In Minecraft, a large aspect of the game is PVP (Player vs. Player Combat). A hardcore Minecraft fan will remember that back in Beta 1.8, combat was switched up, and it really changed the game around. Here are some tips on what a two-year Minecraft player has to say.

An internet connection has become a basic necessity in our modern lives. Wireless hotspots (commonly known as Wi-Fi) can be found everywhere!

Steampunk is a tremendously interesting phenomenon because of its reliance on science fiction, and fiction in general. Steampunk can arguably be broken down into two categories: the fiction, and the aesthetic. Sometimes these categories cross over, but they're often more distinct than most people suspect; that said, the aesthetic is firmly based in works of fiction.

In this series of video music lessons you'll learn how to play Bossa Nova classical guitar. Expert Ryan Larson shows you the essential scales and chord progressions you'll need to know to play Bossa Nova songs, taking you through a piece measure by measure, and offering tips on the distinctive plucking technique used by Bossa Nova guitarists.

In this series of video music lessons you'll learn how to play Bossa Nova classical guitar. Expert Ryan Larson shows you the essential scales and chord progressions you'll need to know to play Bossa Nova songs, taking you through a piece measure by measure, and offering tips on the distinctive plucking technique used by Bossa Nova guitarists.

In this series of video music lessons you'll learn how to play Bossa Nova classical guitar. Expert Ryan Larson shows you the essential scales and chord progressions you'll need to know to play Bossa Nova songs, taking you through a piece measure by measure, and offering tips on the distinctive plucking technique used by Bossa Nova guitarists.

In this series of video music lessons you'll learn how to play Bossa Nova classical guitar. Expert Ryan Larson shows you the essential scales and chord progressions you'll need to know to play Bossa Nova songs, taking you through a piece measure by measure, and offering tips on the distinctive plucking technique used by Bossa Nova guitarists.

It’s called Urophagia—the art of consuming urine. There could be any number of reasons for having the desire to drink your own urine (or somebody else’s). There’s the so-called term “urine therapy,” which uses human urine as an alternative medicine. In urine therapy, or uropathy, it’s used therapeutically for various health, healing, and cosmetic purposes. There’s also those people who drink urine as sexual stimulation, where they want to share every part of each other. And then there’s the o...

In this organization tips video clip series, our expert will demonstrate the essential steps necessary for beginning to organize your home. Assessing the situation, cleaning, ordering and discarding or consolidating products and belongings are all a big part of the organizational process, and you will see demonstrations of these techniques for the front entryway, living room, home office and kitchen. Also get some extensive tips on how to organize your closets. Use these video guidelines to g...

In this series of instructional video clips you'll learn how to build the perfect tool kit for your home improvement needs. Expert Carolyn Saylors offers tips on choosing the right type of box to store your tools in, and shows you step-by step what tools are absolutely necessary to keep in your home. She explains the various types of screwdrivers, including torque and all-in-one models, the most commonly used types of pliers, wrenches and ratchet kits, drill bits, small saws, levels and hamme...

The updated Messages app for iPhone, iPad, and Mac has some really cool new features, but the one you may end up using the most is something you're already familiar with: Tapbacks. With iOS 18, iPadOS 18, and macOS Sequoia 15, Tapbacks are improved and contain even more reactions to choose from.

Unless you have unlimited cellular data, you probably connect your iPhone to every Wi-Fi network you come across. It could be a local coffee shop, public library, or just a friend's place. Wherever it is, you'll need to ask for the access point's password if it's a secured network, and that can be a hassle if the place is busy or the owner forgets the credentials. Luckily, Apple has a solution for this problem.

If you lose your AirPods, AirPods Pro, or AirPods Max, you can turn to Find My to locate them. But sometimes, things don't go according to plan, and many things can go wrong. For example:

Smartphones are now indispensable when traveling. Domestic and overseas travel alike require food, navigation, translation, and so much more to make work or vacation successful. Gone are the days of lugging multiple tourist books around with you everywhere you go — you need to let your smartphone handle the dirty work.

How would you like to make your own lip balm/chapstick? It's easy to do with a few simple products. One way to do it includes beeswax, coconut oil, olive oil, raw honey, peppermint oil (for scent), and mineral powders (for colors). The tubes to put the lip balm in are available online if you want to use those instead of another container.

A little-known setting on your iPhone gives you the power to change the color of certain contact names and email addresses when drafting an email. Customizing the color works well for visually separating contacts at a glance, and it can even help you from sending an email to the wrong person.

The beginning of autumn has delivered a number of new augmented reality developments, and we're on top of it.

One app is continuing to make a name for itself as the go-to platform for celebrity art that transcends canvas and paint and moves in augmented reality.

