Back in the day when computers relied on CRT monitors, having a static image displayed for too long actually resulted in the image being burned into the screen. For this reason, screensavers were developed, which display animated images in constant motion to prevent burning in when you stepped away from your computer.

Shopping online can be as easy as buying cigars in Mexico. You find what you like, ask for the price, and walk away. "My friend! Come back! I give you 10% off. Just for you."

The folks behind StumbleUpon have created a video service that is just as awesome at introducing you to new content as their website service is.
"Millions of us have smartphones with the power to speed up research that will benefit billions of people around the world." - Professor Francois Grey

Amazon just announced its entry into the set-top streaming content marketplace with its new Fire TV box. Competing directly against Apple TV, Google's Chromecast, and Roku, Amazon is betting on big processing power and voice controls to stand out from the competition. Features include the following.

In the wake of the NSA controversy and its subsequent fallout, many dashed towards finding means of secure communication—using private internet browsing and encrypted text messaging applications—out of fear of being spied on.

Streaming apps like Netflix, Hulu and Amazon Instant Video have been available on game consoles for a while, but if you're in a country where they're blocked, it can be hard to find a way around. There are apps and extensions like Hola Unblocker and Media Hint and that to bypass location restrictions on your computer, but what about your Xbox?

There are several ways to get around location restrictions on subscription sites like Netflix and Hulu using apps, extensions and proxies, but they tend to only work on laptops and computers. Users who want to access content from mobile devices and gaming consoles are usually out of luck.

For a photo- and video-sharing app based around privacy, Snapchat sure has a lot of security holes floating around. At one time, you were able to take screenshots of Snapchats in iOS 7 without the sender knowing, which is something that you can still do on rooted Android devices.

How can you tell if the pair of Ray-Ban Wayfarer sunglasses that you are about to buy online are not a fake? Follow these 9 simple steps to verify the authenticity of your purchase. Always ask the seller to use the youVerify app prior to purchase. It's Smarter Selling & Safer Shopping.

Are you constantly traveling? Well, as a Hilton HHonors member, you can enjoy special treatment at all of their hotels and resorts. It's free to register, but the difficulty lies in climbing up their membership level. To reach Gold elite status, Hilton HHonors requires that you have a minimum of 20 stays, 40 nights, or 75,000 base points—all in one year. While this may very will be easily attainable for those with jobs that revolve around traveling, it's almost damn near impossible for the re...

What's the meaning of life? That's the age-old question; but can it ever really be answered? I mean, isn't life just a big game anyway? Perhaps, a game of inches?

Those of you who have attended a Steampunk convention in the last year or two may have heard of something called "Tea Duelling" and been intrigued.

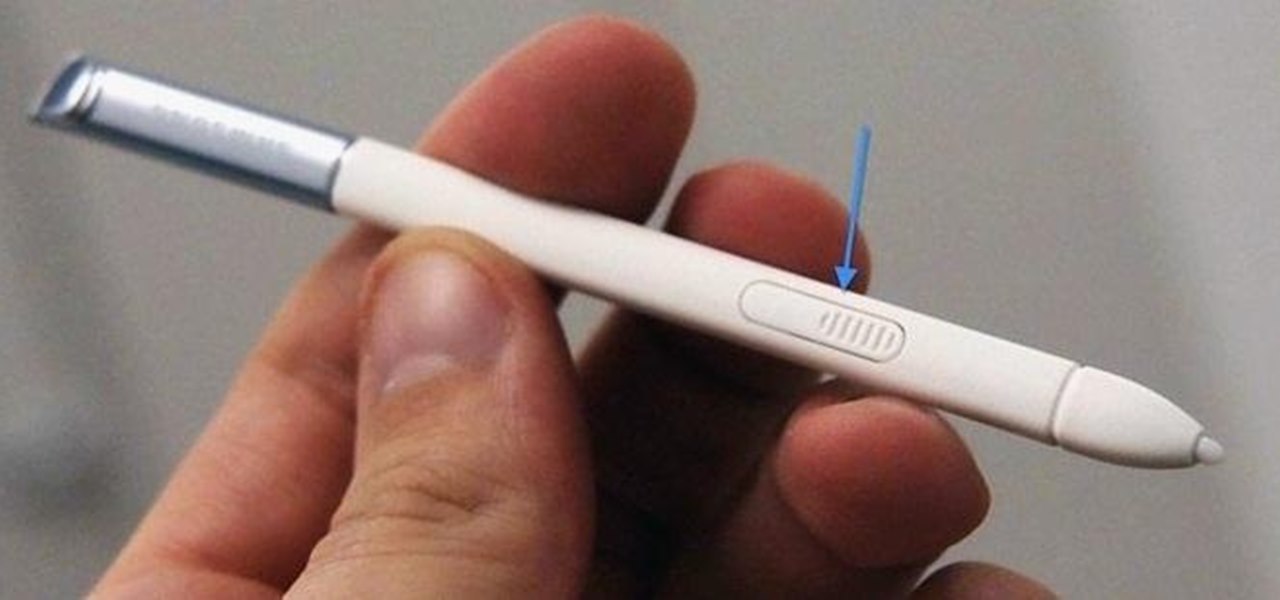
Touchscreens are all the rage these days, and it seems that the stylus has become a relic of the past thanks to newer and better fingertip responsive smartphone displays. But when it comes to phablets like Samsung's Galaxy Note line, the added S-Pen is definitely helpful for more accurate and precise actions (and a less greasy screen). Of course, there are disadvantages of using an S-Pen too, one being hardware issues. Unlike your finger, the S-Pen can malfunction and become a huge problem, n...

