Syringes' to Detect Malaria & Other Emerging Diseases in Wild Animals
Researchers have been studying the blood meals of flies to understand the flow of infectious pathogens in wild animals.


Researchers have been studying the blood meals of flies to understand the flow of infectious pathogens in wild animals.

Hello Friends … My name is Suresh Senarathna and this is my first “How-To” post,

Brand loyalty is one of the main factors behind our decision to choose a particular mobile device, but it doesn't have to be the entire equation. Educated consumers know that certain devices simply fit their budget and usage better than others, which means you can't always let a logo dictate what kind of phone or tablet you buy.

So you want to create a meterpreter virus, but you keep getting caught by AV. How do you create one that will go undetected? In this tutorial, I'll teach you how to code your own simple virus that will download a powershell payload from an apache webserver and execute it - bypassing antivirus.
Ready or not, the USB-C cable is about to take over your electronics. The new industry standard is fully reversible and packed with enough power to serve as a laptop charger or an HDMI cable, so it actually has the potential to replace every cord, wire, and connector in your house. In fact, the conversion has already started: The latest MacBook, Chromebook Pixel, and Nexus phones are sporting USB-C connectors out of the box.
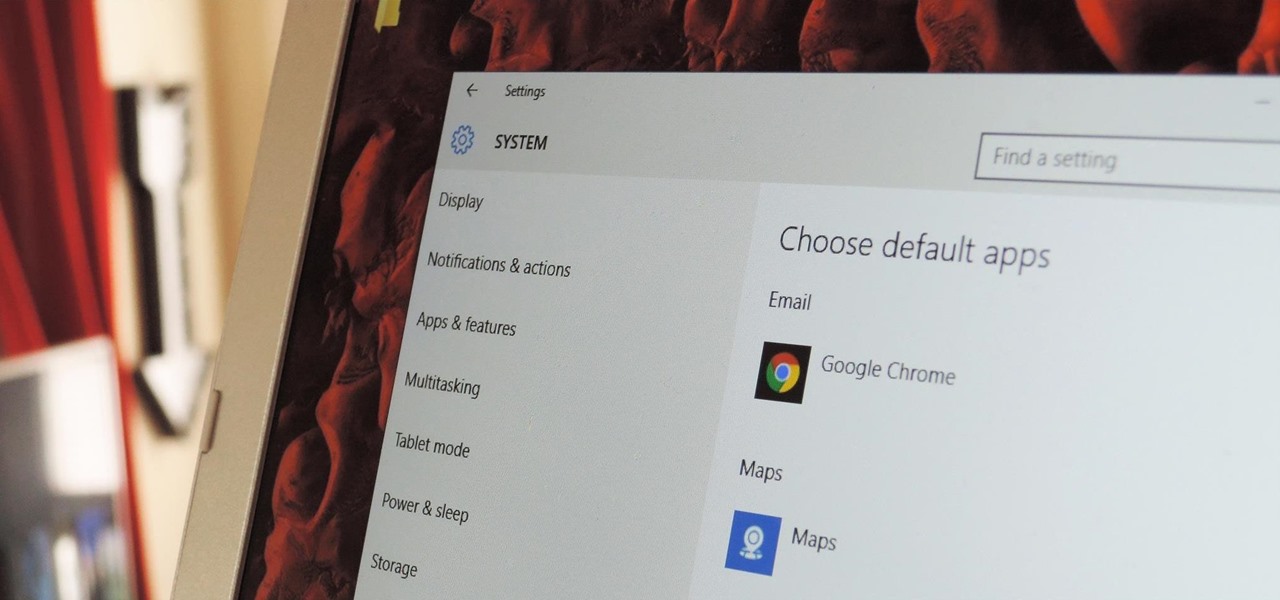
The first time you launch any type of file, Windows 10 will usually prompt you to select an app to open it with. Occasionally, though, this "Open with..." screen doesn't show up, and instead Windows will use a pre-installed system app to launch the file without ever giving you a choice in the matter.

