All of my hacks up to this point have been operating system hacks. In other words, we have exploited a vulnerability usually in an operating system service (SMB, RPC, etc.) that all allow us to install a command shell or other code in the target system.

Pasta is really easy to make but sometimes you just don't have the time to wait for the water to boil, or to clean up the mess. This three part tutorial is here to help! This video series will show you exactly how to cook noodles in the microwave to save time and energy.

Chi running focuses on core muscles, integrating body and mind, and long-term performance to enhance the joy of running. In this tutorial, you will learn how to harness your Chi and improve your running technique and overall fitness.

This fitness how to video demonstrates beginners level cobra poses. Standing poses along with cobra poses are great for opening the muscles in the lower body. Boost your energy level in the morning with a sun salutation that incorporates the cobra pose.

In this series of how-to videos, home improvement expert Amelia Tallman shows you step-by-step instructions on how to install a new power outlet in a wall of your home. She demonstrates how to strip the existing wires, drill holes and properly install a new box for a new outlet. She also shares tips for improving your home by installing insulation using a blower, which should help you save money on energy costs by maintain temperature. By following the advice and techniques shown in these fre...

Armis Labs has revealed eight vulnerabilities, called "BlueBorne", which put 5.3 billion Android, iOS, Windows, and Linux devices that use Bluetooth at risk. With it, hackers can control devices, access data, and spread malware to other vulnerable devices through networks. In this post, we will learn about the vulnerabilities, then look at how to find devices that have them.

When temperatures drop and hit new lows during the cold, winter months, it's hard not to crank the heat up. That means increased energy bills each month, no matter if you rely on gas, electric, or another fuel for heating.

Katarina is one of the champions you can use in League of Legends, being able to both deal out damage and handle taking it herself. Here's a quick overview of what she can do, and the best way to incorporate this champion into a team game on the Fields of Justice.

Malzahar's strength is being able to damage over time. With his silence ability, he is also good at harassing the other team. Here's a video which explains what Malzahar can do as a champion, and then a demonstration of him in action on the Fields of Justice.

Laning is one of the more important phases during a battle on the Fields of Justice. This tutorial shows you the best way to use Nasus when you're trying to take or hold your lane. Make sure you choose the right abilities and items to make Nasus more than able to hold his own during your next game.

It can sometimes be difficult to win a solo queue game in League of Legends when paired with players you don't know. Here are a few tips and hints when you pick your champion in a way to compliment what your teammates are playing.

Dr. Aris Latham suggests setting standard plans for breaking a fast for most of people that he interacts with because the animal body has been programmed to eat in a certain way. This is necessary to train your body well so as to survive and be healthy. Divide your day into 3 equal parts of 8 hours. Take the sleep part of the day where you deal with the waste in your body and create energy within the body. The next period when you get up is basically when you break your fast when your were sl...

Jerky is not only delicious but it is a great way to bring a protein rich energy snack with you anywhere. This video will how you how to make a great beef jerky at home. You will want a think slice of meat and you can create your own fantastic flavoring.

Eeverst isn’t for armatures. If you have the ambition of climbing Mt. Everest you will have to do a lot of preparations including physical fitness work, travel arrangements, not to mention putting aside thousands of dollars to make your dream a reality.

Keep the kids learning and entertained with this fun pinwheel project. Summer is a great time for family activities, and these Fourth of July pinwheels are a math lesson, craft project and decoration-making session all-in-one.

In this video series, our expert will give you an overview of these and other remedies and tell you how to use them in order to harmonize the cosmic energy in your life to achieve happiness and prosperity.

Master Rafael Negron, 6th DAN Master Instructor, and Jessica Sherlock, 2nd Degree blackbelt. Hapkido is an eclectic Korean martial art that is literally translated as “the way of coordinating energy” or “the way of coordinated power.” Hapkido is ultimately used as self-defense and combines other skilled martial arts with common attacks. he main focus of Hapkido is footwork and body positioning used to employ leverage.

If you're concerned about your data ending up where you don't want it online, then a VPN is something you'll want to consider. A VPN can prevent your bank account information from leaking, your data from being taken directly from your device, and it doesn't come at the cost of any of the convenience we've grown to expect and require from the internet.

