This simple technique to creating a bang when people open a door is sure to scare the daylights out of your friends. Using party poppers, you can take them apart and tie them across a door entry. When a person enters, the poppers explode. There are great reaction shots on this video as welll.
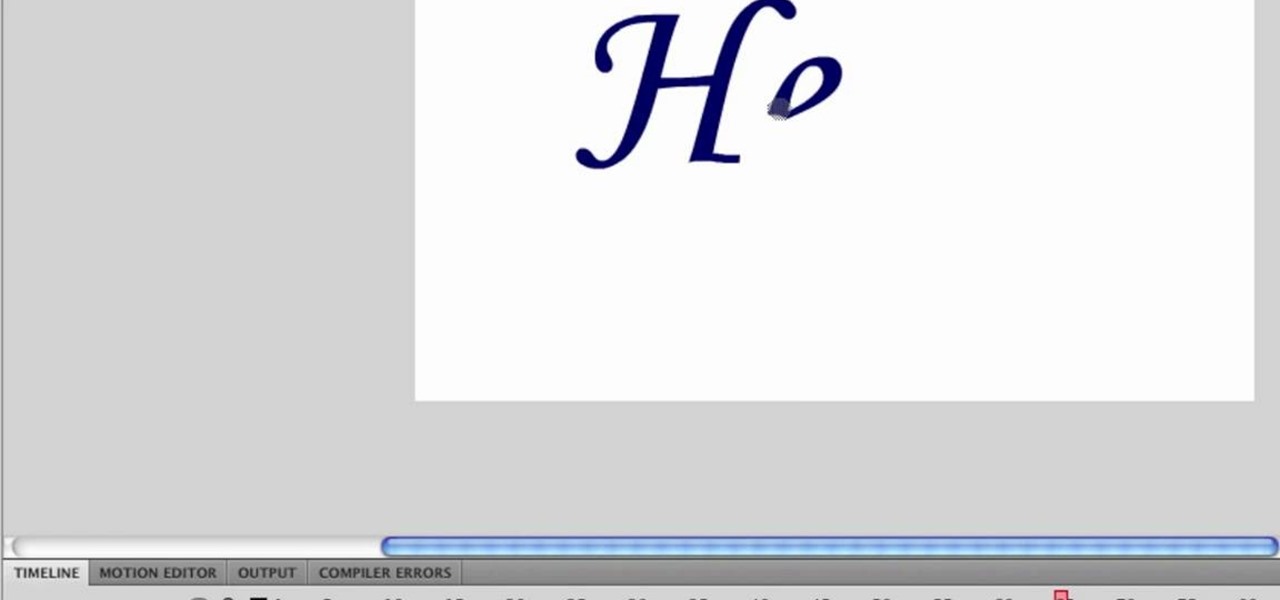
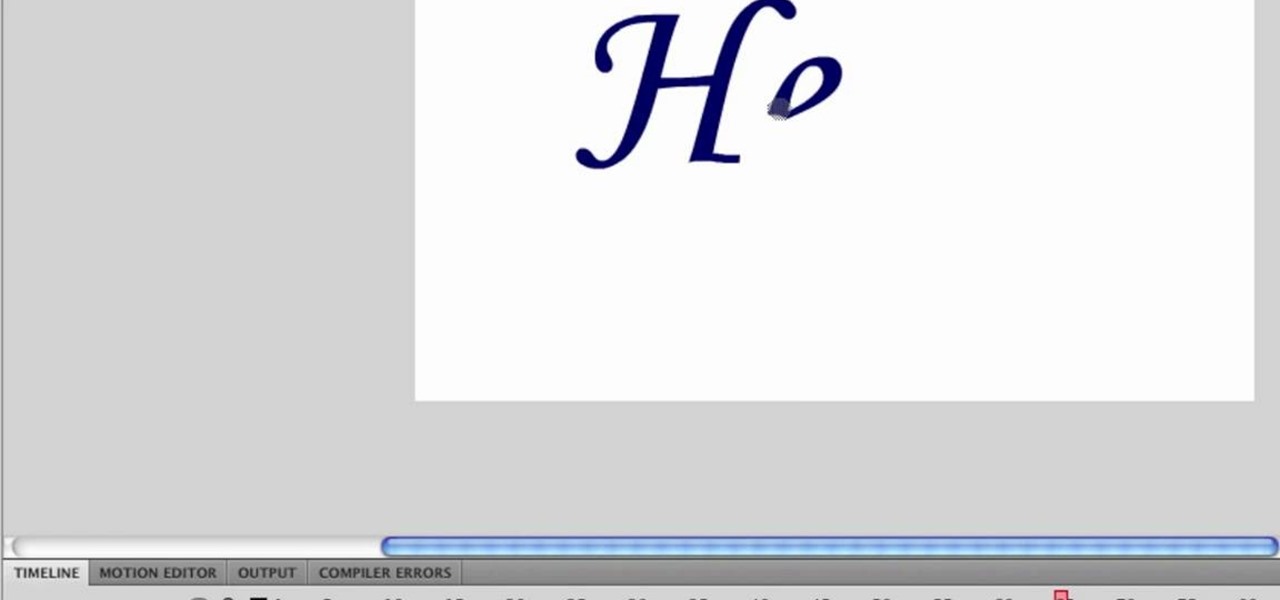
First type your word and set the font. Now select the word and break it apart by pressing the ctrl+B twice. Now select the erasing tool and erase the letters in reverse order like when you write that word, you write it in a order but you need to erase it just reversal of it as you can see in the video. Now press the F6 button, it will create a keyframe, select
