Bamboo is easy to grow, but there are a few things you should know before starting. There are hundreds of species of bamboo and they can be roughly divided into either running or clumping bamboos. Almost all cold hardy bamboos are runners and almost all tropical bamboos are clumpers. Running bamboos send out root like rhizomes underground and can spread many feet each year. Clumping bamboos slowly expand and stay in a tight clump with canes close together. We grow dozens of cold hardy bamboo ...

Sometimes a person can feel life is getting you down - you don't feel productive, or there's not enough hours in a day to do everything you need. You might not feel motivated to get up in the morning or to go to work anymore, and sometimes one might ask oneself "Is this all there is to life?"
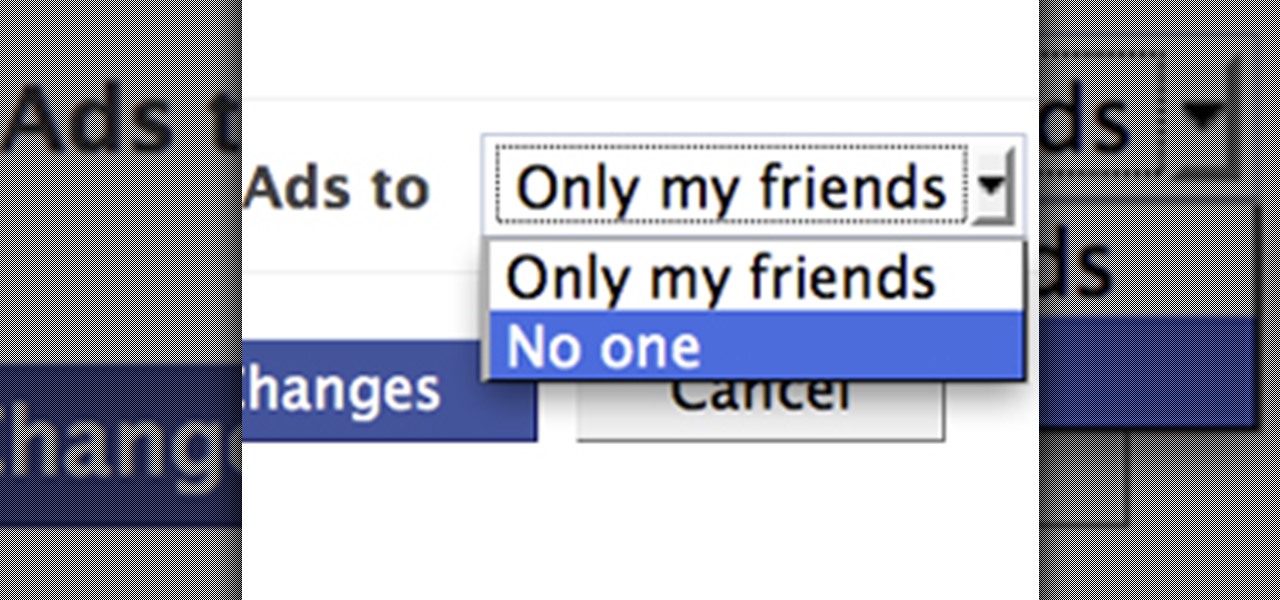
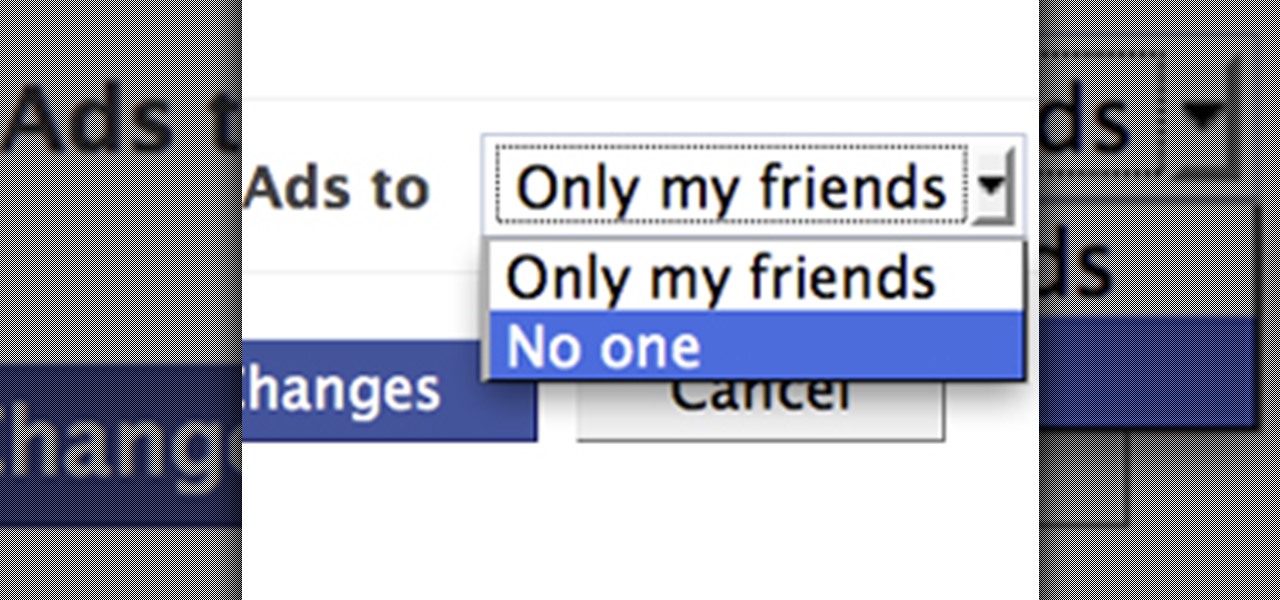
Facebook is constantly evolving, and lately it seems like a bad thing, at least for its users. First, you had to opt out of Instant Personalization, which shared your personal information with Facebook's partner sites. Then, you had to take drastic measures to secure your home address and mobile number from third-party apps and websites. And now?—Now you need to opt out of Facebook Ads.

