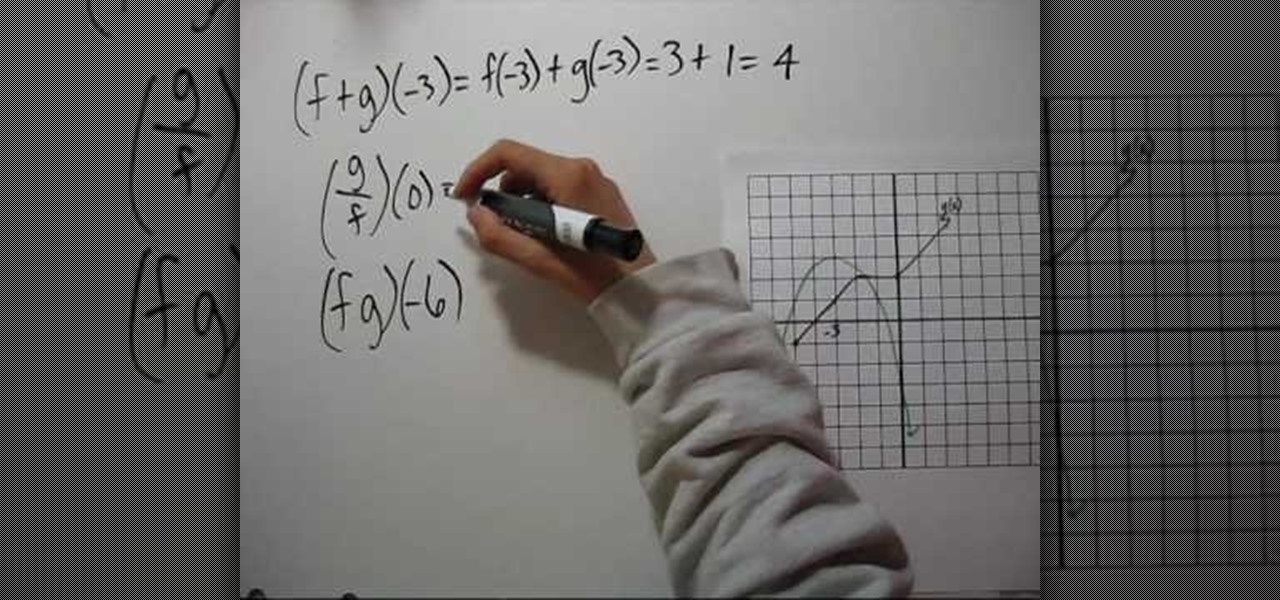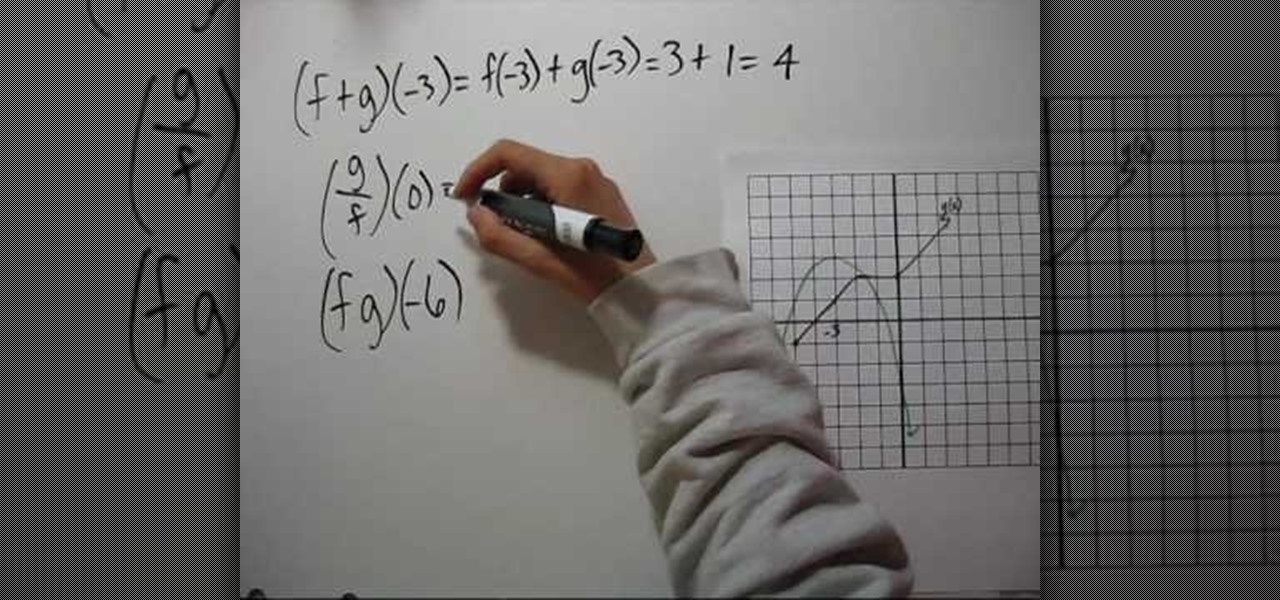
YouTube user NotesCollegeAlgebra teaches you how to evaluate combinations of functions from graphs. You start off with a graph and some functions. (f+g)(-3), (g/f)(0) and (fg)(-6). You start looking at the graph and the first line and you get (f+g)(-3)=f(-3)+g(-3)=3+1=4. (g/f)(0)=g(0)/f(0)=2/-3=-2/3. (fg)(-6)=f(-6)g(-6)=(-3). But then when you want to find out g(-6) you realize -6 is not in g's domain. So the answer to the last equation is that it doesn't exist.
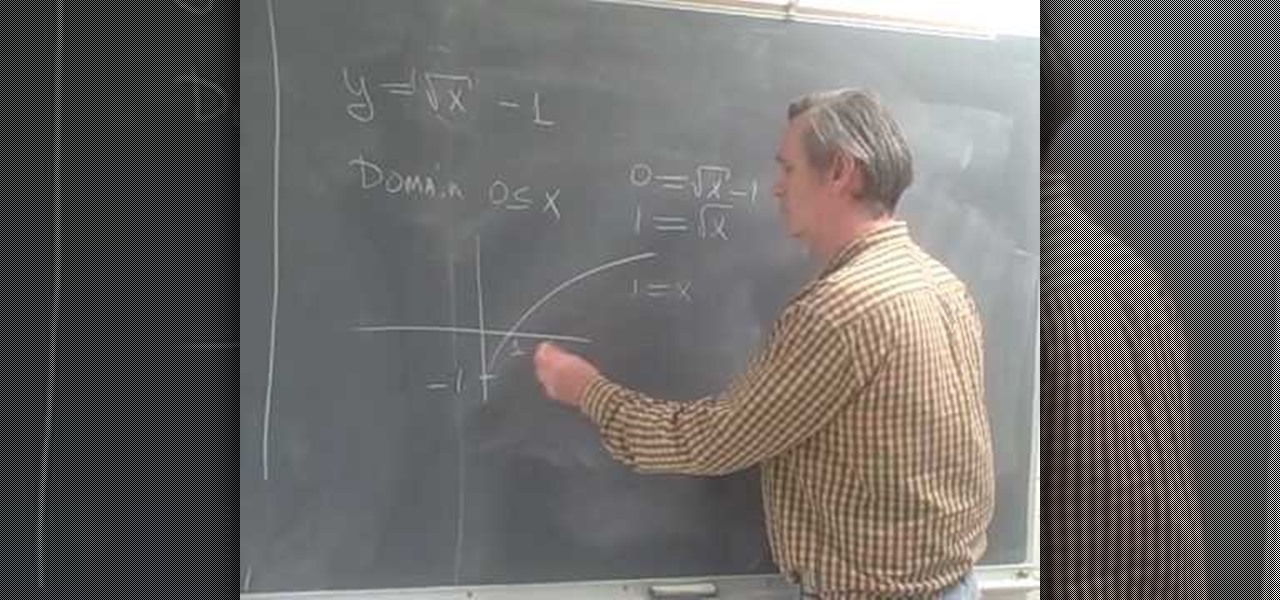
