If you have read any of my previous articles or viewed the many videos I have published, it's quite clear that I appreciate a good rocket or fiery projectile. The following video will certainly not lessen that reputation.

It's a real challenge to create exploding targets that can be set off by low velocity projectiles, yet remain safe to handle without risk of ignition during construction.

Prepaid phones are becoming more and more popular, and tons of people can see the benefits of switching now that some companies are offering prepaid services that are on par with the big players. For a lot of folks, the only thing keeping them from switching is the huge early termination fees that service providers charge to break a contract early.

When was the last time you bought a CD? Most of us listen to music through a number of digital channels—MP3s, Internet streaming services like Pandora and Spotify, and satellite radio, to name just a few.

While putting content and information online gets easier every day, it seems like getting it back is only getting harder. In a lot of cases (we're looking at you, Facebook), once you upload something, it's forever in the hands of someone else. That's where The Data Liberation Front comes in. Believe it or not, The Data Liberation Front is a team of Google engineers who work to make it easier for users to take their stuff back whenever they feel like it.
As if iOS 6 wasn't under enough scrutiny, a new issue has surfaced regarding the App Store for iOS 6 on the iPhone and iPad. According to users, the application store is very sluggish and doesn't load properly. Below is a video of just how slow the application store is.

Dropbox announced Tuesday that a recent security breach compromised a list that included the email addresses of certain Dropbox users. To avoid future complications, the service announced that it would be implementing two-factor authentication, and even more useful, a security page that lets you monitor all activity on your account. In light of this and other recent web security threats, you might also want to know that services like Gmail, Facebook, and Yahoo! Mail have similar pages where y...

Check out this three-part series on how to play Super Smash Bros. Melee (advanced). This is not a beginning tutorial for all you newbie gamers, it's more detailed and advanced for pros, or semi-pros.

To properly set a table for an informal four course dinner, keep in mind that a soup course, a salad course, an entree and a desert will be served. First, add the service plate or charger to the table. Place it directly in front of the guest two inches from the table. It will serve as the under plate before the entree arrives. Use exactly the amount of silverware needed to accommodate the meal. For this meal, you will need a soup spoon, a salad fork, a salad knife, a dinner fork, a dinner kni...

How would you like to be able to watch all of the movies and television shows available on the Netflix watch instantly service on your HD2 Android phone? Check out this video to learn how to download the Netflix app.

Check out this basic back-to-school look that's also great for daily work and church services. It's a neutral makeup look with very little shimmer. It only takes about 5 minutes to create these beautiful eyes! Watch and learn how to apply these eyeshadows and cosmetics.

Want to receive daily, weekly or monthly updates on a subject of your choice? With Google Alerts, it's easy! So easy, in fact, that this home computing how-to from the folks at Easily can present a complete (and somewhat talky) overview of the process in just under five minutes' time. For the specifics, and to get started setting up and using Google Alerts yourself, just watch this handy how-to.

