
How To: Save That Old, Opened Wine in Your Fridge by Making Homemade Vinegar
Don't Miss: Make Opened Wine Last Longer


Don't Miss: Make Opened Wine Last Longer

When it comes to a perfect summertime dessert, lemon meringue pie is the ideal contender with its rich lemon filling and light-as-air meringue topping. In my humble opinion, the meringue is the true star of the dessert, instantly elevating what is simply a lemon pie to something more elegant and certainly more decadent.
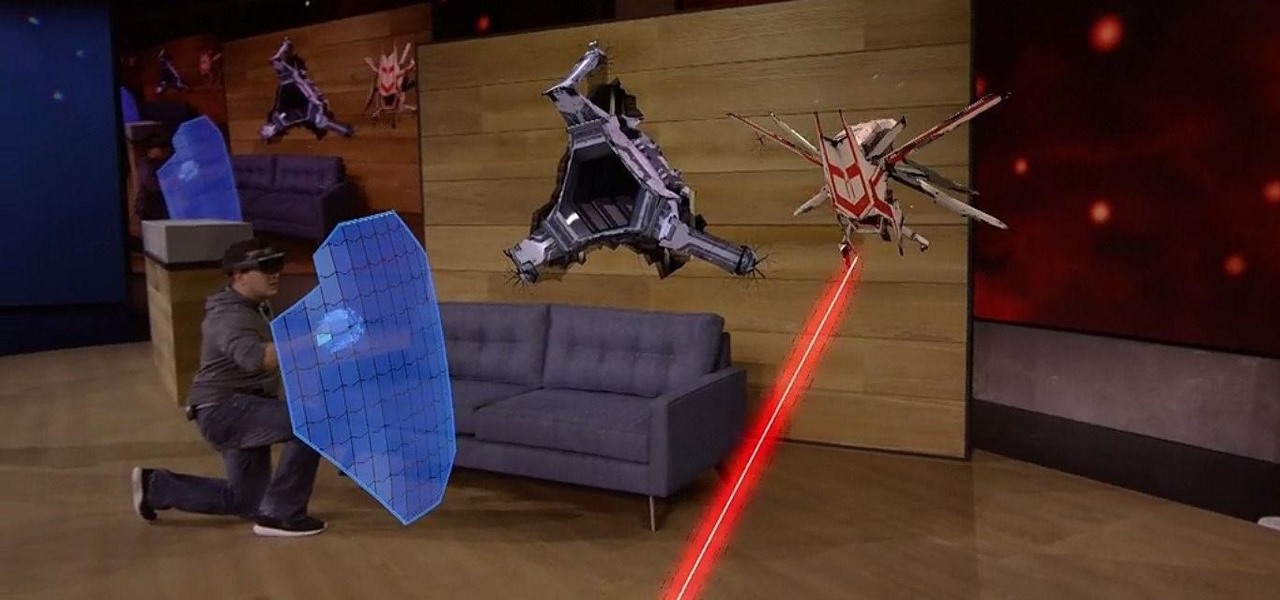
Microsoft's HoloLens has many applications in the business world, both large and small, but what about gaming? Initial demos gave the impression that we could expect amazing first person shooters, platformers, and even Minecraft. Yet, as Newsweek noticed, the HoloLens was nowhere to be found at E3 this year.

Most augmented/mixed reality hardware still exists in the development stage, whether that's one of the more robust headsets or a high-powered smartphone. Most everything else isn't widely used or monetized. Snapchat, however, snuck in under the radar and created the foundation for the first social network to focus on augmented reality.

When Hey Siri was first introduced in iOS 8, it was a pretty lackluster feature since you had to be plugged into a power source in order to even use it. Since then, newer devices (iPhone 6s, 6s Plus, SE, 9.7-inch iPad Pro) don't need to plug in to have always-on Siri, which makes the feature actually worthwhile—when it works.

Apple is planning to completely overhaul its Apple Music streaming service this summer, and is expected to unveil the changes at its Worldwide Developers Conference in June, according to reports from Bloomberg and 9to5Mac.