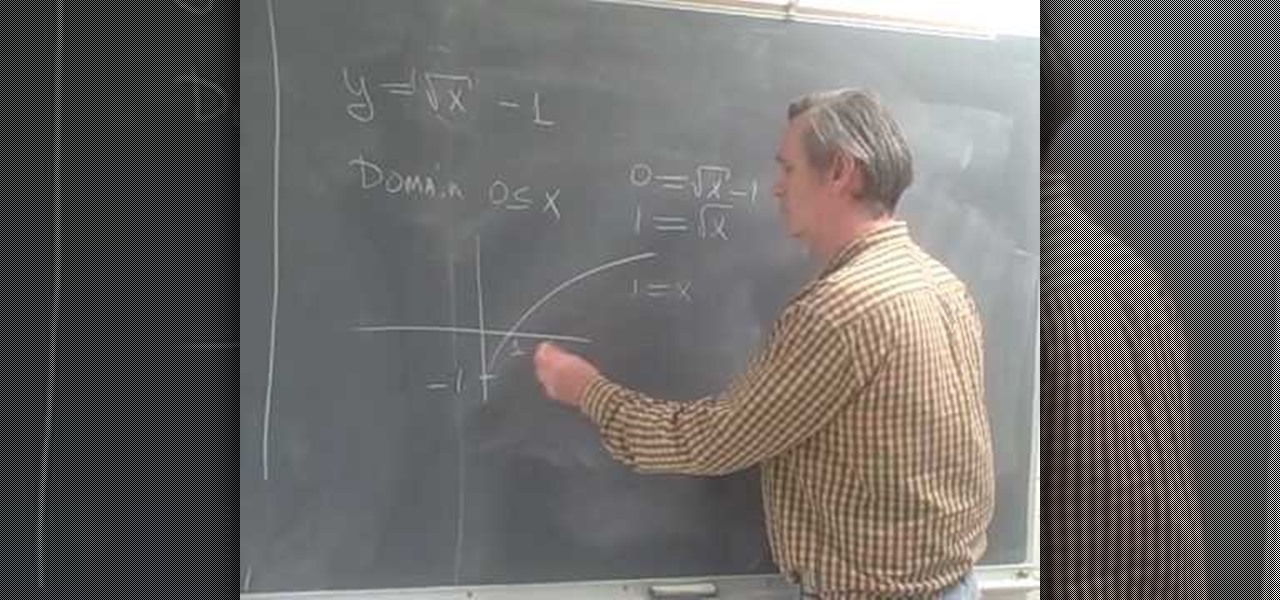
Professor ElvisZap teaches you how to stretch shift and reflect the graph of a square root. A square root function is the opposite of a squared function. You start with y=square root of (x-1) it becomes 0<=x-1. then 1 <=x. You use the graph and solve it as you would for any function using small values first, then you have y=square root of x - 1, the domain 0<=x. This shifted the graph down 1 unit. 0=square root of x - 1, 1=square root of x, 1=x. Then the range is [-1 + infinity). Continue in ...