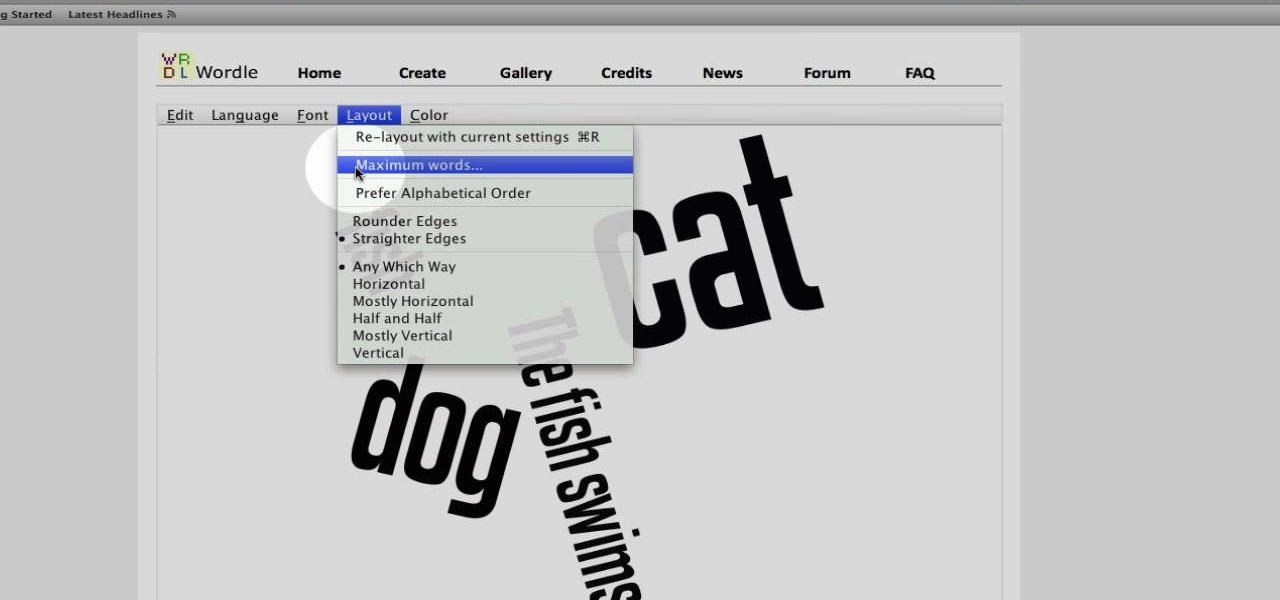
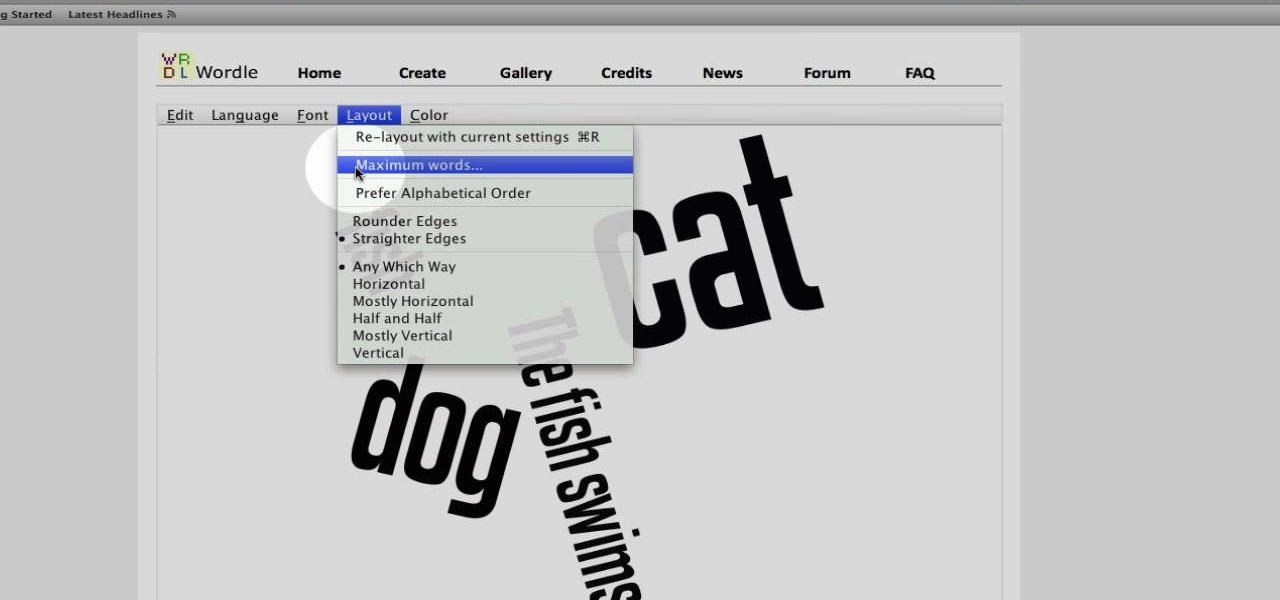
This video tutorial belongs to the Computers & Programming category which is going to show you how to use Wordle to create word clouds. Go to Wordle and click on the 'create your own' link. In the first box, type in your text, and in the second box enter the URL of any blog, blog feed or any other web page that has an Atom or RSS feed. In the 3rd box enter your del.icio.us username, if you have one. After typing in, hit 'go' and you get your Wordle file with the words written in different sty...