If you've been working from home a bit more often than usual lately, you're far from alone. Despite some optimistic predictions that things would have returned to normal right now, social distancing guidelines have forced most offices to shut their doors, and it's looking like this is going to be the new normal for the foreseeable future.

MATLAB, an acronym for "matrix laboratory," was created over 40 years ago to service the applied mathematics community. The powerful programming language now has over four million users worldwide and is of particular import to engineers, scientists, and economists.

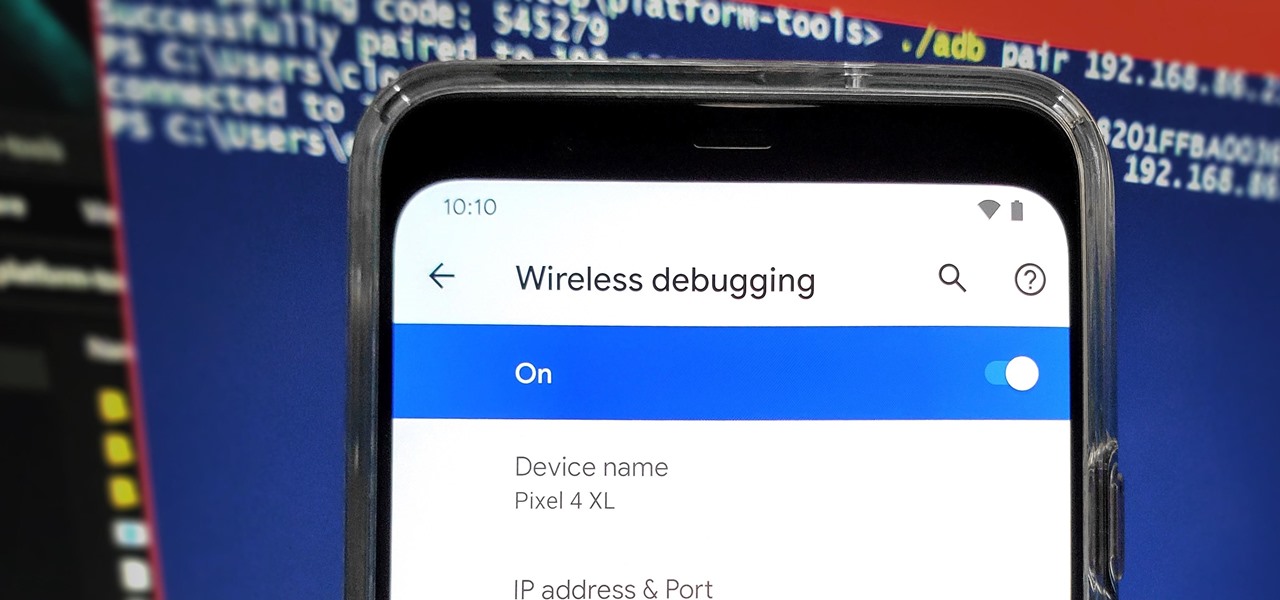
From booting into Fastboot mode with a single command to installing mods without root access, there's no shortage of reasons to use ADB. The catch, though, you had to be tied to a computer with a USB connection. However, a new feature in Android 11 finally allows you to run ADB commands over Wi-Fi instead of being tethered.

If you've tossed around the idea of turning your interest in white hat hacking into a career in cybersecurity or IT, now's as good as time as ever to invest some time and energy into improving your skill set.

Your smartphone is likely full of COVID-19 news and coronavirus panic. These are scary days, and there doesn't seem to be any end in sight. If you're having trouble coping with the stress and anxiety the virus brings with it, know that your iPhone or Android device can actually help you, rather than just bring you further down.

Mobile gaming has exploded, with roughly $70 billion in revenue in 2019. This gave rise to the so-called gaming phone, headlined by names like Razer and ASUS. While the Galaxy S20, S20+, and S20 Ultra are being marketed as everyman devices, make no mistake — these are unstoppable mobile gaming machines.