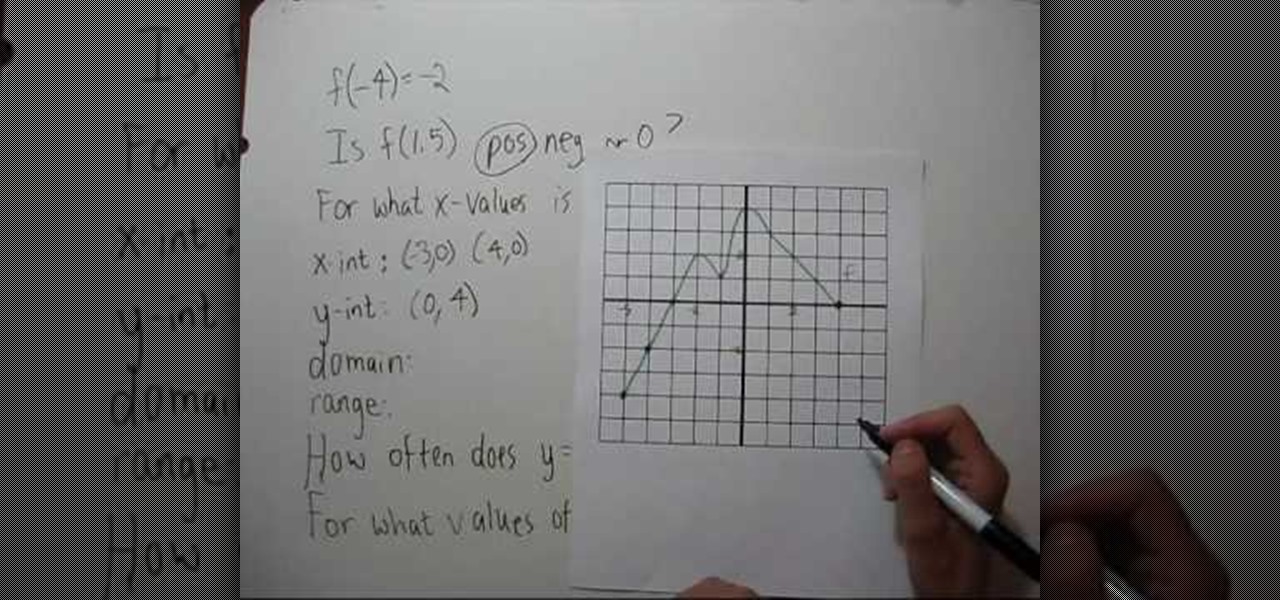
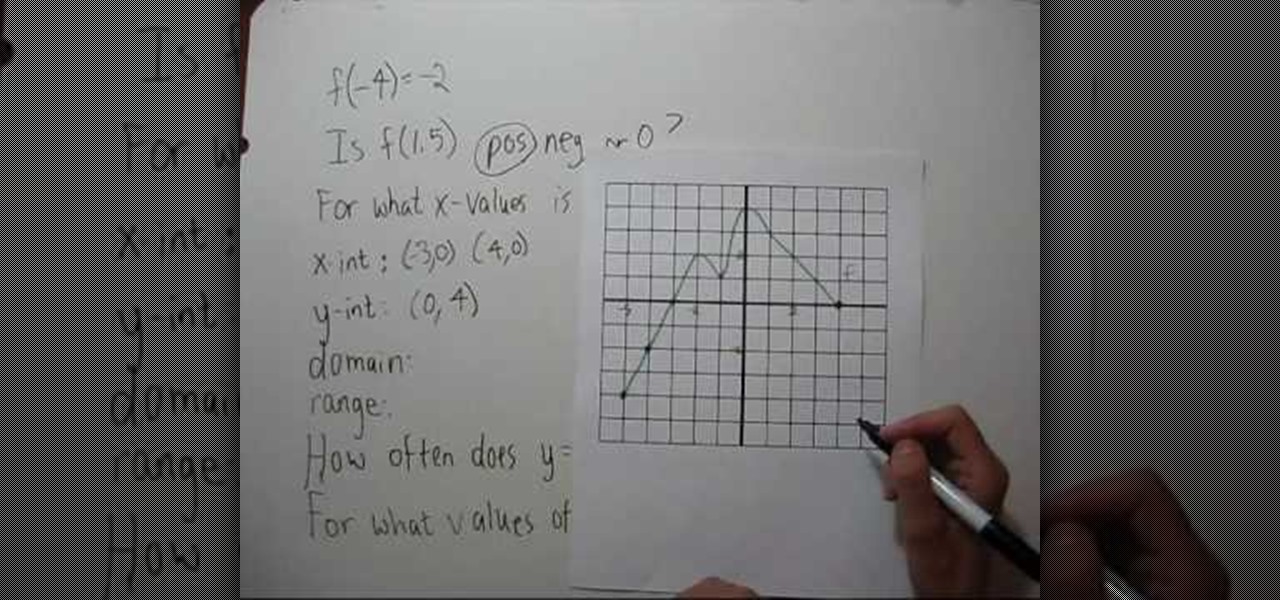
YouTube user NotesCollegeAlgebra teaches you how to interpret a graph. You will learn how to read it and extract information. You go to the graph to see that f(-4)=-2. f(1.5)=2, so it's positive. You then have the question: For what x-values is f(x)<0? You go to the graph and see that you come up with (-5,3). The x-int is (3,0) (4,0). The y-int is (0,4). The domain is (-5,4) and the range is (-4,4). You then have the question: how often does y=7/5 intercept the graph? The answer is 4 times. T...
