The popular RPG Death Road to Canada has finally arrived for the iPhone and iPad, and its impact is immediate. It's fast becoming a top contender for mobile video game of 2017, and it's very easy to see why. The game blends decision making and good old zombie bashing to create a refreshingly unique experience. Add to that the motley cast of survivors that you can recruit, plus the secrets waiting to be discovered, and this game is sure to suck up countless hours of your time.

In a race to make self-driven cars mainstream, Intel announced today that they've bought Israeli microchip technology company Mobileye for $15.3 billion, setting the stage for Intel to dominate a large portion of the driverless market.

Over a billion people use WhatsApp, which makes it the most popular standalone messaging service out there. But if you're one of the many people whose group of friends relies on WhatsApp for all communication, chances are, you have several years-long messaging threads with all sorts of random pictures and GIFs cluttering up the place.
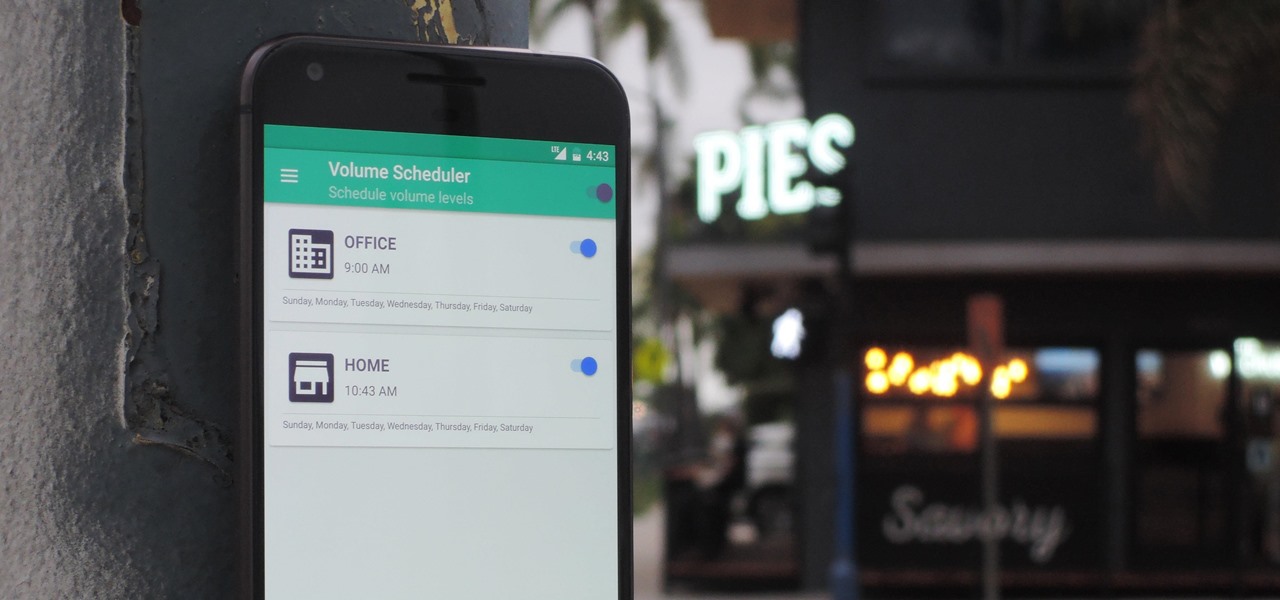
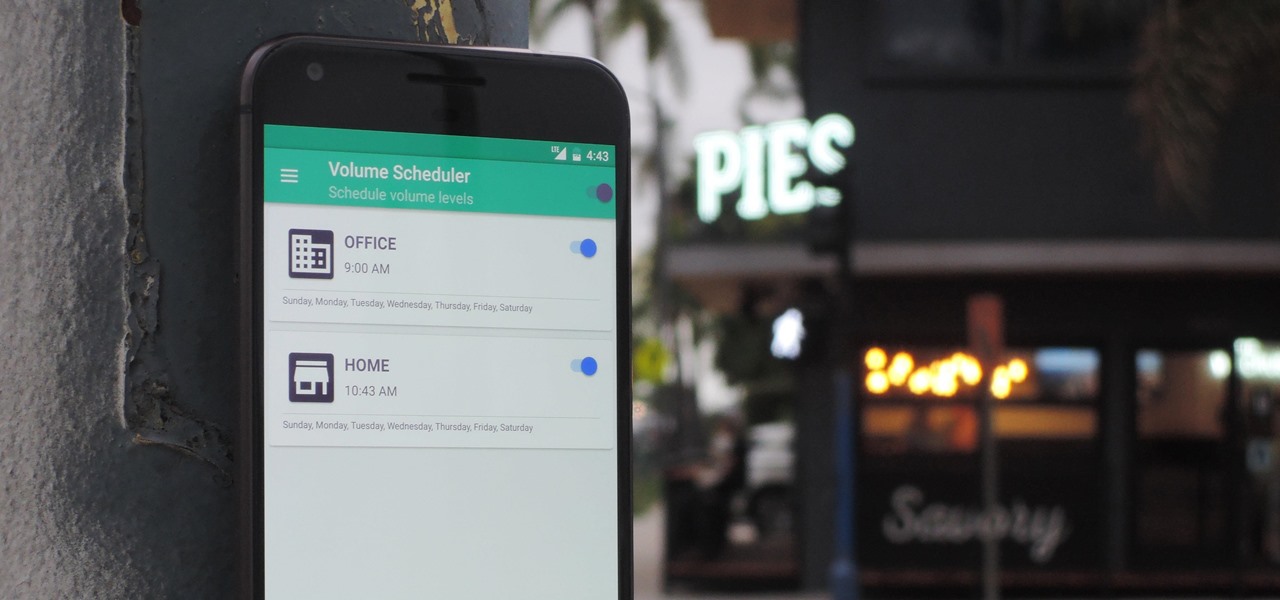
Different times call for different ringtone volumes. When you're at work or school, you need your phone to be quiet so it doesn't make a disturbance—but when you're at home or out and about, the volume should be turned back up so you don't miss any important notifications.
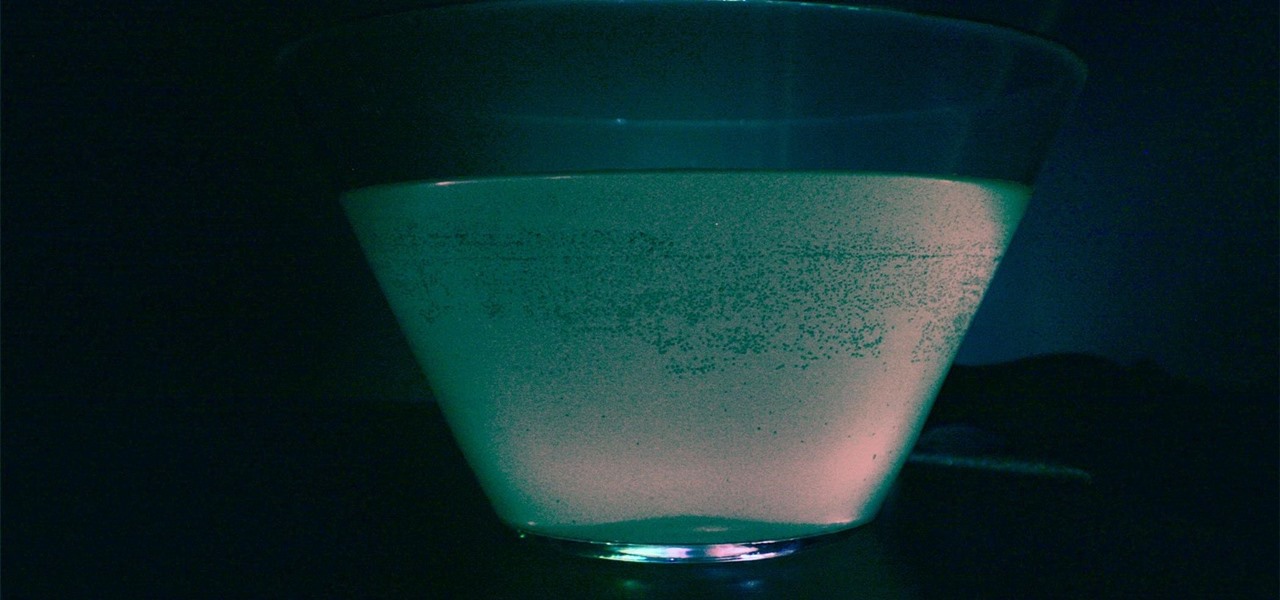
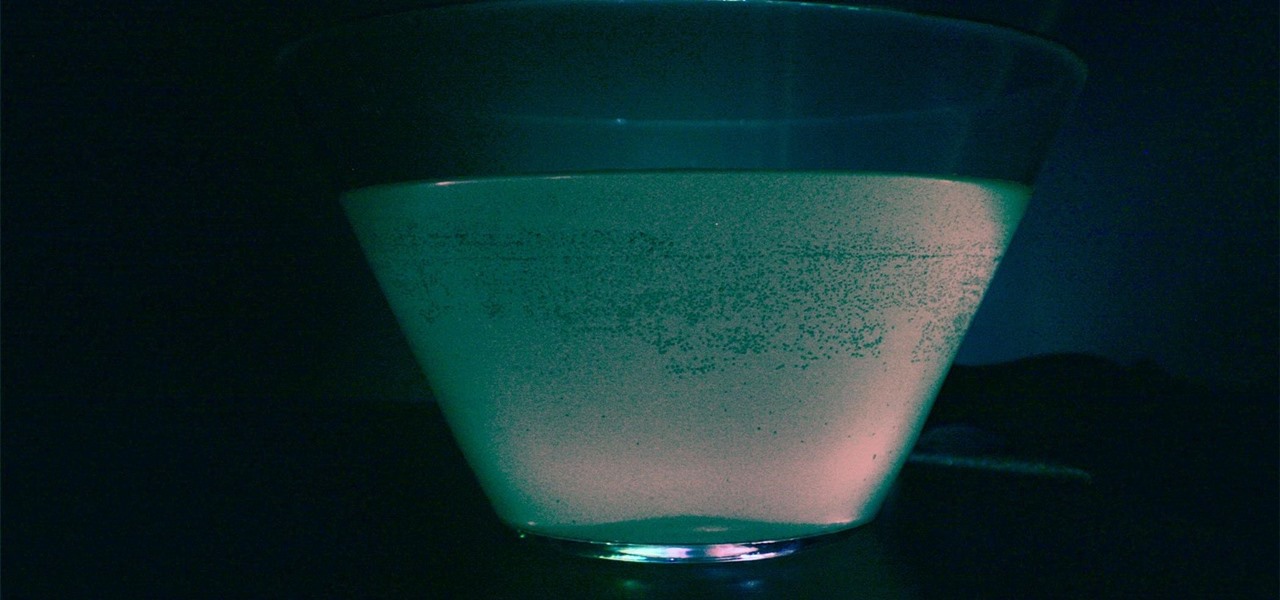
Halloween is this weekend, so if you're looking for a last-minute big batch cocktail that will keep your guests properly hydrated—and might turn them into mutants—look no further! (Note: This will not actually hydrate anyone, just so we're clear. Priorities, people!)