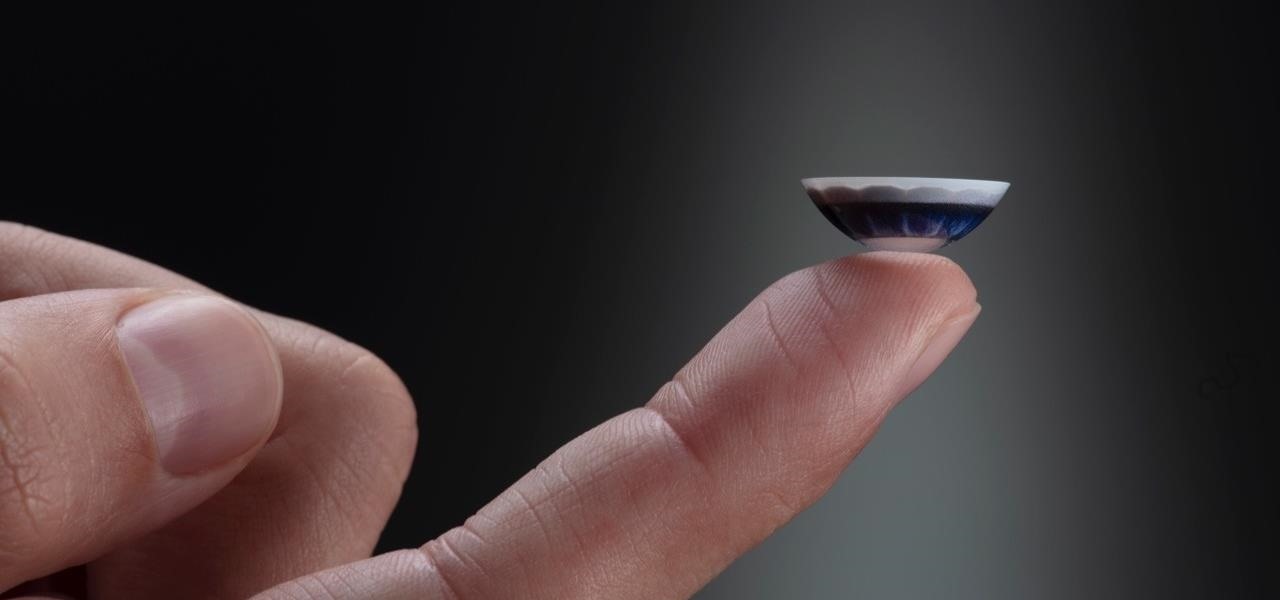
After more than two years of teasing, augmented reality startup Mojo Vision has confirmed that "invisible computing" means what we've suspected all along.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

The Pixel 4 isn't for everyone, but it does have its appeal in several specific use cases. Thanks to Instagram, YouTube, and other social media platforms, the fitness industry and smartphone world are now intertwined like never before, and it appears Google's aware of this.

It's new phone season — new handsets are releasing every few weeks, we're seeing endless software updates, and the holidays are right around the corner.

With its 3D engine being responsible for approximately 60% of augmented and virtual reality experiences, Unity is continuing to place a premium on tools that not only keep developers working in its development environment but also make their workflows easier.

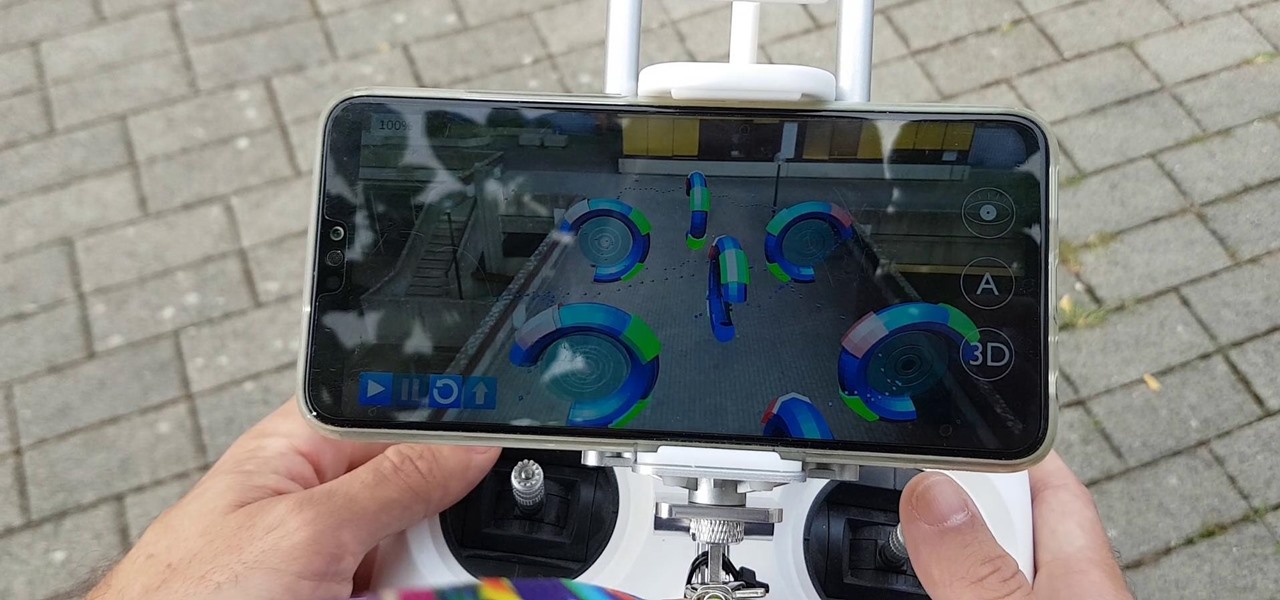
Drone mishaps, such as the collision that scratched a military helicopter in New York, are becoming something of an everyday hazard.

