
How To: Perform easy card tricks
Learn a series of beginner's card magic tricks.


Learn a series of beginner's card magic tricks.
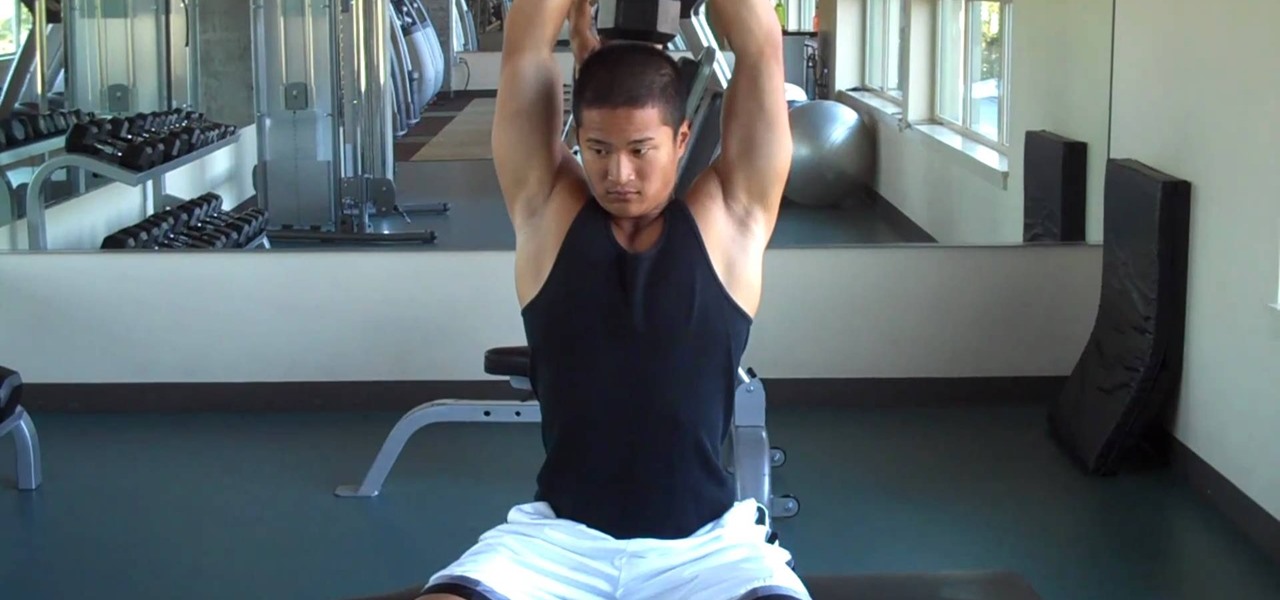
Strengthening your arms takes determination and effort, and one surefire way to get there is by working out your triceps. Triceps extensions are the perfect exercise for those of you with dumbbells at home. It's a great workout to get those dreamy arms and is a basic exercise that isolates the triceps. After doing a couple sets you may start to feel the burn! Lift safety!

This video demonstrates two different ways to make delicious butter. For the first method, take some whipping cream and whisk in a couple of scoops of plain yogurt. That’s all there is to it. Then let it sit unrefrigerated for six to eight hours. The yogurt culture will grow in the cream and add delicious flavor to the butter.

Purify water 3 different waysThere are three water purification methods demonstrated: Chlor floc tablets, 2% tincture of iodine and a MSR hand filter.Gather water into your plastic bottle. Add one chlor floc tablet to one liter of water. Close the top and shake the bottle for one minute. Wait seven to ten minutes. The floculation agent in the tablet takes the dirt out of the water so that it can be separated. Strain the water using a bandana over the cup to trap all loose sediment. The water ...
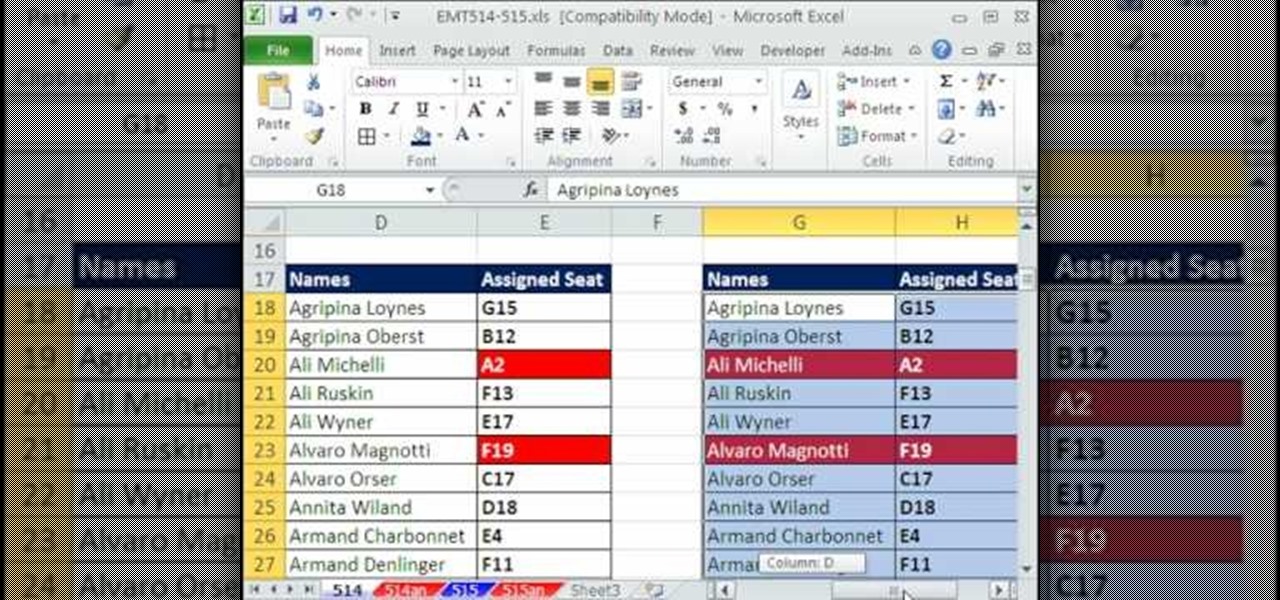
New to Excel? Looking for a tip? How about a tip so mind-blowingly advanced as to qualify as a magic trick? You're in luck. In this Excel tutorial from ExcelIsFun, the 514th installment in their series of digital spreadsheet magic tricks, you'll learn three methods for conditionally formatting duplicate values:

Have you ever heard of tradigital art? Tradigital art incorporates traditional materials with digital media. This is a combination of such techniques as illustration with Decocolor Markers, Prismacolor Markers, pencils, and Photoshop. Watch this tutorial to learn how to enhance traditional art methods with digital media. It illustrates the tradigital process step-by-step. Make sure to pause the video after each step and look at the screen every few seconds while you are drawing.

Clicker train your pup to limp with this training video. This is a video on how to teach your dog to limp using the clicker training method.

If you call yourself a hobbyist or a kid at heart, you know that remote-controlled vehicles are more than just fun. If you're a serious R/C man, you'll know all about doing everything to your model truck or car, like fixing wheels, vamping the pinion gears, waterproofing, troubleshooting, electronic diagnostics, setting up, programming, and finally... racing. As much as you know about these remote-controlled vehicles, it will never be enough; you'll always be looking for more...
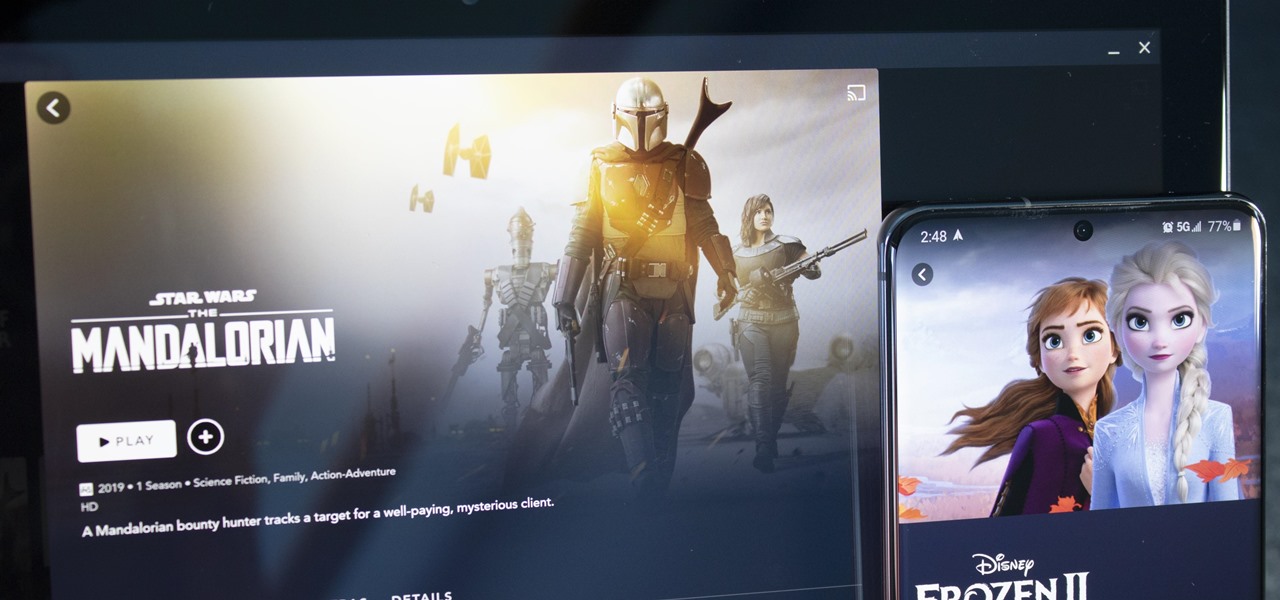
With shows like "The Mandalorian" and movies like "Frozen 2," Disney+ has quickly become a must-have streaming service. However, with Netflix, Amazon Prime Video, and Hulu, adding another subscription-based service can become expensive — but there are ways to trim down the cost.
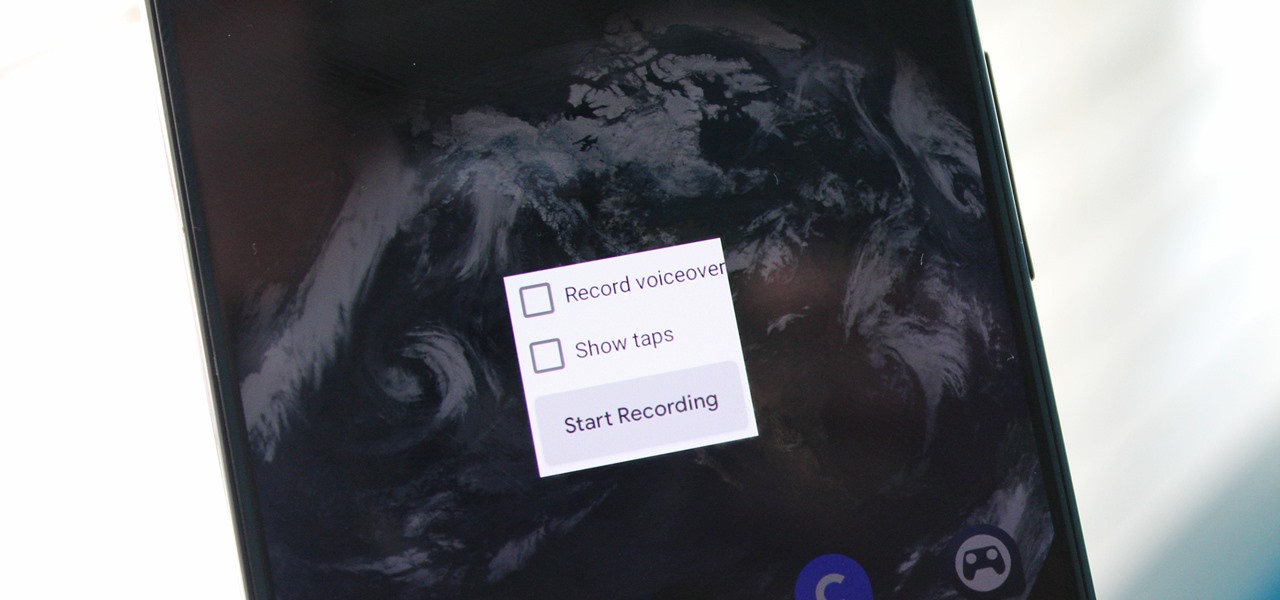
Downloading third-party screen recording apps can be dangerous. The primary function of these apps is being able to record everything on one's display, so it's easy to see how a malicious developer could exploit this for their own gain. That's why the addition of Android 10's built-in screen recording is so impactful.
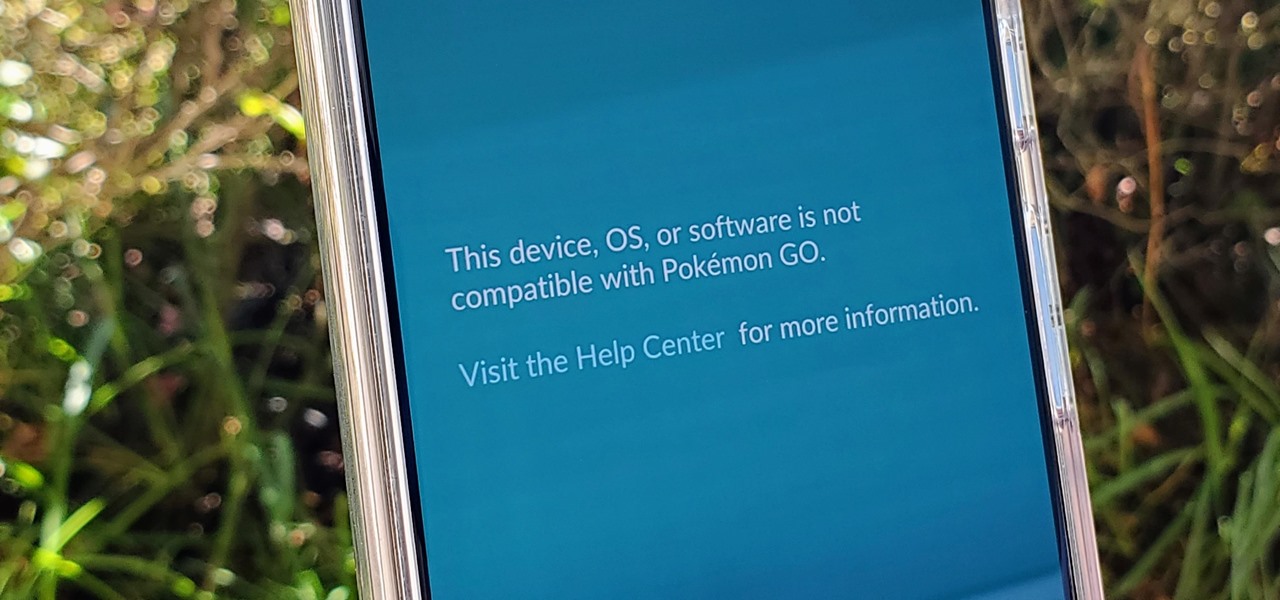