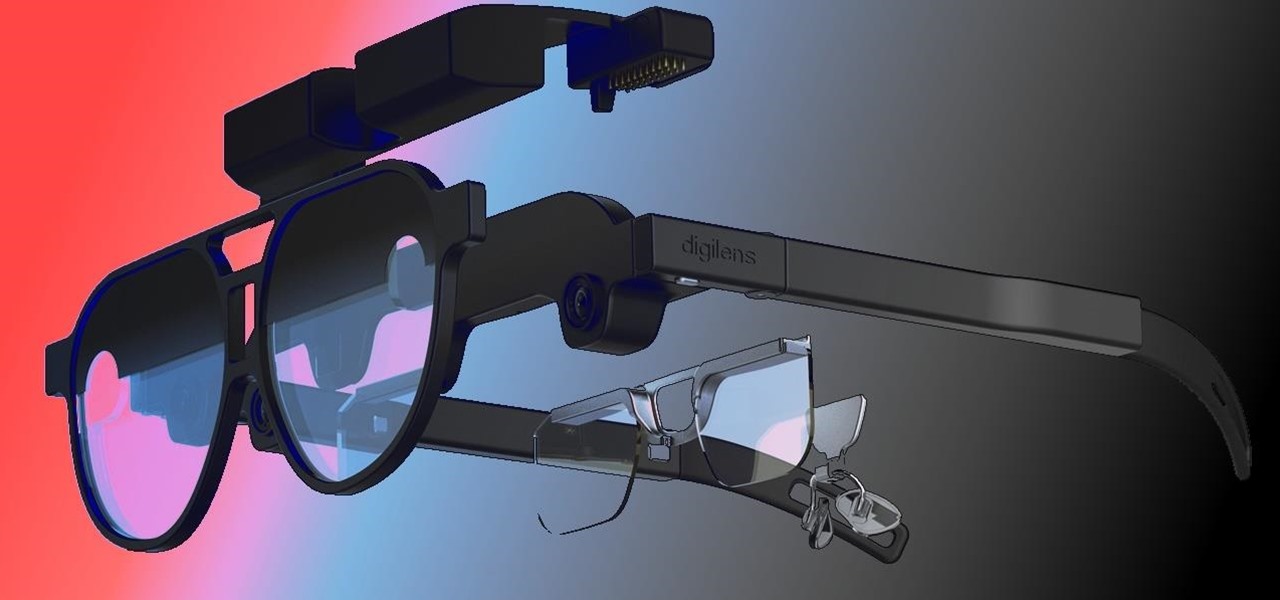
When it comes to the future of AR smartglasses, DigiLens has one word for you. Just one word. Are you listening? Plastics.

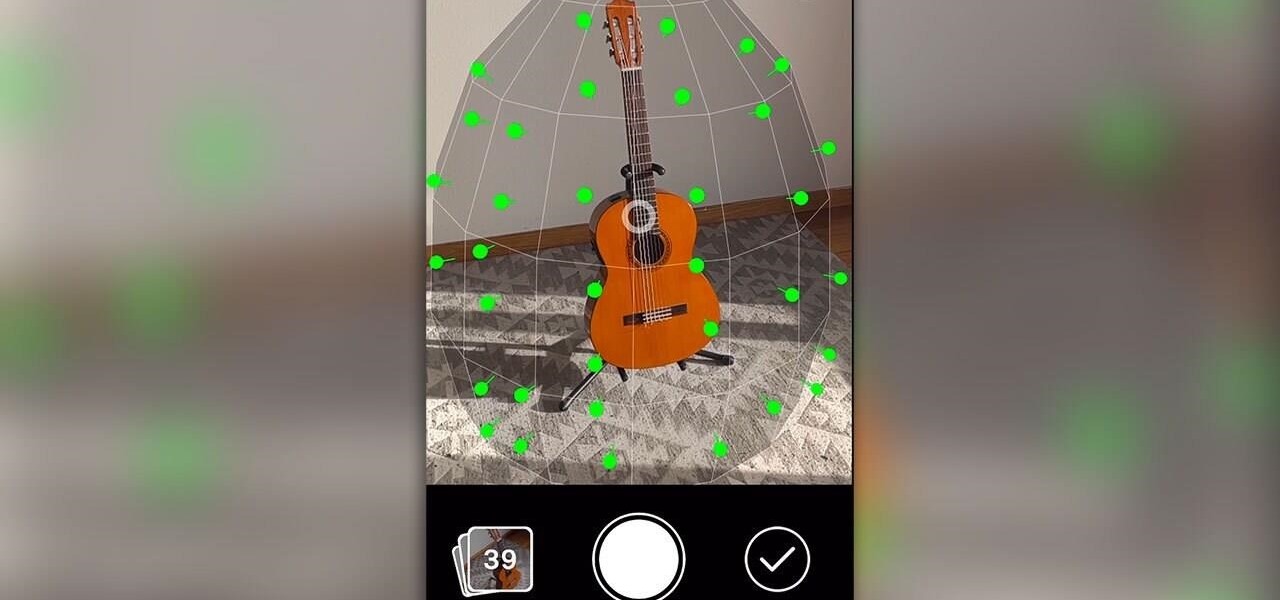
One of the more exciting augmented reality announcements Apple made during its WWDC keynote on Monday came in the form of Object Capture, a new 3D scanning feature coming to macOS Monterey.

