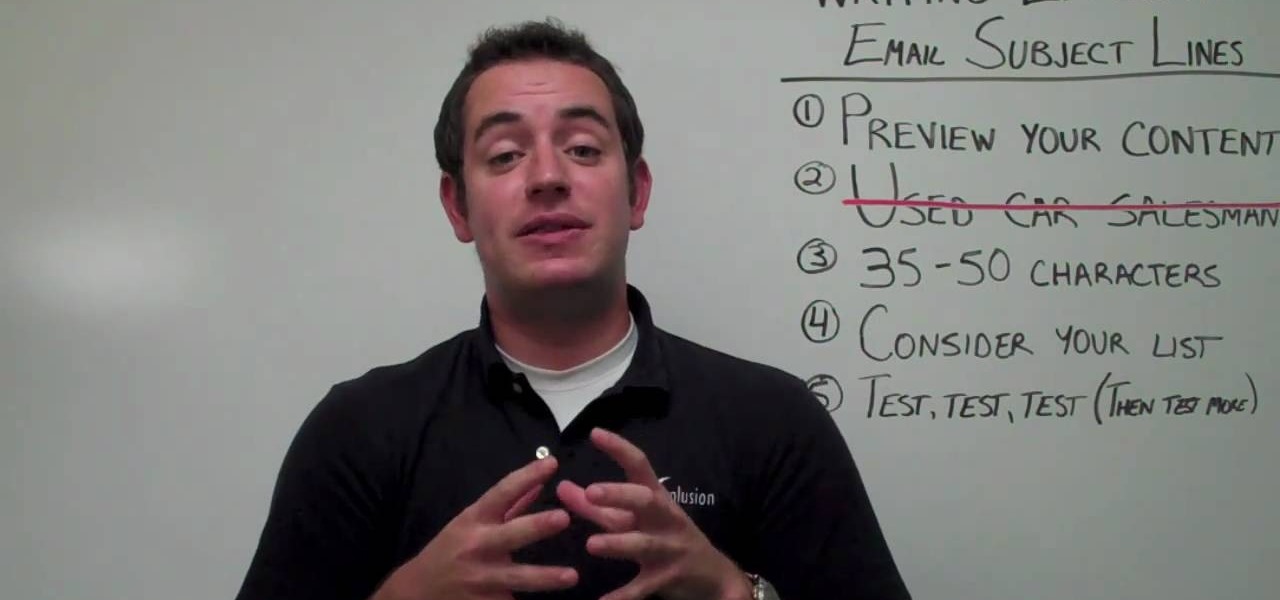
No matter what kind of business you have, small or big, online-based or not, when you're dealing with email marketing, the number one things your targets will see is the subject line, and if your subject line looks spammy or uninteresting, it's not going to help you one bit.

In this tutorial, we learn how to use height change in tango. This will combine many elements of tango to change height deliberately for function and style. You do not want to change your weight and height without knowing it, because it can change how you dance and make it look completely different. Pay attention to your body and how your feet are placed on the ground. If your body weight is shifted too much to one foot it can change how you are dancing and the height of your overall self. Us...

Vault Boy has been around for a long time now, and appeared in the few but proud Fallout games as their mascot and skill-demonstrator. Pay homage to this plucky little guy by creating an XBox 360 Avatar in his likeness using the materials below and following the steps in the video. He looks a little skinny to me, but you can change it if you want right?

As a mechanic, you can't get paid until you fix it, and you can't fix it until you diagnose it, which means a quick diagnosis means a quick fix which means a quick payout. If life was always this easy! This automotive video will show you how to troubleshoot and diagnose a 1999 Mercury Village, 3.3L, with 150,000 miles on it. The chief complaint is the CEL (check engine light) comes on and it runs like it has a misfire. It feels like a steady consistent misfire, which is code P0304 (Cylinder #...

No more do you have to buy additional equipment just to send a quick fax out. And no more going to the local copy store to pay for faxes. Windows 7 has a great feature built right in called Windows Fax and Scan. See how it works.

In our opinion, blowouts at salons are WAY overpriced. A few spritzes of heat protectant, a few good twirls of the blowdryer, and you're done. Well, after you pay $50.

