Pink eye, or conjunctivitis as your doctor may call it, is a contagious disease that affects many college students. Blame close quarters and bad hygiene for this itchy ailment that affects the eyes. Here's how to treat and even avoid this condition.

Someone you love is consuming much too much and you want to stage an intervention. While interventions can work, a person who abuses alcohol has to be willing to stop drinking. Here, everything you need to know to help encourage a friend to quit drinking.

You know you're in pain, but are you just feeling the aftershocks of that spaghetti dinner, or is it a heart attack?

Every year, 250,000 Americans are diagnosed with a form of skin cancer called squamous cell carcinoma. What exactly is SCC?
If you know the triggers that bring on a migraine you can more easily sidestep experiencing one.

Heart disease affects more than 20 million Americans. Let's explore the various forms that heart disease can take.

This video explains how to fold an origami goldfish using a single sided solid colored sheet of paper of size 6".

Learn how to fold an origami rabbit with instruction by Ancella Simoes. This video is in two parts, so be sure to click on Chapter 2 for the complete tutorial.

Learn how to fold an origami Reindeer with instruction by Ancella Simoes. Ancella Simoes is the author of the Origamiancy Blog and creator of all the Origamiancy origami tutorial videos on WonderHowTo. From Ancella's site:

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

We're living in uncertain times. The sudden outbreak of the novel coronavirus and subsequent self-isolation of roughly half the world's population has led to a massive reorganization of the economy, countless layoffs, compromised security networks, and a variety of other significant disruptions that will forever alter the landscape of our daily lives.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

Apple had its Worldwide Developers Conference on June 3, 2019, which showcased big software announcements for all of Apple's hardware, and anyone can watch the keynote as it happened.