Welcome back, my novice hackers! As many of you know, recon is crucial to a successful hack/pentest. In most cases, hackers spend more time doing good reconnaissance than actually hacking. Without proper recon, you are simply guessing at what type of approach or exploit is going to work and, as a result, your time is wasted without any useful outcomes.

Logan's Run is one of my favorite movies of all time. The dialog is cheesy, the set design and special effects are wonky, and the main villain looks like he was conceived and built by an eighth grader in shop class—oh, and his name is Box.

Since its purchase by Microsoft in 2014, Minecraft has regularly been pushed to new platforms such as Windows 10, Wii U, and Fire TV. In that spirit, Microsoft-owned Mojang has been developing virtual- and augmented-reality versions of the blocky sandbox game.

Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

Sourdough is a delightful twist on your traditional bread, but creating and maintaining a sourdough starter can be a headache for many home bakers.

The Stagefright exploit, which allowed for malicious code to be embedded in files on your device, is now very real in the form of Metaphor. Developed by software research company NorthBit, Metaphor is their implementation of exploits to the Stagefright library, and when executed, can access and control data on your device.

Using a fingerprint scanner to keep intruders out of your phone might not be as secure as you think. Two researchers from Michigan State University, Kai Cao and Anil K. Jain, developed a relatively cheap and effective way to beat fingerprint readers, and successfully tested their method on a Samsung Galaxy S6 and Huawei Honor 7.

It seemed appropriate that we announce the winner of the first White Hat Award for Technical Excellence on the Academy Awards weekend. This is, in essence, our "Oscar" here at Null Byte. Remember, this contest began on January 4th, 2016 and just recently closed on February 15th. In this contest, I was looking for:

Hola my fellow hackers! I promised you the tutorials on setting up RAT's and Botnets, but before jumping into those, i want you to know about the precautionary measures and detection of RATs which might be on the system without your prior knowledge. Of course the Anti-virus do most of the job but there are some RATs which slips past the Anti-viruses (This is where Hacker's skill come into play).

Welcome back, my tenderfoot hackers! As most of you know, I am strong advocate for using Linux as a hacking platform. In fact, I would say that without knowing Linux, you will never become a professional hacker/pentester.

Hello fellows nullbyters, first of i will start saying that im addicted to this community, i feel the challenge growing up so fast, all the newbies, amateurs,advanced and professionals hackers around trying their best to help the community, badly but we got some script-kids too but anyway, today we are going to learn how to install and use clanAV in kali linux.. INTRODUCTION

Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.

With each day that dawns, there is a new, major hack that makes the news headlines. If you are paying attention, there are usually numerous hacks each day and far more that never make the news or are kept private by the victims. Every so often, a hack is so important that I feel compelled to comment on it here to help us learn something about the nature of hacking and IT security. This is one of those cases. Last week, the U.S. Office of Personnel Management (OPM) revealed that they had been ...