The video explains how to hack the game Agony: The portal. First he clicked the start game and created new character by entering the name as test dummy and set the difficulty level as normal. The he clicked the start campaign. While entering the game he skipped the tutorial and directly he went into the game.

The life of a busy entrepreneur isn't easy. In addition to coming up with original business ideas and marketing strategies, you also need to be continually thinking about investors, overhead, the competition, and expanding your customer base — often with a limited budget.

SEO is the name of the game. If you want your business or brand to succeed, ranking on the front page of Google is a boon. Getting to the front page of search engines takes work, but it's not impossible when you master SEO best practices.

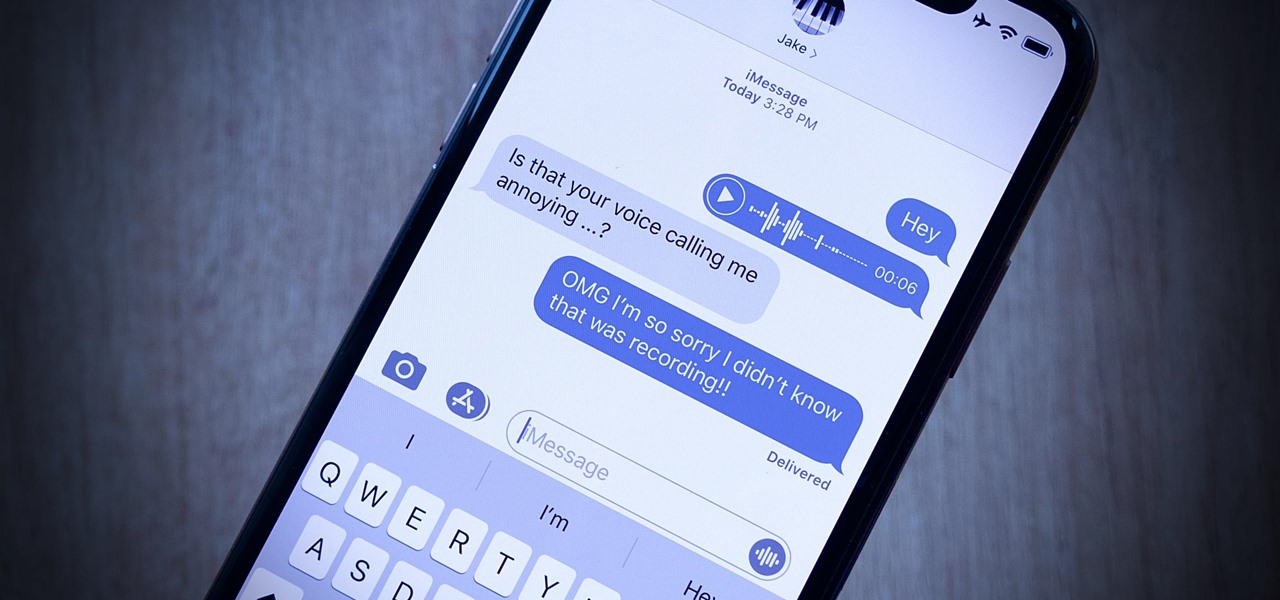
Your iPhone's audio messages may get you in trouble if they haven't done so already. It's way too easy for your iPhone to start recording without your knowledge, only to send a friend or family member a conversation you're having about them. (Awkward.) Luckily, protecting yourself takes only the flick of a switch.

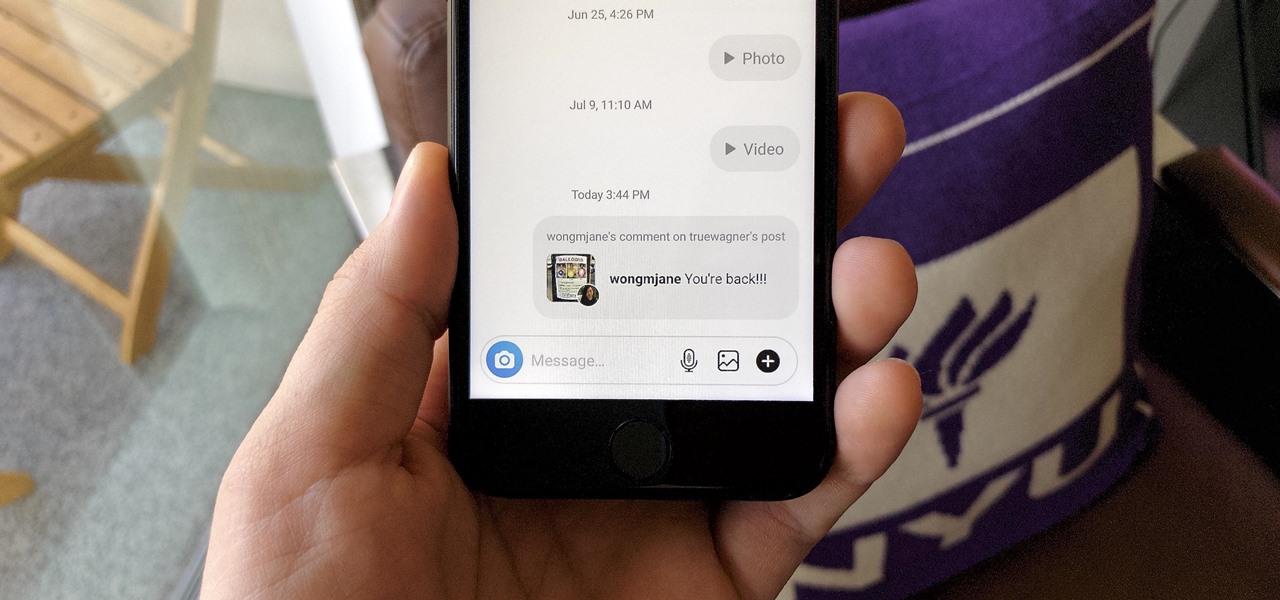
Sometimes, you'll see a comment on Instagram that you really need to share. Maybe it's something funny, possibly offensive. Whatever the case, the only thing to do is screenshot it and share that, right? Hopefully, not for long. Instagram is currently testing a feature that would allow you to share comments with others via a direct message and maybe even to stories and other apps.

