It's somewhat funny that the HTC ThunderBolt smartphone would be released around the same time as Apple's new Thunderbolt technology. Mainly because HTC's smartphone isn't exactly something I would compare to a flash of lightning, which averages around 60,000 miles per second. But Apple's new interconnect surely deserves the Thunderbolt designation.

Search engine optimization (SEO) is now one of the most important topics for website owners to understand. Anyone that depends on their website to bring them business needs to know the ins and outs of SEO in order to maximize their website’s potential. And if you want your website to have a high Google rank then SEO is essential.

How many Facebook friends do you have? The average person on Facebook has around 140 friends while some hit the ridiculous Facebook friend limit of 5,000. Facebook states that its services are for people you know in person. I don't think anyone has 5,000 friends in person, do you? Personally, I don't even think Megan Fox has 5,000 friends in person, so how could any regular person have that many? But that's beside the point.

Your BIOS, or Basic Input Output System, is the firmware on your motherboard responsible for initializing your computer's hardware when it is first powered on. It probes for video adapters, RAM, the whole works. The BIOS provides a small library of basic input/output functions used to operate and control the peripherals such as the keyboard, text display functions and so forth, and these software library functions are callable by external software such as the OS and system software within sai...

PLASTRUM n pl. -S plastron 62 points (12 points without the bingo)
If you're lucky, your digital camera has a built-in intervalometer that lets you operate the shutter regularly at set intervals over a period of time. Why would you be lucky? Because you can create some very awesome time-lapse videos, like the horribly beautiful eruption of a volcano or vivid star trails in the night sky. You can capture the stunning display of the northern lights or even document the rotting of your favorite fruit.

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

Since its inception in 2007, the Pwn2Own computer hacking contest has been challenging the vulnerability of mobile phones and web-related software. In 2010, the fruit of two full days of hacking came down to the exploitation of the following web browsers: Safari 4 on Mac OS X, Internet Explorer 8 on Windows 7, and Firefox 3.6 on Windows 7. The winners walked away with the successfully hacked computer, plus a cash prize, but they left one Godly browser intact: Google Chrome. Even the savviest ...