As many of you know, I firmly believe that hacking is THE skill of the future. Although the term "hacking" often conjures up the image of a pimple-faced script kiddie in their mother's basement transfixed by a computer screen, the modern image of the hacker in 2015 is that of a professional in a modern, well-lit office, hacking and attempting to development exploits for national security purposes. As the world becomes more and more digitally-dependent and controlled, those that can find their...
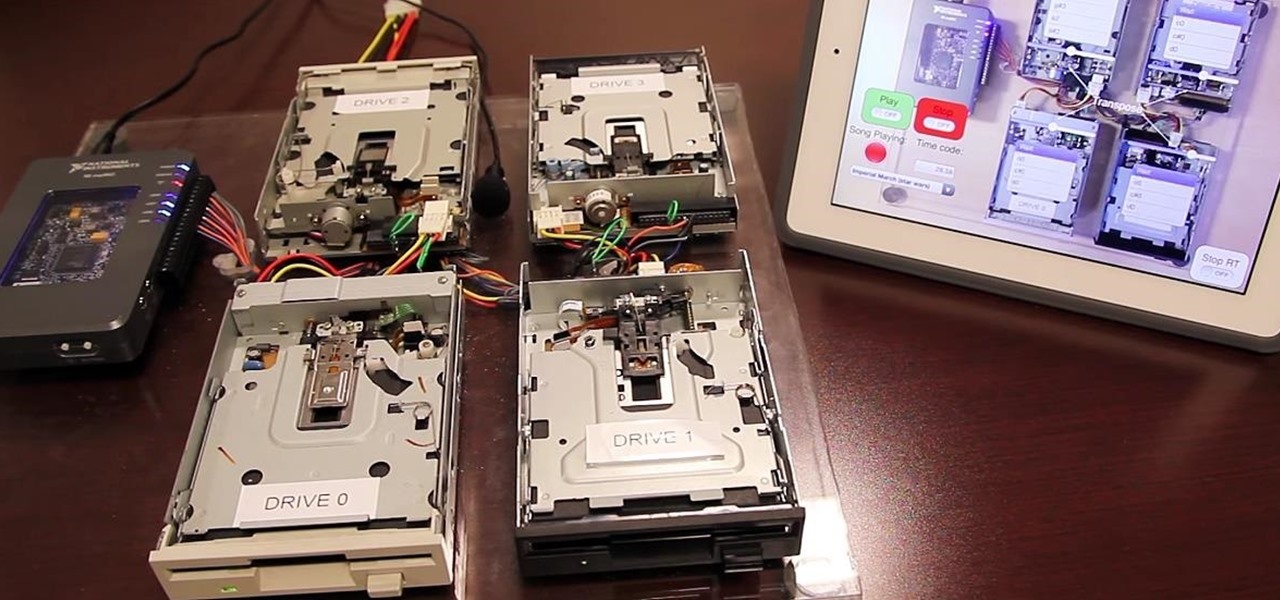
Video: . Project Overview

We use our smart devices for pretty much everything these days, from getting directions to playing games just to kill time. They're extremely important to our daily routine, and as we use our devices more and more, things get a little bit messy.

Among the many gifts that Italy has bestowed upon the world, culinary and otherwise, pesto stands alone. The exact birthplace of pesto, that herby sauce made of pine nuts and olive oil, is an area of Italy called Liguria, whose microclimate is particularly kind to basil, one of pesto's key ingredients.

One of the most rewarding things about jailbreaking is theming. Unlike Android, iOS doesn't allow you to make small changes to certain aspects like the icons or the lock screen, so jailbreaking facilitates the ability to make some of these desired changes happen.

Finding the right mix of custom ROM, kernel, and tweaks for my OnePlus One has left me flashing every new release I come across. This has led to many hours going through thread after thread trying to find the latest and best software out there for my phone. While I do enjoy the hunt, I would rather have a centralized location that covers all my bases, so that's why I have started using OnePlus One, an app by Alex Inthiaano.