In an effort to appease iPhone fans eager for an NFC-equipped device, an option that is available on many other smartphones, Apple created Passbook, their version of a digital wallet.

There are a lot of programs which allow opening archives. Alas, most of them are rather complicated to use. The process of opening of the archive often takes much time. Hopefully, there are some applications which are simpler to use for regular uers.

Facebook is the most powerful social network web site that helps you to connect and share with the people in you life. You need to register an account with the face book website, which is free of cost, to use their service. In face book home page you can show others your live status updates. To do this first log in to your face book application. From the left hand side column select the status updates link. This opens the 'Status Updates' web page, where you can see the status updates of all ...

Your brain actually needs to be refueled throughout the day, and our brains function best on carbohydrates. Brain foods like fruits and fish are important for fueling your brain all throughout the day. Learn some tips on eating brain foods and keeping your mind active in this nutrition how-to video.

Since its founding in 1984, Cisco Systems has been a global leader in information technology. From networking hardware and software to domain security and energy management, the company dominates the IT field.

If there was a version of the Doomsday Clock for counting down the release of Microsoft's HoloLens 2, then the caretakers of that imaginary clock would move the minute hand to "one minute to midnight."

Augmented reality app developer Laan Labs has shared a preview of a beta app that achieves 3D scanning with just an iPhone and produces highly-detailed models for sharing with others.

There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

Any parent with a rambunctious child who may have at one point racked up a hefty bill on their Kindle or Android device can now breathe a sigh of relief. One, Jack Black has had it happen to him too, and two, Amazon will be refunding up to $70 million of in-app purchases made by children after downloading apps from the Amazon AppStore.

This is a quick and easy method for receiving the backend IP (1) of a server who is hidden behind a proxy (2) or a firewall (3).
Hello I have now asked for help a few times, so I figured I should contribute with what I can offer as of right now, which is many valuable sites if you need to look someone up.

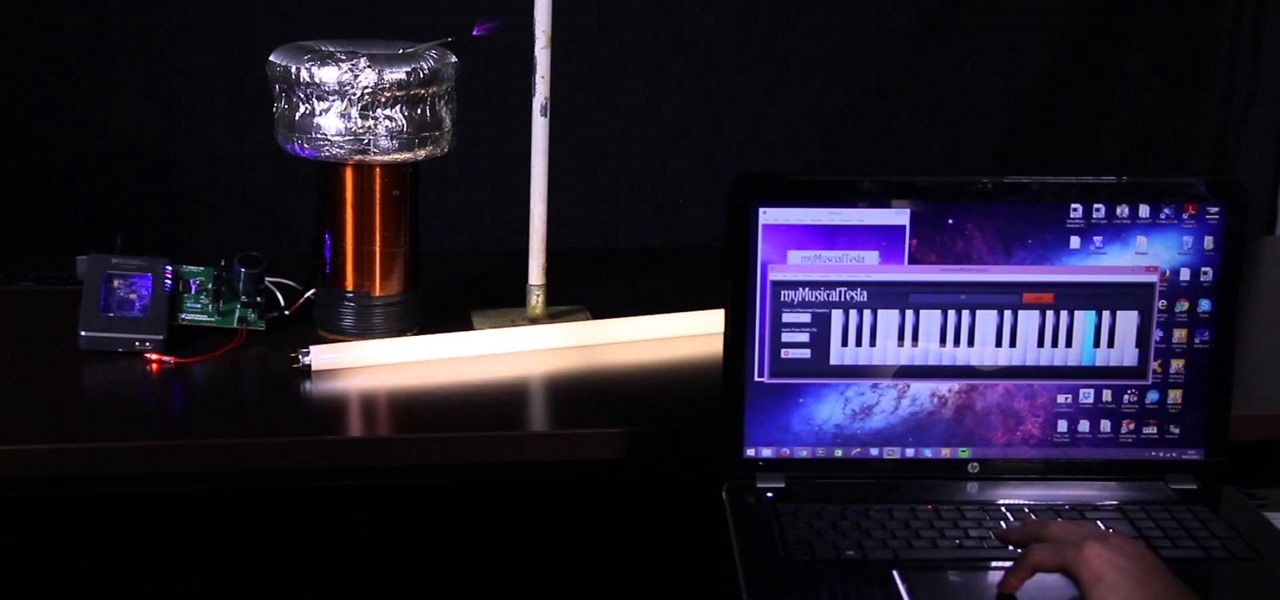
Video: . I made this Tesla Coil using the myRIO and LabVIEW. It uses electricity to play the music, which can be Star Wars, Harry Potter or even Hunger Games! The music is played by the spark heating the surrounding air (causing it to expand) then the spark turning off (causing the air to cool and contract). This expanding and contracting cause's longitudinal waves - or sound waves.

