I don't know about you, but I was obsessed with handheld gaming devices when I was younger. Between my Game Boy and multiple Tamagotchis, I was guaranteed hours of entertainment that could fit comfortably in the palm of my hand.
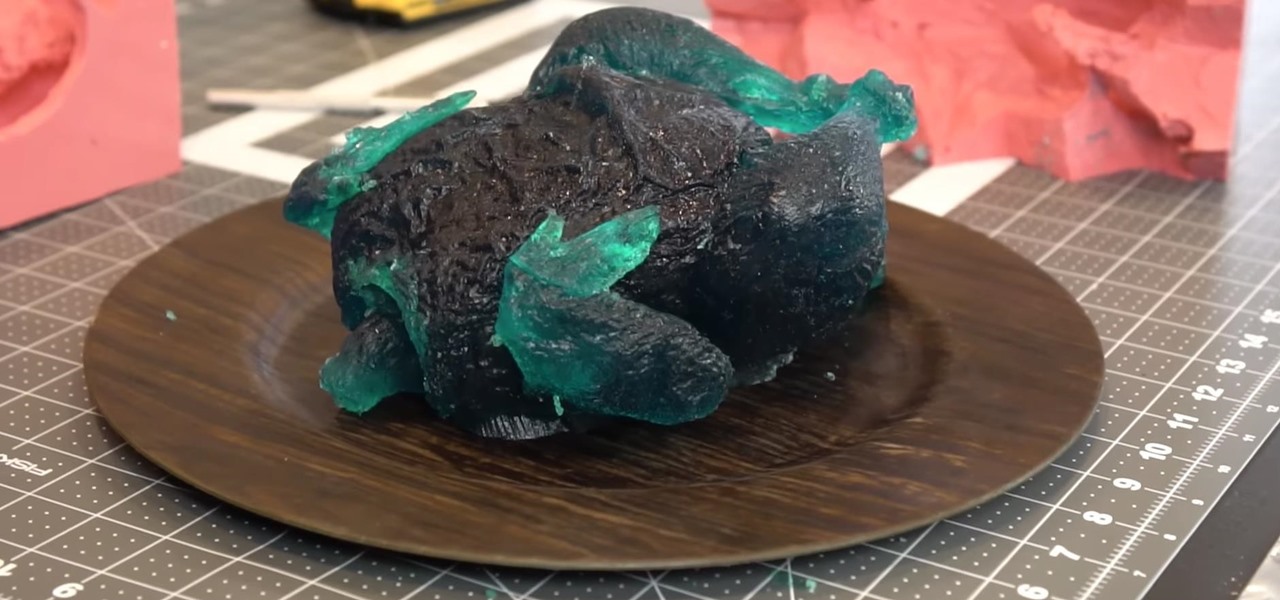
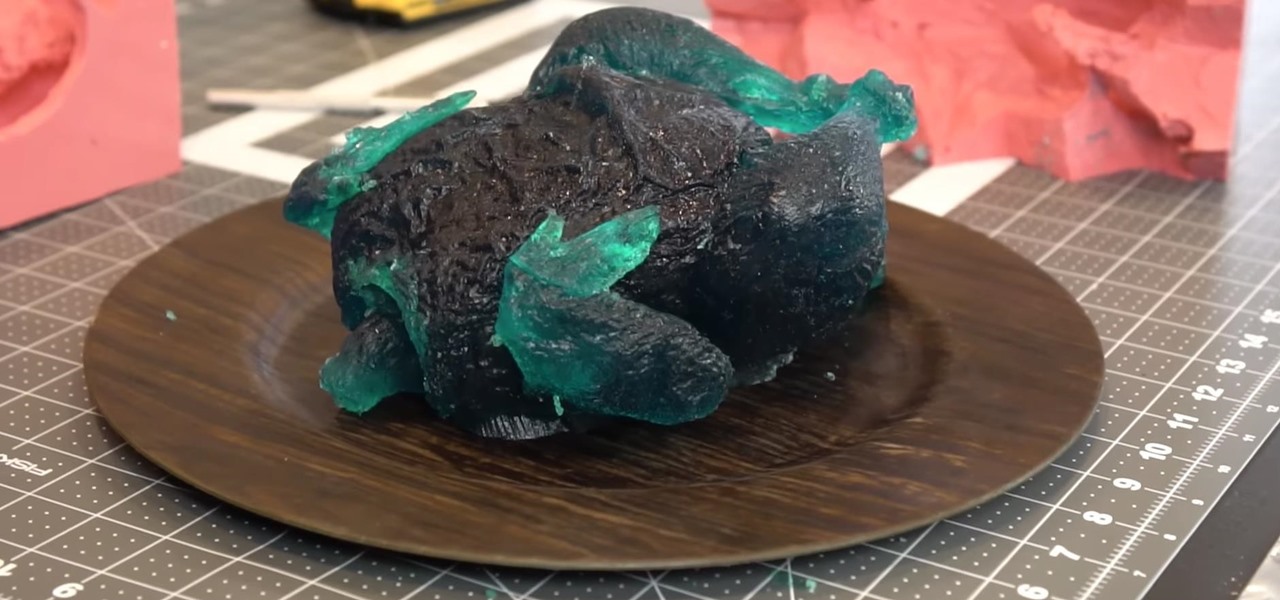
We've seen many things get gummy-ized over the years—worms, insects, Coke bottles, glass cleaner, Legos, brains, Nutella, and even tiny LEDs—but nothing compares to YouTuber and WonderHowTo favorite Grant Thompson, aka The King of Random, who made one helluva creepy gummy chicken that's just as big as the real deal.

