One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform the brute-forcing process, but not all are created equally.

The idea of remote assistant apps in augmented reality has been taking off in the last couple of years, but Epson is introducing a differing kind of solution for companies that may benefit from a more straightforward dynamic before going full-on immersive with higher-end AR remote assistance tools.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.
When flashing files through TWRP, ADB, or Fastboot, there's a slight chance for things to go wrong. Whether it's user error related or something else entirely, it's always good to have a backup plan. In most cases, you'll be dealing with a semi-brick or soft-brick, which can usually be solved by wiping the data of the device using TWRP. However, it can be more severe than that in some cases.

French cosmetics giant L'Oréal isn't wasting any time putting its new subsidiary, ModiFace, to work. On Thursday, the company launched a new tool that enables a photo-realistic augmented reality simulation of nail polish shades and textures to be accurately displayed on a user's fingers in real time.

Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

Germany-based Augmented reality software maker Re'flekt has added a new tool to its enterprise app development platform that makes it simpler to link AR content to physical objects.

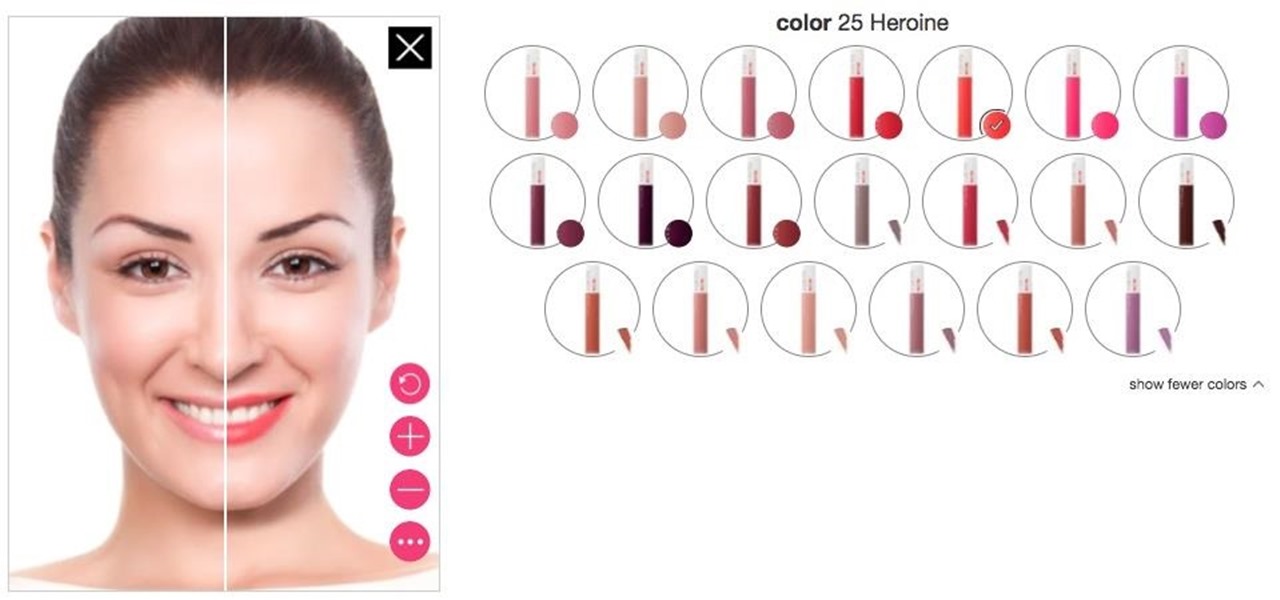
Department store chain Target is the latest retailer to offer an augmented reality cosmetics app for customers to virtually try on lipstick.

During Snap Inc.'s quarterly earnings report, released on Tuesday, the company disclosed that it snagged a revenue total of $230.8 million for the first quarter of 2018, an increase of 54% compared to last year, largely fueled by its augmented reality offerings and other advertising products.

Sketchfab, one of the leading 3D model aggregators, continues to defend its turf from encroachment by Google. This time, the company has deployed a new API that gives developers even easier access to Sketchfab's extensive library.

The latest cosmetics brand to launch its own augmented reality try-on tool is Cover Girl, which introduced its browser-based experience this week.

Android used to have a notification ticker, but those days are long gone. Now, important new messages pop up on the top half of your screen with what's known as a "heads up notification." If you're in the middle of something, these popup notifications can be pretty annoying — luckily, it's pretty easy to turn them off.

Although it sounds like a foodie's take on Facebook, what Calabasas, California-based FaceCake actually offers is more about augmented reality fashion marketing rather than food selfies.

Among consumer brands, cosmetics companies rival furniture retailers as the quickest to adopt augmented reality as a means to help customers visualize how products will look before they buy them.

