Being fixated on all of the great additions to Android 5.0 Lollipop, it can be a little difficult to take notice in the features that went missing. For instance, lock screen widgets. It's speculated that the lack of practical use for lock screen widgets and the implementation of the revamped Lollipop lock screen may have lead to their departure, but some of us want them back!

Portal has been one of the most critically acclaimed and universally loved games of the last few years, and there's plenty of fan art to prove it. From building a Portal gun, to a gravity defying Companion Cube, and even installing Portal onto a graphing calculator, fans have found some innovative ways to show their love for the games.

Last year, Lytro released their first light field camera to help photographers have more control over focusing. This innovative and revolutionary camera allows users to change the depth of focus of a photograph after the picture is taken.

You may remember string art from your elementary school days. If so, it probably makes you think of the 2D geometrical designs that took every ounce of patience you had as a kid. Or those laborious curve stitch drawings, which string art was actually birthed from. But thanks to some innovative modern artists, string art has gotten a lot more interesting. Here are some of the most creative applications so far.

The next time a light bulb burns out in your house, don't throw it out. Believe it or not, burned out light bulbs aren't entirely useless. Besides creating an extra task on your to-do list, they can be hollowed out and used for a variety of different things from home decorations to miniature indoor gardens.

The big question this week would be the controversial Obamacare mandate. And heres the answer: Yes. Obamacare passes Congress' filters and is now an official OK. Texas college hacks drone in front of DHS — RT.

Improve your football game and your value to the team by memorizing and ready to execute your football playbook. Standard memorizing tools like flash cards and practice will help get you through any size playbook.

Watch this video tutorial to learn how to level hack Restaurant Life (12/05/09). 1. Open RL and Cheat Engine 5.5, then point CE 5.5 to the process of your browser.

This is a jumprope hack for Pet Society. It's called the Auto Jump + Coin hack, and involves your jumprope, Cheat Engine, and a little code generator.

You won't even need Cheat Engine to execute some of these hacks. Take advantage of a few glitches in the game before they get patched, and earn way more xp and money than any of your friends who are playing!

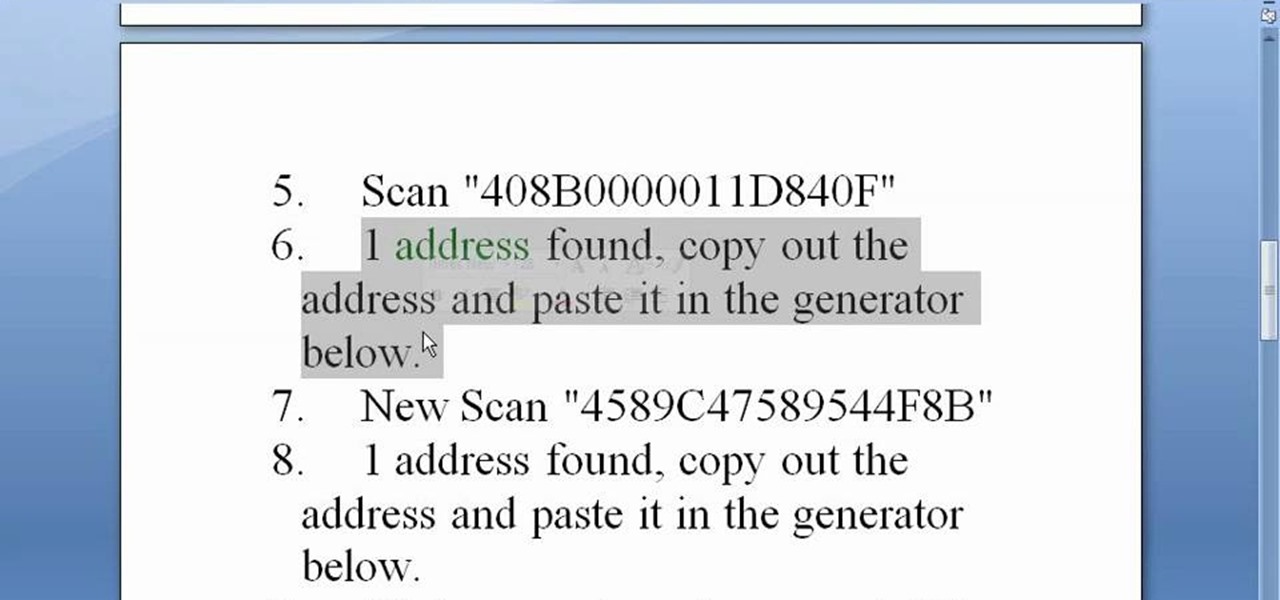
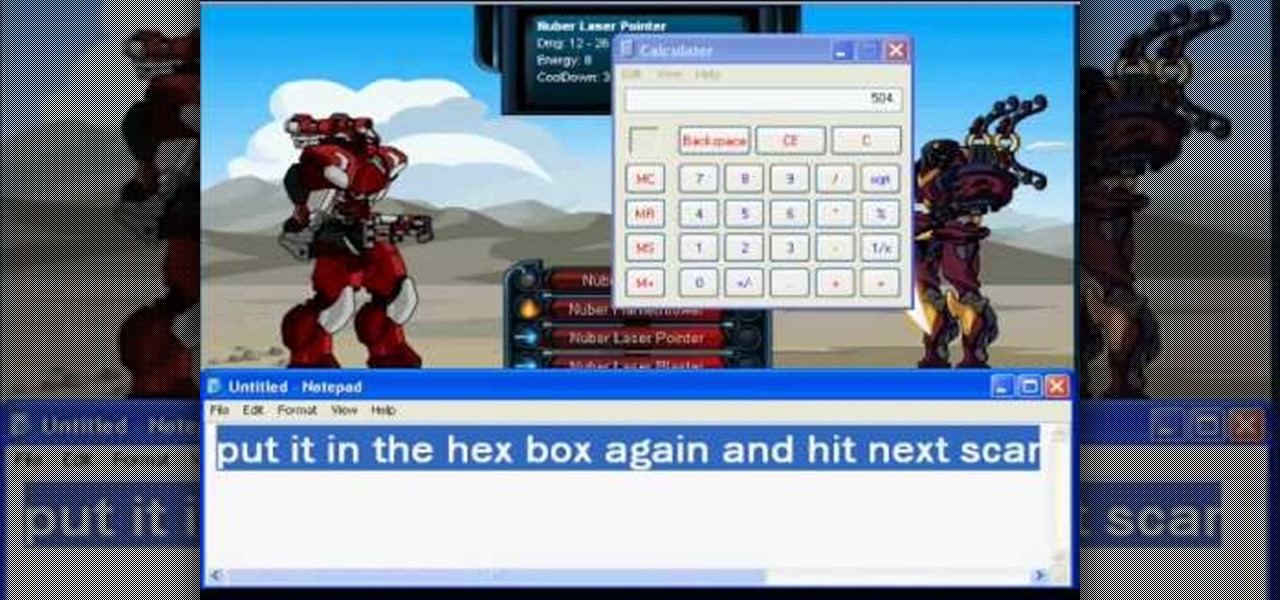
It doesn't matter how tough the monster is you're facing, you'll be able to take them down completely with just one hit! All you need is Cheat Engine (version 5.4 or 5.5) and a compatible browser to execute this hack.

