It seems like every day now that we see a new headline on a cyber security breach. These headlines usually involve millions of records being stolen from some large financial institution or retailer. What doesn't reach the headlines are the many individual breaches that happen millions of times a day, all over the world.

Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.

Welcome back, my tenderfoot hackers! As you know, DNS, or Domain Name System, is critical to the operation of the Internet. It provides us with the ability to type in domain names such as www.wonderhowto.com rather than the IP address. This simple service saves us from having to memorize thousands of our favorite website IP addresses. Instead, we simply type in a domain name to retrieve the website.

You're in the middle of cooking and a car alarm, cute kitten, or neighborhood brawl made you step away from the stove for a few minutes longer that you should have. It happens to almost every home cook. Most of the time, nothing dramatic happens, but every now and then, you end up with something like this:

Security is a priority for many when they first set up their mobile devices. Nobody wants to have a stranger or nosey friend go through their phone and discover risqué photos or embarrassing text messages. These days, the closet is gone—everyone keeps their skeletons in their phones.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.

Just what are probiotics and why are they so good for you? Probiotics are "viable microorganisms" that can confer lots and lots of health benefits if they reach your intestine while they're alive. You may have heard them described as "friendly bacteria."

Journals are a great source of hilarity and embarrassment, detailing everything from your elementary school crushes to those super awkward middle school dances. While rereading your old hand-scrawled entries might make you cringe, that old journaling habit could benefit you as an adult.

Fasting—or the practice of regularly abstaining from ingesting anything except water—is a pretty drastic move. I tried to fast for two days and made it to the 12-hour mark, which is when I broke down and ate a quart of ice cream.

This year's I/O was all about bringing Android into the future and onto new devices. On top of announcing the upcoming "L" release of its mobile OS, Google showcased Android Wear, Android Auto, and Android TV.

Many of the beauty products you buy at drug and department stores are loaded with potentially toxic ingredients like parabens, while their active ingredients are made of things like glycolic, lactic, malic, and alpha hydroxy acids and retinoids, which are all derived from foods.

It took many months of cries from all around the internet—and a particularly large groan from an ex-Lifehacker editor-in-chief—but Apple has not only acknowledged the existence of its iMessage problem, it's promising a fix.

Are you searching for a homemade cat repellent solution? This article will cover natural indoor and outdoor deterrents for every scenario where cats are causing trouble. The first part will cover home remedies for training cats to stay away from furniture and other restricted areas inside your house. The second part will cover outdoor repellents for keeping cats away from your garden, plants and yard. Step 1: Indoor Repellents for Training Cats

Spiders are common pests that typically prefer to live outdoors. However, insects and warmth will eventually attract them into our houses. They like to spin their webs in corners, crevices and unused areas of your house. Most species are harmless and even act as a natural repellent for getting rid of other insects. However, in some cases, spiders can be very dangerous. Whichever the case may be, they are scary and people are always looking for natural ways to get rid of them.

Fresh salsa is so tasty. Who can resist the robust mix of spices, the mouth-watering heat of jalapeños, and the juiciness of fresh tomatoes? Alas, I don't always make my own and have to get the pre-made stuff.

Welcome back, my greenhorn hackers! In my continuing effort to demonstrate to you how to hack the ubiquitous Windows 7, we will going after that notoriously vulnerable Adobe Flash that is on nearly every client Windows system (you are not likely to find it on servers).

Welcome back, my novice hackers! I have tried to emphasize throughout this "Hack Like a Pro" series that good reconnaissance is critical to effective hacking. As you have seen in many of these hacks, the techniques that we use are VERY specific to the:

Welcome back, my novice hackers! We've done a number of tutorials using one of my favorite hacking tools, Metasploit. In each of them, we've used the msfconsole, which can be reached through either the menu system or through simply typing "msfconsole" from the terminal.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.

The @DesignGears guys have been busy today, leaking an unofficial KitKat build (Android version 4.4.2) for the AT&T Samsung Galaxy Note 3. The latest is a peek into what the international variants are beginning to see, although this build is far from official. Still, if you want to give it a shot, I'll show you how to install it, but make sure to check out the details below the how-to to see what you can expect, good or bad.

Welcome back, my tenderfoot hackers! So many readers in the Null Byte community have been asking me questions about evading detection and hacking undetected that I decided to start a new series on digital forensics.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

2 + 2 = 4. That's about as much math as I can handle without a calculator on a daily basis. I literally hate doing math more than anything in life, mostly because I'm not good at it—and I hate doing things I'm not good at.