Hello again, reader! In this post, we are going to cover some data types and how to declare variables. It shouldn't be too hard so just sit back, relax, grab some popcorn and enjoy the ride (while you still can!).

What you probably don't know is when you remove a file on your system, it is actually still saved, and not entirely removed. Let me tell you how to get rid of it completely.

Greetings, hackers and friends! I know it has been a while since I posted a tutorial, and hopefully I can make up for that by posting a series.
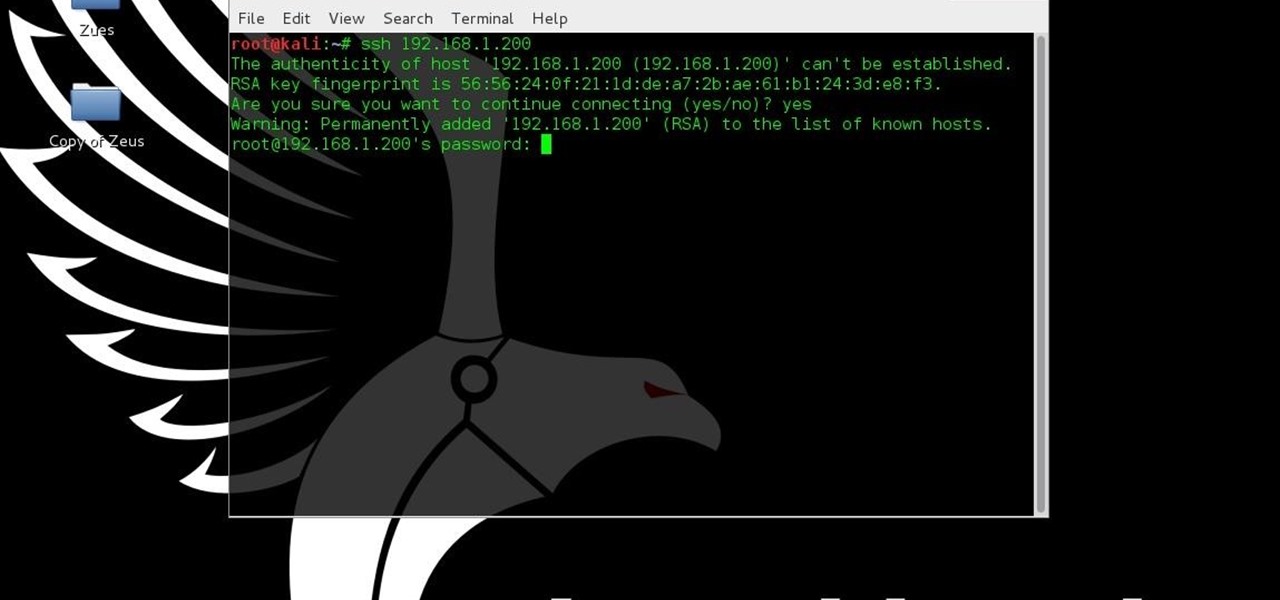
This tutorial is for people who want to try different types of hacks in an environment that is the same for everyone so it will help people to ask questions and learn. This series assumes you know how to run a VM and network them together. This series also assumes that the services running on the Metasploitable machine are needed to be running.
If you have a smartphone, chances are you have something on it you don't want others seeing. Whether it be photos, videos, or documents, some things are best left private. Not everyone is a saint, after all.

Believe it or not, there was a time when smartphones weren't the primary tool for taking photos. People actually walked around with bulky film-based cameras on their necks, and some even used cheap disposables. While photography wasn't introduced to the world when smartphones came out, it's definitely more accessible—and everyone is a photographer now.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

In general, we never really put much thought into fonts, but they comprise a huge portion of our online experience. A whimsical mood can easily be set by using something like Segoe Script, but switch it up to Sentinel and you've got a more sophisticated feel all of a sudden.
Hello Hackers! Welcome to my 2nd Post: This is a tutorial explaining how to hack android phones with Kali.
To contemporize a popular quote, "A cluttered desk(top) is a sign of a cluttered mind." Of course, it's difficult to maintain a tidy desktop... as you read this, mine is cluttered with screenshots, folders, Word documents, videos, pictures, and apps.