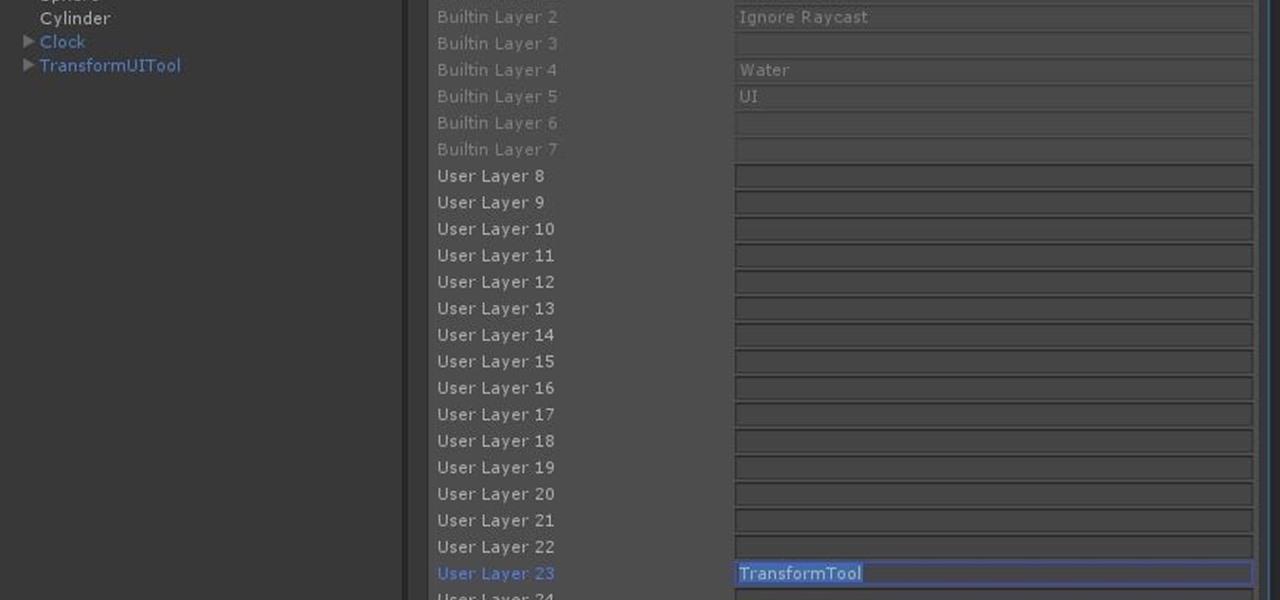
Now that we have unlocked the menu movement — which is working very smoothly — we now have to get to work on the gaze manager, but first, we have to make a course correction.

In 2013, Offensive Security released Kali Linux, a rebuild of BackTrack Linux derived from Debian. Since then, Kali has gone on to become somewhat of a standard for penetration testing. It comes preconfigured with a collection of tools accessible by a menu system, tied together with the Gnome desktop environment. However, Kali Linux isn't the only penetration-testing distribution available.

Buying a smartphone used is an excellent way to save money, but those savings come with a risk that your seller isn't as forthcoming as they claim. You don't want to end up buying a stolen smartphone because it might not work correctly ... and, you know, it's wrong. Luckily, there's an easy way to check if the phone you're about to buy is legit.

When it comes to modding an Android device, a custom kernel can take you farther than almost anything else. Most offer the ability to overclock your processor for performance gains, change your CPU governor, or even under-volt to increase battery life, among other features.

When it comes to hacking guides, most are written from the perspective of a Linux user. There are a few outliers, but it's mainly Linux, which leads to the idea that Linux is the only OS that's viable for hacking. This couldn't be further from the truth. A properly set up Apple machine can do quite a bit of heavy lifting.

When you were unboxing your Galaxy Note7, you probably wondered why a little metal claw tool was included in the packaging. Then, if you looked closer, you saw there were five plastic sticks included with the claw tool that came in two different colors.

First of all, I would like to apologize for a week long absents for the tutorials of this newly series, Raspberry Pi. But obviously I'm back and I present all you guys a article on turning your Raspberry Pi into a hacking platform. I'm gonna use the platform Kali Linux for the Raspberry Pi. I should note that I'm not gonna go into detail on how to install Kali Linux since OTW already has done a tutorial on how to turn your Raspberry Pi into a Hacking Pi. The point of this particular tutorial ...

Simmering or poaching food is a total pain sometimes. The problems are numerous: a layer exposed to air often dries out and creates a gross skin that can ruin the texture of the sauce, the poaching liquid evaporates too quickly and causes the poached protein to burn, and so on.

Screenshots are an indispensable tool when it comes to relaying information about what's currently showing on your monitor. Whether you need help troubleshooting an issue or you just want to save and share a protected image, screenshots are often your best bet.

Hello my anxious hackers, the week has started and here we begin a new series that I think will help many here and not only, for those that have the opportunity to follow our tutorials but they are not yet part of the community.

Brought to you by Purdy Paints The art of painting requires excellent tools. And with so many options on the market, it can be hard to find a brand that works for you and your DIY project. That's where Purdy comes in.

This is a collection of various guides and tools available on the internet. Instead of searching for 1 you can easily find whaht your looking for here.

We're all familiar with the sinking feeling that happens when you cruise through a recipe, only to arrive at an instruction that calls for a tool you don't have. Some of the best food hacks (and my personal favorites) exist to combat that problem. Why spend money on a kitchen tool—or worse, avoid a recipe altogether—when you could find a new way to achieve the same result?