Did you know that your face shows others how much alcohol you drink? Whether you've never had a sip of booze with those around you or you're known as the party animal of the group, the genes that shape your appearance also show others just how much you enjoy liquor. Pinpointing the big drinker in any setting is easy to determine: you just need to make eye contact.
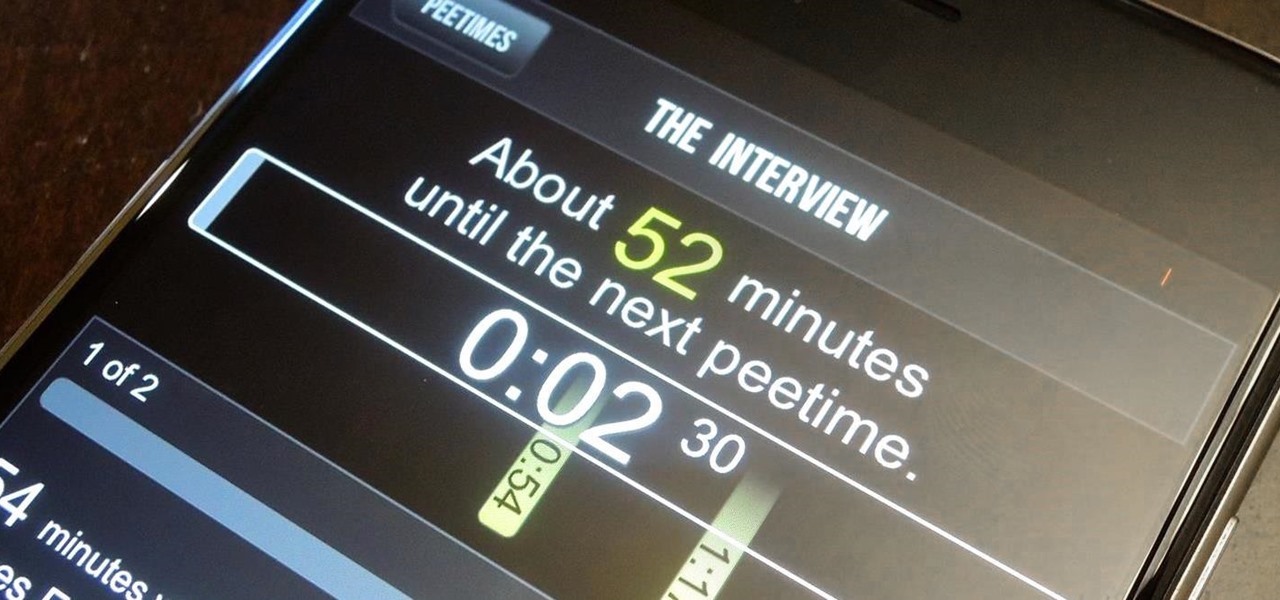
When I watched the first Cincinnati Bengals edition of the HBO series Hard Knocks back in 2009, among wide receiver Chad Johnson's bravado and attention-grabbing antics was a segment on backup quarterback Jordan Palmer and his newly-developed app, which was still in its infancy. Six years later, I've revisited his creation and have to admit—it's pretty damn useful.

Welcome back, my hacker novitiates! As you know by now, the Metasploit Framework is one of my favorite hacking tools. It is capable of embedding code into a remote system and controlling it, scanning systems for recon, and fuzzing systems to find buffer overflows. Plus, all of this can be integrated into Rapid7's excellent vulnerability scanner Nexpose.
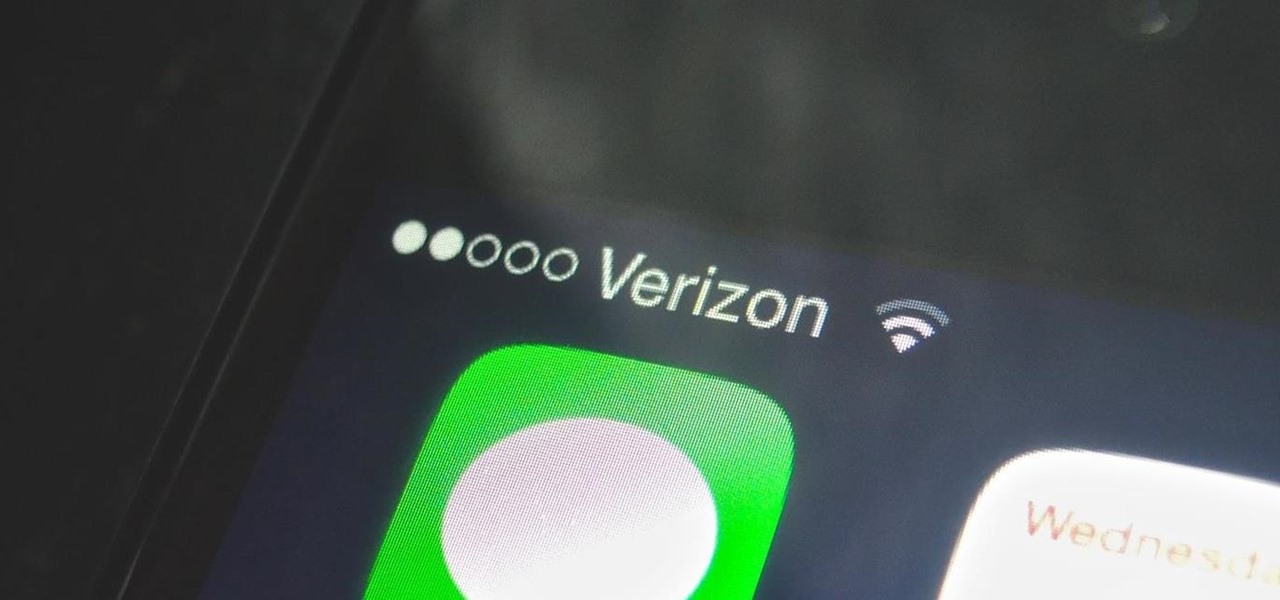
You can find hundreds, if not thousands, of complaints about Wi-Fi performance issues with iOS 8 across all Apple devices. Even I had the issue on my iPhone 5S. The Wi-Fi connection on my router was strong, but I was getting extremely slow speeds. So slow, that I would resort to using LTE instead of Wi-Fi, which in turn led to going over my monthly data allotment.