If you're a root user who has played Pokémon GO over the years, then you're probably familiar with the detection methods used to spoil your fun. The game's developer, Niantic, has publicly mentioned their ongoing battle with rooted Android phones and are unwilling to let up. They have a no-nonsense approach to try and keep you from playing, and they've stepped their game up once again.
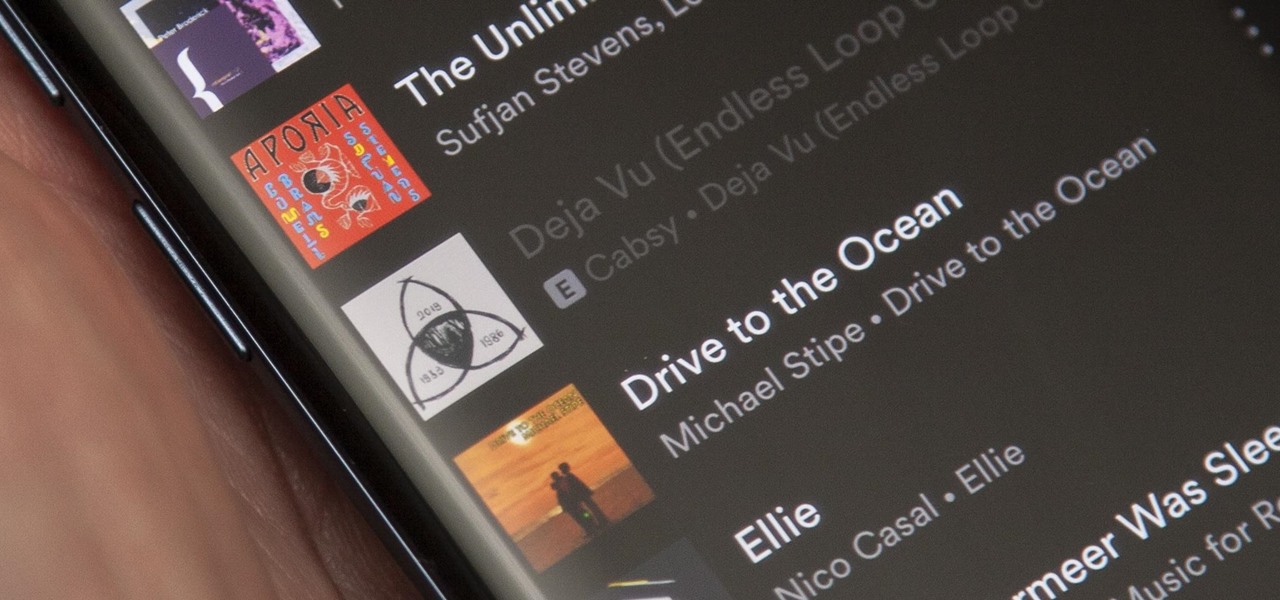
When you dislike or hide a song in Spotify, you'll never hear it again in the playlist or radio station that you blocked it from. If you bury it for the entire app, it won't play anywhere. But that doesn't mean you can't get it back if you change your mind.
No one likes in-app advertisements, especially in mobile gaming, but they're necessary because they offer developers a way to make revenue without having to charge you to play. In some games, in-app purchases give you the chance to remove ads, but what can you do about apps that don't offer the option to kill ads?