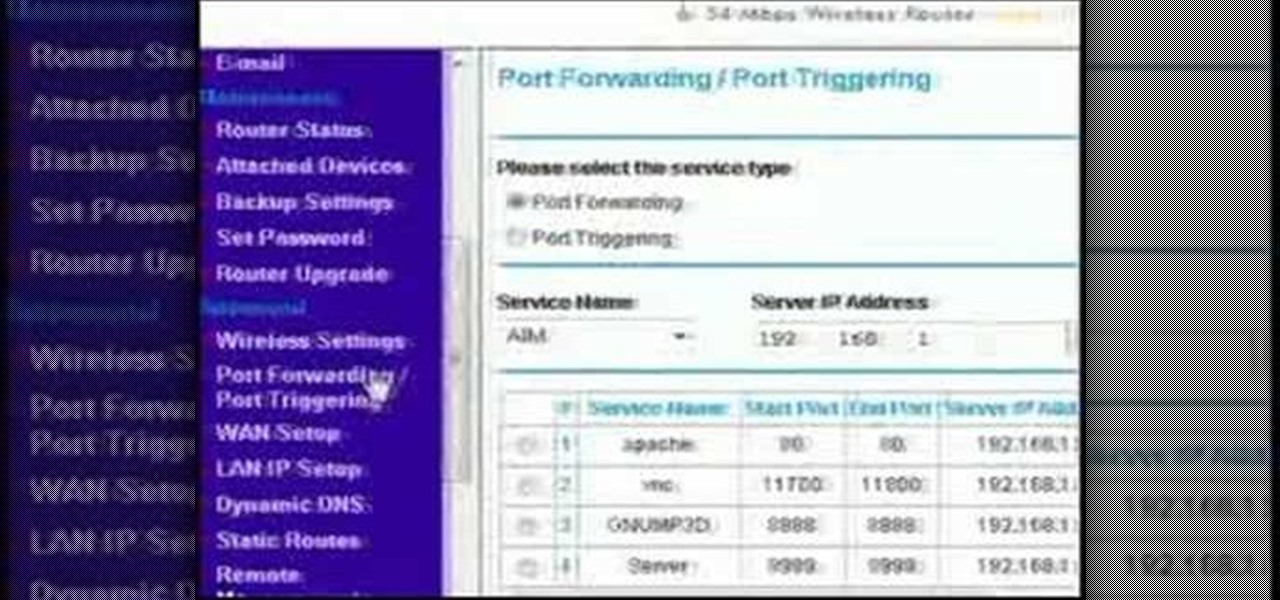
This video discusses how to bypass your router to access your server. In the search window type in CMD to open up a command prompt. Then type in ipconfig to bring up the ip configuration. You want to look for the ip address for the default gateway and the one for your computer. They should both start with 192.168. Once you find them open up internet explorer and type in the ip address for your default gateway and it should then prompt you for a user name and password. Log in and look for a po...