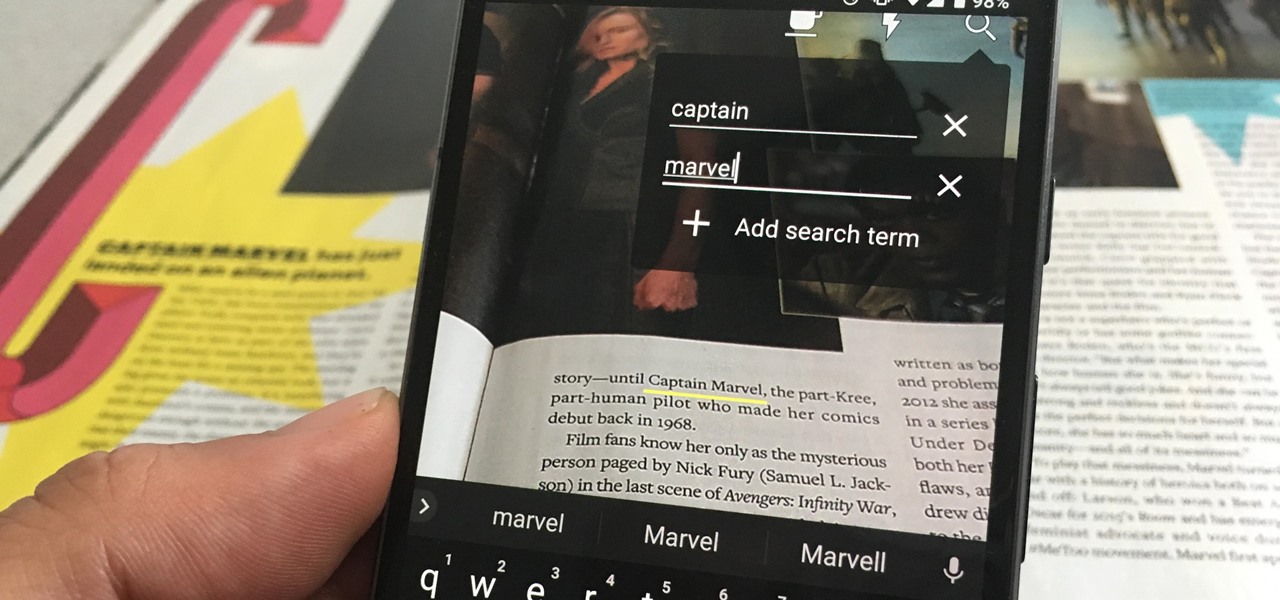
One of the neatest tricks available in Google Lens, an app that can identify and interpret real world information, is the ability to copy text from the app's camera view and paste it into a digital document.

With new iPhone models out, you'll have updated cameras to try out, a faster processor, and new colors to choose from. The only thing that could stop you from picking one up yourself is, well, your current iPhone. Here's how to check if you're eligible to upgrade to iPhone 11, iPhone 11 Pro, iPhone 11 Pro Max, or any other iPhone still being sold.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

While the USB Rubber Ducky is well known by hackers as a tool for quick in-person keystroke injection attacks, one of the original uses for it was automation. In this guide, I'll be going the latter, explaining how we can use it to automate Wi-Fi handshake harvesting on the Raspberry Pi without using a screen or any other input.

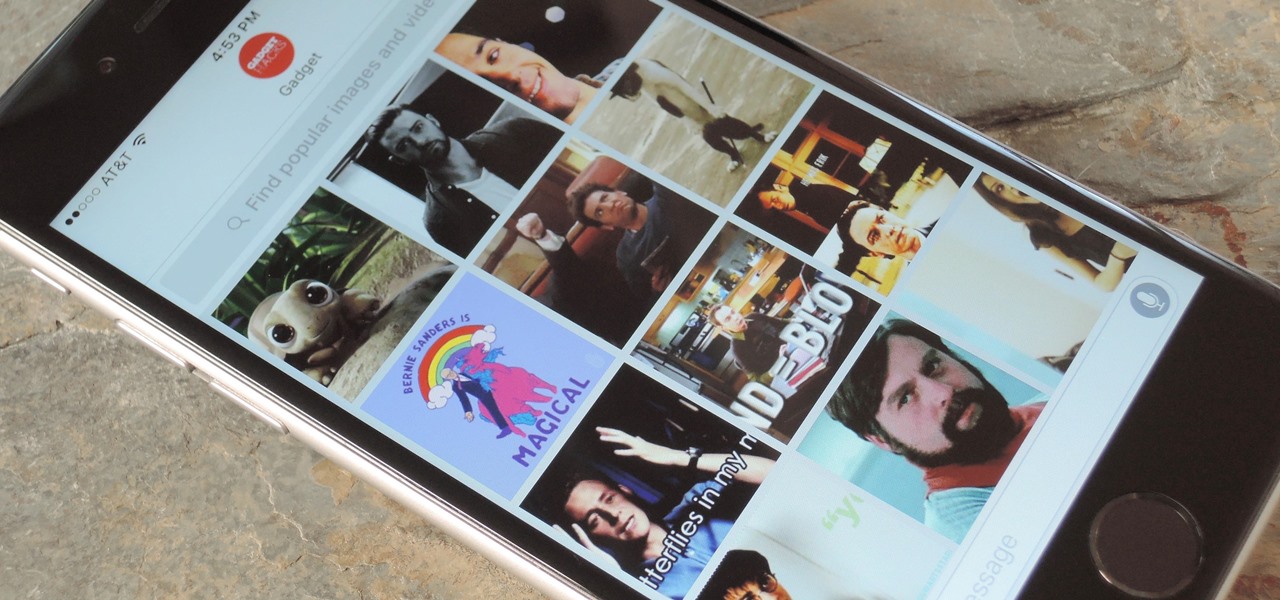
In the revamped Messages app in iOS 10, you can now send animated GIFs from your iPad, iPhone, or iPod touch without a third-party keyboard like Giphy or GIF Keyboard.

If you purchased something from iTunes, the iOS App Store, iBooks Store, Apple TV App Store, or the Mac App Store and it doesn't work, didn't download, is buggy, or wasn't what you thought it was, you can get a full refund from Apple—you just have to know how to ask.
Hello Null-Byte community. First off: this my first post here on Null-Byte. Some of you may have already seen me in the comment section, to all others: Hi, I'm the new guy.