With EA chief executive Andrew Wilson stating the official mobile version of Apex Legends won't arrive until the 2021 fiscal year, fans have to wait at least another year to enjoy their favorite battle royale game on the go. But for those who can't wait, there are ways to play the game on iPhone and Android right now.

Apple unveiled the latest generation of its flagship earbuds, AirPods Pro, on Monday, Oct. 28. Aside from the increased price tag, new in-ear design, and wider charging case, the biggest change by far is in Active Noise Cancellation. Finally, we can listen to AirPods on a plane, walking by a busy road, anywhere with a lot of noise pollution. But how does it work?
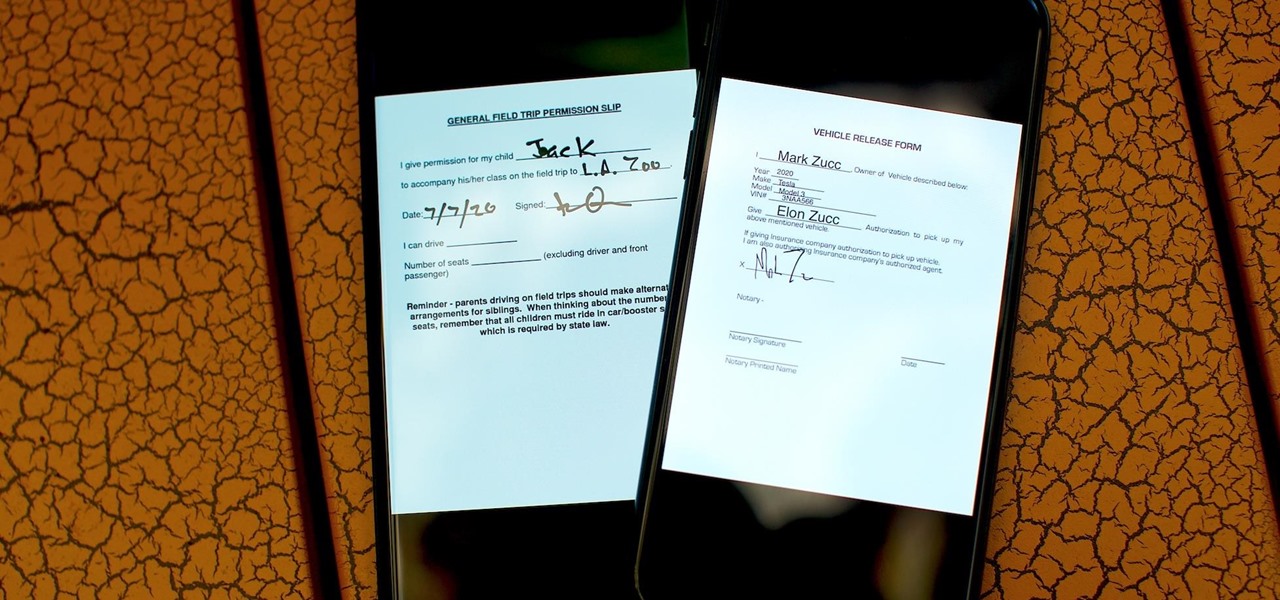
As paper forms become a thing of the past, it's becoming commonplace to fill out contracts, rental agreements, waiver release forms, and non-disclosure agreements online. You can easily fill out forms on your laptop, but how can you best do this using your iPhone or Android device?
Being an Android user and having friends who are in the Apple ecosystem does not need to be a pain. You can easily send high-quality videos to iPhone users, so don't feel handicapped without access to iMessage. Sending high-resolution videos to iOS users is easy with this fast video-sharing method.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.
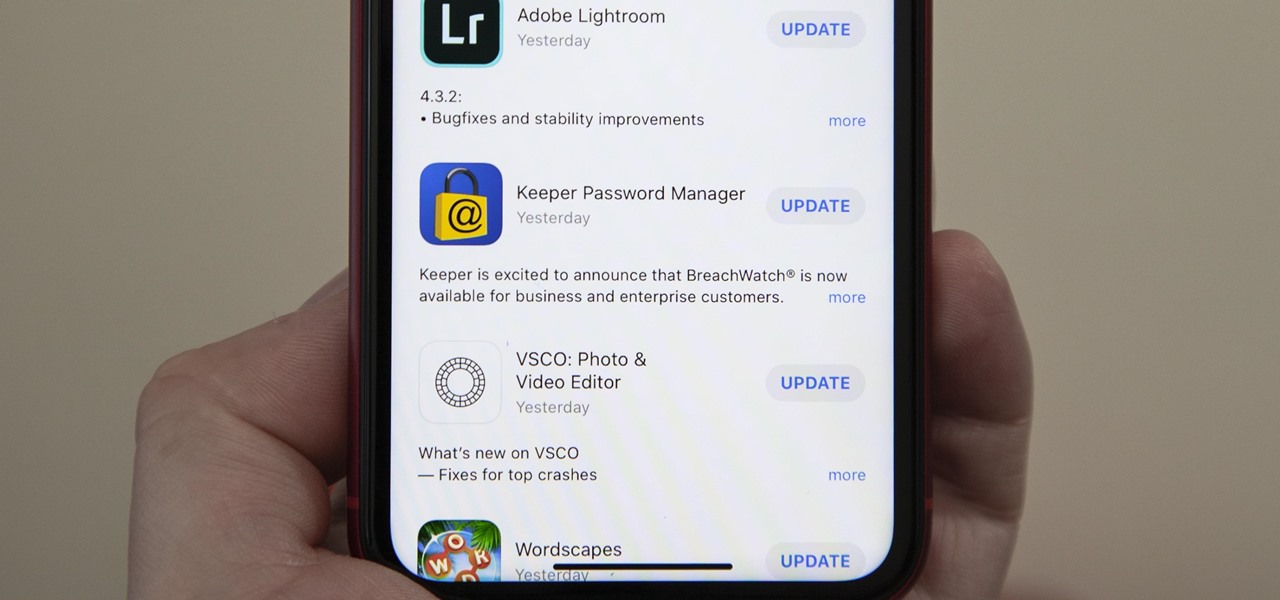
Viewing available app updates and recently updated apps on your iPhone is more confusing and less obvious on iOS 13 than it was in iOS 12 and older.