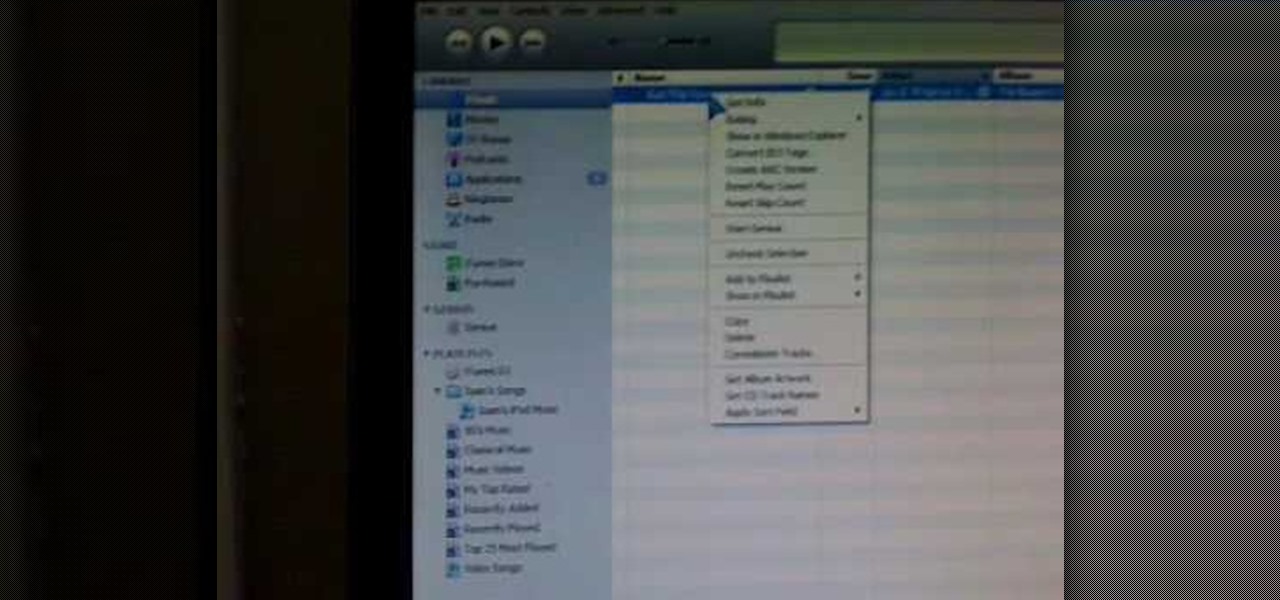
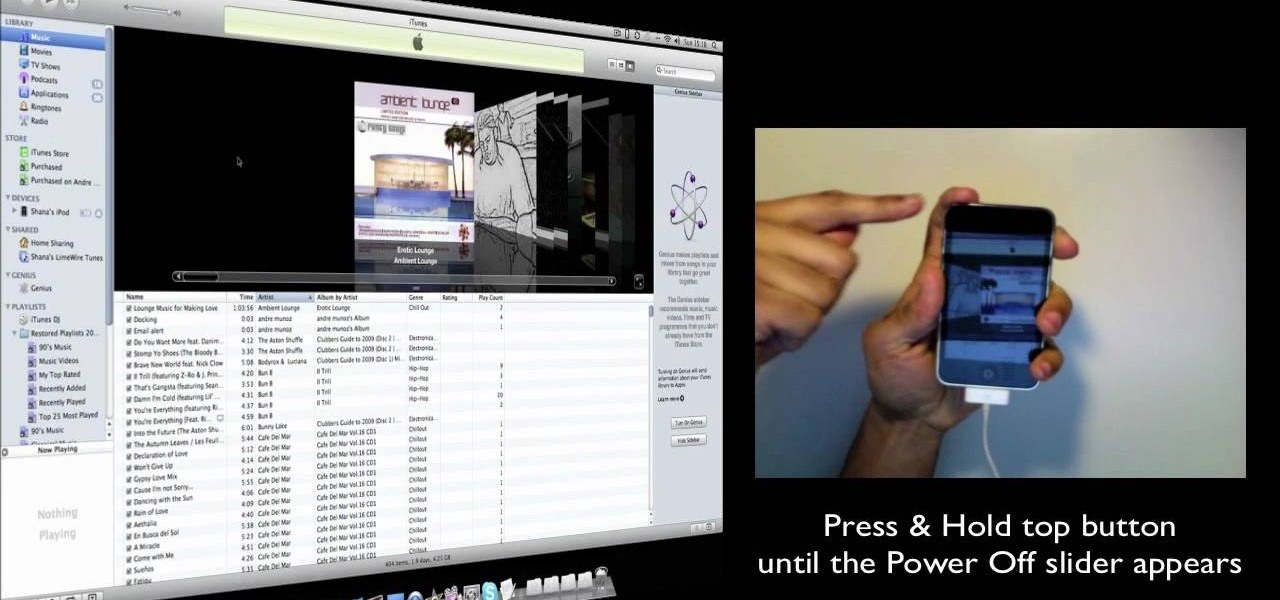
This tutorial will show you a super simple way to get free ringtones for your iPhone. This method will let you bypass iTunes's expensive ringtone service and create your own - anytime, from any song and for free!

Your IP address is what identifies your personal computer while you are online. You may want to change your IP address for privacy, to bypass website settings, to download, or for various other reasons. This tutorial will take you through the steps you need to start surfing more anonymously.

This is an Apple iPhone video tutorial that will show you how to unlock an Apple iPhone 2G or 3G for use with another mobile phone service provider other that AT&T. If you are using a Macintosh computer, you can unlock both the 2G and the 3G phones. If you're using a PC, then you can only unlock the 3G iPhone.