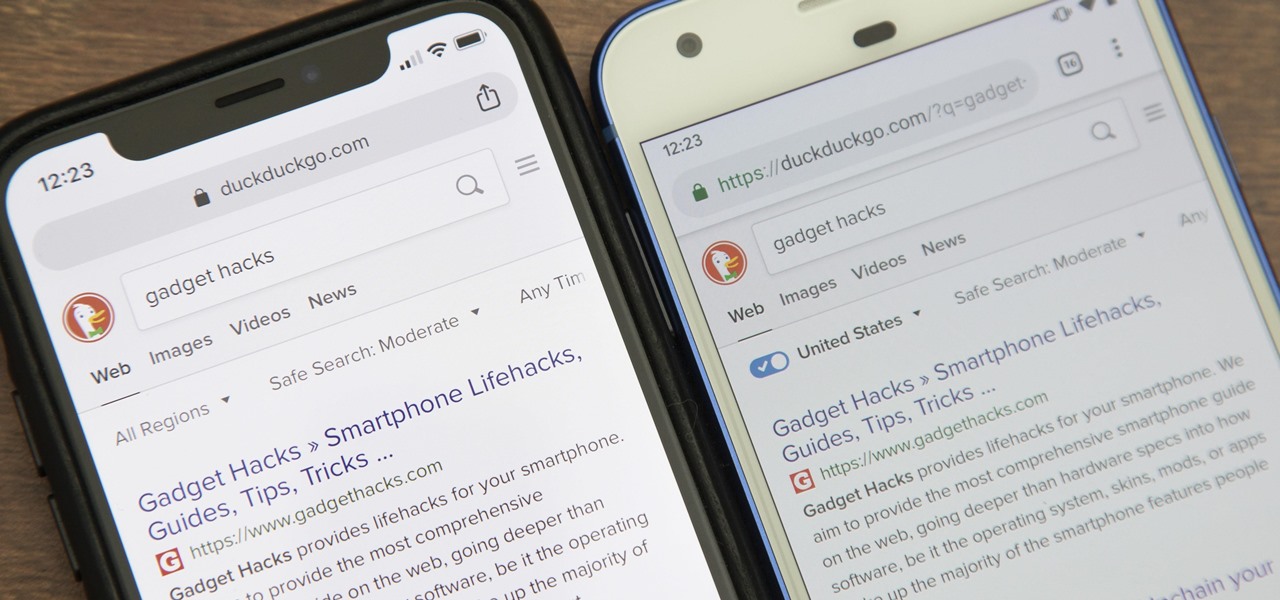
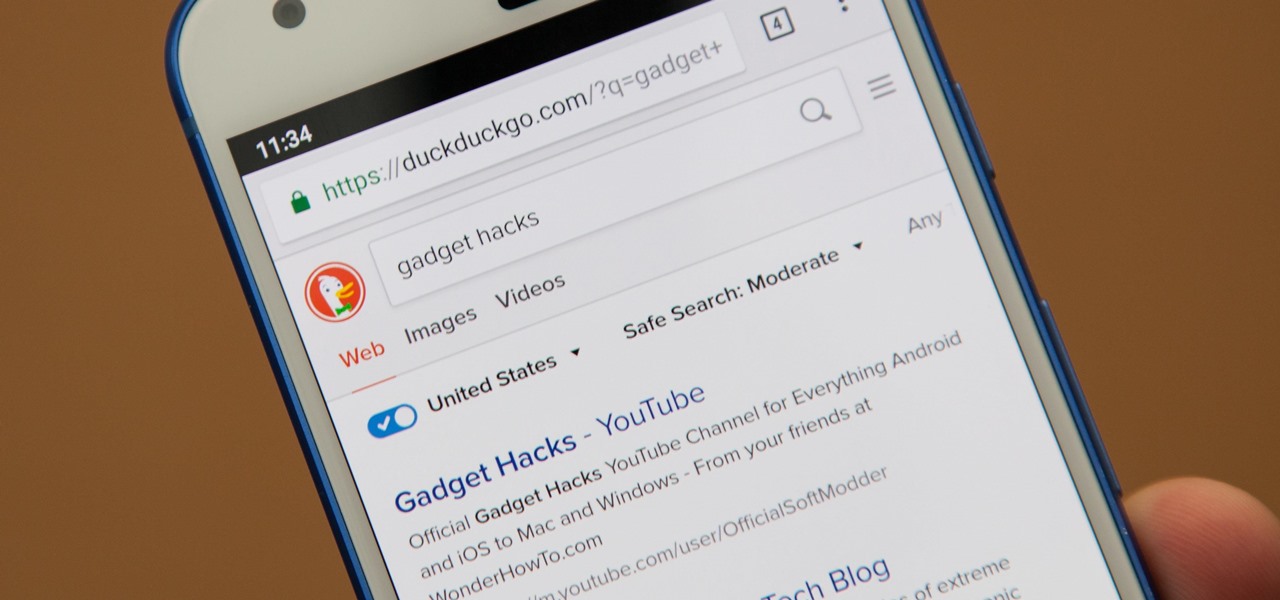
While Google would rather you use Google as the default search engine in Chrome, there's a way to switch to the more privacy-geared DuckDuckGo search engine for all your web browsing needs. With DuckDuckGo, the company does not track anything you search or allow anyone else to track it, so you can effectively search from your iPhone or Android phone anonymously.

Apple Watch owners know the struggle — it's the end of the day, and those rings aren't met. Whether you forgot your watch before hitting the gym, let the battery run out, or just didn't move enough, you could feel the sting of fitness failure. But it doesn't have to be this way. You can actually close your Activity rings yourself; it just takes a little know-how.

Update February 25: The new Sony Xperia flagship has been announced, and it has a new name: The Sony Xperia 1. You can read all of the official specs and details at our full article on Sony's new model.

The macOS 10.14 security update tried to make parts of the operating system difficult for hackers to access. Let's take a closer look at how its new feature works and what we can do to spoof the origin of an application attempting to access protected data.