If you want your photos to look like they came straight out of a movie scene, the best method is to use split toning. Many Hollywood producers use this effect to recreate the cinematic look of cameras before the digital film era, which is why most people associate split toning with a cinematic feel.

Every photo you take is brimming with metadata such as iPhone model, date and time, shooting modes, focal length, shutter speed, flash use, and geolocation information. Share these pictures with friends, family, or acquaintances via texts, emails, or another direct share method, and you unwittingly share your location data. Even sharing via apps and social media sites can compromise your privacy.

Back in July, Google rolled out a new design for the web version of Gmail. The rollout included new features alongside the visual changes, one of which being Confidential Mode. This new privacy-centric feature has now finally arrived on the mobile app version of the service, and here's what you need to know.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.
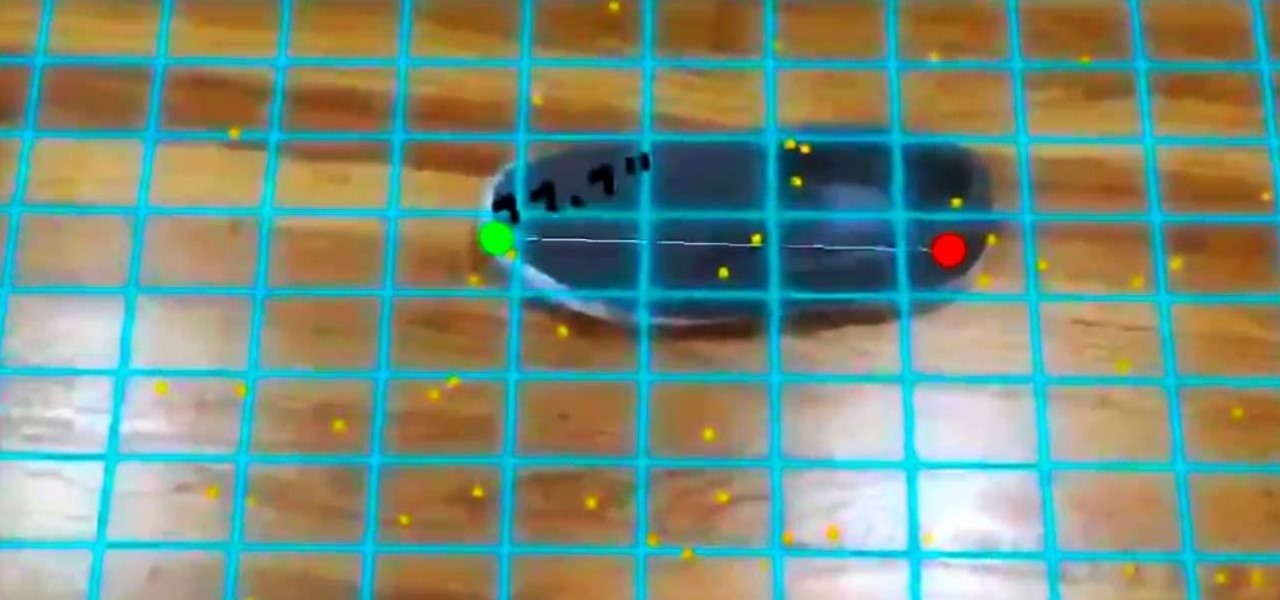
In our last ARKit tutorial, we learned how to measure the sizes of horizontal planes. It was a helpful entryway into the arena of determining spatial relationships with real world spaces versus virtual objects and experiences.

I've called 911 accidentally more than a few times on my iPhone using the Emergency SOS triggers, but it's also just as easy to trigger an unintentional call to emergency services using an Apple Watch. These accidental 911 calls can put a strain on local public-safety answering points, or call centers, as well as local authorities and emergency medical technicians.
The share menu is a vital part of Android that lets you send data between between apps. Many of your favorite apps support the feature, including the new Direct Share sub-menu, which can lead to a messy share menu. However, there are a number of tools to clean up this clutter, three of which don't require root.

Know thy enemy — wise words that can be applied to many different situations, including database hacking. It is essential to performing adequate reconnaissance on a system before even thinking about launching an attack — any type of attack — and this is no different for SQL injection.

Android used to have a notification ticker, but those days are long gone. Now, important new messages pop up on the top half of your screen with what's known as a "heads up notification." If you're in the middle of something, these popup notifications can be pretty annoying — luckily, it's pretty easy to turn them off.