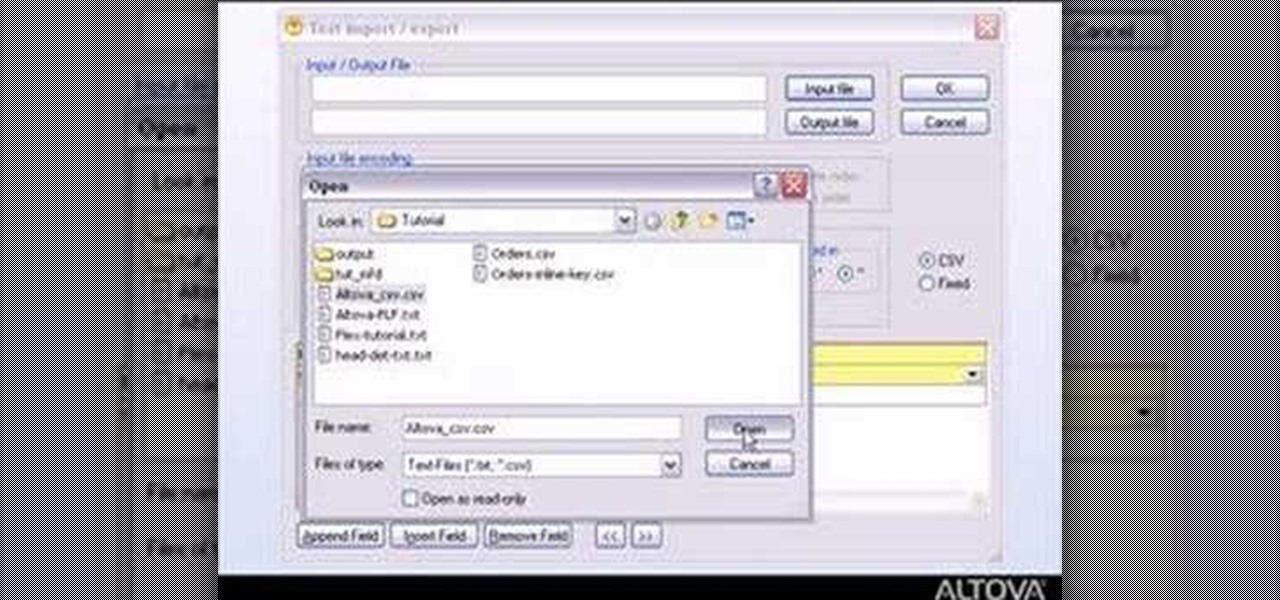
MapForce supports flat files as the source and/or target of any mapping involving XML, database, EDI, web services or other flat file data. In this how-to, you'll find instructions for mapping data from arbitrary text files (such as log files, CSV, fixed-width, and other legacy data sources) to databases and XML files.

The Prada cell phone (the LG KE850) is a unique, sophisticated and elegant mobile phone with the first complete advanced touch interface.

Watch this how-to video to learn how to get 30 days of Xbox Live Gold for free just by pretending you don't want it. Xbox Live Gold is normally a subscription service, but you can get 30 days of it for free by following the tips in this how-to video.

In this how to video you can learn to create a punk, goth, emo red Avril Lavigne inspired eyeshadow look. This makeup tutorial uses the following products:

An installer shows some tips to help remove your trialer hub so it can be serviced and then reinstall it so your wheel can be remounted.

Just some suggestions and roughly the way I handle calls. There is more than one way to do this and every call is different. Enjoy!

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

We've shared a capture-the-flag game for grabbing handshakes and cracking passwords for Wi-Fi, and there are some upcoming CTF games we plan on sharing for other Wi-Fi hacks and even a dead-drop game. While security-minded activities and war games are excellent ways to improve your hacking skills, coding a real video game is also an excellent exercise for improving your programming abilities.