Don't leave your tongs out by the grill, as they are one of the most useful and versatile cooking tools to have in your kitchen. In my house, they come in a very close second to chopsticks, which I cook with everyday. Like chopsticks, they make it easy to delicately flip and turn food with precision. But unlike chopsticks, there's no learning curve, so anyone can use tongs for easier, simpler cooking.

Meat tenderizers are absolutely necessary when dealing with leaner, tougher cuts like flank or skirt steaks. And while fruit like papaya, kiwi, and pineapple contain enzymes that can tenderize meat, the results can be hit-or-miss, and impart a fruity flavor that you may not always want.

Ghee is also known as clarified butter and is an integral part of cooking and a must have in most Indian kitchens. It is made from fresh butter that is melted and simmered to get a clear golden liquid. You can use the ghee to season lentils, vegetables, to make parathas, sweets or even use it as a spread.

Welcome back, my neophyte hackers! I have already done a few tutorials on password cracking, including ones for Linux and Windows, WEP and WPA2, and even online passwords using THC Hydra. Now, I thought it might be worthwhile to begin a series on password cracking in general. Password cracking is both an art and a science, and I hope to show you the many ways and subtleties involved.

How to use a tape measure so that you can write on it clearly. Tape measures are one of the most useful tools in your tool kit. Unfortunately it's difficult to write on them clearly because of its glossy surface. In this video l show you how to modify your tape measure to turn it into a really handy note pad.

Known for its easily recognizable filters—and coining the hashtag #nofilter—Instagram has long been an app that focused more on photo posting rather than photo editing. Yet today, Instagram released an upgrade for both Android and iOS users that edges the app towards becoming a full-fledged photo editor.

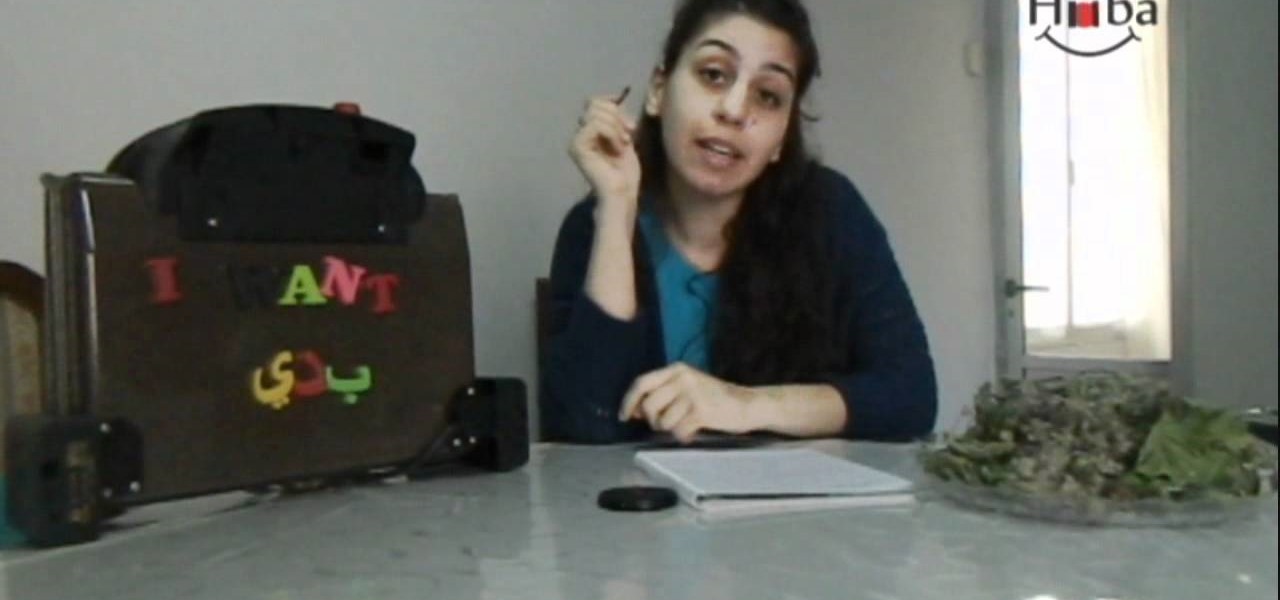
In this lesson I will teach you the verb "to want" and how to use it in sentences. A few practical sentences translated from english to arabic (lebanese) which you could use around Lebanese people.

Learn Arabic or, more specifically, Lebanese through these easy lessons. A few practical sentences translated from english to arabic (lebanese) which you could use around Lebanese people.

Learn Arabic or, more specifically, Lebanese through these easy lessons. A few practical sentences translated from english to arabic (lebanese) which you could use around Lebanese people.

Welcome back my social engineers/hackarians! Today we'll be looking into a fantastic piece of software, The Social-Engineer Toolkit or just SET for short. SET is designed, Developed and used by several Social-engineers. So... Let's get started!

A quick video demonstration about how I tie a tie. I forgave me for my broken English.