When Facebook purchased WhatsApp for $19.3 billion back in 2014, we all knew this was coming—it just took longer than we thought. But starting today, the data mining became official, and now, information from your favorite messaging app is no longer out of reach for the world's biggest social media site.

Although professional sports has been no stranger to emerging technology, it still seems hard to think about how a football player might benefit from strapping on a VR headset. While it won't do much in an actual game, many athletes can improve by using virtual reality as a training tool.

The default screen timeout on most Android devices is 30 seconds. This usually offers a good balance of usability and battery savings, but sometimes, you need the screen to stay on longer. For instance, practically every time I try to show something on my phone to someone else, the screen locks before they get a chance to see it. But increasing the system-wide screen timeout isn't a great solution either, because this can lead to unnecessary battery drain and even screen burn-in.

For most Android phones, the system clock is set using a protocol called NITZ, which relies on a connection with your carrier to ensure that the time stays in sync. The trouble here is that this feature won't work when you're outside of cellular range, and a lot of times, the carriers themselves have technical difficulties that can result in your phone's clock being minutes or even hours out of sync.

Logan's Run is one of my favorite movies of all time. The dialog is cheesy, the set design and special effects are wonky, and the main villain looks like he was conceived and built by an eighth grader in shop class—oh, and his name is Box.

I'm back! We're learning Java WhileLoops today.

It's no secret that the microwave is a modern-day wonder that, when used correctly, can cook a wide variety of food in a snap.

Hello aspiring hackers, It's been a while since I wrote a tutorial, so I figured I might just share one of the tools that I have created to help the community grow.

Hey readers! This tutorial will be the entry point for the introduction of buffer overflows. Something like requesting user input is a very common place for vulnerabilities to pop up and we will definitely have fun while trying to make programs crash. But for now, let's start with how we can get input from a user.