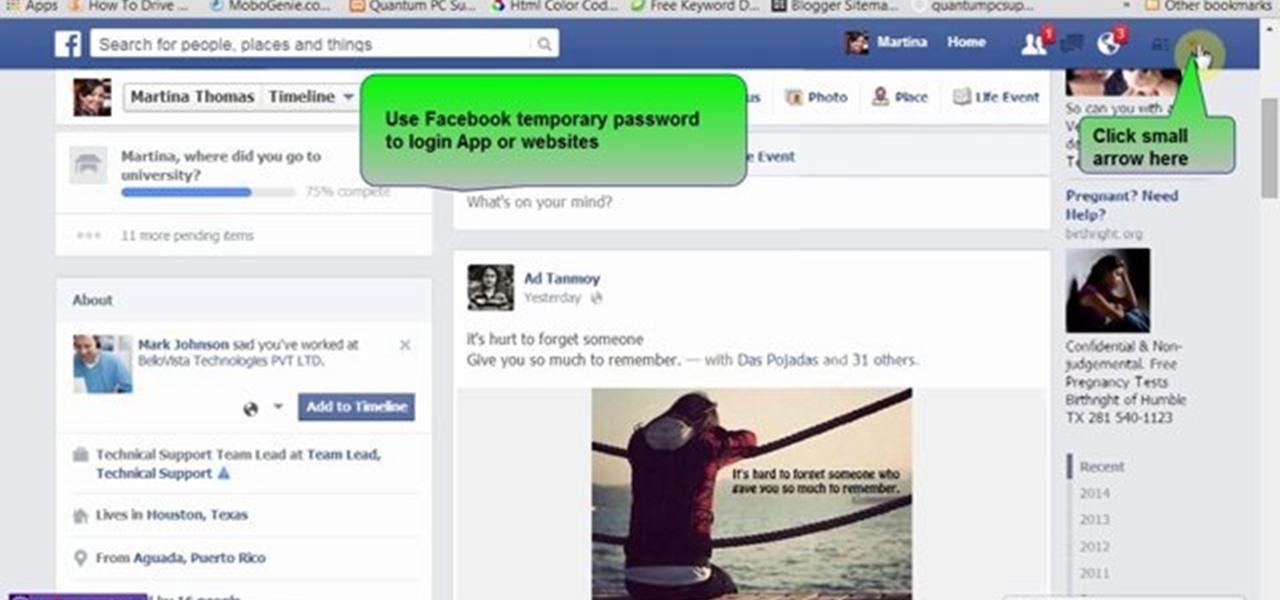
Many people use Facebook login detail to enter different apps or websites. This is somehow dangerous because unethical websites or apps may use your Facebook detail. So to avoid this warning Facebook is generating a temporary password for you. Now you could use this detail to login app or websites. You don't have to use your Facebook original login detail.

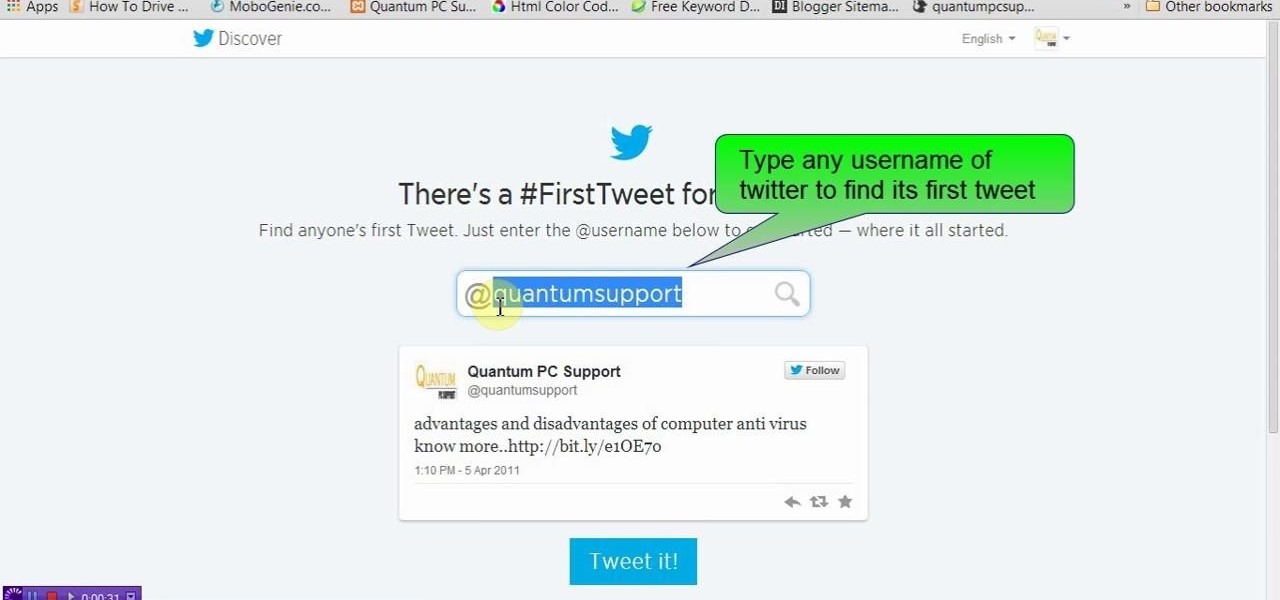
This video will show you how to see first twit of any user in twitter. You could type https://www.first-tweets.com in address bar and the site will be redirected to another place https://www.discover.twitter.com/first -tweet page. You have to enter the user name and twitter will fetch the first twit of that user. Watch the video and employ it yourself.

This HTML Web Design tutorial will explain how to add a Heading tag for your website. The heading tag is very important because it helps search engines to determine what the main topic is on a particular web page within your website. The HTML codes for heading tags range from h1 to h6 with h1 being the most important or in other words the main heading HTML web design tag. Make sure to give the h1 tag the most importance in terms of titles on your web page for headings. Another rule I recommen...

A hidden feature residing in Mac OS X Mountain Lion is the ability to view and also reply to your friend's tweets through the Contacts application, previously known as Address Book. The only way to do this, though, is to provide your Twitter account login data to the Contacts app. To integrate your Twitter, just go to System Preferences, then click on Mail, Contacts & Calendars and choose Twitter. Put in your Twitter login information and then click on Update Contacts. Twitter will use your e...

If you just got a new Android mobile phone, then chances are, the first thing you're going to want to set up is your email account, so you have instant access to your emails all the time, everywhere and anywhere. Setting up your specific email account or accounts is actually not hard. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up an email account on an Android cell phone.