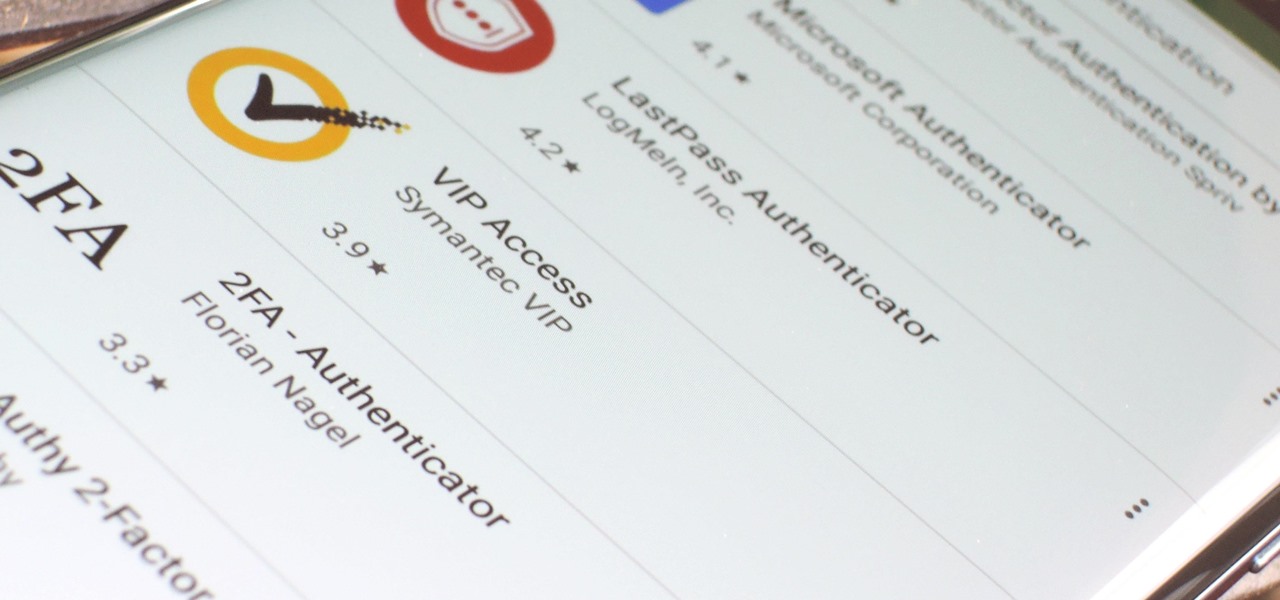
If you want the best two-factor authentication app out there, our pick is Authy. A close second is LastPass Authenticator. If neither of those is to your liking, try Duo Mobile or Microsoft Authenticator. But if you're fine with missing out on great features, then and only then should you look at using Google Authenticator.

Even if your default mobile browser is Google Chrome, you may not want Google to also be your search engine. Maybe you're not impressed with Google's search results all the time, maybe you want a more private search experience, or maybe you just don't want Google's hands over everything in your life. Whatever the case, it's easy to switch from Google to another default search engine.

Binance, a China-based cryptocurrency exchange, is rapidly gaining popularity thanks to the sheer selection of digital currencies you can purchase — Ripple (XRP), Tron (TRX), IOTA, and Stellar (XLM), to name a few — using both Bitcoin (BTC) and Ethereum (ETH). Binance has an iOS app, and there are a couple ways to install it. Either way, you can trade cryptocurrency from your iPhone today.

The threat of an evil access point has been around for a long time, and with the rise of open public Wi-Fi, that threat is often overshadowed by how comfortable we are using third-party Wi-Fi hotspots at coffee shops and public spaces. While we've shown an evil twin attack using the Aircrack-ng suite of tools, MitmAP is a Python tool to configure custom APs for many types of wireless attacks.

Since its debut, retro thriller Stranger Things and its characters have become ingrained in our popular culture — especially the telekinetic Eleven. For cosplayers, it didn't take long before they grabbed their boxes of frozen Eggo waffles, blonde wigs (or bald caps), and pink smocked dresses to transform into El herself.