How to do an NMAP scan on Armitage to find IPs within a certain range. Armitage is a gui interface of Metasploit, and advanced hacking/exploiting program. It can be downloaded from http://metasploit.com/ and http://fastandeasyhacking.com/ and you will need NMAP. http://www.nmap.org/

A no-carb, gluten-free substitute for breadcrumbs. Sounds and probably tastes like cardboard, right? Unless you're talking about Pork Dust. Yes, you read that right. Pork. DUST.

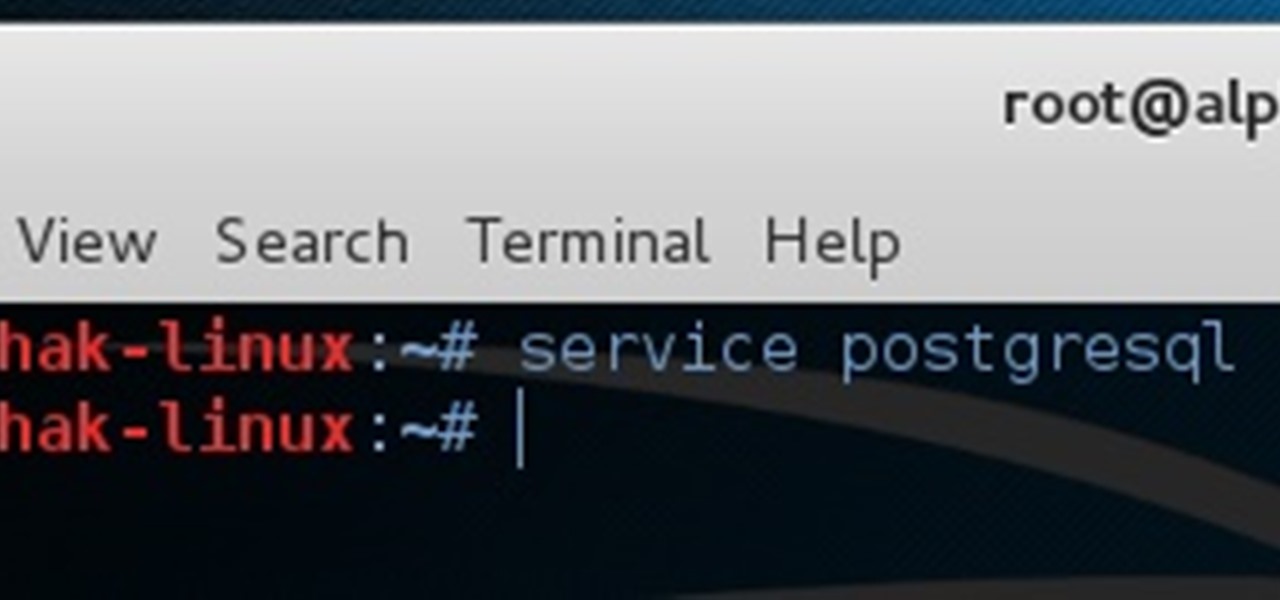
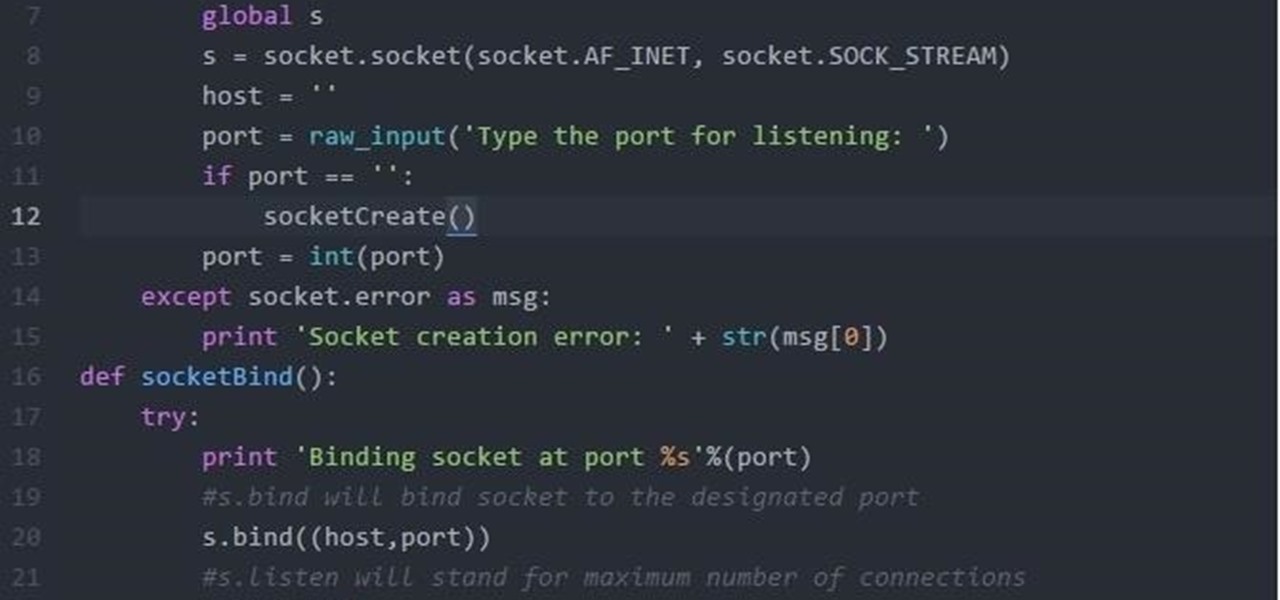
Hi Folks. This is my first post. I will teach how to create a server and client python reverse shell using sockets and python language. The script i'll post here is going to be very simple, and from here you'll have the possibility to adapt to your own purpose. For example, my original script can download files, upload files, make changes to registry, create user accounts and more. I'm sure you could do it on your own too.