Gas prices across the United States have skyrocketed, with today's national average for regular unleaded gas at $3.51 a gallon, with California leading the pack at $3.90 a gallon. AAA reports that last week's national average was just $3.37. That's a $0.14 increase in just one week! Just one month ago, the average was $3.12. A year ago—$2.75 a gallon. Actually, the U.S. Energy Information Administration (EIA) states the price of gas hasn't been this high since since 2008 when it hit $3.57 in ...

You've seen it in action before, but now it's finally got a solid release date, well... release month.
Let's face it— most people don't understand Shakespeare's language. If they say they do, they're probably lying. The poetic words of the world's most famous playwright continue to plague school children and college lit. majors alike, but not anymore.

Thanks to the advent of smartphones and mobile apps, Scrabble has spread like wildfire across the globe, whether it be Scrabble or one of its many popular word game spinoffs, such as Words with Friends, WordWise and Kalimat.

Two friends spend a nice relaxing day at the beach. Only problem is that they were born in 1902.

I recently upgraded from Ubuntu 9.10 to 10.04 and now my boot screen is a bit messy. Since I'm not using the latest GRUB boot kernel (Linux 2.6.32-28-generic), I might as well delete it. For more documentation, visit Ubuntu Forums.

Manicures are beautiful and can add class and style to any person. Here are some step-by-step instructions for giving yourself a DIY manicure.

Tired of seeing all of those ads in your browser? The flashing ones make for a terrible browsing experience, and those rollover ones are just downright annoying. If you don't want to be bothered by them again, you've got a few choices, depending on what web browser you're using.

Letter formation can be fun! Few children enjoy traditional handwriting practice. Copying the same black letters over and over again with a pencil is boring! Here is how you can make letter formation fun while practicing with your child at home.

If you're an owner of a BlackBerry smartphone, chances are you're going to want to use BBM, which for all of you newbie BlackBerry owners, stands for BlackBerry Messenger. BBM is an instant messaging application developed solely for BlackBerry device owners.

Plastic Jungle.com offers an awesome service in which you can sell your unused gift cards for cash, other gift cards, and even Facebook credits!

Want a face lift? Scared to go under the knife? Then, your solution is dimethylaminoethanol. Um... what is dimethylaminoethanol?

Forget CNN. Forget New York Times. Forget BBC. You can even forget the Washington Post. And yes, the Wall Street Journal, too. You no longer need these well-established and reputable news organizations to get your daily fix on what's happening in the world today.

WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most popular communities. Users can join and participate in any World they're interested in, as well as start their own community.

Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying various SQL injection vectors over and over. This is especially so if they are using an automated framework like sqlmap that can spam a ton of requests in a short time. More often than not, the access logs are what most amate...

You walk over to your laptop, wiggle your mouse to wake up the screen, then fire up your browser to come visit Null Byte. Catching the article about Anonymous and how they presumably will not take down the Internet, you find yourself wondering... how would someone take down the Internet? Could they even do it?

Industrial espionage, social engineering and no-tech hacking are all very real and there are simple precautions that you can take to protect yourself, which this article will discuss. Whether you are a high-profile businessman or a housewife (or husband), keeping information you want to keep private, private, should be important to you.

