In the wake of the NSA controversy and its subsequent fallout, many dashed towards finding means of secure communication—using private internet browsing and encrypted text messaging applications—out of fear of being spied on.

Update 1: Evad3ers have released a statement to the jailbreak community, claiming that the safety and security of their users is the most important thing to them and that all speculations about malware being encoded into the jailbreak is simply not true. You can read the full letter over at Evasi0n's site.

In a world where more features are king, sometimes it's a good thing to breathe, take a step backwards and keep it simple. With home launchers, this isn't often the case, as developers add a galore of features to their apps in order to be at the top of the game.
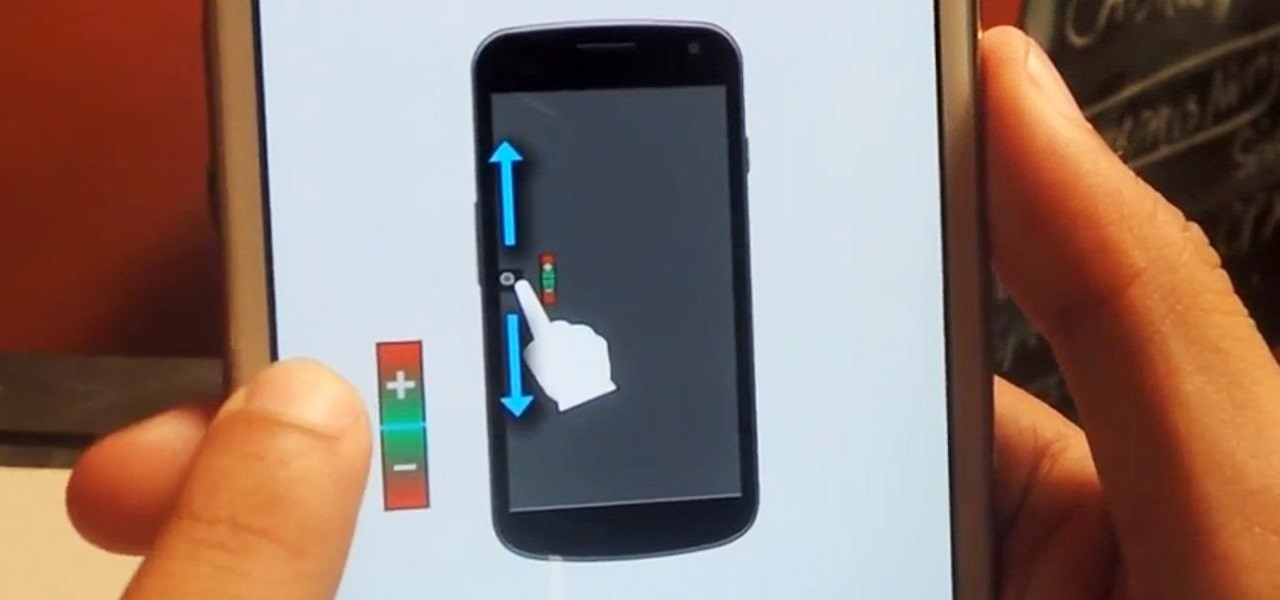
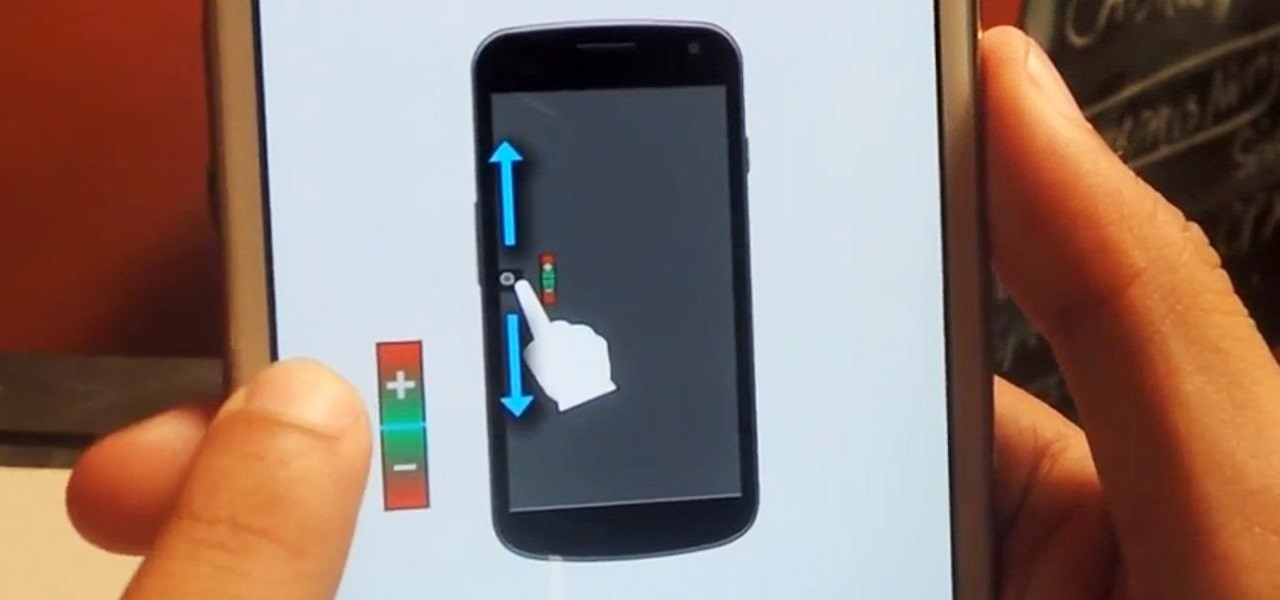
Due to its enormously awesome size, the Samsung Galaxy Note 2 usually takes two hands to maneuver through photos and texts, write emails, and get directions on the map.

