Need help getting started on this week's WTFoto Challenge? Look no further! In this tutorial, I will teach you how to create simple chalk symbols and writing in Photoshop. So read through this post and try it out yourself—or I'll tell your cousin what you said when you were drunk that one time. Keep in mind that the steps are similar for other programs, such as GIMP.
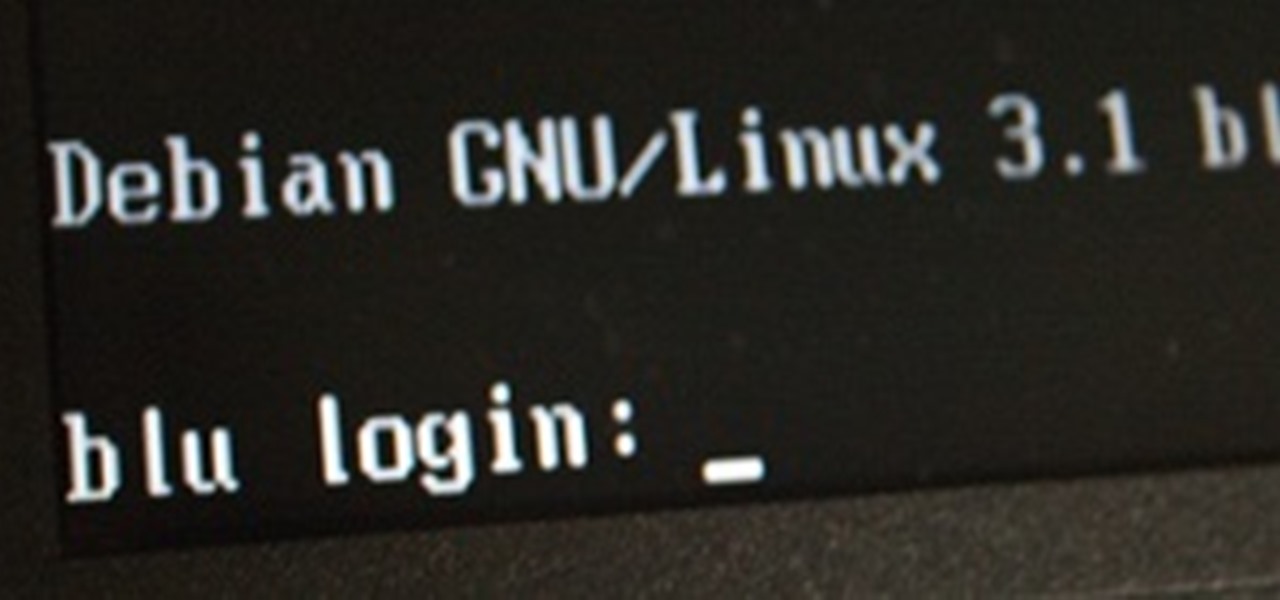
This morning, I received a message from a friend who was reading a hack log, and she had some questions about the commands used. This got me thinking, as Linux has a ton of commands and some can be archaic, yet useful. We are going to go over everything you need to know to read a hack log and hopefully implant the steps in your head for future use.

Do you need to email your wife your Social Security number? Send confidential business plans to your partner in Thailand? Send your hacker buddies the recovered hashes from last night's breach? Try using GPG, a valuable and easy to use open-source encryption program.

We're officially seeking Null Byters on a weekly basis who are willing to take the time to educate the community. Contributors will write tutorials, which will be featured on the Null Byte blog, as well as the front page of WonderHowTo (IF up to par, of course). There is no need to be intimidated if you fear you lack the writing skills. I will edit your drafts if necessary and get them looking top-notch! You can write tutorials on any skill level, and about anything you feel like sharing that...

Last Friday's mission was to accomplish solving HackThisSite, realistic 1. This is the first in a series of realistic simulation missions designed to be exactly like situations you may encounter in the real world. This first mission, we are asked to help a friend manipulate the website voting system for a Battle of the Bands vote count in his favor.

For this particular example, I will be working on Wndows (sorry X users). I might write a similar guide once I am more comfortable with programming in Linux.

Hello, welcome to my first post! Today, I would like to talk about setting up a Page File Encryption in Windows 7 and Vista. But first - what is a Page File Encryption? Why should you enable this option?

This week, in addition to the double exposure weekly challenge, we have a promotion specifically for iPhone users. The International iPhoneography Exhibition has asked for Phone Snap's best iPhone shots to enter for a chance to win a spot in the exhibition which will be taking place on December 16-22 at The Soho Gallery for Digital Art in New York City.

File Transfer Protocol, or FTP, is a network protocol made for transferring files in a client and host fashion over a Transmission Control Protocol (TCP) network, such as the internet. FTP is integrated into most browsers, and you have probably used it before. It is a common way to host files and transfer them easily. To access an FTP, a login is required, unless the server is configured to use anonymous logins (like the Arch Linux mirrors).