Welcome back, my novice hackers! In my series on cracking passwords, I began by showing off some basic password-cracking principles; developed an efficient password-cracking strategy; demonstrated how to use Hashcat, one of the most powerful password-cracking programs; and showed how to create a custom wordlist using Crunch. In this tutorial, I will show you how to create a custom wordlist based upon the industry or business of the targets using CeWL.

Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way for computers to communicate over the LAN by just using computer names rather than MAC or IP addresses.

As messaging and texting have all but replaced the need to actually call someone, emojis have seemingly replaced our need to type out text. With a simple emoji, you can relay emotions like "I don't feel very well" or "I love you" quickly and easily, knowing that the other party will instantly know what you're feeling.

Welcome back, my novice hackers! Before we try to attack a website, it's worthwhile understanding the structure, directories, and files that the website uses. In this way, we can begin to map an attack strategy that will be most effective.
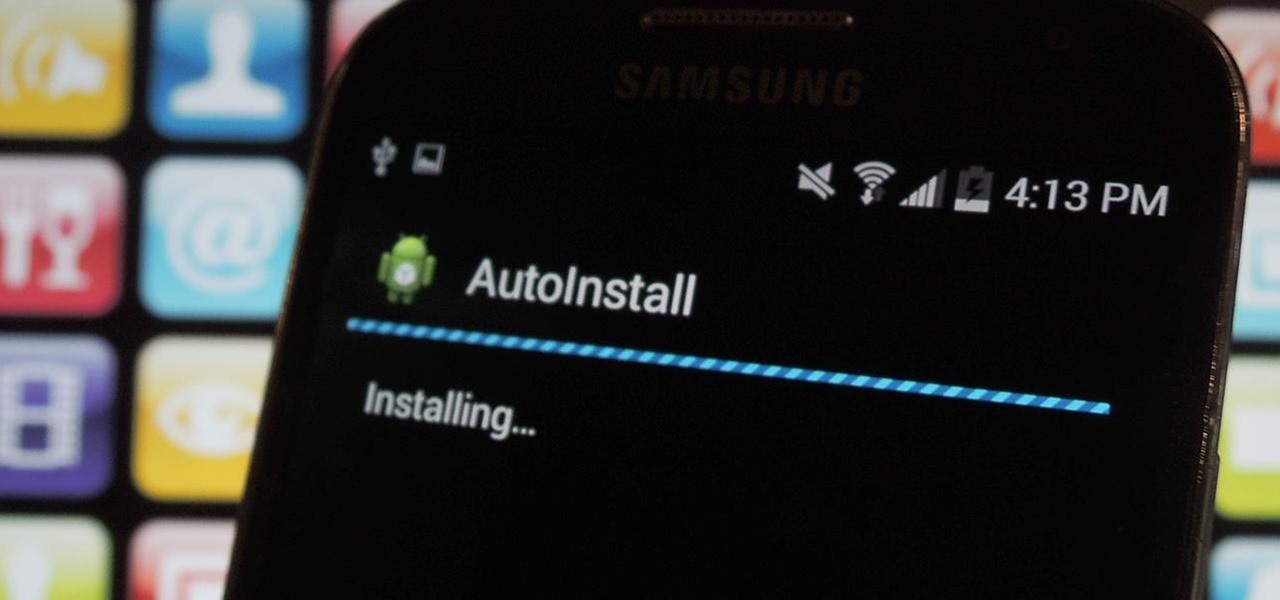
I'm always looking for the best apps and services for my Android, and that means sticking strictly to the Google Play Store is a no-go. If you're like me and tend to install a lot of APKs (application files), you're probably tired of seeing the "Install" confirmation that always pops up.