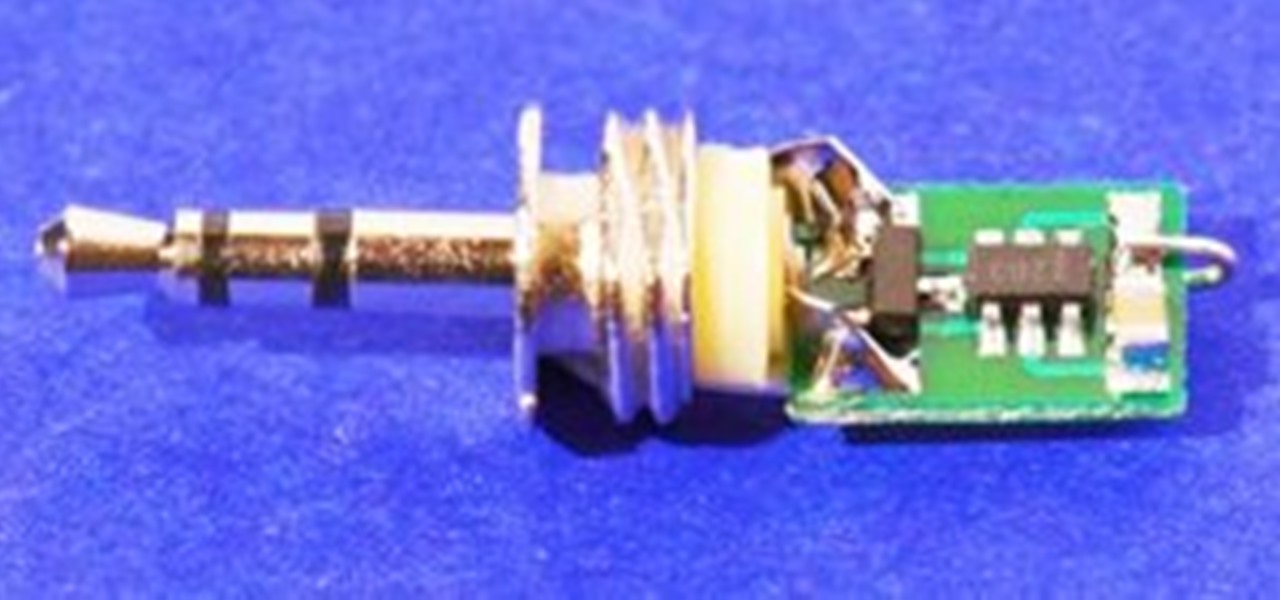
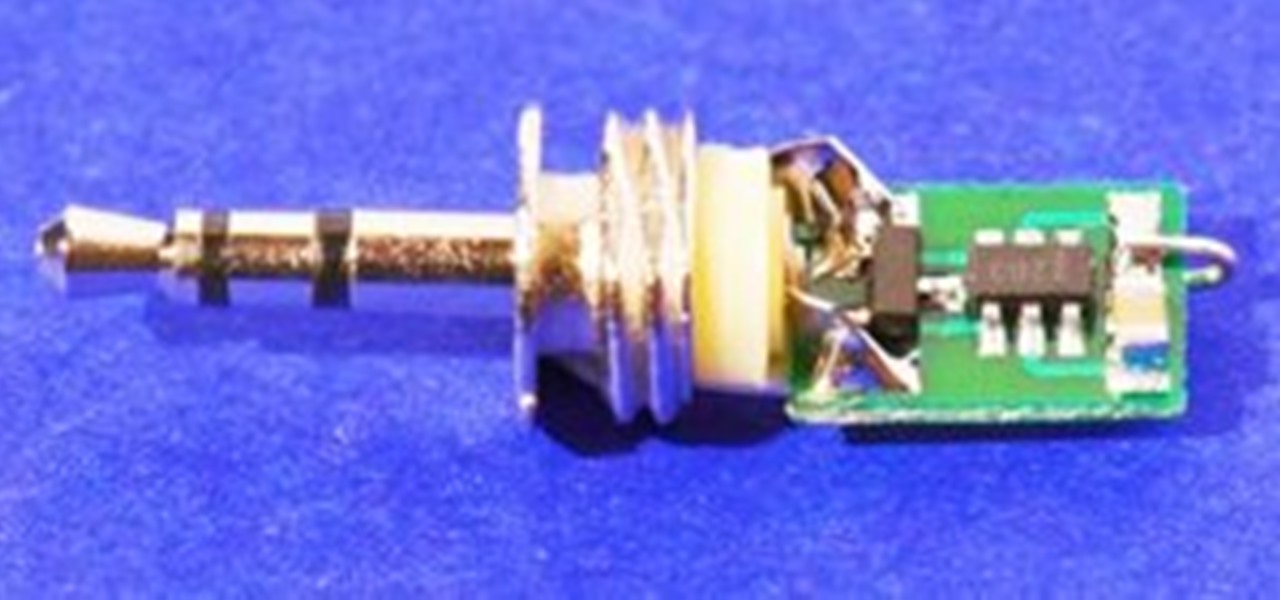
Granted the iPhone is an awesome phone... but their choice for default ringtones kind of, well, stinks. They have plenty of apps you can BUY to PURCHASE ringtones... but why waste money when you can make an unlimited amount of ringtones yourself forFREE? At first glance, it looks complicated and confusing, but I'll break it down so simply, you'll be making ringtones for everyone in iTunes.

You've had a massive hard disk failure.. ...in your PC or laptop and like a large number of people who think it will never happen to them...you did not have a backup of those 2000+ family pictures, those hundred of important Word documents, those family videos that you downloaded from the camera then erased from the cameras disk...the inevitable "I'm Screwed!'

Watch this first 'tutorial'.FauxTo! Hoax! Con! May 28, 2008, this video was uploaded to YouTube illustrating the popcorn popping power of a circle of ringing mobile phones. Radiation. Amazing. Viral. Millions viewed.