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Well this is it folks, the final Pre-Release before Minecraft officially launches! These changes should be the final game changes until it releases in Vegas this Friday. Mojang has made it clear, however, that they will continue making changes to the game while it's released.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. Minecraft Pre-Release 1.9 Version 6 is out! This update includes more bug fixes from Version 5 and Ender Dragons! We'll be reporting more changes as we find them, so stay tuned.

Welcome to part three in a series about steganography, the art of hiding things in plain sight. We are practicing steganography because it can be a useful skill if you don't have access to encryption software, or need a quick solution to make sure the sender and recipient are the only ones who are able to read your message.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. We're back again for another Pre-release!

Update 2: 1.9 Version3 is currently out. Click here to download and install 1.9 Version 3. Update: 1.8 is now officially out! It'll prompt you to update the next time you launch.

Since our Canon 5D World is just starting out, there's not a lot of activity in the forum. If you have a question about your 5D or 5D Mark II, then ask away. But there are other communities on the Web that already have great information from its members. Hopefully, the Canon 5D World forum will be just as helpful to everyone, but for now, here are some of the best forums on the Internet that can help you with Canon's EOS 5D and 5D Mark II cameras.

Today's segment of Making Art on Your iOS Device takes us into the third dimension. The below apps are suitable for beginners looking to venture into the world of 3d modeling, as well as pros who simply want the basics of Maya in their pocket.

There's a lot of talk going around about Google's new social network and how it's heavily influenced by Facebook, but truth be told, how could they build Google+ without taking a note

Dropbox continues to make headlines with their recent programming blunder which left the accounts of its 25 million customers wide open during a four-hour time span. During the duration, anyone in the world could access any Dropbox profile by typing in any password. And seeing as this wasn't the first security failure, everyone, including the most loyal users are considering dropping the Dropbox.
AMD vs. Intel processors - How to pick your ideal PC. Okay figuring out what computer you want is one step, but figuring it out what it's used for could save you money and achieve you much better performance. Every dollar saved could be used for something else in that computer to make it last longer, stronger, faster and better in general.

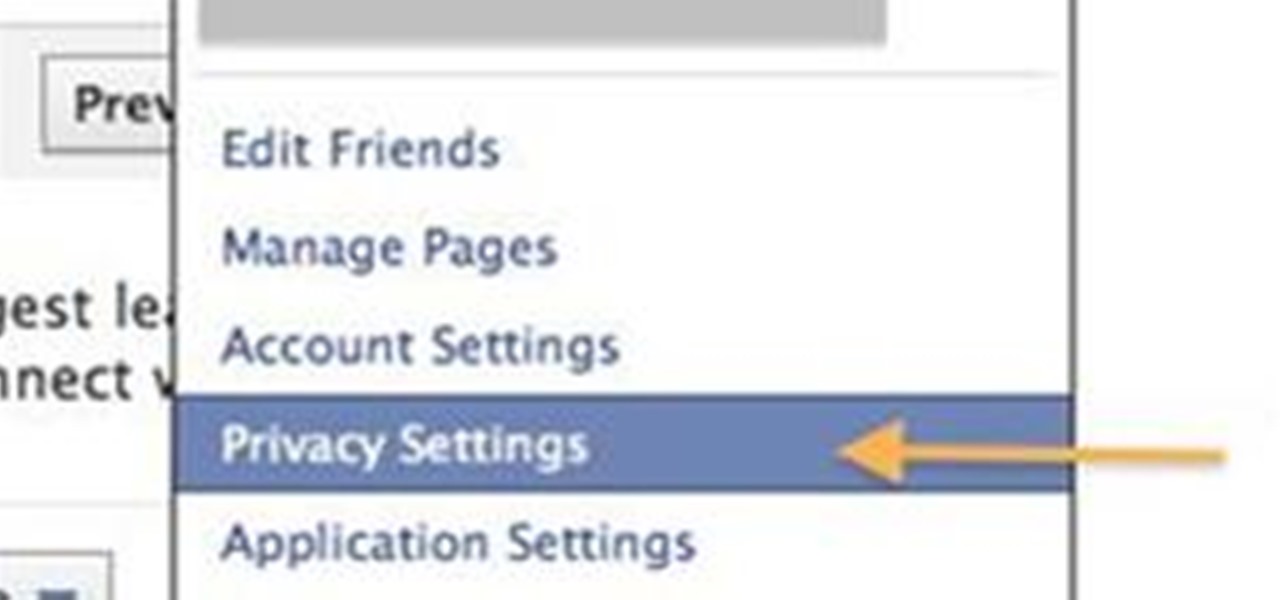
You could read through Facebooks Privacy Guide, but I found it a little confusing and a lot of people have been asking me for specific settings. SO here are some screenshots of the privacy settings so you can find where everything is located really easily!
HOW TO CAPTURE STREAMING MEDIA many websites stream songs and videos

Meet Aperture 3.1.1, Apple's powerful photo post-production tool with the Amazing Shrinking Price Tag. First released in 2005 for $500, Aperture is now available in the Mac App Store for a measly $79.99—a price reduction of 83.67%! That means a lot of new buyers and, as a result, a lot of new users.