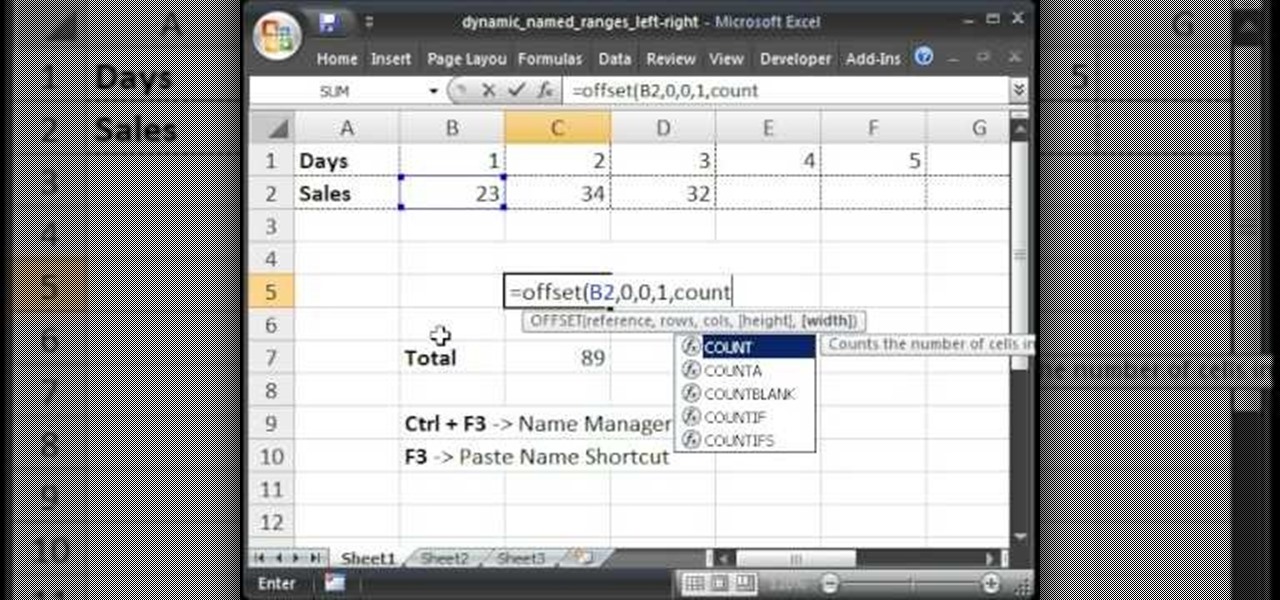
Teach Excel describes how to create a dynamically updating named range that goes from left to right using Excel. First, you define the named range by highlighting the cells containing numbers in a certain row. In the name box to the left of the formula bar, type the name of the data. In this example, the numbers correspond to sales, so type "sales." To check if the named range works, click on an empty cell and enter =sum(sales). That should return the sum of the highlighted cells. However, as...

Advance Photoshop shows viewers how to make the Photoshop CS3 icon in Photoshop. First in Photoshop go to File and then click New. Make a new blank at 500 x 500 pixels. Go to your layer button and create a new layer. Next, go to your rectangular marquee tool, hold down shift, and make the rectangle slightly smaller than the canvas itself. Set it from foreground to background and change the background color to a dark blue, enter 15396F for the color. Click on foreground color and enter 3070CA ...

This video explains how to add a bulleted or numbered list in Microsoft Word 2007. The shortcut to create a bullet-list is simple holding Shift and pressing the "A" key. After you hit the space bar or type a character the bullet will appear, and when you hit the Enter key it will continue the bulleted list. For numbering you just need to type the number you want and a dot after it and it should begin a numbered list. The list will continue if you press enter just like a bullet-list will. If y...

Want to forget about always pulling out your credit card to purchase something on your BlackBerry? There's a little application that can do it all for you? But how? Best Buy has answers. The Best Buy Mobile team explains how to use the BlackBerry Wallet application. This application can store personal information such as credit card information and shipping addresses on a secure website for easy access when shopping online.

This is a great playthrough of The Saboteur for the Xbox 360. In the fourth mission in Act 2: Jailbreak, you will need to do the obvious… jailbreak. Once you acquire the papers to enter Area 2, you'll be able to start this mission by visiting the resistance in the Western District. They will charge you with freeing a man named Bryman from a Nazi prison. Grab a car and follow the GPS to the destination. Here you'll find a heavily occupied Nazi area. Bryman's cell is within the courtyard surrou...

Check out this L4D2 walkthrough for some tips on Campaign 5: The Parish - Park. Stock up on items and exit via the door right next to the one you entered. Clear out any zombies and work your way up the large staircase into the park. Be prepared to deal with a likely Crescendo event in the plaza here. Pick a one of the staircases to climb up and enter the park. The restrooms near the entrance of the park usually contain a throwable item or two. For more info, watch the whole gameplay.

Farkle hacks, cheats, glitches. How to hack Farkle. Watch this video tutorial to learn how to hack Farkle with Cheat Engine (09/12/09).

TWRP is the premiere custom recovery for Android because of how many devices it supports and how simple it is to use. But installing it in the first place hasn't always been the easiest thing to do — until now. With the help of a Magisk module, you can finally use one Android device to flash TWRP on another.

In previous Android versions, you lost about an inch of screen real estate to the status bar and navigation bar. But if you enable Android 10's new navigation gestures on your Samsung Galaxy, you can regain the bottom part — and with the help of ADB, you can reclaim the top portion as well.

At least one hurdle to China-based augmented reality startup Nreal going mainstream in the United States may be about to be knocked down, thanks to behind the scenes legal movements Next Reality has uncovered.

Semi-untethered jailbreaks are here to stay, as evidenced by iOS 11's Electra method, Chimera for iOS 12, and even the new bootrom-based Checkra1n tool for iOS 13. While not as convenient as fully untethered, re-enabling a semi-untethered jailbreak is still pretty easy once you get used to the steps involved.