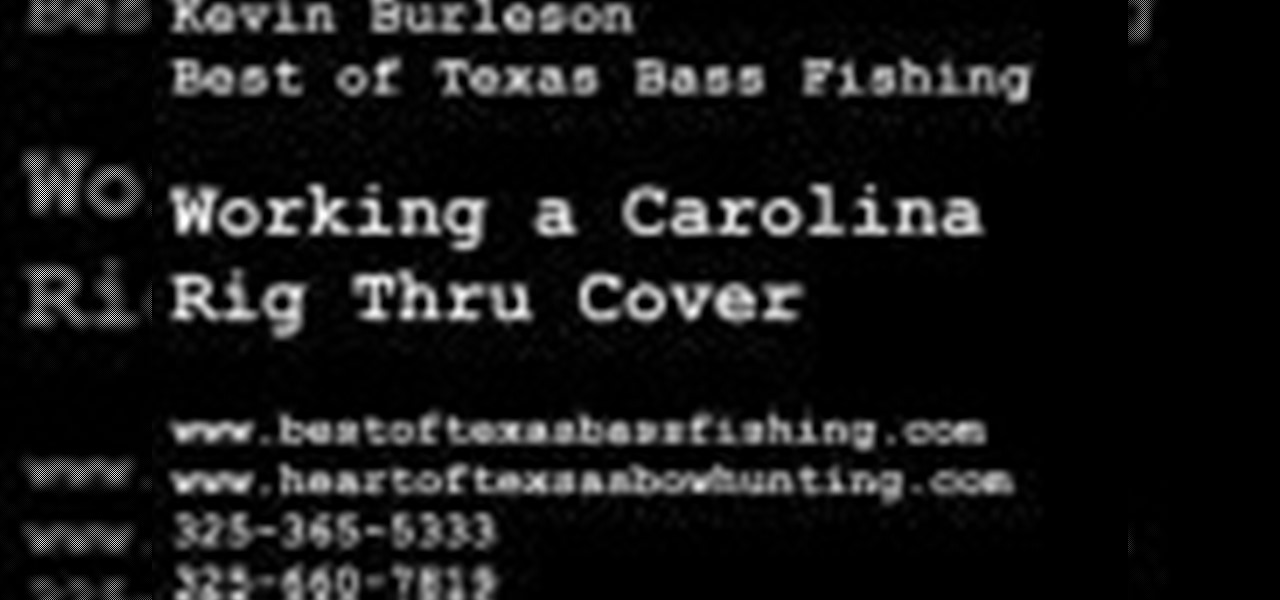
When you're out bass fishing, things can get a little difficult. Not only do you have to deal with getting the right equipment ready to go and catch fish, but you also have to be wary of your surroundings. In this tutorial, you'll be finding out how to work a Carolina rig through some tough cover when out fishing. Not being able to do so can result in a snapped line or loss of bait or the fish. So pay attention and good luck!

Baby animals are some of the cutest things in the whole world. They can sometimes be even cuter than human babies! One of the most adorable set of baby animals would be chicks and baby ducklings. There's something about all the chirping sounds that make them so hard to leave. In this video tutorial, you'll find out how to build a simple brooder box using easy to get material. So sit back, pay attention, and enjoy!

Let's be honest. Who actually pays for their music these days? Take your internet piracy to the next level and become a certified bucaneer by watching this video on how to get free applications on your iPhone and iPod Touch.

In this Beauty & Style video tutorial you will learn how to make your hair grow faster with castor oil. Castor oil practically doubles you hair growth, though not many people use it. When you take it out from the container, it is like hard cream. Take it on your palm and rub your palms until it turns oily and apply it on the scalp and the bottom end of the hair and leave it for sometime. It is a bit smelly. Therefore, you have to wash it off with shampoo and apply conditioner. The next day yo...