Apple's latest updates to its operating systems add another security feature to its Find My service, so you have an even better chance at locating your lost iPhone, iPad, or Mac should it ever happen. As long as you have the option enabled, you can leverage other Apple users' devices to find yours on the map.

Your writing is just that — yours — so the work you do in Apple Pages should remain private until you choose to share it. Apple seems to share this sentiment. As another symbol of its dedication to user privacy and security, the company includes a feature in its word-processing app for iOS that allows you to lock documents behind a password, as well as with Face ID or Touch ID.

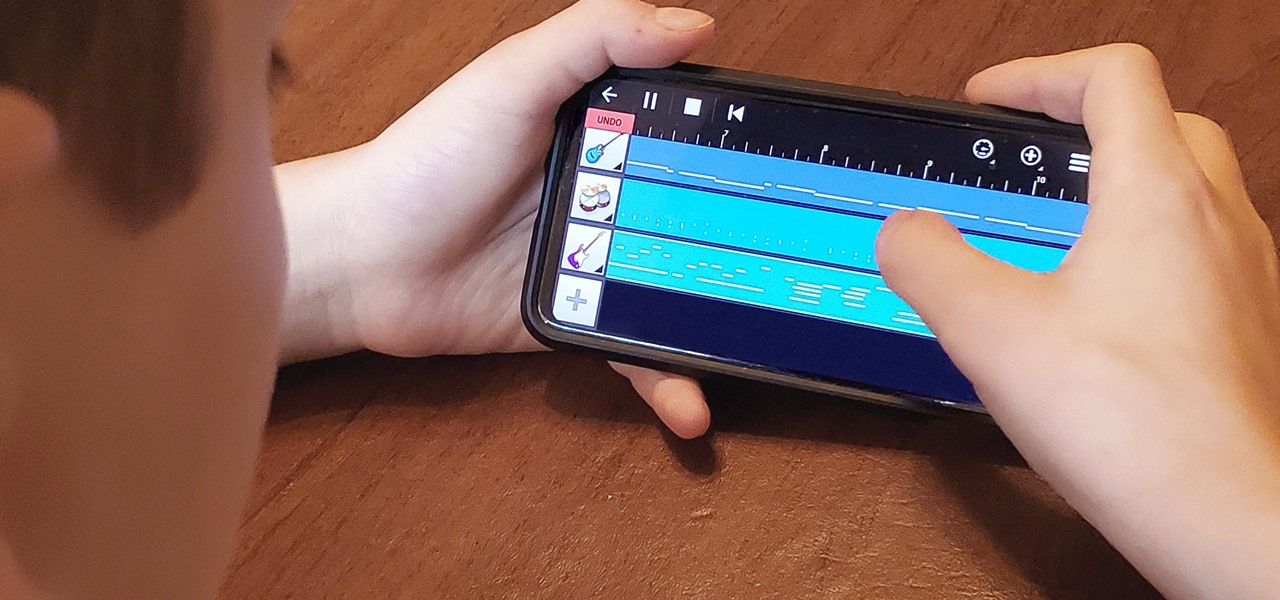
My autistic son loves music. One afternoon, when he was nine, I downloaded GarageBand to his iPhone to help with the boredom of a long wait at a doctor's office. Instead of pacing or escalating into a meltdown, he spent the entire hour and a half practicing, learning, and composing. When we finally left that day, the rest of us exhausted and irritated, he shared his first composition with a big smile.