It's officially the holiday season, which means everyone will soon be traveling home to spend time with loved ones. And anyone who has any knowledge whatsoever of computers knows what else that means—family members left and right asking you to fix their various technical woes.

If you had the original Microsoft Surface with Windows 8 and a Type or Touch cover, you know how big a pain in the ass it was to change the scrolling direction of the trackpad.

With so many cloud storage services out there, many people are starting to keep their important documents online, especially when they know they'll need to view them when they're away from their computer.

Any living creature will die if deprived of sleep for long enough. The longest documented occurrence of a person not fully sleeping and surviving is only 11 days. There is a rare disease where deep sleep is never achieved, affecting roughly 100 people worldwide. Patients usually only survive between 6 to 18 months after the onset of chronic insomnia, and only 3 to 9 months in a parasomnia state without any real REM sleep.

There is nothing worse than losing valuable information or programs on your computer. And if you've ever accidentally deleted a file or document, you know how agonizing that entire process can be.

Microsoft's first venture into the tablet market, the Surface RT, combines many of the capabilities of a normal Windows 8 laptop into a super compact tablet, whose super-thin touch cover and kickstand can transform it into a functional mini-laptop, small and light enough to go anywhere you want. But like most tablets, the Surface comes with a rather limited amount of storage space. The tablet comes in either 32 GB or 64 GB, but we all know that's not the actual amount of storage space you can...