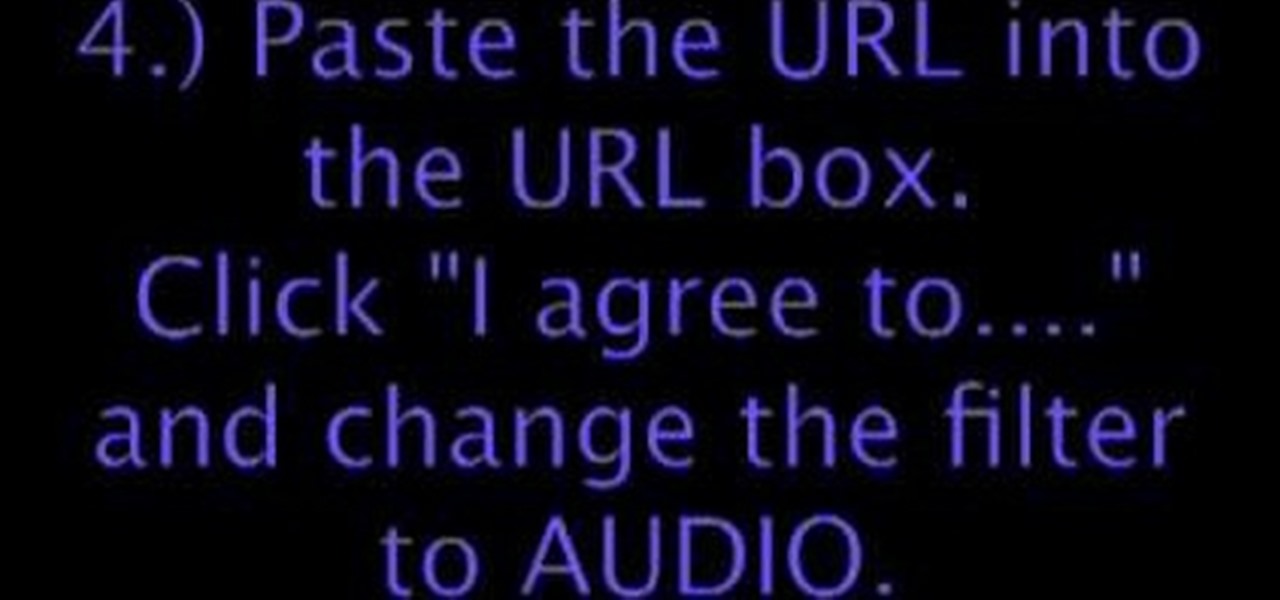
This how-to video shows you how to download music from MySpace in good quality. This method is one hundred percent free and legal as long as you don't share the files with anybody other than yourself. The video shows viewers everything from accessing the artists music page of which you would like to download songs from, to clicking the get files button and getting your music. If you use this method of downloading music you will bypass paying a dollar per song and still keep things legal.

Kevin Gianni of the Renegade Health Show interviews vegan bodybuilder Robert Cheeke. Since a vegan diet doesn't consist of any dairy products or meat, vegans can often find themselves losing weight. Robert Cheeke shares his secrets on how he gained weight while following a vegan diet and how he gained muscle mass. Robert says that the toughest challenge is putting the time and effort into gaining weight by eating the right things at the right times and being consistent. Hard work will pay off.

Sorority Life hacks, cheats, glitches. How to hack Sorority Life. Watch this video tutorial to learn how to hack unlimited invites in Sorority Girls (08/16/09).

Feeling calmer and happier is at the tip of your nose: It’s just a matter of using your common scents. Check out this Howcast video tutorial on how to use Aromatherapy's Essential Oils to improve your life.

If you call yourself a hobbyist or a kid at heart, you know that remote-controlled vehicles are more than just fun. If you're a serious R/C man, you'll know all about doing everything to your model truck or car, like fixing wheels, vamping the pinion gears, waterproofing, troubleshooting, electronic diagnostics, setting up, programming and finally... racing. As much as you know about these remote-controlled vehicles, it will never be enough, you'll always be looking for more...

Park Skateboarding: Show Off Your Skills The first skateparks appeared in the 1970s, and nowadays, they're the epicenter of the skateboarding world, a place to see and be seen. That being the case, you don't want to show up to the park without your "A" game. Let our trick guide get you up to speed. Watch this video tutorial to see how to do skateboard figure eights at a skatepark.

Window and portable air conditioners use a lot of power to do their work. Make sure you're getting what you pay for by cleaning your air conditioner out periodically. The cleaning costs are negligible and can save you a lot of money. In this two-part tutorial series, you'll learn how to make your air conditioning units run as they should. Remember to be careful; air conditioners can be heavy. Get help if you need it and, of course, unplug the air conditioner before doing anything seen in this...

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

The 2020 iPhone SE had been through the rumor mill for a long time, but Apple finally unveiled the second-generation iPhone SE on Wednesday, April 15. While it doesn't sport the 4-inch design of the original SE, it combines a small form-factor with modern specs. The big question, of course, is when and how you can get your hands on one.

They're finally here. Apple revealed the brand new iPhone 11, 11 Pro, and 11 Pro Max on Sept. 10, and despite the questionable names, these are the best iPhone models money can buy. If you're looking to get your hands on one of these devices as soon as possible, there are few important dates you need to know.

Phone specs get better and better each year, and multiplayer mobile games are right there with them. Instead of playing solo, jump into some real-time gameplay with co-op and player vs. player modes, and battle friends, family, and strangers from around the world. But which multiplayer games are worth your time on Android or iOS?