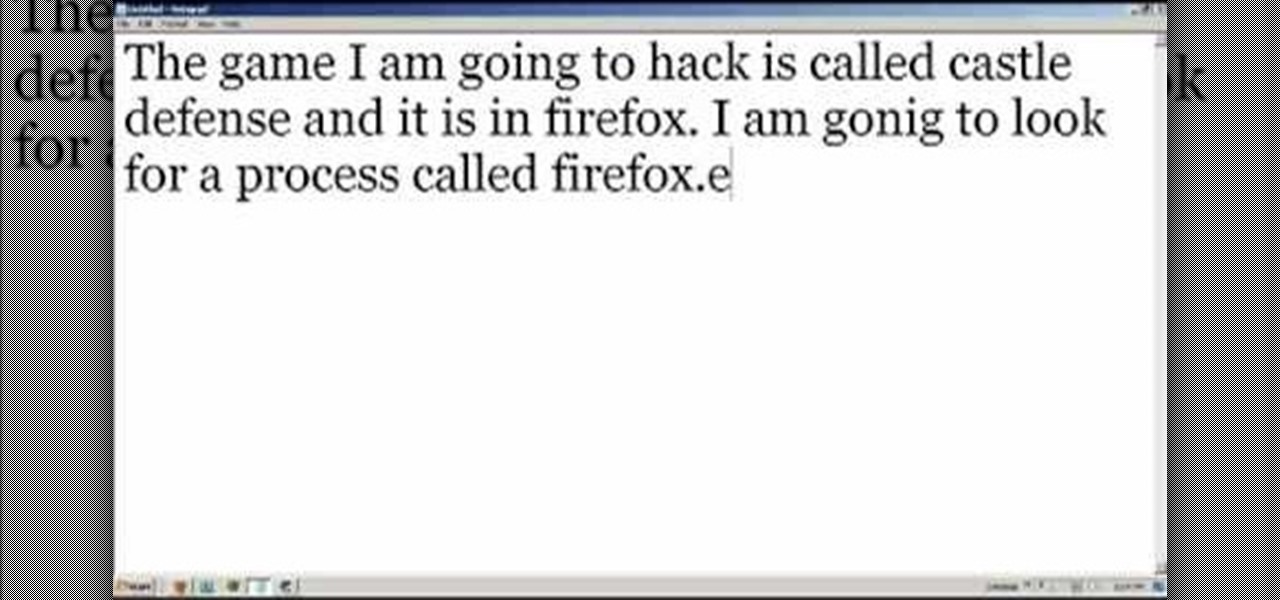
Many tutorials show you how to use Cheat Engine to execute one function of one particular game - but not this one! This tutorial gives you a good understanding of what Cheat Engine can do, and how you can use it to hack nearly any game!