If we learned anything from Mulan, it's that "the flower that blooms in adversity is the most rare and beautiful of them all." Well, these have been a trying couple of weeks in the US, hence the need for a blooming marshmallow flower.
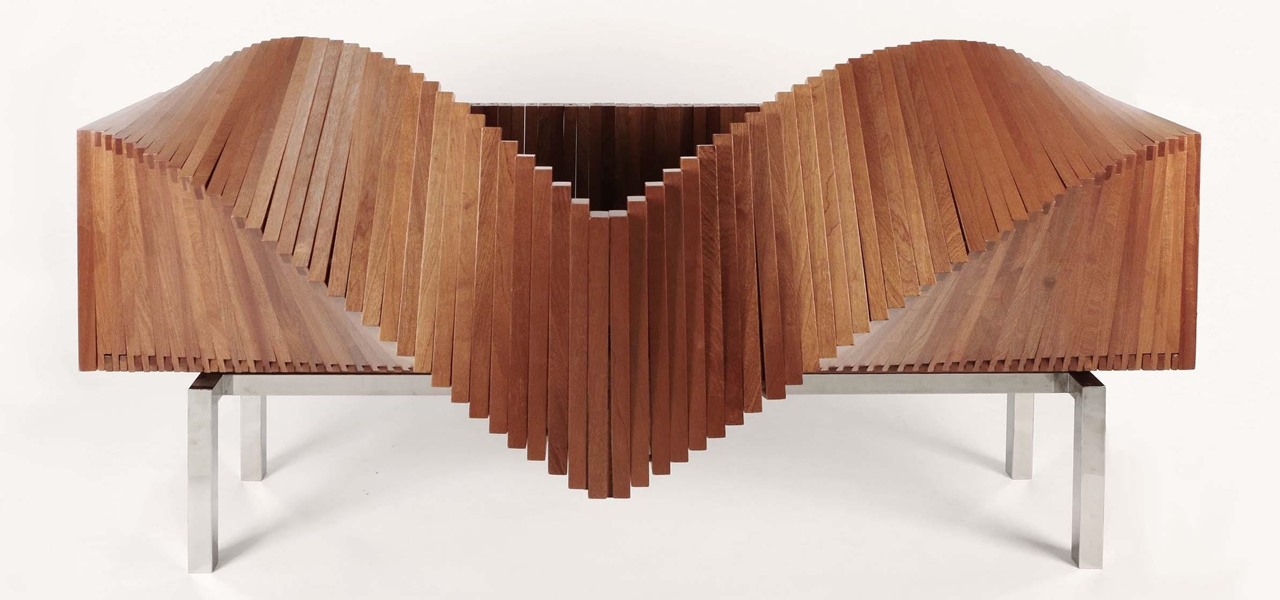
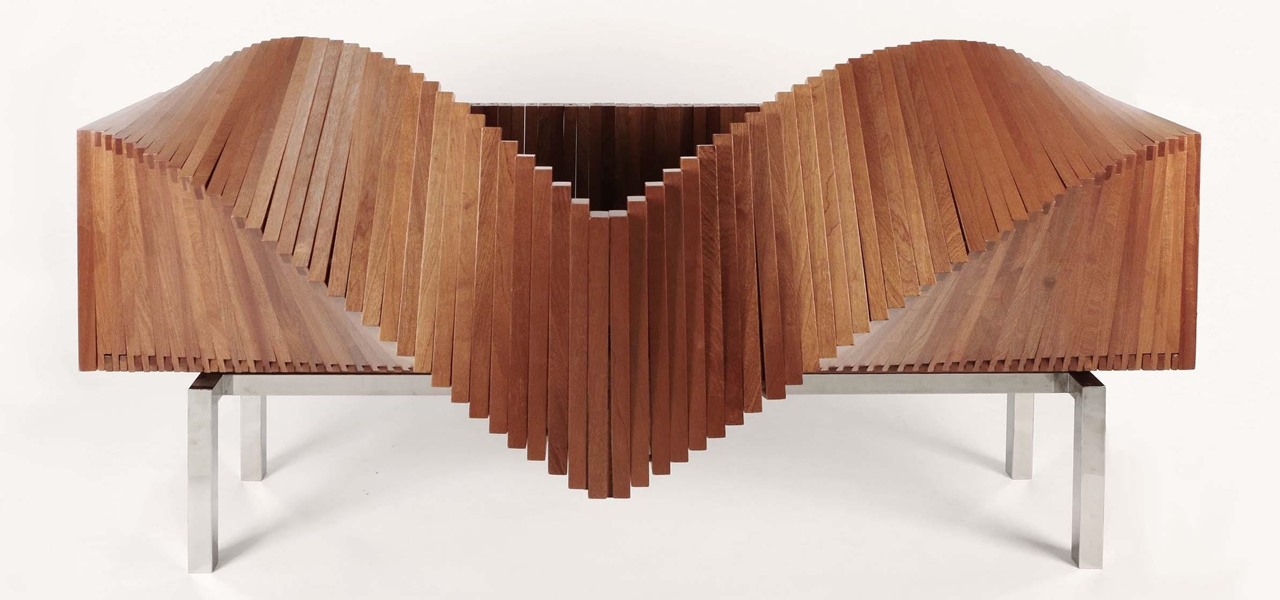