I'm still amazed by all the things some people just don't know. Script-kiddies often refer to Metasploit if someone asks them how to hack a computer because they think there's simply no other way. Well here I am today trying to increase your set of tools and -of course- skills.

Drilling holes in wall tiles is a fairly easy skill to master once you know how. Follow these simple steps on how to drill a hole in a tiled wall for a hassle free experience.

One of the very first Photoshop skills we learned in my tenth grade photojournalism class was cropping the background out of images. I hated it. It was extremely time consuming, and the magnetic lasso tool never seemed to want to cooperate with me.

Rubik's Cubes are classically frustrating on their own, but what if you want to go that extra mile and make your puzzle impossible to solve?

If you've ever listened to your loved ones sing in the shower or watched a few minutes of American Idol, you would think that the majority of the population is tone deaf. In reality, only about 4 percent of the world's population suffers from tone deafness, or the inability to distinguish between different pitches. Che Guerava, Charles Darwin, and Ulysses S. Grant were all tone deaf.

I get advice from my friends on a lot of things in life—cool video games, movie reviews, and feedback on my choices in women. Friends can be very helpful in filtering out some of the excess noise and are more likely to give you suggestions you can relate to.

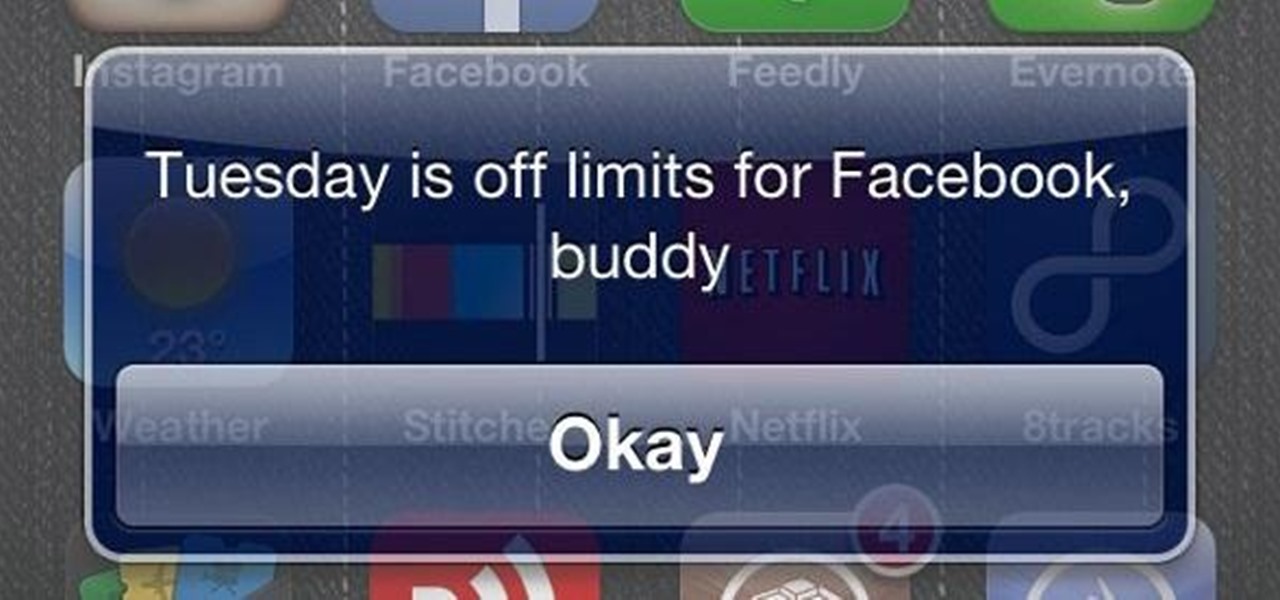
Self-restraint is one of the hardest thing to do. I'm a world-class procrastinator, and one of the biggest causes for my procrastination is my iPhone. Temple Run 2 was probably the best and worst thing that could have happened to me.