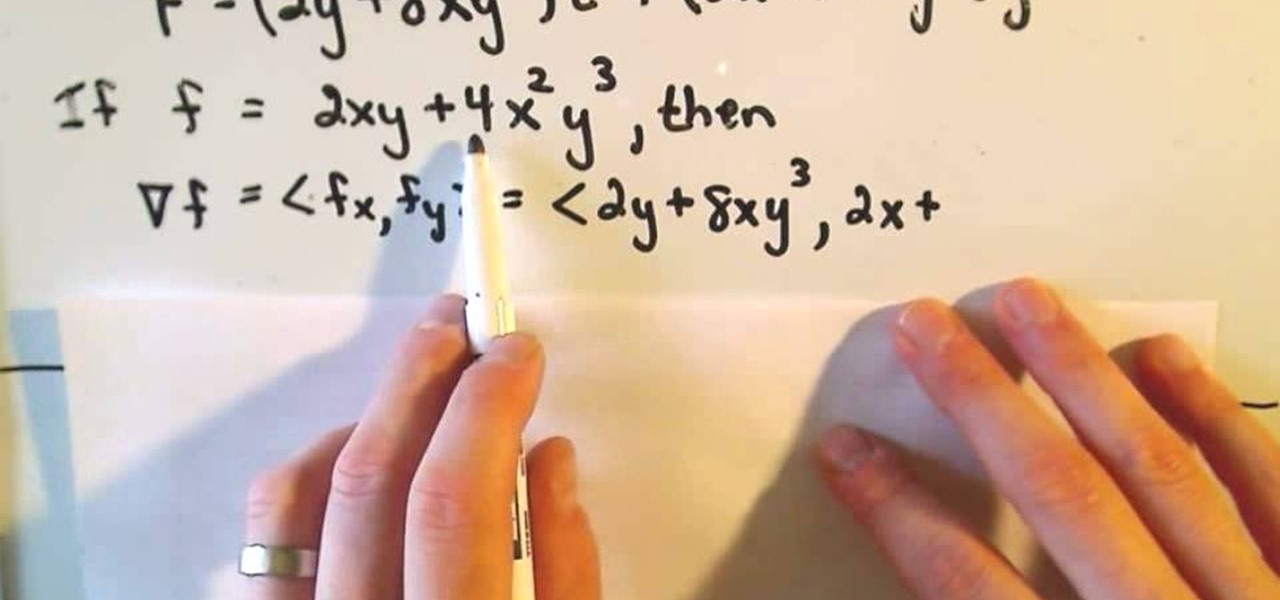
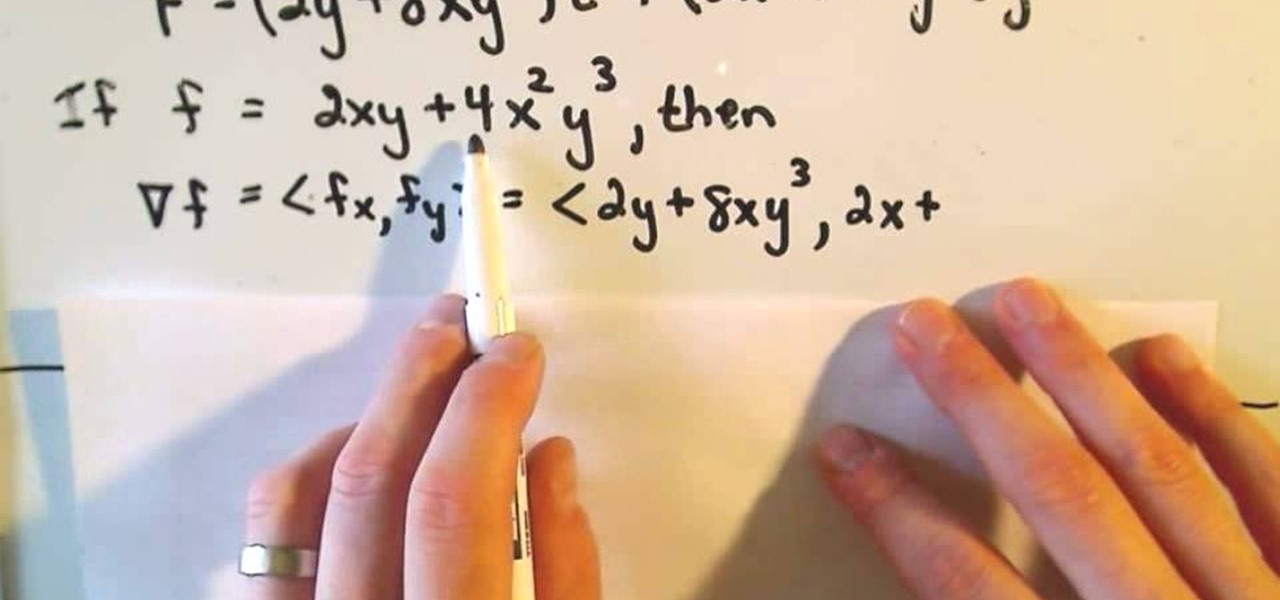
A conservative vector field is defined as being the gradient of a function, or as a scaler potential. Conservative vector fields are not dependent on the path; they are path independent. Conversely, the path independence of the vector field is measured by how conservative it is. These fields are also characterized as being ir-rotational, which means they have vanishing curls. Actually, ir-rotational vector fields are conservative as long as a certain condition on the geometry of the domain is...