In this era of smartphones, we all know very well how easily we can get addicted to our devices. Spending hours each day doing the endless scroll through Facebook and other social media sites just because we feel like we'll miss something if we don't. Both Google and Apple are aware of this and are trying to help control smartphone addition in their own way for Android and iOS.

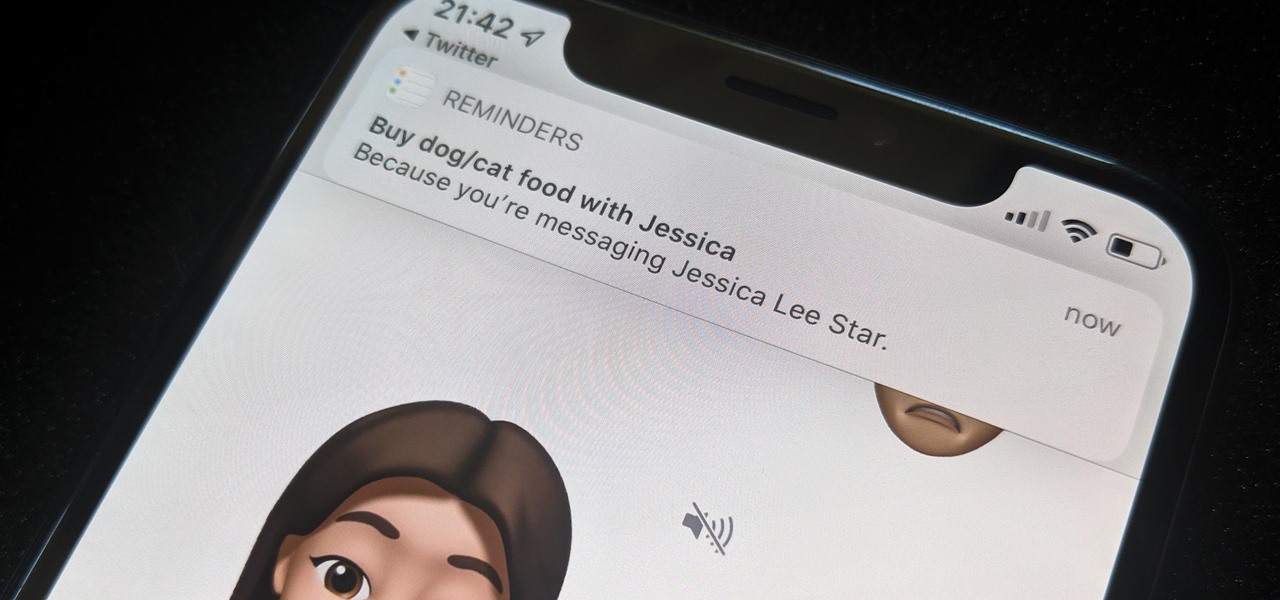
While iOS 13 might have made waves for some of its more prominent features — most notably system-wide Dark Mode — some of the more interesting tools lie with its smaller, unannounced updates. One of those updates is a new Reminders setting to tag contacts in a to-do task so that iOS pings you when texting that person in Messages.

Filmic Pro has a superb suite of professional settings — bit rate, frame rate, and mic choice, to name a few — which can enable you to capture the best footage possible. But different shots require different setups, and it can be frustrating to change settings on the fly. Filmic Pro lets you skip that whole process by saving your favorite settings as presets for quick and easy access.

When it comes to customizing Android, there's nothing quite like Magisk. You can potentially combine dozens of modules to create a one of a kind user experience tailored to you, but not all modules will work well together. You might run into a bootloop by accident once in a while, which could cause some issues on its own.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.

If you salivate at the idea of waking up to the Jarvis-powered smart window from the opening minutes of Marvel's Iron Man, then connected home appliance maker CareOS is here to make your playboy billionaire philanthropist dreams come true.