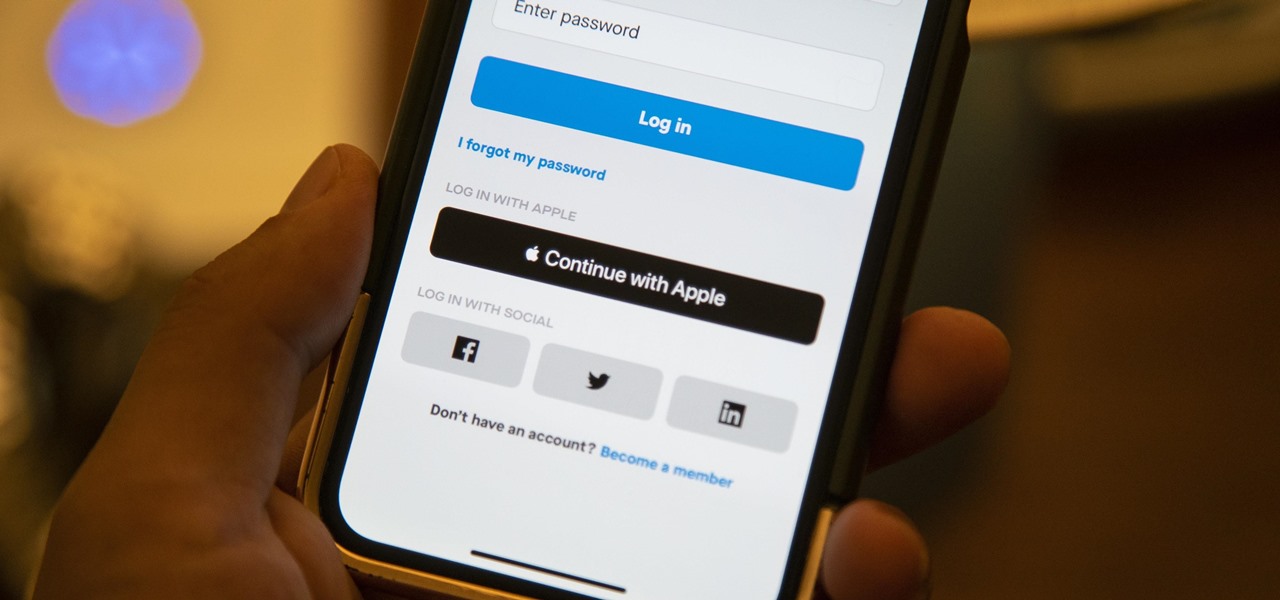
We've all seen the login pages that allow you to log in to third-party accounts using your credentials from Facebook, Google, or Twitter. It saves you the trouble of creating another account and remembering more passwords — but it can also become a privacy and security issue, which is why Apple created the "Sign in with Apple" feature for iOS 13.

On April 26, 2019, Sinemia posted a note on its website stating it has ceased all operations in the United States. It's not known if it continues to work in other countries or if US users will be getting any refunds, particularly, for annual subscribers.