Robert Templeman from the Naval Surface Warfare Center in Crane, Indiana and several of his friends from Indiana University recently developed an Android application that is capable of gathering pictures and videos from mobile devices in order to reconstruct a user's environment in 3D. The malware would come coded inside of a camera application that the user would download. The malware, called PlaceRaider, would then randomly take pictures throughout the day and carefully piece them together ...
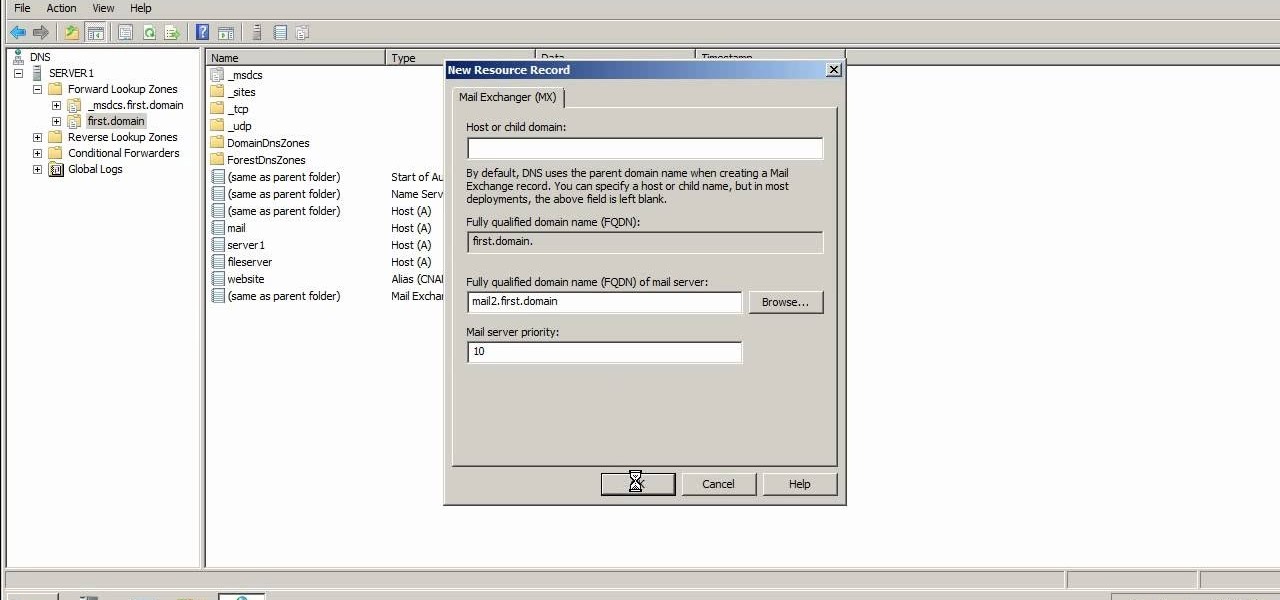
You can create many types of domain name service records in Microsoft Windows Server 2008. Glue records, CNAME records, mail exchanger and many other types of records are possible. Follow the instructions in this video to learn how to manually create DNS records.
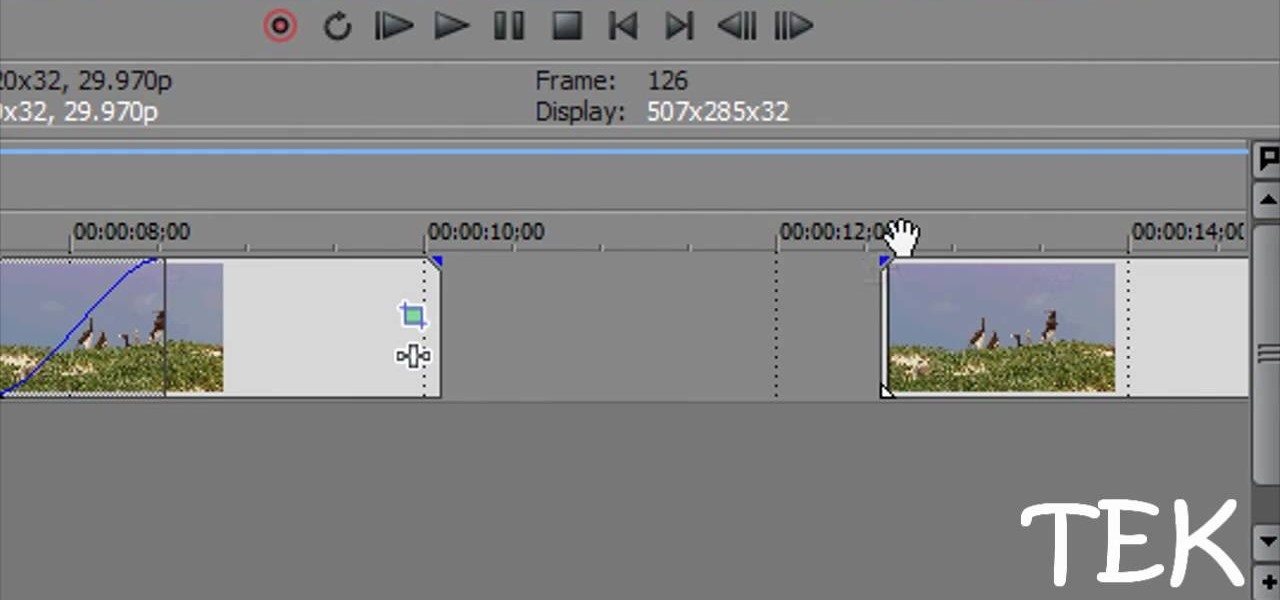
This tutorial shows you several different types of fades you can use when working with Sony Vegas. Fades can add a little something extra to your web clips, slideshows and other media, and Sony Vegas offers several ways to customize your own.

In this video from AppleGenius0921 we learn how to enable a Live/Hotmail account on the Mail application on a Mac. Open Mail. In full name put your full name. Type in your email address and password and continue. Leave the account type on POP and name the description what you'd like. The incoming mail server is pop3.live.com. Type in your live.come username with @live.com in it! Click Continue. The outgoing mail server should be smtp.live.com. Check use only this server and check use authenti...