This tutorial shows you how to execute a speed hack when playing Roblox. All you need is the free game hacking program Cheat Engine. Open Roblox, then open Cheat Engine and use the following hack to change the speed of the game.

After you've mastered the basics of an extension, you can move on to the extended liberty cheerleading stunt. Join Matt Null (NCA/Cheer Excel/Millersville), Jhana, Dena, and Lauren (Fire and Ice Allstars), and Greg (Step 1 Allstars) as you learn step by step how to do an extended liberty.

One of the most common web application vulnerabilities is LFI, which allows unauthorized access to sensitive files on the server. Such a common weakness is often safeguarded against, and low-hanging fruit can be defended quite easily. But there are always creative ways to get around these defenses, and we'll be looking at two methods to beat the system and successfully pull off LFI.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

Using Netcat to backdoor a macOS device has its short-comings. If the compromised Mac goes to sleep, the Netcat background process will occasionally fail to terminate correctly; This leaves Netcat running infinitely in the background and the attacker with no new way into the device. As an alternative, we'll use the lesser-known Tcl shell which can handle abrupt backdoor disconnections.

One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.

Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

The default tool for payload generation is MSFvenom, a Metasploit standalone payload generator as well as encoder. This tool is an incredibly powerful tool for payload generation, but it can be difficult and requires a bit of reading for newer users.

Gaining access to a system is always exciting, but where do you go from there? Root or bust. Sure, a compromised host is a great way to run a botnet, or do some other boring, nefarious thing—but as hackers, we want root. We also want to take the easiest path possible, search out low-hanging fruit, and exploit them. SUID programs are the lowest of the low-hanging fruit.

Welcome back, everyone. In the previous part of this rapid-fire miniseries, we built the victim portion of the shell. Today, we'll be building the attacker portion. This script will initialize interaction with the victim portion of the shell, send commands, and receive the output.

Welcome to a tutorial explaining functions. This article will help clarify some things we have already been exposed to such as function prototypes, function calls, return values, etc.

Hello fellow training hackers. I do not know if many of you are familiar with ruby, but since it is a useful scripting language, that hasn't been covered too much here on Null Byte, I thought why not do some How-tos about it now and then.

And we meet again Crackers! Welcome to my 7th post (Part-2), this tutorial will explain about some more basics of Batch Scripting, with C00L Scripts, which in turn will help you learn and understand better

Welcome back, my tenderfoot hackers! As you know, Metasploit is an exploitation framework that every hacker should be knowledgeable of and skilled at. It is one of my favorite hacking tools available.

Welcome back, my tenderfoot hackers! I have written many tutorials on hacking using Metasploit, including leaving no evidence behind and exploring the inner architecture. Also, there are my Metasploit cheat sheets for commands and hacking scripts.

http://www.texturemind.com/post463/ TypingRobot is an artificial intelligence studied to increase your points record with the Typing Maniac game on Facebook. It can recognize several labels because it uses a powerfull OCR system (tesseract) and some principle of word correction. With this program you can make millions of points without problems (my personal record is about 2.700.000 points).

Chess is a strategy and logical deduction game between two players that is enjoyed by children and adults alike, from park benches to convention halls across the world. Though the game of chess has taken many variations over its long history, today's form involves black and white teams orchestrated by players and has even entered the digital age, as games and tournaments are played online and via email. Using a square board composed of grids and smaller squares, the game pits a queen's army a...

Learn how to use the ProSear Burner on your Lynx Grill. The Lynx grill has many innovative features and understanding how to use each grill feature can make you more proficient user of the grill.

Learn how to use the main grill burners on your Lynx Grill. The Lynx grill has many innovative features and understanding how to use each grill feature can make you more proficient user of the grill.

Learn how to use the rotisserie feature on your Lynx Grill. The Lynx grill has many innovative features and understanding how to use each grill feature can make you more proficient user of the grill.

Learn how to light a Lynx grill. The Lynx grill has many innovative features and understanding how to use each grill feature can make you more proficient user of the grill.

Learn how to learn the basics of skateboarding. Initially an offshoot of California’s surf scene, this extreme sport has taken America by storm. Before you can execute sweet tricks, you need to start with the basics.

In this video tutorial, viewers learn how to play the song "Hilo March" on the ukulele. The video reveals the string movements and the order in which the notes need to be played, in order to execute the song. The video provides step-by-step narration and a visual demonstration for viewers to easily understand and follow along. This video will benefit those viewers who are interested in the ukulele and want to learn how to play a new song.