Read this great how-to article on generating a fantasy world in Adobe Photoshop. Constantin Potorac leads you through, step-by-step, as you follow along and create a fantastic scene, beginning with basic stock images. Combine stock images of a background, tree, and model. Transform the background into a magical wonderland, add atmosphere with cloud effects, and birds to give it life. Edit the image of the model to blend in with the background - add some elegance to her dress and hair, with fa...

In this Adobe Acrobat video tutorial you will learn how to touch up text in a PDF file. This video shows you how to open a PDF file, and edit the page title, as well as change fonts and font colors. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Touch up text in Adobe Acrobat.

At first, the Black Ops 1.04 patch seemed like a godsend. It was supposed to fix the horde of issues plaguing Call of Duty: Black Ops on the PlayStation 3.

Recently, buyout talks between Google and Groupon ended with Groupon turning down Google's $6 million offer. But with Amazon backing LivingSocial, should they have? Your guess is as good as mine, but one thing's for sure— Groupon has a great voice, and they're sharing it with the world via their Public Groupon Editorial Manual.

Help your non-active friends remove the FarmVille application. We all have friends who have installed Farmville at one time or another and then end up quitting the game. But since they might be real life friends, we do not want to delete them from our friend list. Here are some directions to remove the application.

(a jeff dahlin came to wonderhowto offices... hand delivered 26 written prank ideas.... and a motorized File cabinet from hell.)

The importance of the brow has not been forgotten as much as it has been overlooked. A natural tool of communication, the brows can convey surprise, disdain, and sorrow with a lift, a furrow, or an expressive softness. The masters of makeup, like Max Factor and Ben Nye, knew the importance of perfectly styled brows, and how that would affect the work of the actors with whom they worked.

This is a 3 part tutorial. Be sure to click on Chapters 2 & 3 to get the full tutorial. In Part 1 of this 3 part Adobe Illustrator tutorial series, Vincent Rosati explains how to use the free transform tool to take the first step in creating a helix with AI.

You never know when you may need to sharpen an axe... and who better to learn from than the Boy Scouts? Brace the axe head on the ground between a log about 6" in diameter and two woooden pegs or tent stakes. Sharpen your axe with an 8-10 inch mill bastard file. Be sure to wear leather gloves. Make a knuckle guard out of leather, plywood, or an old inner tube. Place the file on the edge of the blade and push it into the bit. Lift the file as you draw back for each stroke. Turn the axe around ...

Hello! Today, I will show you how to add captions to your YouTube videos. Captions help people understand when the video itself does not entirely explain your tutorial.

When Windows stores a password, it is done so by hashing the password in an LM hash and putting it in the Windows SAM file. In the scary moment that you lose your password, but don't want to pay some geek to have full root access to your computer, you need to recover it using Ophcrack. Ophcrack doesn't remove the password, or bypass it, it cracks the password hash using rainbow tables.

This is the first of a multi-part series on steganography techniques. Steganography, the art of hiding things in plain sight, has existed for a long time, and in many forms. When you manipulate the alphabet to have your own cipher and decipher, this is considered steganography.

This Null Byte is a doozey.

INTRODUCTION In this Digital world now almost every one knows the a, b , c of computer. From a child of 5th grade to an old man, everyone knows how to operate computer and do simple work on it. Thats why you need to have something which makes you different from others.
The best thing about Google eBooks, besides its 3 million titles? You can read the books on any device - from your iPhone to your Sony Reader. It doesn't currently support Amazon Kindle files, but you can download the books you buy as PDFs or ePub files and then convert them on your Kindle.

PDF's are handy ways to send and receive documents so that you never lose formatting. But, did you know that you can view these files in places other than your computer or smartphone? In this tutorial, learn how to check out PDF documents using your PlayStation Portable! Your PSP is like a mini computer in your hand and can do a lot more than support video games.

Another continuation of my file carving video and selective file shredding (DOD 5220.22-M) to thwart forensics tools video, this video shows how to use Darik's Boot and Nuke (DBAN) to totally wipe a drive. DBAN is a great tool to add to your anti-forensics tool box. Use Darik's Boot and Nuke (DBAN) to wipe a hard drive.