Automated tattoos are now a reality, with 3D printers being hacked into tattoo machines. Multiple people have posted videos of their 3D printer that can "print" tattoos, with one of the more impressive ones shown in the two videos below.

To become a Victoria's Secret model, use the Internet to locate agency Web sites and register photos on-line to be viewed by modeling agencies. Build a portfolio and gather head shots for becoming a Victoria's Secret model with tips from a modeling instructor in this free how to video on modeling.

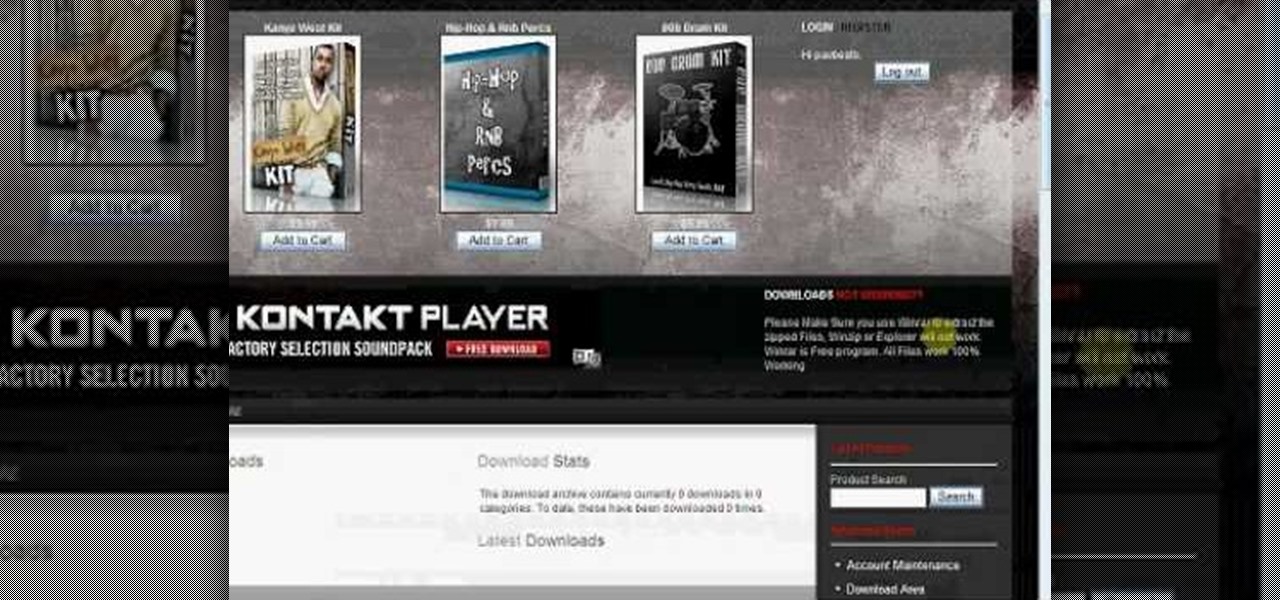
In this tutorial, we learn how to download free drum kits and samples from FruityTuts. First, go to FruityTuts and register on the site. After this, log into your account and look to find the kits that are available under the downloads section. Different kits will appear that you can download, choose the one that you like. After you have picked the one you like, click on it and then click on the download button. After this, save it on your computer in the file that you prefer, then you will b...