Over the past month, we've spent significant time covering Samsung's Oreo Beta program, and the detailed list of features in Oreo is extensive for the Galaxy S8 and S8+. Many of you were upset when the Galaxy Note 8 was left out of the official Oreo beta program entirely, but we found a method to install a beta Oreo build right now on the unlocked and US variants if you'd like to give it a try.
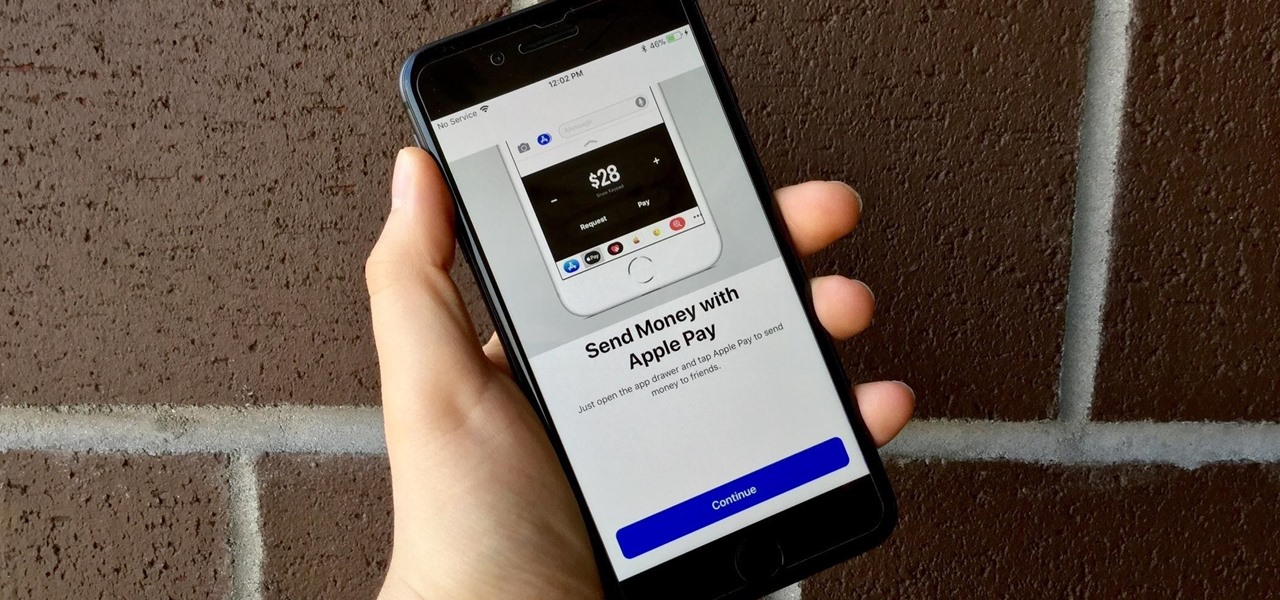
Move over Venmo, Apple Pay Cash is here, and it's built right into iMessage. If you're like us, you've been eagerly waiting to give this new feature a try on your iPhone ever since Apple announced it during WWDC 2017 back in June. While it was never released in the main iOS 11 update, it finally showed up in iOS 11.2.

The iPhone X is one of the most beautiful phones ever made, but the aesthetics stop just short of perfect due to one thing: That notch. It was a necessary evil since Apple had to incorporate a front-facing camera somewhere, plus it houses all the sensors for Face ID, but that doesn't change the fact that it looks a bit goofy.

There are a few different ways to install Magisk. If you're already rooted and you just want access to Magisk modules, you can use Magisk Manager to install the Magisk framework. Or, if you want to pass SafetyNet on a rooted device, you can switch from SuperSU to Magisk SU. But the best way to do it is to start fresh by installing Magisk on a non-rooted phone using TWRP.

Your smartphone is the perfect place to watch Hulu on the go. Whether you're looking to catch up on your shows in a hotel, or your phone is the only screen available, mobile streaming can be a lifesaver. But what about when you have access to a TV? Wouldn't you rather watch your favorite Hulu Original on the big screen than on your comparatively tiny smartphone?

Zooming in and out within Instagram Stories is a good way to take your videos to the next level. Whatever a next level is. Sometimes I just run out of words to describe how fun using Instagram is, so for today, I got "next level," which means whatever you want it to mean.
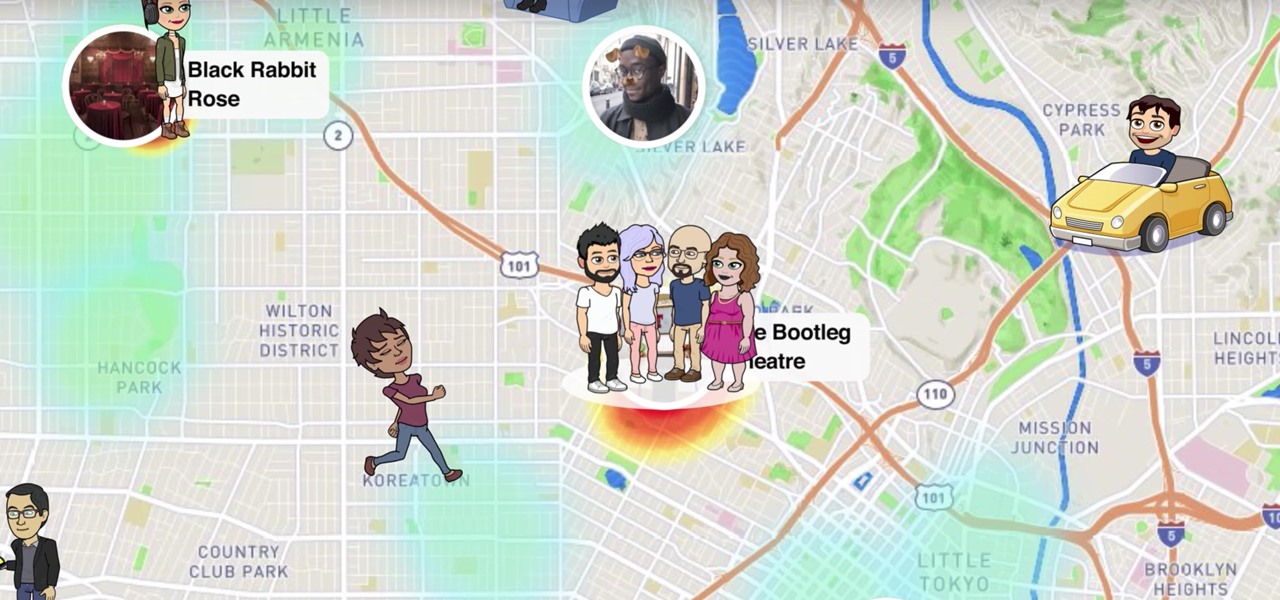
Snapchat recently updated their Android and iPhone apps with a new feature called Snap Map which lets you share your current location with other Snapchatters, as well as see their current locations. It may sound like an interesting new feature, but sharing your exact location with all of your Snapchat followers is dangerous, to say the least. Luckily, it's easy to turn this feature off.