Need a quick primer on how to solve type-1 error problem in stats? Let this video be your guide. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps. For all of the details, watch this installment from Internet pedagogical superstar Salman Khan's series of free math tutorials.

In this video, we learn how to identify number types. You will need to figure out what numbers from a list is a rational numbers in your math equations. A natural number is a counting number (1,2,3). A whole number is a natural number and zero (0,1,2,3). An integer is a whole number and a negative whole (-2,-1,0,1,2). A rational number is any number that can be expressed as a ration of integers. An irrational number is any number that's not rational and non-perfect. Once you understand these ...
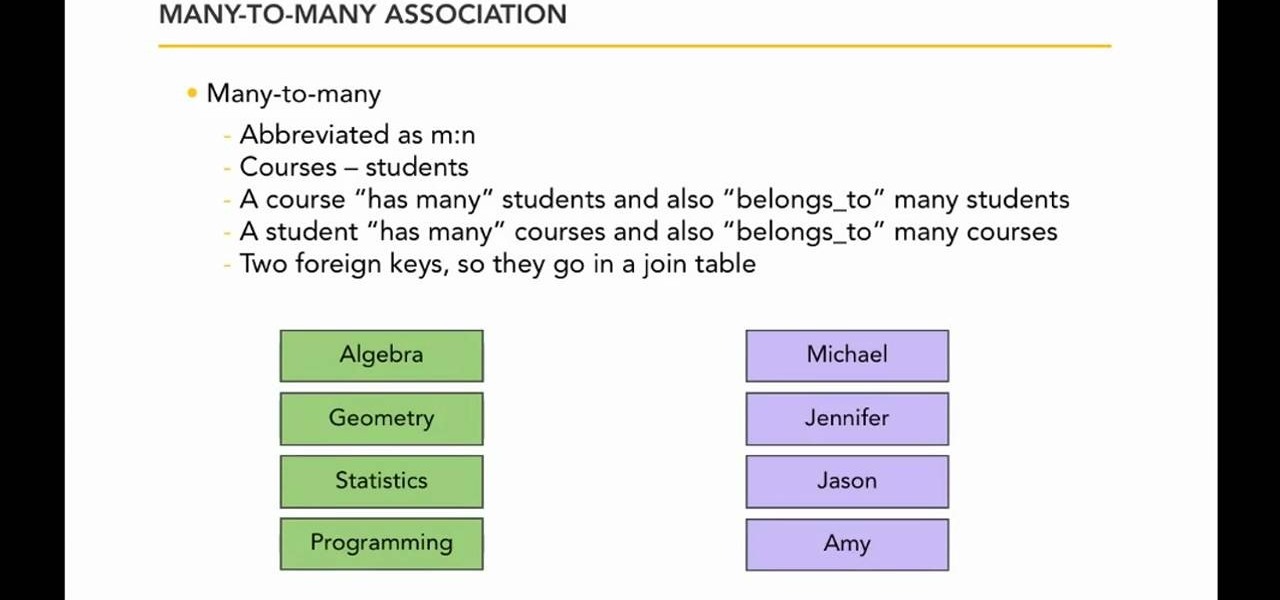
In this free video programming lesson, we learn how to work with relationship types when writing an application with Ruby on Rails 3. Whether you're entirely new to Ruby on Rails 3 or are a seasoned developer merely looking to brush up on a few of the basics, you're sure to find much to take away. For more information, take a look!

In this tutorial, we learn how to tag friends and fan pages on Facebook. First, open up your Facebook account and go to your main profile page. After this, you can start to type in your status update that you want all of your friends to see. When you are ready to tag in your friend or fan page, type in "@" and then type in the first letter of the name. From here, their name will show up and you can click on their name to tag them. Now, your update will show up on their page as well as yours, ...

In this tutorial we learn how to use the Facebook status tagging feature. This will let you update your Facebook status and add your friends in with it. This will appear on their wall as well, for all their friends, mutual friends, and your friends to see. To do this, you will begin typing in the status update, then type in "@ and then that person's name" Their name will show up underneath where you are typing. Keep in mind you cannot tag someone you aren't friends with. Click on their name w...