The COVID-19 pandemic forced many businesses into remote work models, whether they were ready or not, making Zoom a household (or home office) name for its video conferencing service.

One of the best reasons to enter Apple's ecosystem is iMessage, where you can communicate more securely with other Apple users and send and receive chats across all of your connected iPhone, iPad, iPod touch, and Mac devices. While those blue bubble conversations sync across devices, the green bubbles — SMS and MMS texts — remain on your iPhone alone unless you change a setting manually.

It's Black Friday time, and in 2020, that means a lot of online deals to make up for more stores closing on Thanksgiving, as well as everyone avoiding in-person shopping because of the coronavirus. But while you may wish to grab a better 65-inch 4K TV, the new PlayStation 5, or some hacker hardware on sale, Black Friday is also the best time to invest in your programming and cybersecurity education.

If you have a group of iPhone users to manage, whether for work assignments, planning a trip, or organizing an event, Reminders might just be your new best friend. With iOS 14, the app now lets you assign reminders to contacts, so everyone knows what they're supposed to be working on.

With over two billion websites floating around cyberspace — only 400 million are estimated to be active — you need every tool you can get to stand out. Great design, fonts that capture attention, and SEO placement are all necessary ingredients to success.

Penetration testing, or pentesting, is the process of probing a network or system by simulating an attack, which is used to find vulnerabilities that could be exploited by a malicious actor. The main goal of a pentest is to identify security holes and weaknesses so that the organization being tested can fix any potential issues. In a professional penetration test, there are six phases you should know.

The Pi-hole project is a popular DNS-level ad blocker, but it can be much more than that. Its DNS-level filtering can also be used as a firewall of sorts to prevent malicious websites from resolving, as well as to keep privacy-killing trackers such as Google Analytics from ever loading in the browser. Let's take a look at setting a Pi-hole up and customizing a blacklist to suit your needs.

Getting files from an Android device to a Mac or iOS device is not always easy or convenient, and the same goes for transferring content from a Mac or iOS device to an Android device. But we're here to tell you there is a better way than using USB cables, email, and cloud storage, and it gives you the look and feel of AirDrop.

For a hacker, there are a lot of advantages to creating a fake network. One advantage forces nearby devices to use their real MAC address if you happen upon a network that's stored in their preferred network list.

If you're using the default Samsung Keyboard on a Samsung Galaxy smartphone or Gboard on a Google Pixel or any other Android device, here's a cool trick you should know about.

If your new 2020 iPhone SE is frozen, unresponsive, or won't load the system, and a standard power down and up procedure didn't work, there are few more things you can try. Force-restarting the device may do the trick, recovery mode is a last-ditch option, and DFU mode is your fail-safe.

It feels like just yesterday Apple unveiled iOS 13 to the world, introducing game-changing features like system-wide dark mode and enhanced editing tools in Photos. But WWDC 2020 is rapidly approaching, which means iOS 14 is as well. As it turns out, we don't need to wait for an official announcement to get an idea of what new features and changes are coming to iPhone this year.

A macOS computer can reveal a lot of information about the owner, including which Wi-Fi network they have permission to access. With an Arduino-based attack, we'll use a five-dollar setup to inject a rogue Wi-Fi network and steal the list of trusted Wi-Fi networks, allowing us to see where the computer has been.

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

When you think about your Apple Watch, what comes to mind? Fitness tracking? Replying to texts? There are a lot of things Apple Watch is good for, but social media doesn't appear to be one of them based on the App Store. If that's your perception, however, it's time for a reality check because you can start browsing Twitter and Reddit on your Apple Watch right now.

Arduino is a language that's easy to learn and supported on many incredibly low-cost devices, two of which are the $2 Digispark and a $3 ESP8266-based board. We can program these devices in Arduino to hijack the Wi-Fi data connection of any unlocked macOS computer in seconds, and we can even have it send data from the target device to our low-cost evil access point.

We all want to be healthy, but in practice, it can be tricky, especially from the fitness angle. Our lives seem busier and busier, which makes hitting the gym quite the challenge. What if we told you there was a real way to work on your fitness in the comfort of your own home — in just seven minutes a day? All you need is a chair, a wall, and a 7-minute workout app.

One of my favorite perks of this job is the opportunity to try out all the big flagship phones each year. Whether it's rating their suitability for a particular use-case or just entering their specs into our comparison tool, we have to get our hands on all major phones released in the US. We pride ourselves on being fair in our reviews and roundups, but that doesn't mean we don't have preferences.

In iOS 13, Apple added an important new feature to its HomeKit smart home ecosystem called HomeKit Secure Video. With it, you have a secure, private way to store and access recordings from your smart home IoT cameras.

So you want to know what that person who is always on their phone is up to? If you're on the same Wi-Fi network, it's as simple as opening Wireshark and configuring a few settings. We'll use the tool to decrypt WPA2 network traffic so we can spy on which applications a phone is running in real time.