As it stands, Android's notification system is one of its biggest strengths—but that doesn't mean it couldn't use a few tweaks here and there. For one thing, when you receive multiple notifications from the same app, there is no indication as to exactly how many notifications you've received.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

If you've ever used a custom ROM on one of your devices, chances are it had a built-in feature that allowed you to kill any app by long-pressing the back button. This function comes in handy quite often, especially in situations where an app is acting up, since it stops all associated processes and clears the app from memory.

Samsung's got a pair of beautiful new flagship devices coming out this spring that will surely top the sales charts. The Galaxy S5's successor is truly worthy of that title, but a second variant with a curved display turned heads at Mobile World Congress this weekend.

In general, we never really put much thought into fonts, but they comprise a huge portion of our online experience. A whimsical mood can easily be set by using something like Segoe Script, but switch it up to Sentinel and you've got a more sophisticated feel all of a sudden.

My college days are long behind me, and while I don't necessary miss them, I am jealous of all the countless resources available to students these days. Apps like PhotoMath are something I wish I had access to in my student days, making assignments less strenuous and easier to complete.

Android 5.0 "Lollipop" has only existed for a few months, but a leaked version of Samsung's take on the firmware has already been spotted in the wild. This update came straight from Samsung, and brings with it a plethora of new features, including greatly improved performance and a revamped TouchWiz UI.

Whether you use a third-party keyboard or the stock offering, your Samsung device keeps a history of the last 20 words you copied on its clipboard. Samsung added this feature to Android to help make multitasking a bit easier, but if you use a password manager like LastPass, this feature quickly becomes a gaping hole in security. While you're copying and pasting your various passwords, the last 20 of them become freely available to anyone that gets their hands on your device.

Google's music offerings have been on a roll lately. First they announced a new music video streaming service called YouTube Music Key, offering ad-free playback with background listening. Then they stated that the new offering would be rolled in with their Google Play Music service, with members allowed to exclusively test the Music Key beta, which just went live. And if all that wasn't enough, they're also offering free music to boot!

Steam is by far the biggest and best service for getting games on your Linux, Mac, or Windows PC. With their catalog containing everything from the biggest blockbusters to indie games created by one-man development teams, it's no easy task to keep track of their best values—until now.

With an Android device left at its default settings, your location history is automatically recorded. You can view and manage this data, but the simple interface of points plotted on a map leaves a lot to be desired.

The OnePlus One definitely fits the phrase "more bang for your buck," and despite the absence of something like the HTC One M8's Duo Cam or the LG G3's Laser Auto Focus, it still takes a great photo. For normal, everyday pictures, the 13-megapixel camera sensor is great, even if night shots can be a little grainy.

If you're like me, then you've got an incredibly complicated Wi-Fi password with uppercase and lowercase letters, numbers, and special characters.

In February of this year, the Higher Court of Berlin ruled that Facebook must follow strict German data protection laws, which Facebook's terms of services and privacy policies circumvent.