If you're looking to mix up your home décor with something a little bit outside the traditional cabinet box set, check out the amazing Wave cabinet from NYC-based, Chilean designer Sebastian Errazuriz. This revolutionary design will change the way you think about interior decoration and furniture functionality.
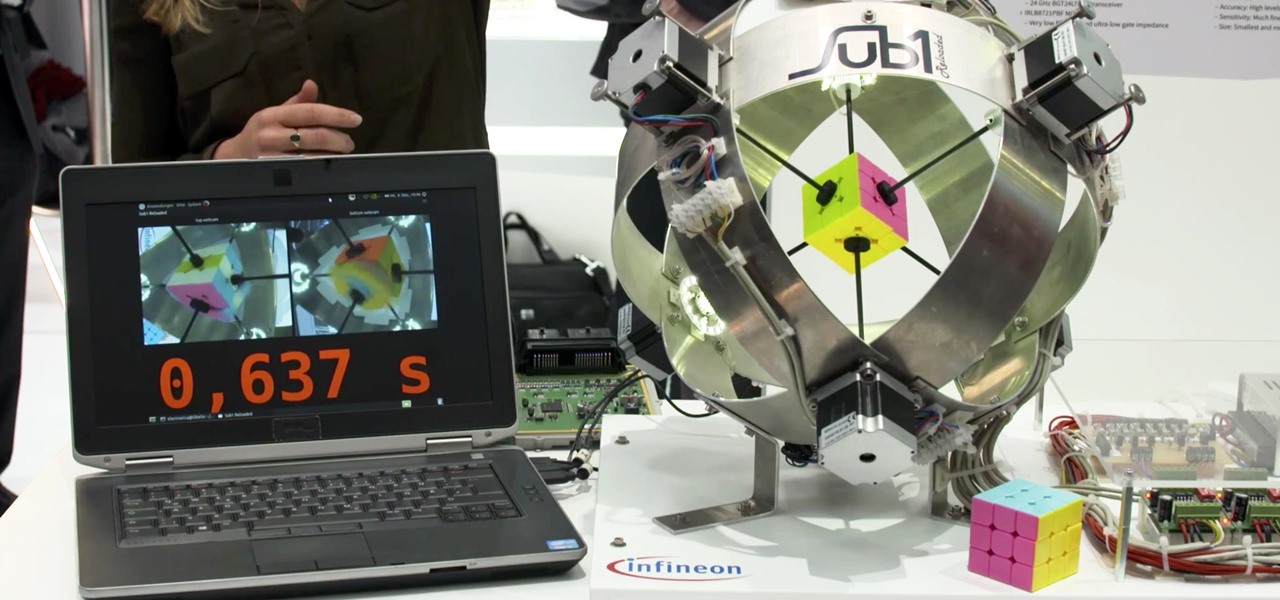