Wet shoes are uncomfortable, no one can deny that. Just think about walking around with soaking wet footwear ... and each squishy step you take. Makes you cringe, doesn't it? It can happen in heavy rain, at the beach, or from an unforeseen puddle on the street. And while you can't always avoid soggy shoes, you can rest easy knowing that the next time this happens to you, you know the secret trick to drying your shoes faster without damaging them with excessive heat.

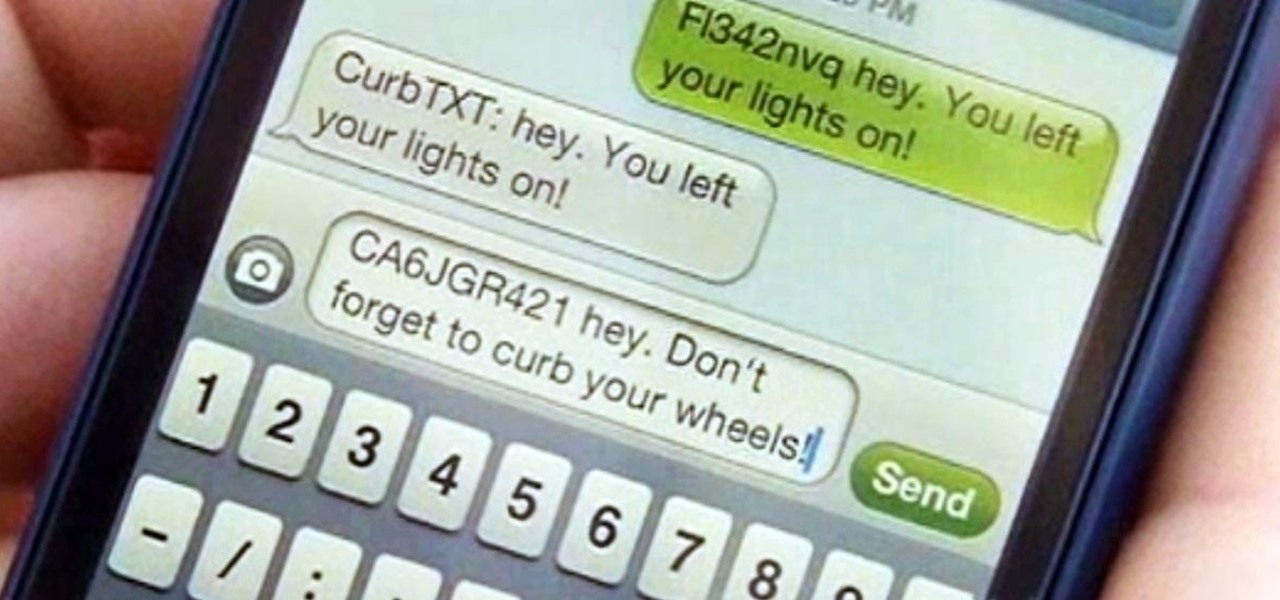
Parking. Ugh. Parking is about as fun as running through a swarm of bees while being chased by a pack of wolves from The Grey.

All kinds of people pretend to be someone they're not on the internet, including scammers, people attempting to wind others up, hackers and web predators. Almost all of these people will leave bases uncovered and they're all easy to expose when you understand how to. Here are my favorite ways of finding out when somebody is lying quickly. Image Search

In order to convert a sweater into a sporty strapless dress you will need the following materials: a sweater, some white chalk (or something washable to make markings with), a scissors a table (or workspace of some sort), and a sewing machine. To start lay the shirt out flat on the table. Then make markings using the chalk in the style of a dress. (About 2-3 inches from the edges and fan out at the bottom.) Then measure the marks on your body and make sure they line up with your sides. After ...

Conflict is a part of life but how you deal with that conflict is up to you. You may find yourself in an argument and instead of making it a shouting match, employ some techniques that will be sure to keep this conversation civil.

The video describes how to replace the fill valve, the rubber flapper, and an older plastic water fill line with a stainless steel one so that the toilet will no longer leak. Purchase a fill valve kit at your local hardware store before beginning. Start by turning water compression valve off, and then flushing the toilet to remove the water. Next, remove the fill valve by loosening the bottom, then top nut with a pair of pliers. Remove the plastic water fill line. Next, loosen the nut on the ...

This cute and colorful flower button is a perfect Spring craft project for the kids. Not only do you get rid of unwanted buttons but you can keep the kids busy and make a cheerful brooch all at the same time.

In the art of paper crafting, the fortune teller is one of the easiest one that anyone can do it. First you need a sheet of paper, some markers to write over it. Fold one of the corners on an angle to match the other side. Now with the excess paper here, cut along the line. Now open it up and you should have a square. Fold the other corner to the opposite corner and make your fold. Once you have made your creases, fold to the center. Now you should have a smaller square. Now once you've compl...