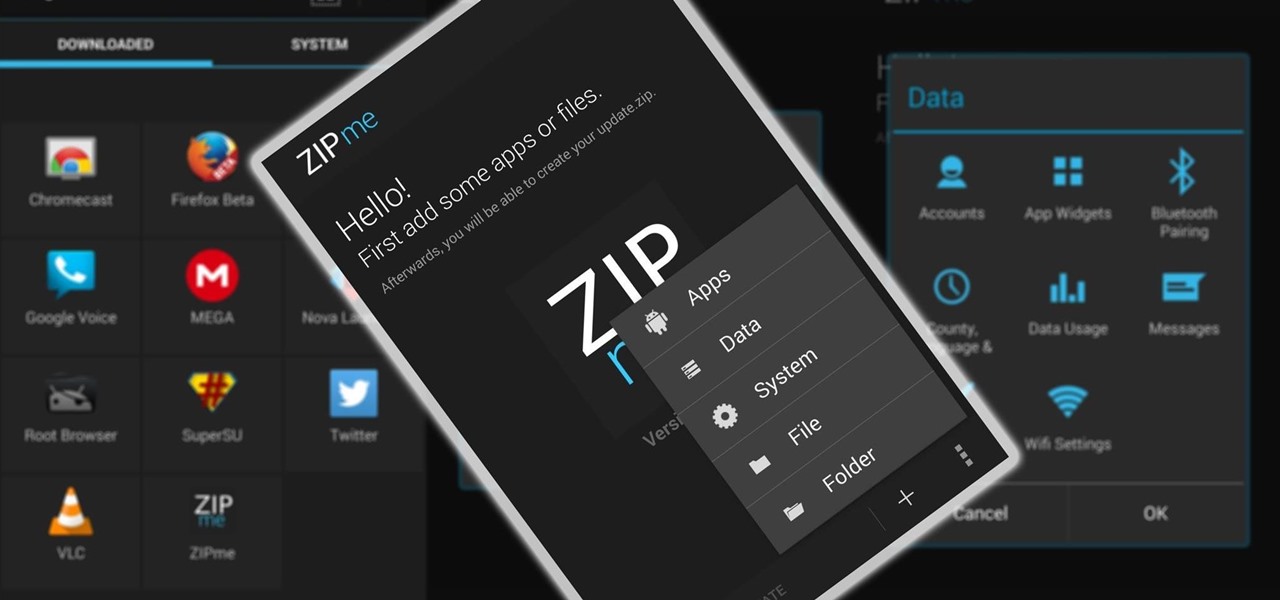
Restoring data is not always the easiest thing to do when you flash a new ROM on Android. Google can back up your contacts and Wi-Fi passwords, and various tools can back up your apps and data, but the rest is usually lost in-between ROM flashes. This leads to a lot of wasted time getting everything back into place, and it'll take a long time before your new ROM feels like "home" again.

Earlier this month, John Oliver spent a segment on Last Week Tonight explaining native advertising, a practice followed by many online media outlets such as BuzzFeed, The New York Times, and VICE, which combines editorial content along with sponsored advertisements.

Researchers at the University of California, Riverside and the University of Michigan announced recently that they have developed a hack that works 92% of the time on Google's Gmail system on Android, as well as with the H&R Block app.

Just when you begin to doubt the future of humanity, advances in ice cream scooping science continue to develop. Yumi showed you some super-cool ice cream hacks just in time for summer, and we've already discussed how to use a knife to slice ice cream when it's too hard to scoop.

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.