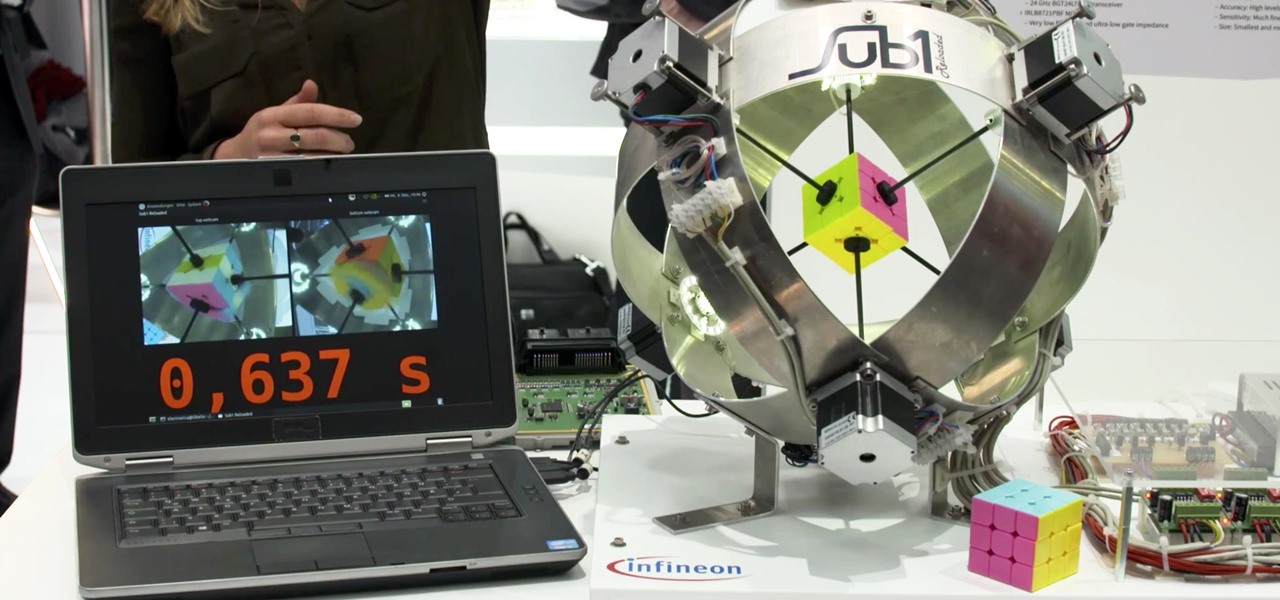
In December of last year, Australian Feliks Zemdegs broke the human world record for solving a Rubik's Cube with a time of 4.737 seconds. Well, this robot did it way, way faster by solving one in under 1 second. Don't tell me a robot takeover isn't real possibility.