After closing its office last year, enterprise AR company Daqri has moved on to the final stage of its lifecycle with the liquidation of its assets.
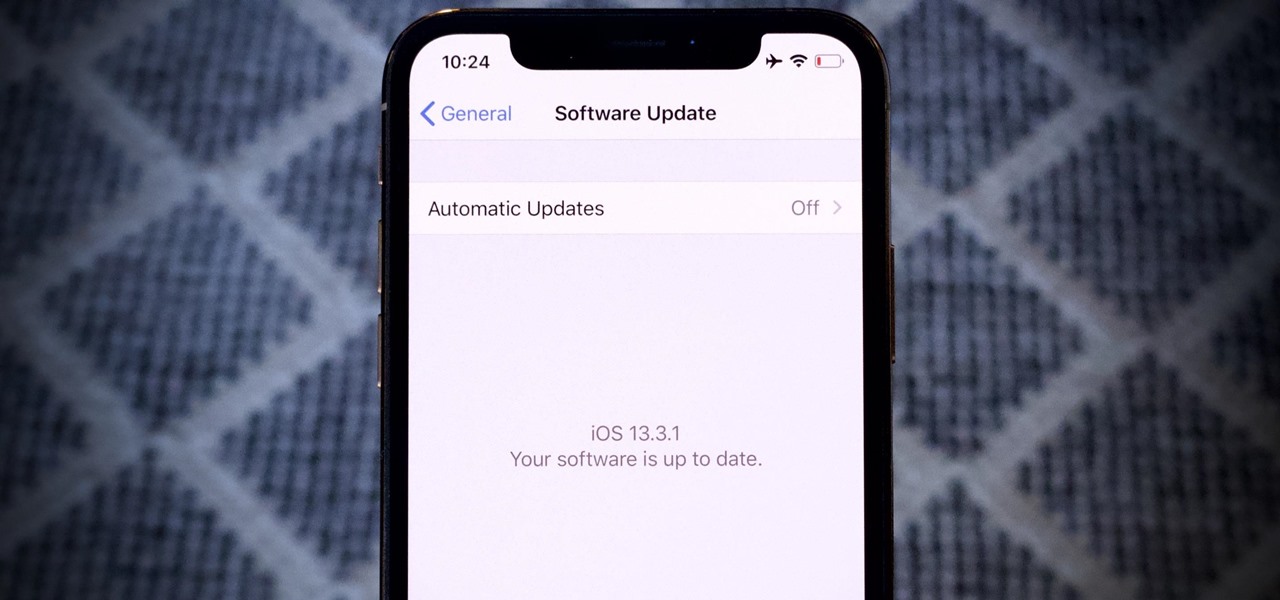
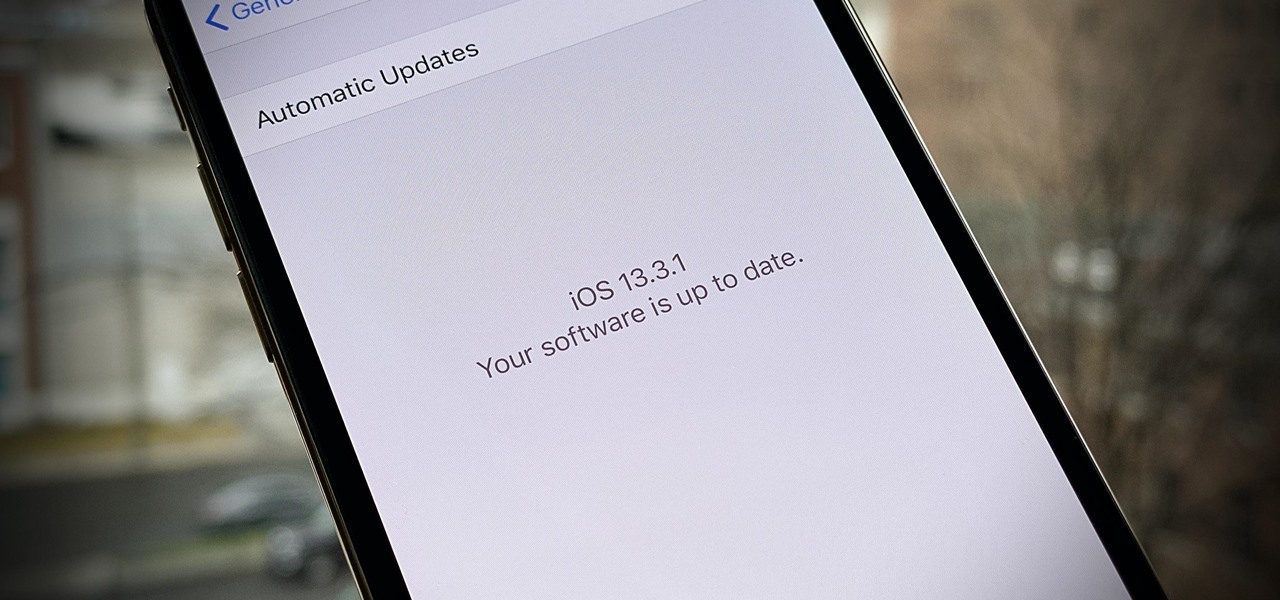
Since the release of iOS 13.3 beta 3 on Nov. 20, Apple has remained silent on new beta updates. That's likely because there was a holiday the following week, and then all of the major shopping events after that. But now, it's back in the game, and on Thursday, Dec. 5, Apple pushed out iOS 13.3 developer beta 4 and public beta 4.