In this tutorial, we learn how to use the HLSW game server organizer program. First, go to the HLSW website and download their product. After this, save it to your computer and then install it. Next, register an account with them, then fill out your information. Now, when you are in the program you will be able to find servers that don't require key checks for games. Then, you will be able to add the servers to your computer. To download the server list, you will have to login, then you will ...

Google is an incredibly useful database of indexed websites, but querying Google doesn't search for what you type literally. The algorithms behind Google's searches can lead to a lot of irrelevant results. Still, with the right operators, we can be more exact while searching for information that's time-sensitive or difficult to find.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

Signal Private Messenger is famous for its end-to-end encryption, but you can't even use the messaging app without having a real phone number attached to it. Luckily, there is a way around this limitation, so you can use Signal even if you don't have a valid SIM card in your smartphone.

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

hello my dear colleagues, I made a visit to nullbyte and found that there is not a complete tutorial about the google dorks, so I felt the need for this tutorial, and seeing that there are many newbies around, so here's a tutorial that will teach you how to use google to hack.

Hi everyone. Recently I've been studying some topics about Assembly, memory and exploitation, and thought I could write something nice, easy and fast about it, just because I like to share what I learn, and probably sharing what you learn and trying to explain it to a stranger is the best way to learn it better. It worked for me, and I hope it will be useful for you too.

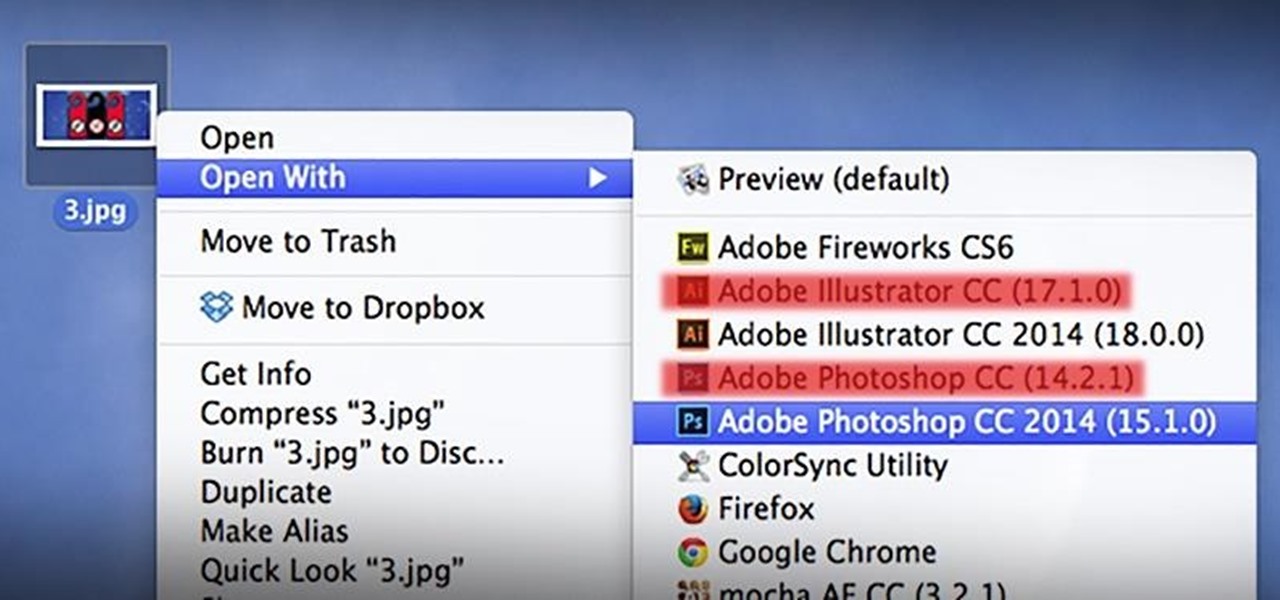
As a regular Mac OS X user, I have a love/hate relationship with the "Open With" contextual menu. Sometimes, it has just what I need. Other times, it's often packed with unnecessary or duplicate items, or missing the app I want to open the file up with the most.

Welcome back, my neophyte hackers! There are innumerable ways to hack a system. We must not overlook any of the possibilities if we want to "own" the system. As systems become more and more secure, we need to be vigilant in our search for weaknesses. In this hack, we'll look at abusing the trust that a user innately has for software updates to install our own listener/rootkit on their system.

In this video you will see how to select from the various web hosting options to host a domain at GoDaddy.

How to use XAMPP to set up a .com domain name for yourself.