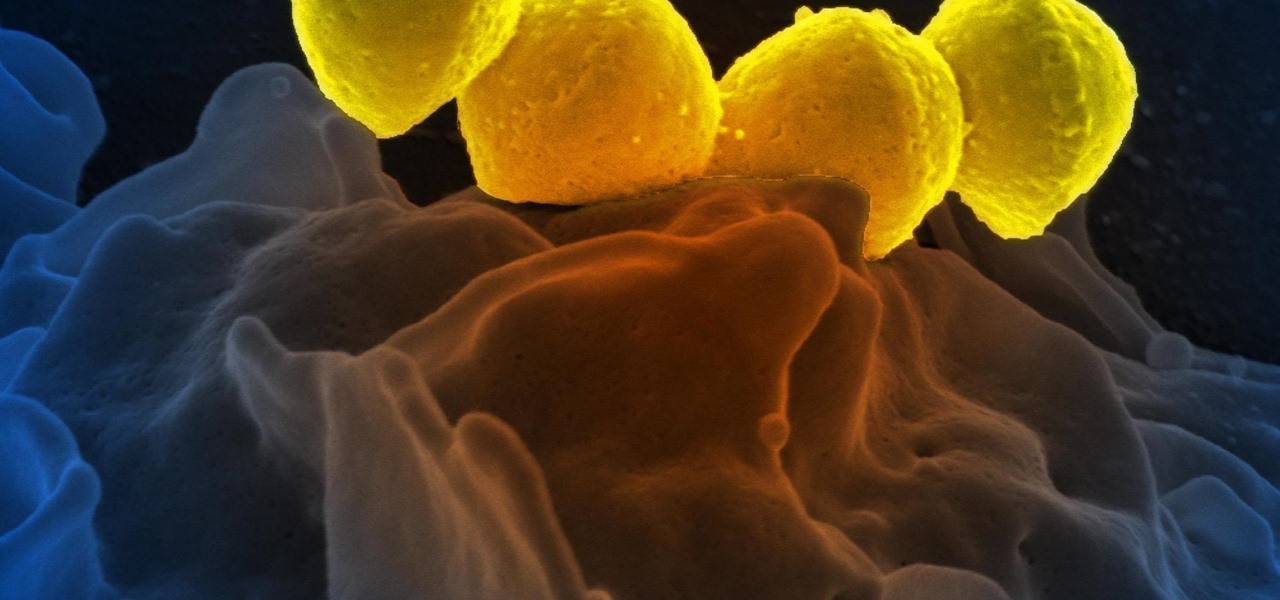
Significant strides have been in the race to find antibiotics to treat superbug infections — those caused by bacteria resistant to the antibiotics used to treat them. Now, an international team of scientists has discovered a new antibiotic produced by a microbe found in Italian soil.

Apple's been hard at work adding new features and finishing touches to iOS 11, and there's evidence of it everywhere. But there's one place where these changes are more noticeable than perhaps anywhere else — Safari.

LOOOK, a Seattle-based mixed reality and development studio, can now peer into the future with their new geotechnical engineering visualization application for Microsoft HoloLens.

New statements from Apple make it clear that they do not believe a hacker, or group of hackers, breached any of their systems. This comes after a recent report from Motherboard that a hacker gang called the "Turkish Crime Family" is threatening to remotely wipe up to 559 million iPhones by April 7.

Google switched things up this year by releasing a developer version of Android N far ahead of I/O, but that's not the only convention they've done away with this year. For the first time, Google will accept name suggestions from the public.

"It just ticked me off," he said. In March 2011, Neil Singh paid $50 to back the Hanfree iPad stand on Kickstarter. The project was funded at $35,000, but production stalled, and the delivery estimates kept getting pushed back.

Good day to everyone, today I will present some basic and advanced concepts that targets sophisticated attacks on the social basis, also I will write about some steps that can prevent this attacks from occuring, basically we will examine Social Engineering from the angle of attacker and victim, some people who are interested in security and work for middle-sized companys can learn and use something interesting from this post.

It would be an understatement to say that Supercell hit it big with Clash of Clans. The game has topped both Google Play and the iOS App Store for years and shows no signs of ever slowing down.

