You probably already know that your digital pictures have quite a bit of information embedded in them. What you might not know is just how much personal information is included in that metadata, including your camera information, and in some cases, even the precise GPS coordinates of where you took the picture.

Do you have two dollars and a water bottle? Then you can put together this simple but awesome solar-powered lantern that will provide more than enough light to read by at night.
Unless you're living in some weird parallel universe where plug-in light bulbs are the norm for household lighting, chances are you've had to unscrew a light bulb every now and then.
This is a video teaching how to use the Wiiflow USB loader with an external hard drive. This will allow you to store Nintendo Wii games in an external Desktop hard drive. The narrator shows you his consoles and his hard drives while loading the cover on his Wiiflow. The Wiiflow will let you store all of your Wii games onto a large hard drive, instead of your Nintendo Wii. It allows you to play the games from the USB loader without a game disc. This is a convenient way to play your games witho...

In this two part how to video, the Beverly Hills Organizer, Linda Koopersmith demonstrates how to use skirt hangers for neat and compact storage. The way you store your clothes makes a huge difference in the appearance and longevity of your garments. Watch this organizing tutorial and you will be properly hanging and storing your skirts in no time.

Do you have trouble remembering where you put your keys or what you need to buy at the grocery store? You're not alone, millions of Americans suffer from bad short-term memory, but there are ways to help improve your memory. Watch this video to learn how to play some easy memory games that will help you remember things.

Fring is a free app available from the Apple store which will allow you to use video chat, Skype or AIM on your iPhone 4 over a 3G network. This tutorial demonstrates how to use the app with your iPhone to make video calls.

The perfect craft for storing Valentine's cards and candies. Watch this video to learn how to make a simple and sweet present for your Valentine. It's easy to do with your kids, and perfect for holding the many cards and candies your kids will come home with. The woven quality gives it a unique look, and will make your kids the envy of the classroom!

Depending on where you live, you will have to prepare for the hazards from different types of natural disasters. You can sleep easy if you have a secure location, stalked with food and supplied you might need if there is an emergency.

Put your imagination into solid form by working with clay. Now all you need is the clay. No need to buy it at the store when you can make all the clay you like at home. Clay is a fun medium for adults and kids to work in.

Knowing how to build a box out of plastic is a highly useful skill. In this video, the folks at Tap Plastics show us how to do it. The example they use is how to make an organizer for your cutlery drawer, when organizers from the store won't fit. But there are many other possible applications for plastic boxes.

A cool skimboard can really set you back. What's more, you're only buying designs off the shelf. In this video, you'll see how to make your own skimboard out of carbon fiber. It will be a lot cheaper than the store-bought kind, and you'll be able to design the graphics yourself.

Check out this computer hacking video tutorial from Unorthodox Hacking. The subject of today... hidden Windows passwords. This is a short episode with a fast pace is intended to expose a few of the areas where Windows hides stored authentication credentials. Be very cautious the next time you use a public kiosk!

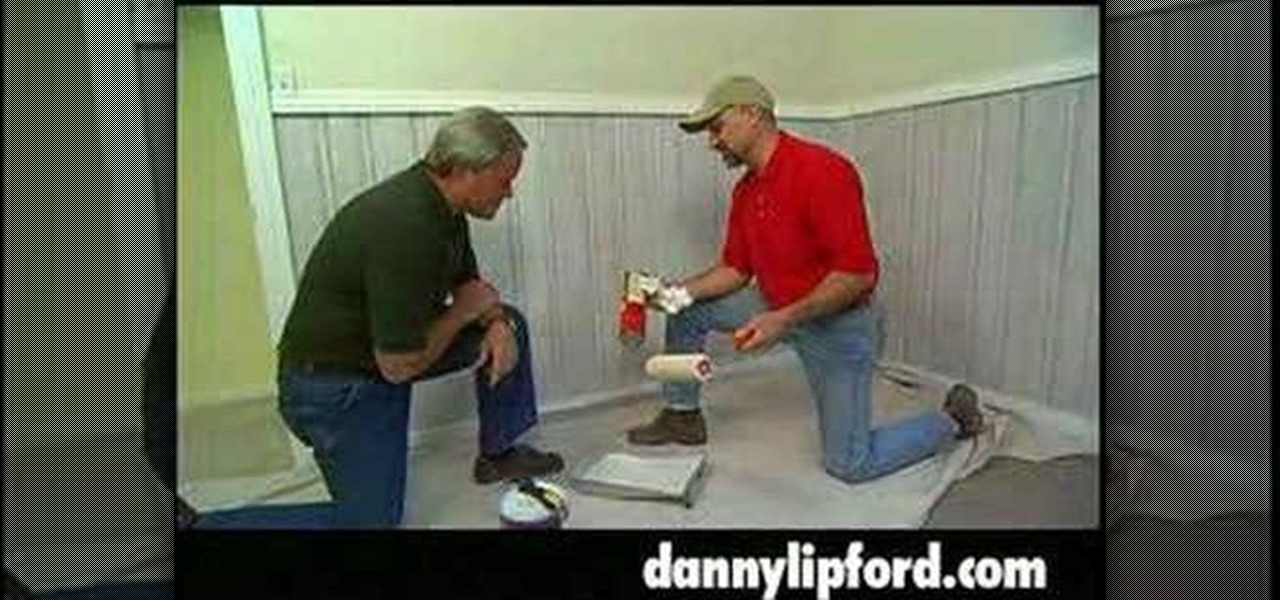
Washing at your paint rollers at the end of every day can be a real pain. If you plan on painting again the next day, cleaning your rollers can seem pointless. In this how to video a professional painter shows Danny Lipford a great trick for storing your paint rollers over night so they don't dry out. All you need is a Pringles chip can to keep your paint rollers moist overnight.