I loved the Gold Rush unit back in third grade. We went up to the American River and panned for gold, and my panning skills balled above all. I got like three tiny pellets. Of course, it was all fool's gold, aka pyrite, but it was still pretty legit. And this was before wearing gold chains was cool—or not.

The stereotypical geek is not good at sports. Think about it, we’re known for spending time in dark basements doing weird stuff that has nothing to do with running around and being active. So we’re known for our inability to play sports, but I wouldn't call it an inability so much as a creative way of passing these challenges by the skin of our teeth. Examples:

Social media is where we post our thoughts for the world to see, but sometimes a little more exclusivity is needed. And that's where Scrambls comes in.

Glitches can be extremely annoying when playing some of your favorite games, but sometimes, only sometimes, there are glitches in the game that give you an unprecedented advantage against the computer or other players online.

With the ever-evolving technology that imbues photography, we are never short of fantastic awe-inspiring shots. Digital cameras can capture things that the naked eye only wishes it could see, like streaking lights, rapid movements, and faraway objects, and it's fairly easy to capture these things if you know the basics.

Take everyday sprinkler parts and form them into a high pressure rocket launcher that will shoot paper rockets nearly 300 feet!!! It's cheap to make and a lot of fun!

There's a broken canister of mutant ooze leaking down into the sewers! But don't worry because this sticky slime is non-toxic, and it's so easy to make, a three-year-old can do it!

This design is super simple and is the easiest invisible door that I've ever seen. Unlike designs that use horizontal pistons, the redstone here is completely hidden underground, and the door itself doesn't create an unsightly dip or gap in the wall.

There are a lot of programs which allow opening archives. Alas, most of them are rather complicated to use. The process of opening of the archive often takes much time. Hopefully, there are some applications which are simpler to use for regular uers.

All you science and astronomy nuts out there, pay attention, this detailed video tutorial series will tell you everything you need to know about using the Meade EXT Backpack Telescope to ogle the universe.

In this tutorial, we learn about treating pimples overnight with toothpaste. This should only be used as a spot treatment overnight to dry the pimple out. Remember not to put this all over your face, or your face will become irritated and extremely dried out. Only put the toothpaste in the spot that your pimple is at. If you have very sensitive skin, this is not recommended. A good acne treatment and regiment is going to be the best method for not getting acne, but this is a great way to take...

This is a video tutorial on how to create a mouseover link (button) in Flash. According to the author, this is an extremely easy task, the first step of which is to select the file in which the button is to be made. Then, on the extreme right-hand side, in the middle of the column of icons, one has to choose the button icon, and then select which shape and color of the button one would prefer. The text is then typed in the text box selected over the button, and converted into a symbol by pres...

There's absolutely nothing comfortable about flying, unless you happen to be tiny enough to fit into the limited space offered on airplanes, or wealthy enough to afford a first-class ticket. And if you're about to embark on a long flight, catching a few Zs can feel like an impossible task. But it's definitely not impossible to get some quality sleep for a few hours, you just need to know how to use that limited space to your advantage.

If you own a 2010 Ford Lincoln MKX, you probably never knew about this handy feature. Not only can you see how much gas you have left in your car's tank, but you can see an estimate of how many kilometers or miles your car has left until your gas tank is empty. This is extremely helpful if you're in unknown territory. Watch and see how to set your Information Center to see how much gas you have remaining until empty in your 2010 Lincoln MKX.