Dutch filmmaker Anthony Van der Meer published his 2015 thesis short from Willem de Kooning Academy in South Holland online in December 2016. It's a brilliant piece of work that managed to be touching, alarming, and informative at the same time. His documentary, which already has over 6 million views on YouTube, covered the journey made by a stolen smartphone and how the theft and ensuing tracking affected all parties involved.
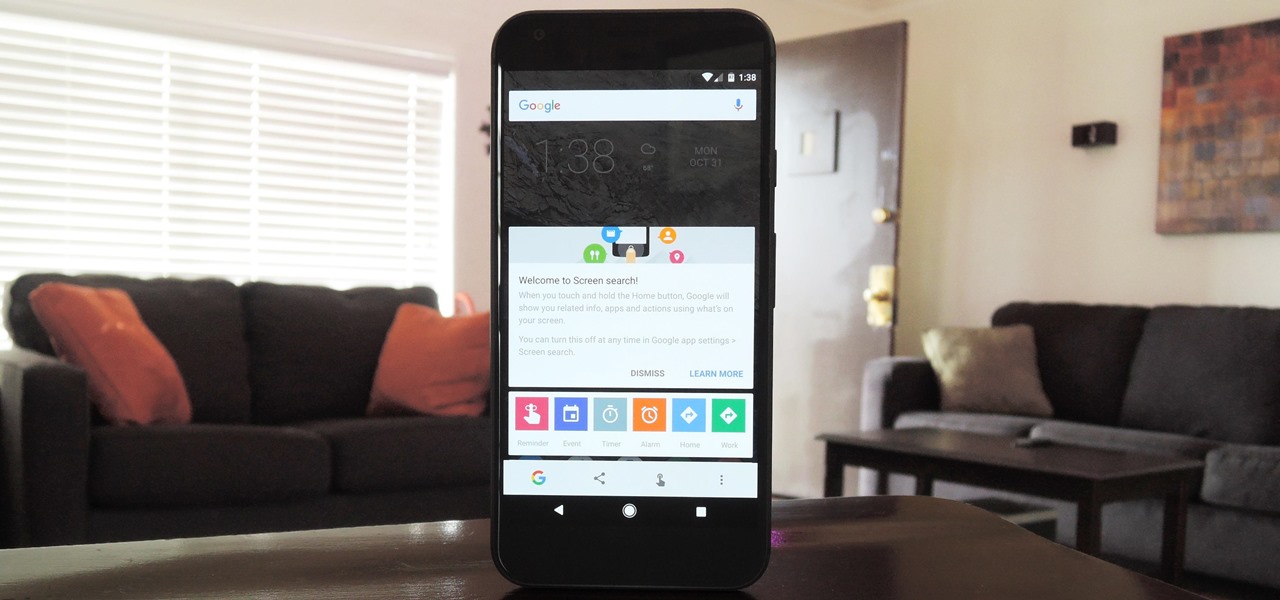
Now that Google Assistant is coming to all devices running Android Marshmallow or higher, roughly one out of every three Android users will no longer be able to access the old Google Now interface. The Assistant, which was previously exclusive to Pixel devices, takes over your home button long-press gesture and completely replaces all of the old Google voice search functionality.

Avocados have been the darling of the food world for quite some time now—so you'd think that we might have already exhausted the ways in which to enjoy this amazing fruit.
Most of you lot would be aware what WPA/WPA2 is so I won't bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit encrypted with a maximum of 64 characters in the password. The encryption is really only 64bit but x 4 because of the way the authentication functions as a 4 way handshake.