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

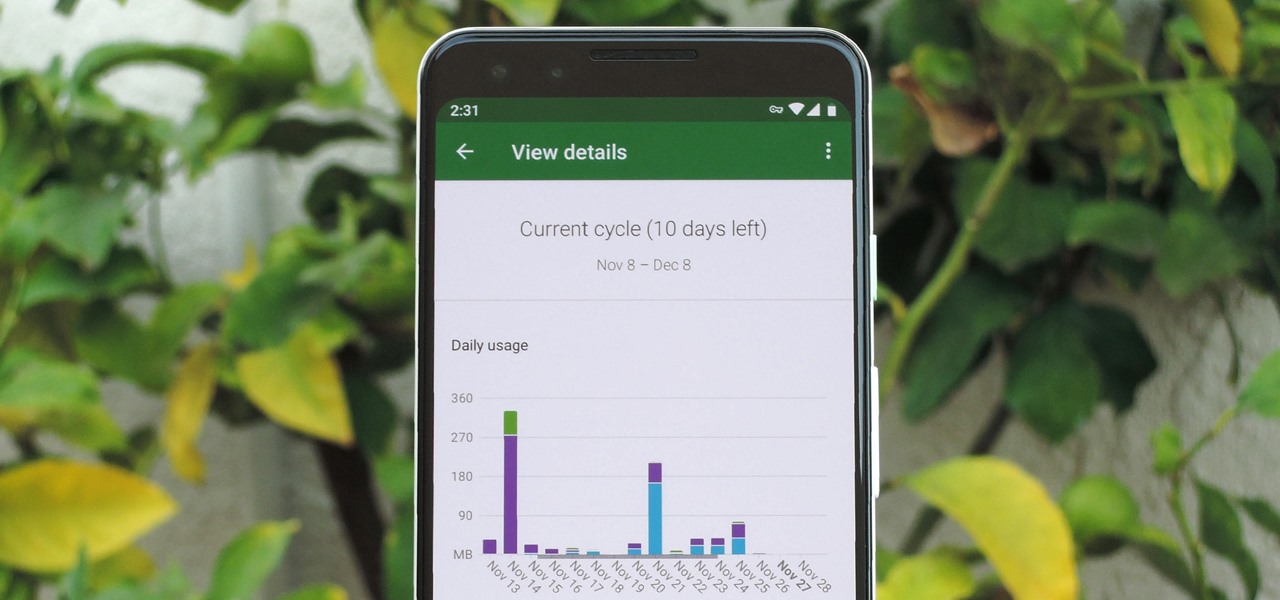
In case you hadn't heard, Google is now a legit cell service provider. Google Fi has its pluses and minuses, but the biggest upside is in the pricing. Depending on how much data you typically use, there's a good chance you could save a lot of money without sacrificing coverage by switching to Fi.

The first few minutes after gaining access to a MacBook are critical — but where do we begin? Using tools built into macOS, we can develop an in-depth understanding of running background processes, detect antivirus software, locate sensitive files, and fingerprint other devices on the network. All of this can be done without installing additional software or modifying any files.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.

If you're looking for a new Reddit client on your iPhone, look no further than Apollo. Launched with iOS in mind, Apollo is a free app that offers an exceptional Reddit experience, but some of its excellent features — as well as some necessary ones — are hidden behind its "Pro" paywall. Are these extras worth your money?

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

One of the best things about Android is the ability to customize your phone to your liking. From changing the layout of icons to finding the perfect wallpaper to reflect your current mood, there's a wide range of tools to make your phone yours.

Everything from disposed of drugs to hormones and disease-causing bacteria — anything that is rinsed or flushed down the drain — can contaminate wastewater.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

Welcome to a tutorial on crypting technology. In this article, we will be discussing types of crypters, how they work and why they work. After defining these, we will then make our own basic crypter using the function I gave to you as a task to complete by yourself in the previous tutorial.

Welcome to an introduction on writing basic malware, an optional sub-series in which I expose you to malware and its technologies. This is written for those who wish to seek a beginning in malware analysis or enlightenment on the subject. We will be justifying the writing and covering types of malware.

Continuing this series, I am now moving on to the section, 'Anonymous'. Hope you are looking forward to read this.

CEO's of IT companies doesn't know this because they are not a hacker. Only a true hacker can become a successful Security head officer.

Part 1: What is Popcorn Time? Part 2: What is a torrent?

It seems like every day now that we see a new headline on a cyber security breach. These headlines usually involve millions of records being stolen from some large financial institution or retailer. What doesn't reach the headlines are the many individual breaches that happen millions of times a day, all over the world.

Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.