In this video, we learn how to unblock a Facebook firewall at school. First, you will need to try to go to the website you want to go. If you try this and you can't reach the site, go to the top of the bar where you typed the website in at. Once here, you will find where it says "http". Type in an "s" after the "http" so you end with "https" then type in the website that you want to visit. After this, you should be able to go to the website you want to go to without any trouble, just make sur...

This video tutorial is in the Computers & Programming category which will show you how to hack a wireless network with WEP encryption. This video is intended only as a means of testing the security of your own network. Go to Backtrack Linux, download the backtrack4 and burn it to a DVD. Now put it in a computer with a wireless card and restart the computer so that it boots to the DVD. When it boots up, type "startx" to start the interface. Bring up the command prompt and type in "/etc/init.d/...

In this video, we learn how to access Facebook at school using "https". You don't have to go to any website to do this, it's simple and easy. All you have to do is type in "https" into your browser before you type in the website you want to visit. Make sure you type in this extra "s" or the website will not work. This should bypass the security settings your school has set so you can access your Facebook account. If you happen to end up on a page when it doesn't work, just make sure the "s" i...

In this clip, you'll learn how to usebooleans, type casting and constants when coding in PHP. Whether you're new to the PHP: Hypertext Preprocessor scripting language or are a seasoned web developer merely looking to improve your chops, you're sure to find benefit in this free video programming lesson. For more information, including detailed, step-by-step instructions, take a look.