Copying files from a computer to your Android device has always been pretty straightforward—just connect the two devices with a USB cable, open your desktop file explorer, then move the files over. But what if you didn't need any wires at all?

In the past, some of Google's Nexus devices have had root methods even before the phones hit shelves. The Google Pixel and Pixel XL are basically Nexus devices from a software standpoint, so why have we gone more than a week since release without a working root method or custom recovery?

Android device manufacturers may see the new Pixel "Phone By Google" devices as just another competitor, one that likely won't upset their entry-level margins. But that would be a mistake. Pixel is Google's call to action. With Google now offering as near to perfect an Android experience as we've had so far, OEMs that want to keep selling smartphones in a world flooded with them will need to start working for the privilege.

If you own a Samsung Galaxy S7 and use the Samsung Gear VR, you may have woken up yesterday to an unpleasantly hot surprise. But don't worry—your phone isn't going to explode (probably). The problem is with a stubborn update to the Oculus apps.

Some manufacturers, like Samsung and LG, have had split-screen multitasking on their custom versions of Android for years. But starting with Android Nougat, Google added this functionality to AOSP, which means that all phones and tablets running Android 7.0 or higher will now have a new multi-window mode.

Many phones these days are being manufactured without a notification LED—it's a cost-cutting move, and it's really not an essential component. However, the notification light on Android devices has traditionally alerted users to any missed messages, and this is functionality you can't get without the proper hardware.

These days, the user experience on stock Android is a lot more refined and polished than manufacturer skins like Samsung's TouchWiz or HTC's Sense. This is mostly due to Material Design, the look and feel that Google implemented back in Android Lollipop, which has finally started to give Android a unified appearance with its sleek icons and abundant use of colors.

When you change smartphone ecosystems, there are a lot of minor hurdles to clear along the way. It's definitely not hard to switch from Android to iOS, but little things like making sure your contacts get transferred over can take a bit of work.

Wi-Fi signals have limited range, so if you live in a two-story house or work in a larger office, you may have set up multiple routers or repeaters to ensure full wireless coverage. Sadly, Android handles the transition between networks pretty poorly.

Many midrange phones are being manufactured without a gyroscope sensor—the Moto X Play, third-generation Moto G, and several of Samsung's Galaxy Grand models, among others. It's not exactly an essential smartphone sensor, and leaving this out keeps the phone's price point down, so it's an understandable omission.

Like previous installments in the Pokémon series, as you progress through Pokémon GO you'll be able to evolve your Pokémon into more-powerful monsters with new and more-damaging attacks. However, unlike older entries in the series, your Pokémon won't simply evolve when they reach a certain level. Instead, you'll have to "feed" them a certain amount of character-specific candy to induce the transformation.

One of the biggest causes of smartphone battery drain is the mobile data connection—particularly if you live in an area with poor reception. But, chances are, you don't actually need this connection most of the time, because you're probably connected to Wi-Fi for a good chunk of the day, which uses far less battery life.