While Apple has moved on from Touch ID to Face ID in newer iPhone models, there are still plenty of iPhones with fingerprint sensors — in fact, Apple's second-generation iPhone SE is the first new Touch ID iPhone in three years. With Touch ID, you can register up to five fingerprints, but it doesn't stop there. Using a little-known trick, you can sneak another five fingerprints in there for a total of ten.

Auditing websites and discovering vulnerabilities can be a challenge. With RapidScan and UserLAnd combined, anyone with an unrooted Android phone can start hacking websites with a few simple commands.

Not all threats to our privacy come from hackers thousands of miles away. Often, we just want to keep our data safe from those around us, who may snoop in our phones or demand we reveal our secrets. That's where BlackBerry Locker comes in.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

In the digital age, maintaining your privacy is a never-ending battle. All sorts of companies and agencies have access to your data, and quite a few can eavesdrop on almost every method of modern communication.

Apple just showed off iOS 9 and its new features at WWDC 2015, including multitasking support for iPads (finally!), a new Low Power Mode to save battery, local area search and transit directions in Maps, a highly improved "Proactive" Siri, a better Spotlight search, new apps, and so much more.

The wait is over. The Samsung Galaxy S6, arguably the best Android phone of this year, has just launched. There was already a lot of hype about this super phone—its looks, its specifications, and its other functions have been under the microscope for quite some time. It will not be a good idea that you take this phone in your hand and use it in the same fashion as you have been using your other phones in the past.

Apple just unveiled iOS 8 at the Worldwide Developer's Conference, and it has a lot of exciting features to play around with. Unfortunately, it won't be available to the public until this coming fall—but that doesn't mean you can't get it right now.

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.

Parking. Ugh. Parking is about as fun as running through a swarm of bees while being chased by a pack of wolves from The Grey.

You've written the great American novel, and you want to make sure that your story stays yours. Register your copyright and preserve your intellectual rights. In this video, learn how to copyright produced material.

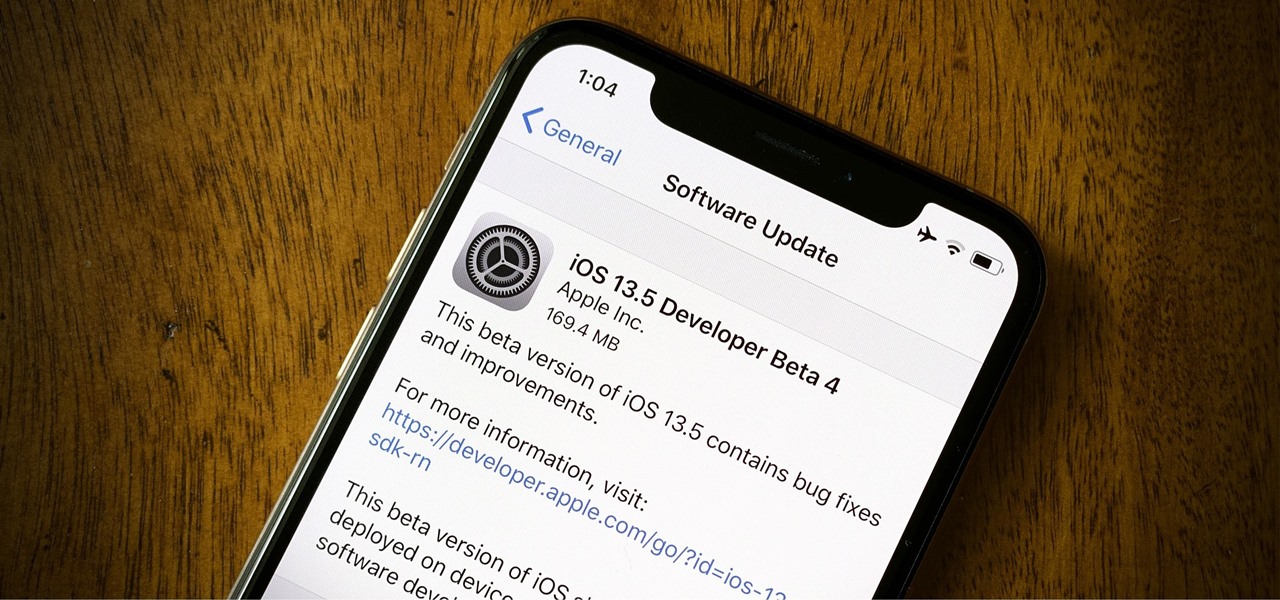
Apple just released iOS 13.5 for iPhone developers today, Monday, May 18. This GM (golden master) update comes 12 days after the release of iOS 13.5 dev beta 4, which introduced updated COVID-19 exposure notification logging settings and the ability to share your Medical ID with first responders when placing an emergency call.