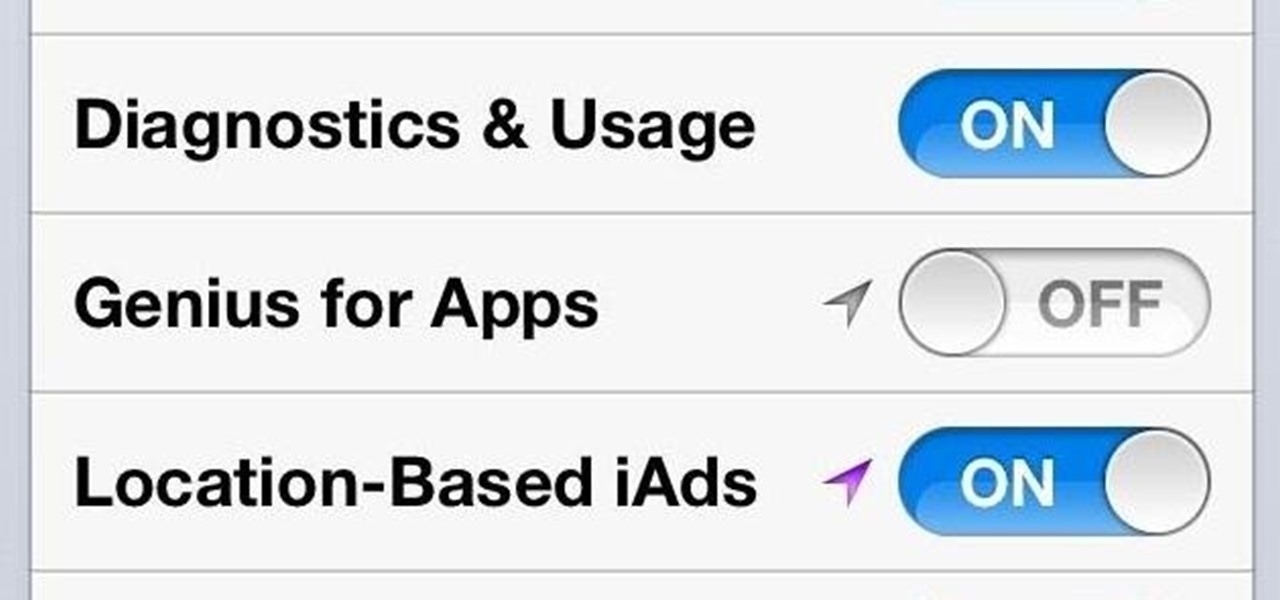
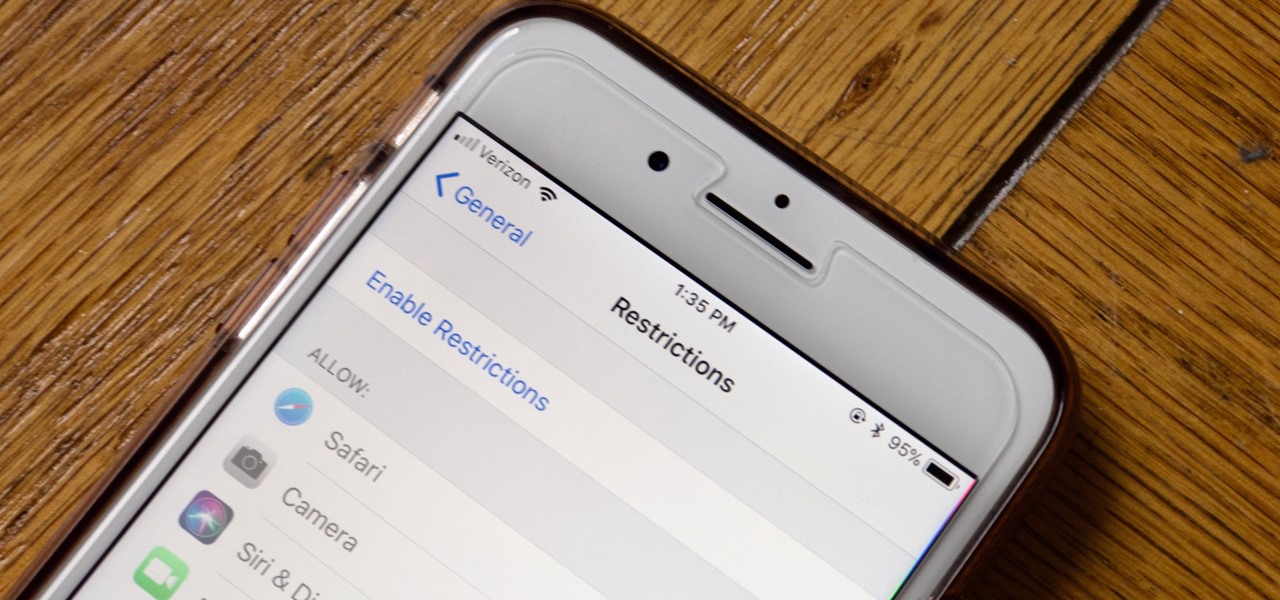
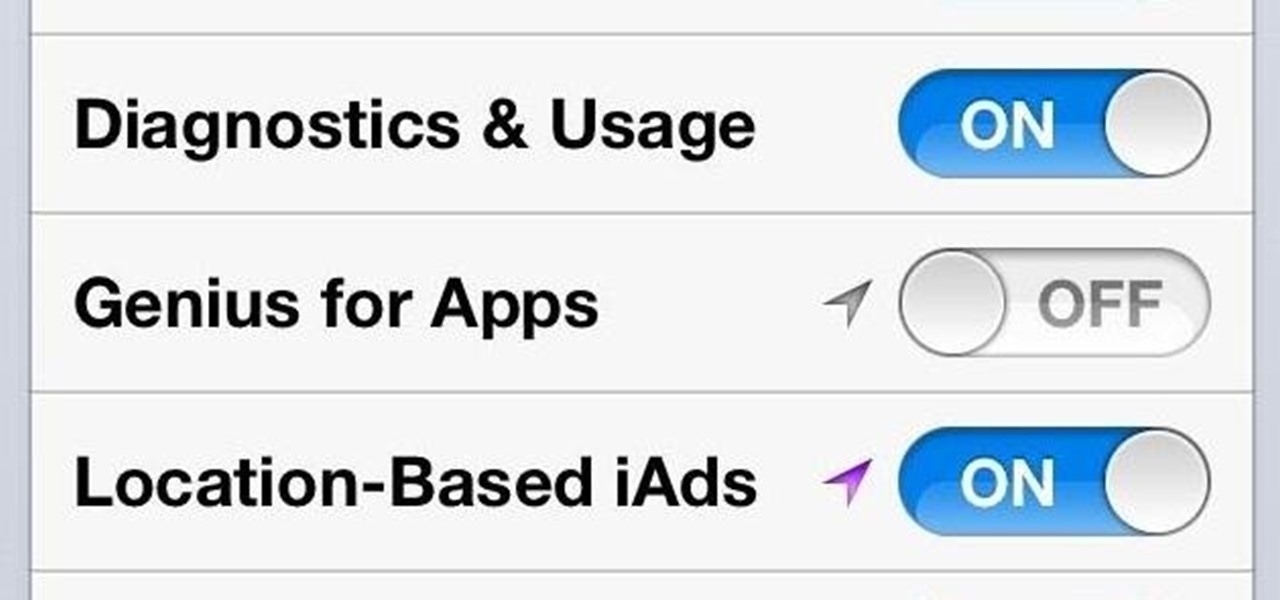
Apple has tools built into iOS to help parents monitor the iPhone habits of their children. However, those same tools can be used by everyday iPhone owners to both hide apps they don't care about, as well as restrict features they don't need or that infringe on privacy. Whether you fit into one category or the other, all iPhone users can benefit from the "Restrictions" feature.