If not the future of computing in general, augmented, virtual, and mixed reality certainly will change the world of gaming. If you want to try your hand at shaping this evolved medium, the Unite Europe conference posted a talk that explains the first things you need to learn to develop holographic games.

If you're a fan of sleek, powerful computers and highly-customizable smartphones, then you probably own a Mac and an Android device. But the downside to this glorious hardware pairing is that it can be hard to get the software on the two devices to play nice together.

Even with today's high-powered devices, battery life is still an issue. We, as users, have to almost habitually check the current battery percentage, because otherwise, we might end up draining too much in the morning, then get stuck with a dead phone at night.

There are so many great apps in the Google Play Store that it's become the number one app marketplace in the world.

Google has an intriguing feature called Nearby that lets users share content without being on the same Wi-Fi network, or without even exchanging contact info first. Instead, the function uses an array of standard smartphone features, as well as subsonic sound, to identify other devices that are in the room, then makes a secure connection to transfer any data.

GIFs are awesome, but GIFing from your keyboard is some next-level stuff, and Apple knows this. That's why they've included a way to find and send GIFs in Messages from the stock iOS 10 keyboard. However, iOS 10 is not out for the public just yet, so if you want to easily send GIFs in your messages, you'll have to settle for a third-party keyboard.

If you've been keeping tabs on the rumor mill for the iPhone 7, one of the most discussed elements of Apple's upcoming device is the possible elimination of the headphone jack in favor of a Lightning connection.

Facebook Messenger is getting ready to roll out a Snapchat-esque feature that will let users send messages that self-destruct after a certain amount of time, so you'll have an extra level of security when you need to send sensitive financial information or, more likely, risqué texts or images.

According to sources, Google has been working on a travel app for some time, and now it has a name: Google Trips. Google Trips aims to be the all-in-one place to go for travel information about your trip. It hasn't been officially announced, but from the leaks that have come out so far, think of it like Yelp, TripAdvisor, and your itinerary in one.

It seems like Microsoft has finally come to the realization that their Windows Phone mobile operating system is probably never going to compete in today's smartphone market. Why do I say that, you ask? Because they've recently started to embrace the more popular platforms by releasing some quality iOS and Android apps.

Samsung's Galaxy S7 is an incredible piece of technology, but the Skype app that's preinstalled on some models may have some nasty issues, such as video and audio that freezes. Luckily, the fix for these problems is a simple one, although somewhat buried in the phone's Settings app.

If history holds true, we'll see the iPhone 7 arrive this September, and just like many times before, there are already a ton of rumors about its features. As usual, many claims are pure speculation, but there are some trustworthy reports and lots of good information we can use to make some educated guesses regarding Apple's upcoming flagship.

Over the course of the past year, a lot of Android apps have added pull-to-refresh functionality. It's a very useful and intuitive gesture, because all you have to do to refresh the page you're viewing is scroll to the top of the screen, then slide your finger down one more time.

Hello Friends … My name is Suresh Senarathna and this is my first “How-To” post,

Smartphone displays are getting bigger every year, and Samsung devices are at the forefront of that trend. But, from a software standpoint, the icons, buttons, and other on-screen elements seem to stay at the same scale. So while phones are getting bigger, their interfaces are getting bigger as well.

Android's flexible operating system allows for lots of customization, and one of the most common ways to add personal flair to your smartphone is to set your own ringtones and notification sounds.

Hey everyone, this will be a quick post. Facebook does not use HTTP Strict Transport Security (A header that tells the browser to only use HTTPS when communicating with the server) on subdomains of facebook.com. That means, if someone uses facebook in a different language, the browser will attempt to connect using HTTP first. An attacker can intercept that request and serve a different page, including a fake login one.