We all love the sandies sold at the store. This how to video shows you how to make hickory nut sandies with fresh edibles. These nutty cookies are super easy to make, watch and learn how to bake these hickory nut sandies.

Making homemade pickles at home is a lot less expensive than buy them. Watch this how to video to learn how to pickle homegrown cucumbers. If you don't grow cucumbers, buy them at a grocery store. Add some fresh garlic, dill, water, vinegar, and pickling salt to your jar and you are ready to pickle.

In this how to video, the Beverly Hills Organizer, Linda Koopersmith demonstrates how to fold a thong for compact storage. The storage of your clothes and underwear makes a huge difference in the appearance and longevity of your garments. Watch this organizing tutorial and you will be properly folding and storing your clothes in no time.

Ok first thing first, you need to download the HackPack. In there is necessary things I use in the video. If you are on XP you must install .net frame work. ( the dotnxfx file) vista users don't have too.

Ok, let's pretend that you just got back from the store with a $200.00, maybe $300.00 silk blouse. You put it on, it looks perfect. You go out on the town, everyone else loves it, you're the center of attention. Then you come home, you go to hang it up, and there is a huge stain on the back. This how to video tells you how can save that $200.00 blouse for only $1.50.

Store-bought spices are convenient, but making them in your own kitchen brings a fresher flavor to your meals. Follow these steps for making chili powder at home so you can alter its spiciness.

Dr. Mercola addresses factors that could degrade the quality of this beneficial form of nutrition. Watch and learn how to make the most out of fish oil supplements.

If you have an Etsy store, or a small business, this video is full of great ideas. Learn how to make your own creative tags for your items.

Sam from Pete's Candy Store shows us how to mix a Ginger Sour.

Photos are stored in the library of iPhoto and it's important to keep them organized. Photos are best viewed by events. Each time you upload photos, those photos are put in one event. Follow along with this tutorial as it shows you how to use events to organize your photos.

Codenamed "Nougat" after the sugary stuff that fills your Snickers bar, Android 7.0 is living up to its name with tons of sweet features. There's almost too many changes over Marshmallow to cover in one go, with new functionality ranging from a revamped Doze Mode for battery saving, to split-screen apps, and even an easier update process. All told, the Nougat update has a lot in store for your phone or tablet.

I'm an Android user. Over the course of the past seven years, I've owned ten different smartphones—all of them powered by Android. This isn't due to some blind trust in Google or some unfounded hate for Apple, either, because I've always made sure to get my hands on each iPhone iteration along the way to see what it had to offer.

There are literally hundreds of granola recipes floating around the internet—but I can tell you right now that they're all completely unnecessary. You don't need a recipe to make granola; I've been making granola for years and have never once used one!

While attempting to hack a web app, there may come a point where the attacker may have to escape the default directory in order to access unauthorized files. This is known as a directory traversal attack. Much as the name implies, this attack involved traversing the servers directories. But in order to move to an unauthorized directory, we need to know where those directories are. Today we'll be building a tool to brute force these directory locations based on HTTP response codes. Before we g...

If you have a local Trader Joe's, you know first-hand how enchanting the frozen aisles are—almost every item offers the promise of a delicious meal or dessert. (We're always tempted to open the package and eat the cookie butter cheesecake, stat.)

Welcome back, everyone. In the previous part of this rapid-fire miniseries, we built the victim portion of the shell. Today, we'll be building the attacker portion. This script will initialize interaction with the victim portion of the shell, send commands, and receive the output.

Welcome back, my novice hackers! In this series, we have been exploring how a forensic investigator can find evidence of illegal or illicit activity. Among other things, we have examined the registry and prefetch files for artifacts and have done some rudimentary forensic analysis. For those of you who are seeking career as a forensic investigator or security engineer, this can be invaluable training. For hackers, it might be life-saving.

Juicing fruits and vegetables is very beneficial to your health. For some, it's a trend; but to me, it's a part of my morning routine.

What's up readers? Today I'll be introducing to you a new vulnerability called the Format String vulnerability (in case you missed the title). It won't be much, just a little motivation to keep you guys going. A little teaser, if you may.

If you open your refrigerator door and find leftovers there, then you are fortunate—even if you don't realize it right away. Leftovers are the ultimate budget hack because they maximize the value of your meals; and it's a smart way to save money while making the most of your food purchases.

The first written account of "stock" as a culinary staple goes back to 1653, when La Varenne's Cookery described boiling mushroom stems and table scraps with other ingredients (such as herbs and basic vegetables) in water to use for sauces. But really, the concept of stock has probably been around for as long as people have been using water to boil food.

When anyone brings up Tasker, the first topic that always gets discussed is how powerful the Android automation app can be. But all of that power can be overwhelming for some people, so even if you're a Tasker pro, it's hard to share your awesome creations with friends that don't quite understand what's going on.

I have been on Null Byte for a long time, a very long time and. I havent always had an account here, ive like many of you also have, been looking and decided to make a profile to contribute.

Welcome back, my nascent hackers! In the conclusion of the Mr. Robot television series, Elliot and fsociety successfully completed their mission of encrypting all of Evil Corp's data with AES-128 encryption and destroying the key.

Oven space is scarce on that fated fourth Thursday of November. Even if you can find a spare space for pumpkin pie on the bottom shelf, you risk turkey drippings overflowing from above and ruining your beautiful dessert — not to mention a burnt crust from different temperature requirements. The bottom line is: oven real estate is valuable, and it's tough to multitask cooking for Thanksgiving when every dish requires baking or roasting.

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...