If you follow the Anonymous, Occupy, and IT security scenes, you have no doubt heard about a dox release. What is it? How can it hurt you? And most importantly, how can you protect yourself from it? Some of these steps might seem common sense, while others will be an ah-ha! moment. Your private info is both your biggest weakness and your biggest weapon in your battle to remain anonymous. You must learn how to use it as both.

WonderHowTo is made up of niche communities called Worlds. If you've yet to join one (or create your own), get a taste below of what's going on in the community. Check in every Wednesday for a roundup of new activities and projects.

There are seemingly endless photography apps for the iPhone—it is perhaps one of the most popular arenas for application developers. We've covered a few in Giveaway Tuesdays, but nothing comprehensive.

After the media outcry of Google Buzz's privacy issues, Google has set its goals on making the privacy parameters of Google+ simple to learn and as explicitly manageable as possible. No small feat.

It's that time of year again when pizza boxes line the room and buffalo wings stain the couch. When cases of beer sit in the cooler and the big screen TVs are fired up and properly calibrated. When two of the best football teams vie for the championship title and the Vince Lombardi trophy.

The last few months of WikiLeaks controversy has surely peaked your interest, but when viewing the WikiLeaks site, finding what you want is quite a hard task.

The CNA certification exam can be stressful at times, especially on the clinical exam portion. However, despite the exam difficulties, everything has a solution. Qualified nursing assistants are preparing various CNA study techniques and CNA study guides just to reduce any test anxieties and stress.

Advances in technology continue to make our lives easier and more convenient. If you want to send fax, for instance, you no longer need to own a fax machine. You can easily and quickly send fax directly from your computer in one of several methods, including via an Internet fax service provider or using Windows built-in Fax and Scan tools. Read on how to use an Internet fax service, one of the faster faxing methods, to send fax messages from your PC.

After his fall from Asgard into space, the Asgardian Loki meets the Other, the leader of a warmongering alien race known as the Chitauri. In exchange for retrieving the Tesseract,2 a powerful energy source of unknown potential, the Other promises Loki a Chitauri army with which he can subjugate the Earth. Nick Fury, director of the espionage agency S.H.I.E.L.D., arrives at a remote research facility during an evacuation. Physicist Dr. Erik Selvig is leading a research team experimenting on th...

If Null Byte had a large Batman-like spotlight calling for help, we would definitely be using it right now. However, we don't, so this is my digital equivalent. Information security is a huge field, far too much for one man to cover adequately, so I need your help!
Each year on Shrove Tuesday and Ash Wednesday, Ashbourne becomes a war zone! The majority of the ablebodied men, women and children take to the streets to play what is probally the largets football game in the world! - The two teams number in the hundreds, and the palying field is 3 miles long, 2 miles wide and has the town of Ashbourne in the middle!

If you've read my darknet series, you've probably got a pretty good idea of what I2P actually is and is capable of. One of the features of I2P is that it's designed with P2P file sharing in mind. Using a built-in service called I2PSnark, you can host and seed torrents quickly and easily!

Last time, we looked at archaic cryptography, so you should have a basic understanding of some of the concepts and terminology you'll need. Now, we'll discuss one of the most important advances in computer security in the 20th century—public key cryptography.

Did you know there is hidden data in your digital pictures? Well, there is, and that data might be a security risk to you. Think back at all of those pictures you're in and are connected with. I'm sure some of those you'd like to distance yourself from. And surely you wouldn't mind checking out the metadata in a few of those images. In this article, we'll be going over how to do just that.

Cryptography is a quintessential part of computer security in the modern world. Whenever you buy something on eBay or log into Facebook, that data is encrypted before it's sent to the server in order to prevent third parties from eavesdropping and stealing your sensitive information.

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

I recently posted a link to what seemed to be a very useful guide on Lifehacker for creating a TOR button in Chrome. However, when I tried it myself, it did not work. Also, it lacked a warning on the limits of Tor, which I think are important. Therefore, I decided to create an updated and more comprehensive tutorial.

When it comes to webcams these days, most people are using their laptops over desktops. The cameras are centered, integrated, and require no configuring. They're a cinch and usually have great resolution. So, then what do we do with all of those old wired desktop webcams that we've accrued over the years? Even if you still use an external USB one, chances are you're not using it daily, so why not come up with a better use for it?

It has been suggested that about 150 million internet users will be affected by today's blackout of Wikipedia in protest of SOPA and PIPA. If you don't know what those are, go here and read up on it, and then take action yourself! After you've contacted your Representatives about these bills, you'll probably still need to get some work done today using Wikipedia's English-language site.

Here's a nasty little Null Byte. An open redirect vulnerability was found in both Facebook and Google that could allow hackers to steal user credentials via phishing. This also potentially allows redirects to malicious sites that exploit other vulnerabilities in your OS or browser. This could even get your computer flooded with spam, and these holes have been known about for over a month.