You gotta love Android—not only can you replace your default home screen entirely, but there are tons of options that provide alternative methods for launching apps with ease. We've covered some of these options in the past, including an app called Bar Launcher that lets you launch apps from your notification tray—but that one's starting to look a little dated these days.

Android 6.0 Marshmallow added a new permissions system that can make your digital life much more secure. Unlike previous versions, apps now have to ask for your consent before they can access certain data, which puts you firmly in the driver's seat.

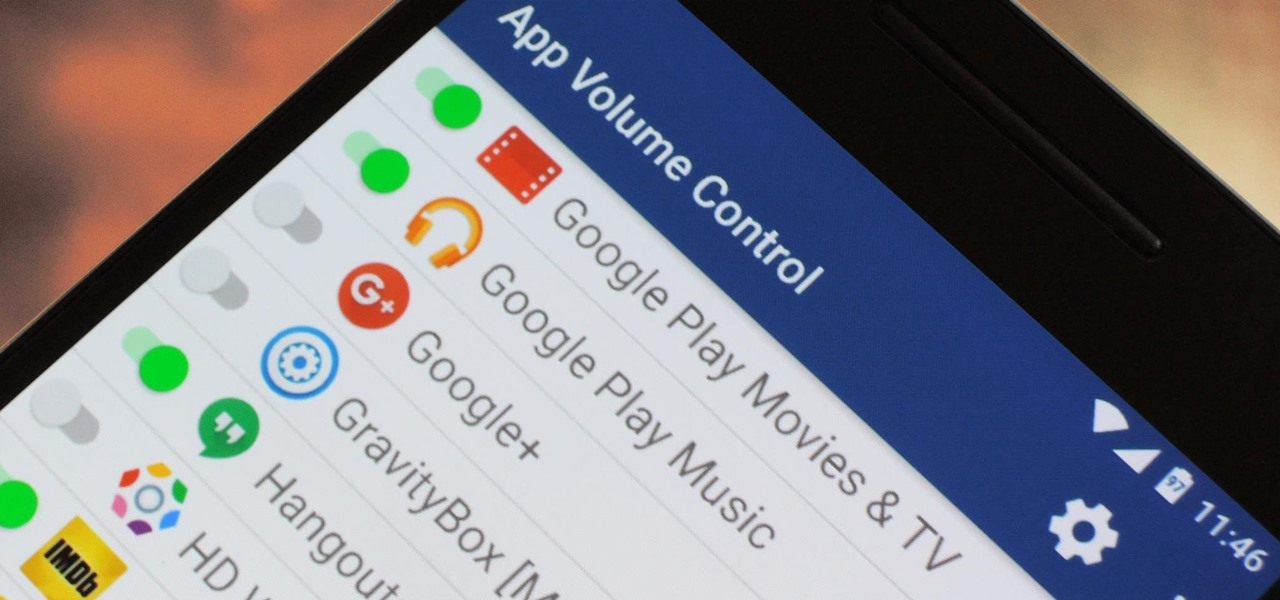
You can do practically anything with a modern smartphone or tablet, so it stands to reason that the apps you have installed may serve vastly different purposes. Picture a game and a video player sitting right next to each other in your app drawer—odds are, you want the sound turned up while you're watching videos, but would prefer that the game was muted or a little lower. As a result, we're constantly tweaking volume levels to get the best experience.

infosecinstitute posted a handy article about what to expect in the new year for cyber security, along with highlighting major game changers from 2015; 2016 Cyber Security Predictions: From Extortion to Nation-state Attacks - InfoSec Resources.

It's looking more and more likely that rumors stating that the iPhone 7 will not include a 3.5 mm headphone jack are true. Chinese websites Wei Feng and Anzhuo.cn reported that anonymous sources on the supply chain confirmed that the controversial design choice is a reality.

Virtual reality technology company Oculus VR announced that it will begin accepting preorders for its long-awaited Oculus Rift headset beginning Wednesday, January 6th, at 8 a.m. Pacific time.