Apple released the fourth developer beta for iOS 13.5 today, Wednesday, May 6. This update comes one week after the release of iOS 13.5 dev beta 3, which introduced Apple and Google's joint COVID-19 exposure notification API to iOS for the first time. Apple updated that settings page to now include an "Exposure Logging" setting instead.

Beta testing on iOS is as Wild West as Apple gets. From feature-filled to featureless releases, there's a high level of unpredictability for what to expect. And not everything is found right away. For instance, last week's developer beta 2 added a new feature that was left undiscovered until three days later. So what has Apple hidden in today's iOS 13.3.1 dev beta 3 update?

Did you take a vacation this holiday season? It appears Apple did. After the release of iOS 13.3.1 developer beta 1 (then public beta 1 one day later), iOS beta testing went silent for almost a full month. With 2019 now in the books, it seems Apple is back to work, as developers received iOS 13.3.1 beta 2 today, Tuesday, Jan. 14.

The Pixel 4 and 4 XL are the first Android phones released in the US to support secure facial recognition. You no longer have to hate on your Apple's friends because you now have "Face ID" as well. So I assume you want to set it up right away — here's how.

Millions depend on Google Maps for directions, and it's easy to see why. The app comes with tons of features like offline navigation, location sharing, and more. Google is far from done, however, and continually improves upon its navigation app to make it even more efficient and safer to use.

The quality and length of your sleep will almost always dictate how the rest of your day unfolds. Sleeping fewer hours increases your chances of spending the day in a tired and cranky state, while having a restful night's sleep contributes greatly to being alert and productive. Luckily, if you want to track your sleep patterns to figure out how you can improve your circadian rhythm, Samsung Health has you covered.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.

Last week, augmented reality startup Proxy42 released Father.IO, a multiplayer game that turns any indoor or outdoor space into a laser tag arena.

It seems that mobile app developers are constantly coming up with new ideas to apply augmented reality, with Apple's ARKit promising to increase adoption in apps exponentially.

Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

3D Touch on the iPhone 6S and 6S Plus is a pretty cool feature, and will only get better as more developers begin to roll its functionality into their apps.

Hi everyone! Last time we explained what roles Ebp and Esp registers have. We first introduced function's stack frame building, return address and calling conventions, but left some of the concepts floating without a full stop.

Text input on a touchscreen device is constantly evolving. From early beginnings of pecking out each individual character to today's predictive text and gesture keyboards, we've already come a long way.

Nearly two years ago, Peter Chou, CEO of HTC, confirmed that the company would no longer be locking bootloaders. Whether or not they've actually lived up to this claim is debatable. Any phone bought from a wireless carrier comes locked. Only the new HTC One Developer Edition ships with an unlocked bootloader, and it does not have any carrier add-on software installed.

I love my Mac just the way it is. Well, minus the fact that I accidentally deleted iPhoto and would now have to pay $14.99 to get it back. Other than that, my Mac is pretty sweet.

This video tells us the method to prepare a gourmet beef stroganoff. Take 3/4lb sirloin steak tip. Cover it with 1 teaspoon of soya sauce. Cover it and put in the refrigerator for 15 to 20 minutes. Take 1/2 teaspoon of mustard, 1 teaspoon of sugar and 1/4 teaspoon of black pepper. After this, heat 1/2 teaspoon of salad oil and let it smoke at medium high. Brown both sides of the meat. Take out the meat when the internal temperature registers 125 10 130 degrees fahrenheit. Add 1/2 lb mushrooms...

This video tutorial from gogeeks shows how to install mIRC application on Mac OS X operating system.

In this video Dynamite Jack from Hugegamer shows you how to get the most out of your Playstation 3 by setting it up to instantly stream movies and video from Netflix. Start by ordering your free Netflix streaming disc, from Netflix, once you receive the disk load it into your PS3 and start your system. You will also receive an activation code so that you can go online to register your PS3 with your Netflix account. Once your PS3 is booted go to the "video" section on your PS3 and bring up the...