As great as Google's own Play Music app is, your MP3 library is restricted to Google's own app. There are much better music players that give Google Play Music a run for its money, but duplicating music files on your device for this reason alone is a waste of storage space.

T-Mobile continues to make waves in the U.S. wireless market behind CEO John Legere's UnCarrier program. At the latest installment in a series of industry-challenging announcements, Uncarrier 5.0 unveiled Test Drive. The new program is set to allow would-be customers to try out the "latest generation" iPhone for seven days on T-Mobile's network without any financial commitments.

Samsung's TouchWiz interface comes with tons of small features that can increase your productivity and user experience. From Mulit-Window Mode to Stress Level Monitoring, there are so many functions that some even go unnoticed.

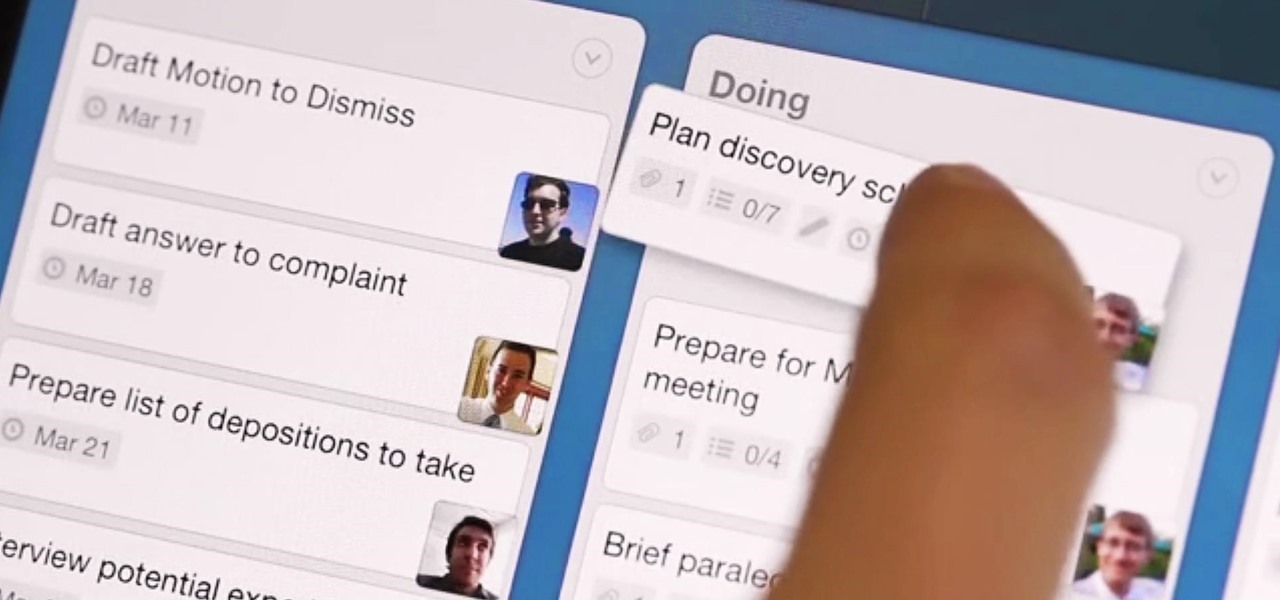
What separates the work habits of the ultra-productive from us mere mortals struggling to check items off our never ending to-do lists? While the answer to that question is by no means simple, one undeniable factor in their success is a clearly defined, highly organized workflow.

When Google first introduced Android 4.4, the most glaring user-facing change was a new trend towards transparency. The stock launcher, originally exclusive to the Nexus 5, had transparent status and navigation bars and its app drawer added a touch of transparency.

With the introduction of the Control Center in iOS 7, we finally had a way to access common system toggles like Wi-Fi, Airplane Mode, and best of all, Flashlight. Of course, there were plenty of adequate flashlight apps in the iOS App Store, but none that made it available straight from the lock screen.

For the most part, Xbox Live is amazing, but there is one thing that has been annoying for pretty much everyone, to say the least. Microsoft Points.

We all know about PRISM. The Surveillance Program allowing the U.S Government to access private user information. Such as, Google Searches, Tweets, Facebook Posts, Private Images, and other private user data. "Hiding" yourself can be very difficult, but it is possible. I'm here to show you How to Become Anonymous & Browse the Internet Safely.

For the most part, keyboard shortcuts are great. They save you some time and make it easier to do everything right from the push of a button. But like most things in life, there is always a caveat, and in this case, for me—it's a huge one.