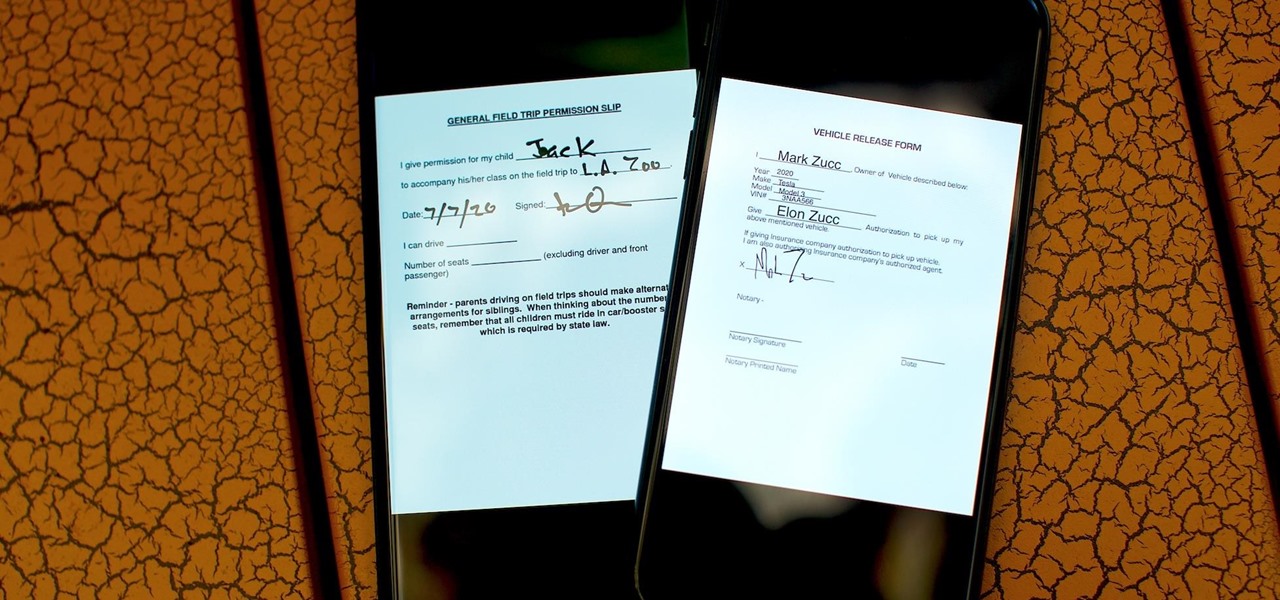
As paper forms become a thing of the past, it's becoming commonplace to fill out contracts, rental agreements, waiver release forms, and non-disclosure agreements online. You can easily fill out forms on your laptop, but how can you best do this using your iPhone or Android device?

Your writing is just that — yours — so the work you do in Apple Pages should remain private until you choose to share it. Apple seems to share this sentiment. As another symbol of its dedication to user privacy and security, the company includes a feature in its word-processing app for iOS that allows you to lock documents behind a password, as well as with Face ID or Touch ID.

The first thing you'll always have to do before getting your customization game on with most phones is to unlock the bootloader. Doing so opens the true potential of the device, allowing you to root, install TWRP, Magisk, custom ROMs, and other mods. No matter your wants or needs, there's no way around it — the bootloader must be unlocked to modify the system.

When Stardew Valley launched back in 2016 on Steam for PC, it was instantly deemed a success for steering the RPG farming simulator genre back on the right track. Before its release, we hadn't seen too much in this particular field of games that caught the eye of the general public. Since then, the mega-hit Stardew Valley has made its way to the mobile world of Android and iOS.

Before you can dive into customizing your OnePlus 6T, you must take the initial step of unlocking the bootloader to gain the ability to install TWRP, Magisk, custom ROMs, and other mods.

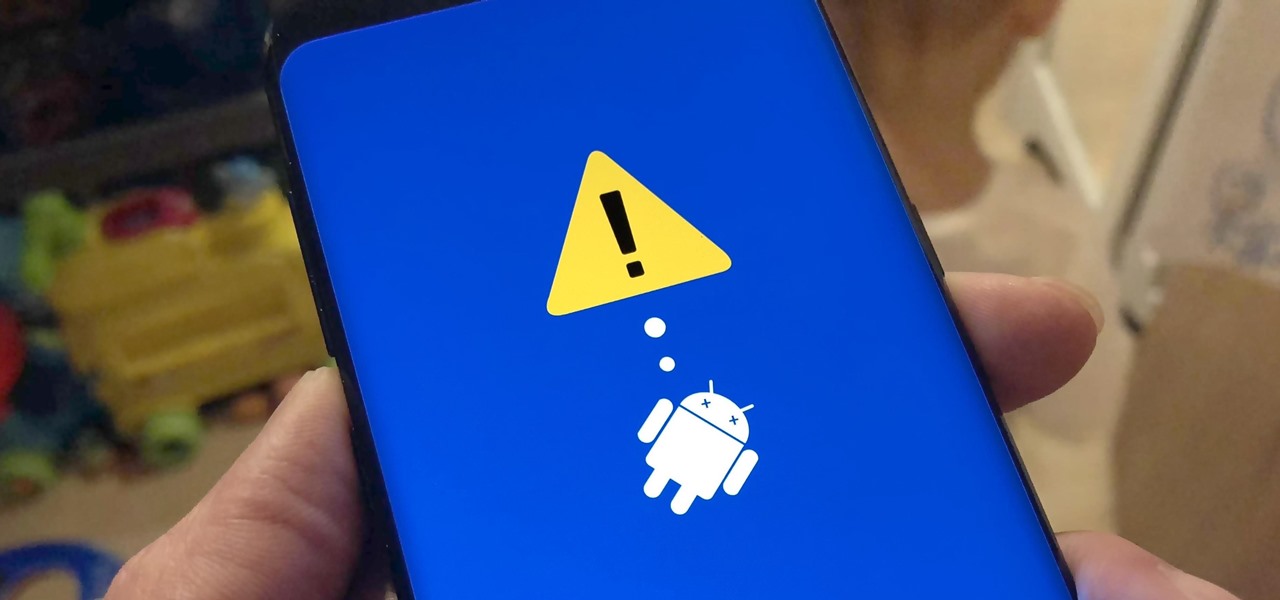
As advanced as the Galaxy S9 is, it can still be susceptible to the occasional hiccup. Several factors can cause your smartphone to behave erratically or become unresponsive, such as buggy apps or updates that didn't properly install. Luckily, most of these issues can be easily resolved with a press of a button — or two, to be exact.