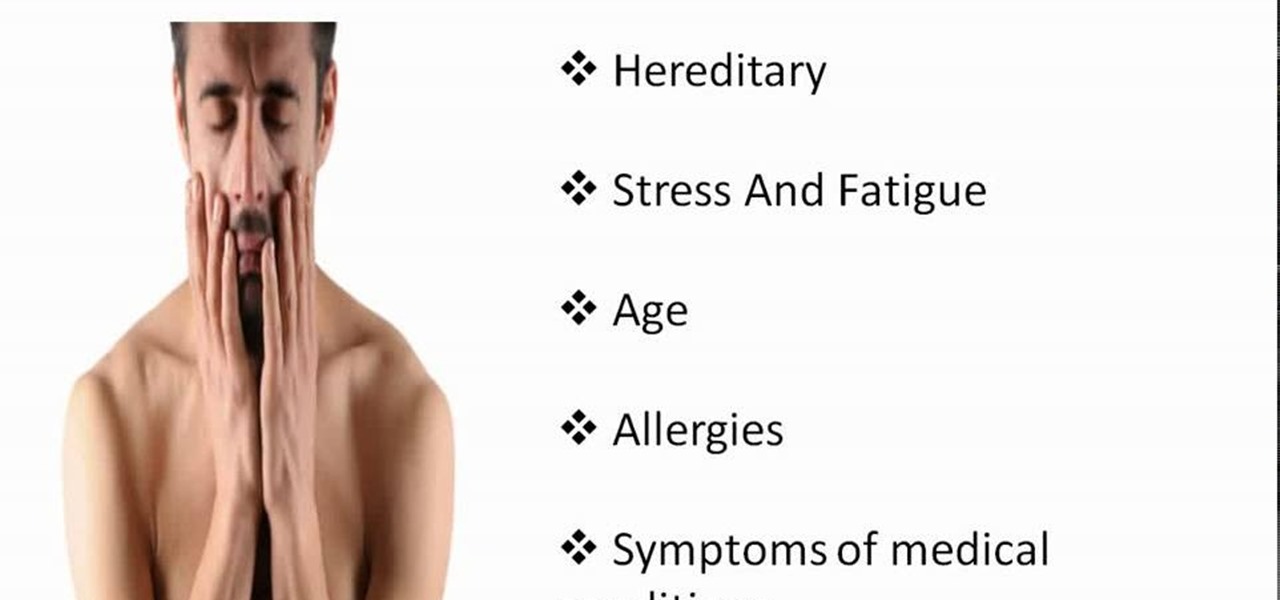
GetYourSkinBack discusses the various causes of black circles under the eyes and how to get rid of them. Skin discoloration under the eyes affects almost everyone at one time or another. It can add many years to your appearance, so getting rid of it is extremely important. The main causes are heredity, stress and fatigue, age, allergies, and medical conditions.

Need a quick fix for some nasty pimples? It could be a real disaster to have a huge pimple on your face during an important moment in your life. Even during a normal day, these pimples can be extremely embarrassing.

It's winter, and you've just woken up to find your car covered in a thick sheet of ice. What are you going to do? Turn your automobile on and hope that the heater and defrost melts that ice before it's too late, before you're late for that big meeting, or your final exam.

Expressions are new in SSIS (meaning that they were not in DTS) but they allow you to create extremely flexible packages. Expressions can be used to assign values to variables, help you determine whether to execute a task, and to assign properties. If you ever found yourself writing ActiveX code (VBScript) in DTS to determine which task to execute based on a variable's value, then you probably can forego the scripting all together in favor of expressions! They are very powerful in SSIS and yo...

Probably the most iconic of knots, this knot is easy to make and absorbs movement and shock extremely well.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

The long wait is over — the best augmented reality device on the planet is finally available.

We've already shown you our favorite new action games that have come out this year, but now it's time to share our all-time top ten list. These games are available for both Android and iPhone, they don't have intrusive ads or freemium schemes, and most importantly, they're all completely free to play.

Cross-site scripting is one of the most common vulnerabilities found on the web today, with repercussions of this type of flaw ranging from harmless defacement to sensitive data exposure. Probing for XSS can be tedious and time-consuming for an attacker, but luckily there are tools available to make things a little easier, including Burp Suite, Wfuzz, and XSStrike.

The ability to execute system commands via a vulnerable web application makes command injection a fruitful attack vector for any hacker. But while this type of vulnerability is highly prized, it can often take quite a bit of time to probe through an entire application to find these flaws. Luckily, there is a useful tool called Commix that can automate this process for us.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

If you want to use your iPhone with another carrier, all you have to do is contact the original carrier to request an unlock, which is usually granted in a few days. Unfortunately, you need to meet specific criteria to officially carrier-unlock your iPhone, like paying off the device in full and completing any contracts. But that doesn't mean there isn't a workaround you can use beforehand.

Watching an ice cream pro build you a custom frozen treat mixed with your favorite fruit, candy, and/or toppings makes buying a cone even more exciting. But why go out for ice cream when you can create your favorite combinations in your own kitchen? While you might not have an expensive frozen slab for ice cream topping your kitchen counters, you can mimic the creamy consistency and customizable options from Cold Stone Creamery and Marble Slab any time you're craving it. Best of all, you don'...

Lenovo brought out the big guns for CES 2014, with the Vibe Z showcased as the Chinese company's' first foray into the LTE smartphone space. Slated for a February release, the ultra-thin and extremely light smartphone will certainly be in the running for top smartphones of this very new year. Photo via CNET

Here's how to make dry-ice at home, or wherever you feel like it! All you need is a pillow case, and a CO2 fire extinguisher.