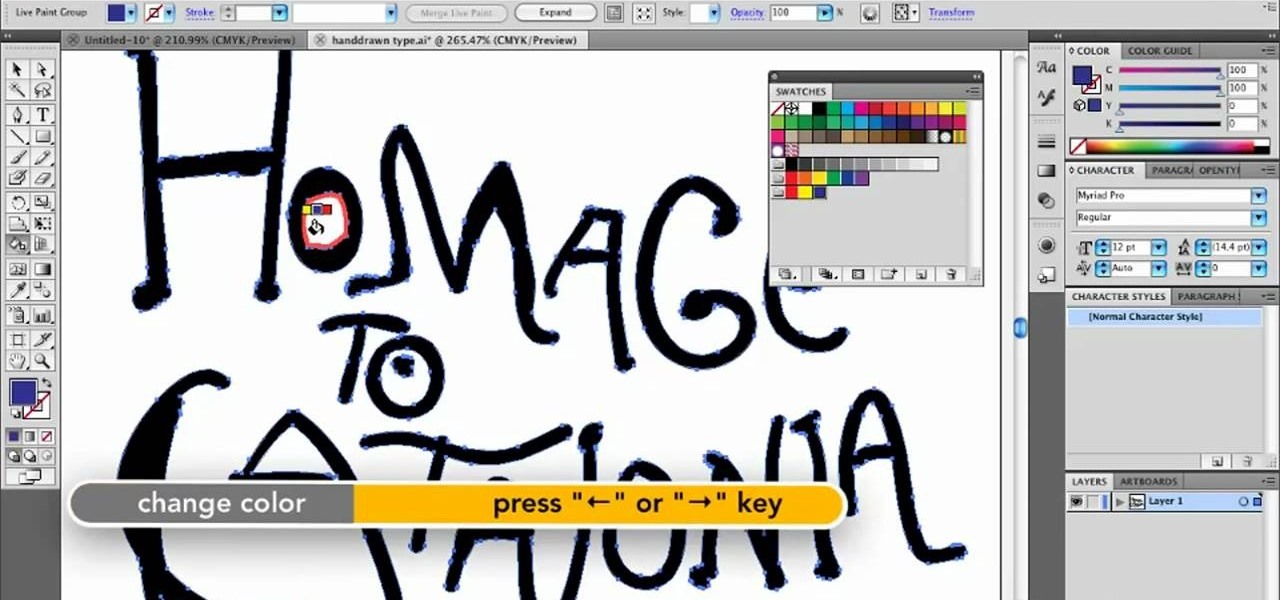
In this clip, you'll learn how to use the Live Paint tool to color in type when, for example, designing a book cover within Adobe Illustrator CS5. Whether you're new to Adobe's popular vector graphics editor or just looking to pick up a few new tips and tricks, you're sure to enjoy this free video software tutorial. Take a look.
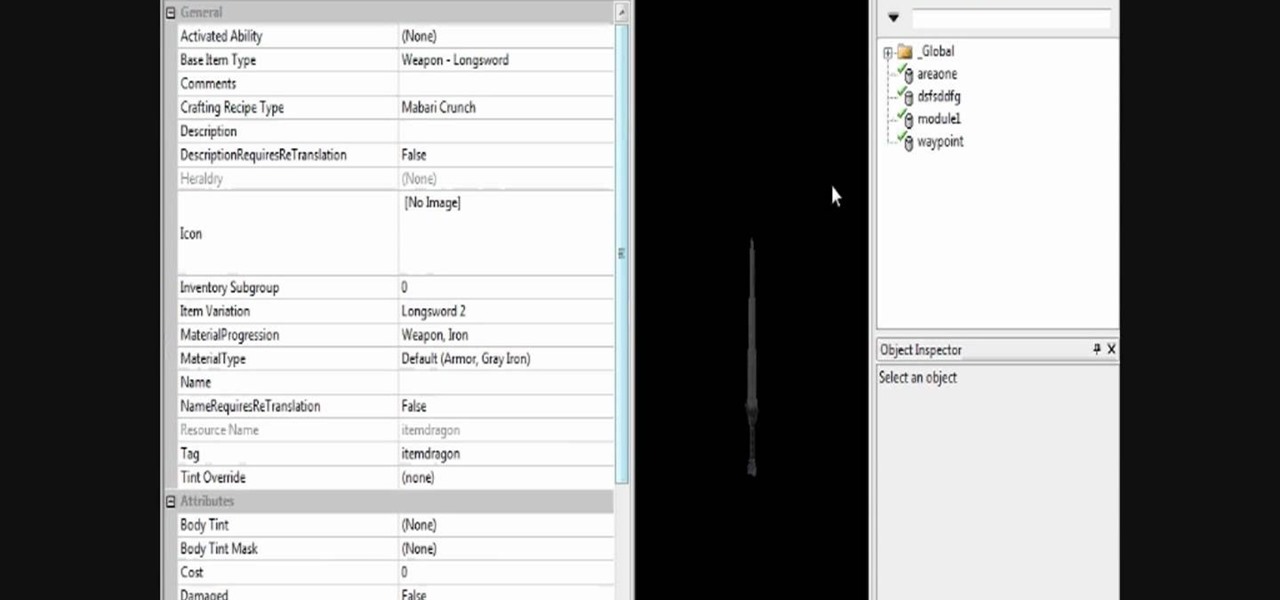
If your Dragon Age story calls for an "Excalibur" or some other type of legendary weapon, armor (armoire of invincibility, kekeke, 5 points to whoever gets the reference!), or any other type of armor but aren't sure how to make them in the toolset you're covered! In this video you will learn how to create, edit and customize your own items! So go on, make that over-powered weapon and go have some fun slaying the Darkspawn!

In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....
If you're a big fan of the Left 4 Dead games, then you're going to love this next tutorial. In this video, you'll find out how to spawn a very unique zombie: the Jimmy Gibbs Jr. zombie!

In this tutorial, we learn how to tie a Carolina rig fishing line. First, grab your favorite type of hook, then apply it to a Carolina rig that has a bead on it to protect the knot from sliding up. You can also use a giant worm on your Carolina rig to have better results while fishing. Push the hook into the worm, and thread it through so it's secure. This type of fishing line is used to fish on the bottom and can be used to catch more fish and a different type. Use this as often as you'd lik...