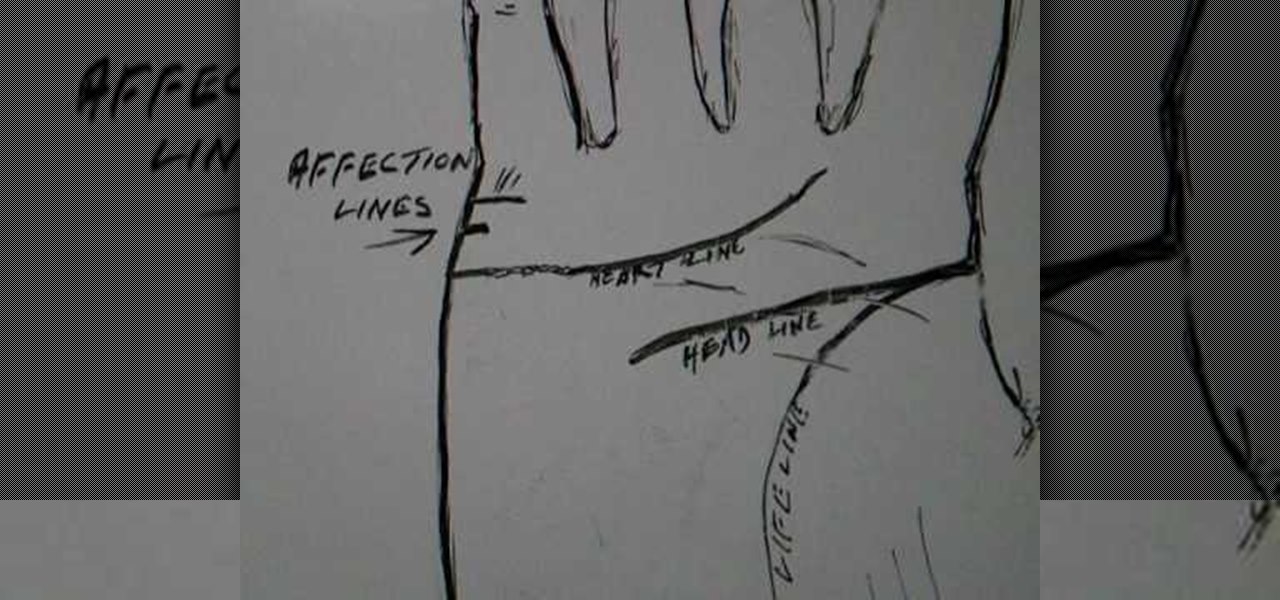
Read affection lines and the heart line in palmistry. The affection line sometimes two and some time just one. Looking at the affection line one by another person. Now looking for married not necessary a two affection line and heal the heart line finishes up. Some time settle for the head. Dividing the affection so feel change time to time. On the wide life feel about different people. Now looking for the heart line show early in beginning. We can show under the little finger. After early mar...

If you're serious about playing marbles, than you probably knew there are actually marbles tournaments around the world. If you want to know how to play marbles, the tournament way, then this video will help you understand the basic rules and regulations. This is for serious marble players.

This video slide show tutorial gives a step-by-step guide to scissoring a poodle topknot. 1. After clipping the face against the grain with a close blade, the line is first scissored from the outside corner of the eye to the top of the base of the ear.

In this video series, Gary Zier teaches the object and rules of Gin Rummy. Learn about match scoring, knocking, and deadwood. Gary also offers tips and strategies for the experienced or beginner gin player. So, grab a partner and start playing Gin Rummy today!

If you’re camping outdoors, you’ll probably need to know how to make a campfire at some point. Fire is an important tool to have for cooking food and purifying water, for warmth and light, and for protection from wild animals at night. In this video series, learn the proper way to make a safe, long-burning campfire. Our expert, Brian Rajchel, will show you how to choose the right area in your campsite for the fire, how to build a fire pit, how to start a fire without matches, and how to prope...

In this video series you're going to get started on making a fabulous tote bag with a matching make-up case.

The Holy Grail of chicken has just been found by an unsuspecting reporter of the Chicago Tribune. Yes, that's right: The secret 11 herbs and spices in Colonel Sanders' Original Recipe chicken has finally been revealed, and it looks legit as hell.

Giving a speech in front of a large crowd doesn't need to be the nightmare everyone imagines it to be. We speak to many people every day and yet it is still very common for a person to be nervous when delivering information in front of several people. This fear can be overcome by practicing how to give a speech and being prepared.

In these music lessons on video, learn how to play a funk groove on the piano. Get some tips for playing effective bass lines and using rhythm techniques like stab breaks, hangs, stops, and glissandos.