Configuring onion services for the first time can be tricky. A surprising number of system administrators make seemingly trivial mistakes that ultimately lead to catastrophic cases of de-anonymizing supposedly anonymous sites on the dark web. OnionScan is a tool designed to identify common misconfigurations in onion services and aid us in understanding how to fix them.

The telecommunications industry has come a long way since Ma Bell opened the first telephone exchange in the late 1800s. With the advent of fiber optics and wireless broadband technology, we no longer have a need for a dedicated phone connection, as today's data networks can carry much more than a simple voice conversation.

Welcome back, my novice hackers! Reconnaissance is one of the most important preparatory steps to hacking. As I have emphasized many times before here on Null Byte, you must know the operating system, the ports, the services, the applications, and sometimes even the language of the target to be effective. If you haven't taken the time to gather this info, then you are likely wasting your time.

Welcome back, my novice hackers! There are SOOOO many ways to hack a system or network, which means you need to think creatively in order to be successful.

'The Deep Roads Expedition' is the exciting conclusion of Act 1 of Dragon Age 2, and this excellent walkthrough of it runs to nine separate videos. Worry not, friends, it in very enjoyable and well-made viewing that will teach you everything you could ever possibly want to know about this quest. It is a strategy guide among strategy guides.

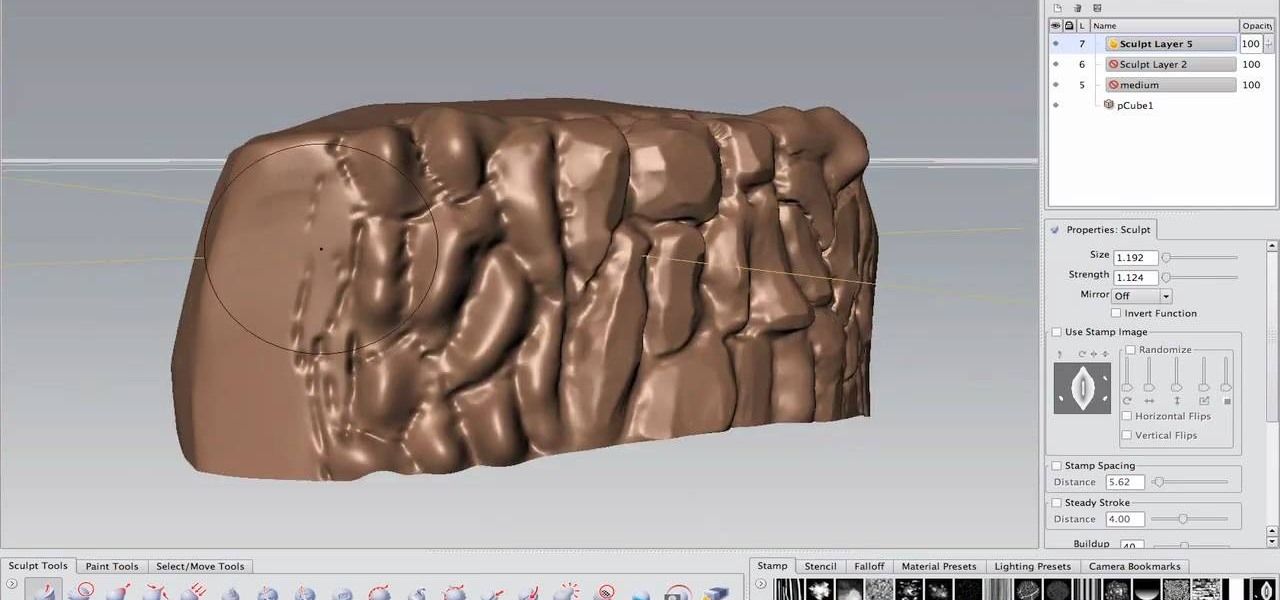
If you're an Autodesk Maya user and you're looking to create rocks, boulders or rock walls, check out this excellent 7 part tutorial and learn how it's done. Maya is a massive 3D creation tool with so many aspects it's really mind blowing. This tutorial will help you improve your skills for your game building or just for you own art.

Unlocking the iPhone can save you a ton of money and irritation by getting you off AT&T and onto a better service provider. One way to do that is flashing the baseband to one that works on the iPad, and this video will show you how to do using Redsn0w that, provided you're working from a iOS 4.2.1 / 4.1 equipped iPhone 3G / 3GS on baseband 5.14 or 5.15 (about to be 6.15 when you're done).

Combination locks are a major part of life for people High School, the Armed Services, and enough other places to make this video very useful to a lot of people. It will show you how to open any twisting combination lock (like a Masterlock) with using math or any other sophisticated skills or tools. All you need is a sharp knife and your fingers. Now you won't have to wonder whether Person X has your picture up in their locker or not anymore.

Apple really ate some mud in the media over the iPhone 4's blatant antenna problems, but they're finally trying to make good by offering free problem-solving bumper cases to all of their iPhone 4 customers. Keeping true to their "There's an App for that" slogan, they've made an App that allows you to order the free bumper case that they're promised you right from you iPhone. If you have service that is! This video will show you how to use it and get what you deserve from Apple.

1. Type in WWW.sendthisfile.com in the web toolbar and press enter 2. Click on Register found on the top right side

Now more than ever, people everywhere are suffering from bad credit. Credit is important. You need it to take out loans, buy a house, rent an apartment, get a car, almost anything! Check out this two part video, presented by Daniel Medina from United Credit Education Services, and listen along as he offers you tips on how to improve your credit - even in a recession. This helpful and informative video can start you on the right track to financial stability, no matter what the circumstances.

This video illustrates the method of Downgrading the iPhone 3Gs firmware from version 3.1.3 to version 3.1.2. The process is composed of the following steps -Step 1Download the iPhone 3Gs firmware version 3.1.2 from the internet. You can find this on apple's official site or you can get this from a customer service center.Step 2Upload the firmware files in the root of your iPhone's internal phone memory. Create a folder named "firmware v312" and add the firmware files in it.Step 3Access this ...

Link shortening is the process of cleaning up the URL link which is long and converting it into a short URL. You can use bit.ly to do link shortening. Using bit.ly you can not only shorten the link but also track the users who are using those links. To use this service go to the http://www.bit.ly website. There in the home page you are provided with a text box. Enter your long link in the text box and submit it. Now the website converts the long URL and provides you with a short link which ca...