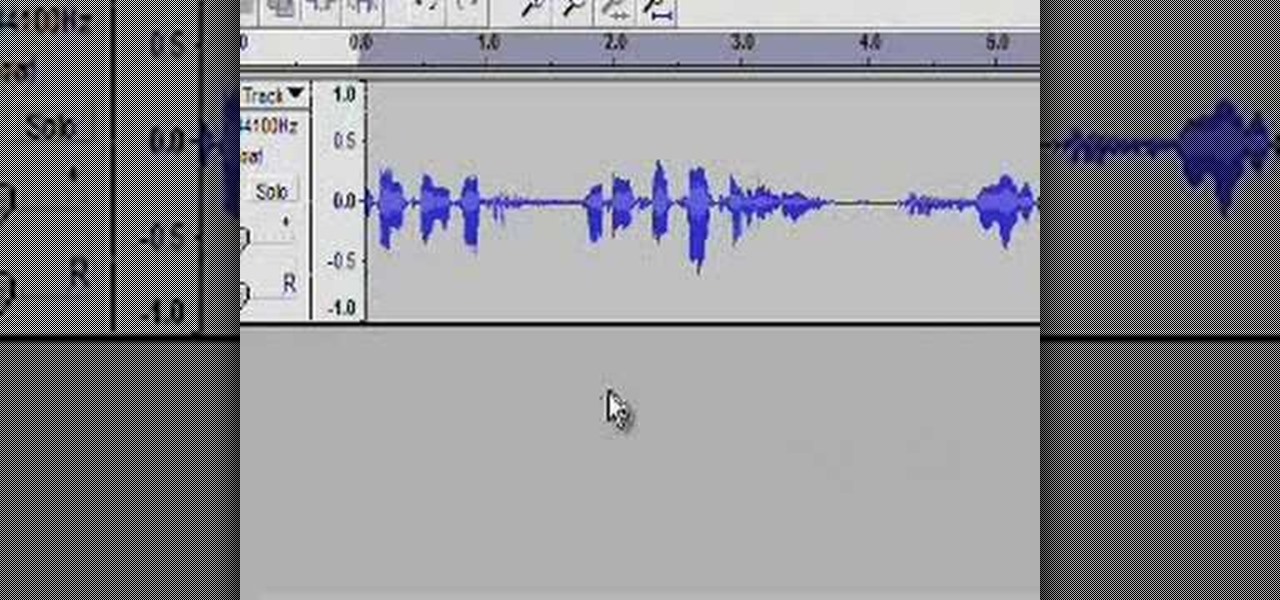
RabbidHedgeHog shows viewers how to easily make a podcast. This features how to make the podcast with the program Audacity. First open your internet browser and go to Audacity. Scroll down to download Audacity 1. 2. 6, save the file, Install and download the program. Now, open up Audacity which is basically a recorder. Connect your microphone which will allow you to record. Click edit, preference, find microphone and select the device you will use. Now, record your podcast by clicking the red...

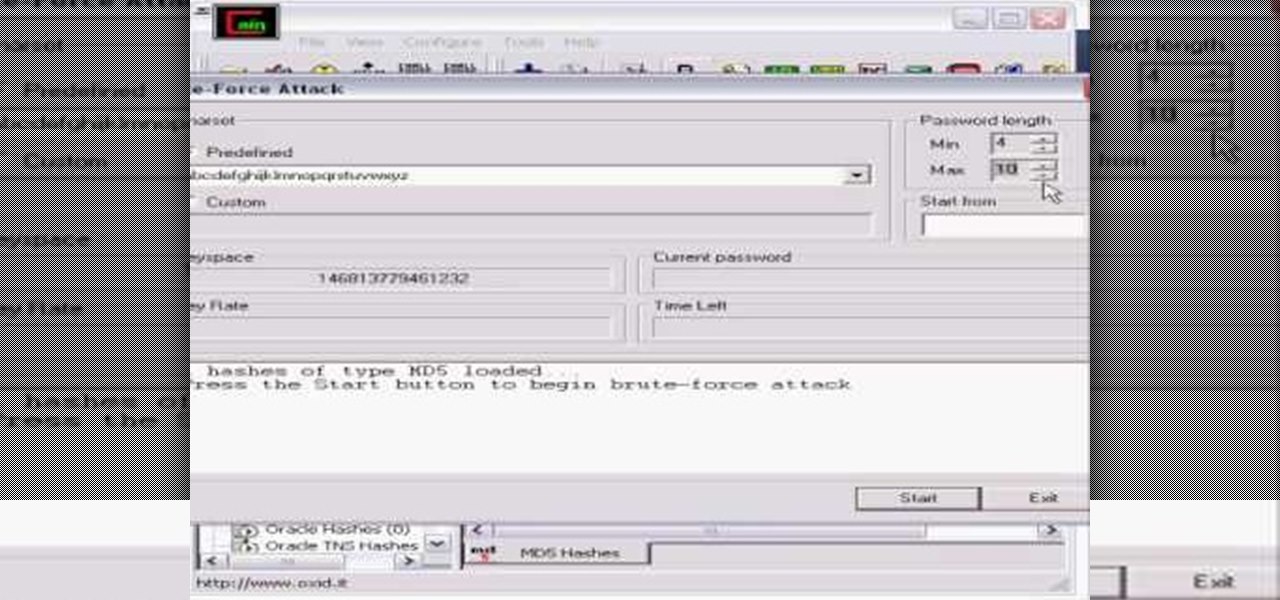
Whatever your reasons for doing it, if you are trying to hack passwords, it helps to have the right software for getting the job done. With the Cain and Abel program, you will be well on your way to hacking even the toughest personal passwords.

Set the packaged roast on the kitchen counter. Let the roast warm to room temperature for an hour or more. This helps it to cook evenly.