How To Sing Without Lifting Your Larynx

Learn how to exercise by doing the medicine ball throw on incline bench. EXERCISE DETAILS:

Learn how to exercise by doing the alternating incline rear shoulder dumbbell row on bench. EXERCISE DETAILS:

Learn how to exercise by doing the incline reverse dumbbell fly on bench. EXERCISE DETAILS:

Learn how to exercise by doing the rear shoulder incline dumbbell row on bench. EXERCISE DETAILS:

Learn how to exercise by doing the 1 arm diagonal dumbbell row and shoulder press with overhand grip.

Learn how to exercise by doing the cable shoulder press on bosu flat down. EXERCISE DETAILS:

Learn how to exercise by doing the alternating backward dumbbell crossover lunge and side raise. EXERCISE DETAILS:

Learn how to exercise by doing the barbell snatch. EXERCISE DETAILS:

Learn how to exercise by doing the dumbbell clean and jerk. EXERCISE DETAILS:

Learn how to exercise by doing the dumbbell clean and press. EXERCISE DETAILS:

Learn how to exercise by doing the cable side lunge with shoulder side raise. EXERCISE DETAILS:

Learn how to exercise by doing the dumbbell side lunge and shoulder side raise. EXERCISE DETAILS:

Learn how to exercise by doing the dumbbell snatch. EXERCISE DETAILS:

Learn how to exercise by doing the barbell clean and jerk. EXERCISE DETAILS:

Learn how to exercise by doing the squat and cable shoulder press with overhand grip. EXERCISE DETAILS:

Learn how to exercise by doing the 1 arm dumbbell clean and jerk. EXERCISE DETAILS:

Learn how to exercise by doing the 1 arm kettlebell clean and jerk. EXERCISE DETAILS:

Learn how to exercise by doing the 1 leg 1 arm dumbbell hang clean. EXERCISE DETAILS:

Learn how to exercise by doing the alternating incline dumbbell chest press with overhand grip. EXERCISE DETAILS:

Learn how to exercise by doing the standing targeted 1 arm cable chest press with overhand grip. EXERCISE DETAILS:

Learn how to exercise by doing the straight arm side bridge and hip abduction. EXERCISE DETAILS:

We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web.

With the mass arrests of 25 anons in Europe and South America, and the rumors of an FBI sweep on the east coast of America floating around, times look dicey for hackers. Over the past few days, a lot of questions have been posed to me about removing sensitive data from hard drives. Ideas seem to range from magnets to microwaves and a lot of things in-between. So, I'd like to explain a little bit about data forensics, how it works, and the steps you can take to be safe.

At some point, we all go from organized to disorganized. Let's assume you are a business executive working in a busy corporate building. Chances are you are going to get a heavy workload and it will impact how clean your workspace is. However, this article is about keeping your desktop clean and clutter free, along with the use of software to find documents you have misplaced.

This tutorial will be based on creating a partition in Windows Seven. I have seen so many people attempt to do this themselves without guidance. Ultimately, they end up with a corrupt system. The aim of this tutorial is to make sure you don't corrupt your system.

Here's a nasty little Null Byte. An open redirect vulnerability was found in both Facebook and Google that could allow hackers to steal user credentials via phishing. This also potentially allows redirects to malicious sites that exploit other vulnerabilities in your OS or browser. This could even get your computer flooded with spam, and these holes have been known about for over a month.

Paying for web hosting isn't ideal in most situations. If you have your own website, hosting it yourself is very acceptable and easy to do, assuming your internet bandwidth permits. Most people want to run a personal site, nothing crazy, so hosting from home on low-bandwidth internet is actually a better solution in most cases.

When you buy computer parts, it can be a tough decision where you want to put all of your hard earned dollars into. Not only that, but when you buy a top of the line component, 3 months later (at most), your hardware will likely be outdated. This puts consumers like us in a bit of a pickle when it comes to purchasing, especially on a tight budget.