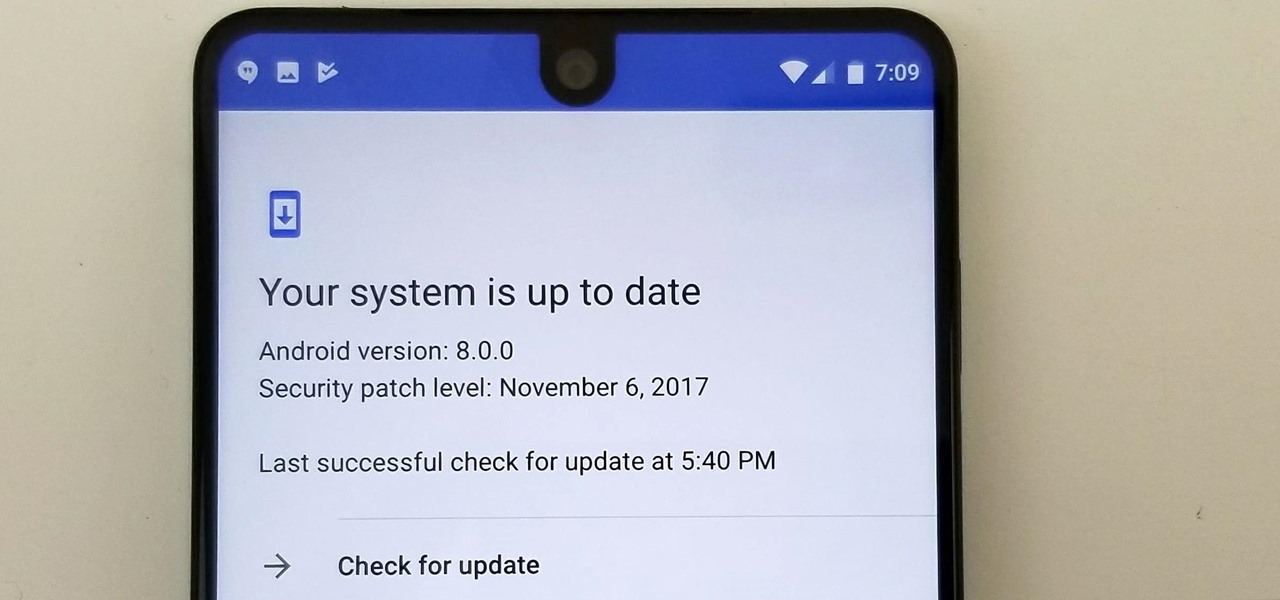
Essential just dropped the Oreo Beta Program for their flagship PH-1 phone. Users have been eagerly awaiting this update as the early Nougat builds of the PH-1 software have suffered from numerous performance issues and lag. The good news is that you can grab the Oreo update today with a few simple steps.

Ransomware is software that encrypts a victim's entire hard drive, blocking access to their files unless they pay a ransom to the attacker to get the decryption key. In this tutorial, you'll learn how easy it is to use the USB Rubber Ducky, which is disguised as an ordinary flash drive, to deploy ransomware on a victim's computer within seconds. With an attack that only takes a moment, you'll need to know how to defend yourself.

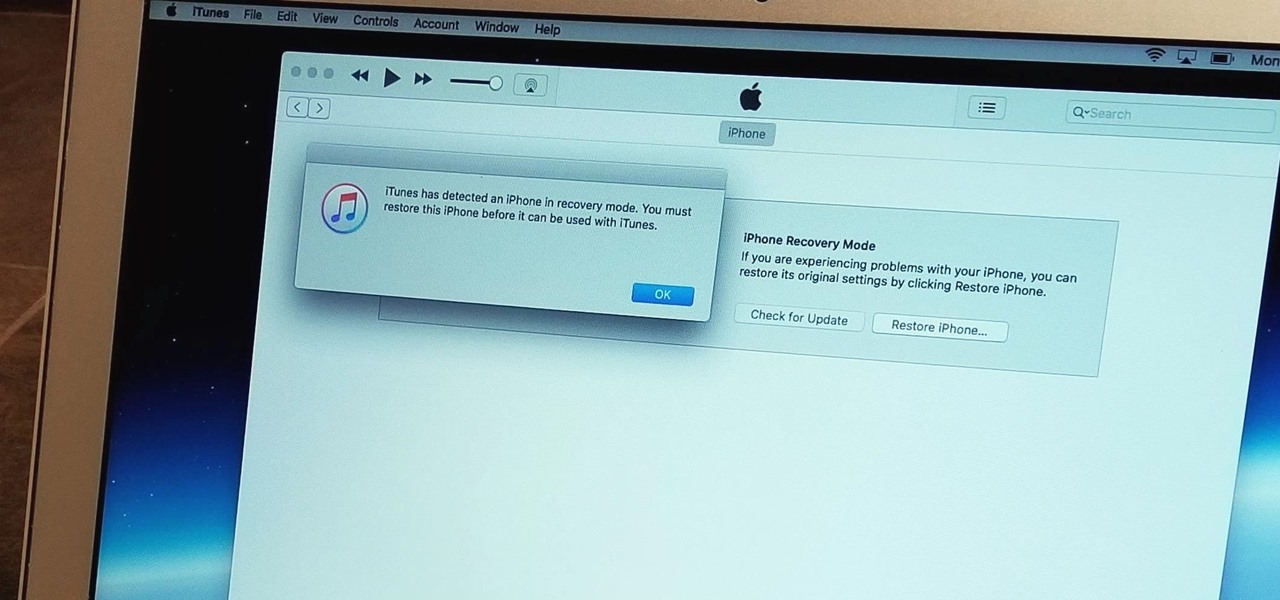
With the iPhone 8, 8 Plus, and the exclusive iPhone X, Apple has come full circle in transitioning its users away from the home button present since the first iPhone a decade ago. This gives us a window into Apple's design philosophy moving forward, but it also presents some new problems, especially when it comes to entering and exiting DFU mode in iTunes.