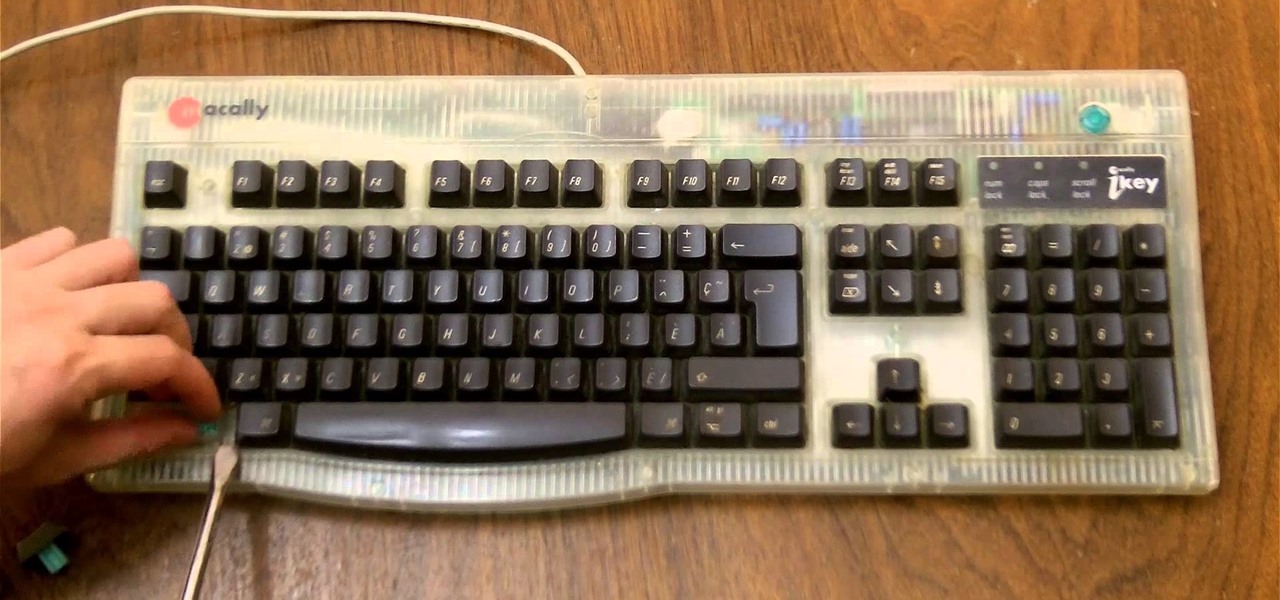
If you need to control a software like Ableton Live while you play guitar then you need a foot switch. In that video I will show you how it is easy to build a foot switch with an old keyboard. Then you will need to configure your software to map the keys to specifics functions like Play, Next, Pause, etc. Enjoy !

To play Minecraft with mods you will need to install Forge. Most people think this is hard to do, not so. It is very simple and in less than 5 minutes you can be playing Modded Minecraft.

There is many different types of stars in the universe. Majority of them are red dwarf stars. However, there are plenty of stars like ordinary stars (like our sun), red giants, blue stars and etc. Furthermore, when you look in the night sky, we see a lot of small and bright stars. What people don't know is that there are stars that are not even completely understood by astronomers and scientists.

Apple released the iOS 8 Gold Master build to developers shortly after their WWDC event ended on Sept. 9th, which is jam-packed with tons of new features for iPad, iPhone, and iPod touch. The public version comes out on Sept. 17th, but if you can't wait to test out iOS 8, you can get it right now.

A raw video shot by Jason McMinn, using a GoPro mounted to a helicopter drone, gives us a look at Apple's new campus, currently under construction in Cupertino.

While some mobile sites have built-in text-resizing tools, many do not. A lot of those that don't won't even let you pinch-to-zoom. That makes it difficult for people with low vision to read small fonts on their iPhones. In some cases, like with photo captions, even those with perfect eyesight suffer.

Foodies and big-time chefs like Thomas Keller go crazy for fleur de sel. This finishing salt appears in fancy eateries and cookbooks the world over, and in the early 2000s, it was not uncommon to see diners in a high-end restaurant sprinkle a pinch of fleur de sel on their plates from their own personal stash.

Facebook is a very useful social media sites. Shared album is a place where multiple users can upload, view and edit photos. Maximum of 50 people could share a Shared album. This video will show you how to create a shared album on Facebook. Hope this feature will be available to all users and countries in near future. Watch the video and Employ the technique in your Facebook account.

LastPass is a password manager that's been around for some time, and has finally made its way over to Android for use with apps, not just websites.

Most people keep their ungodly sexual desires deep inside, only to be indulged in private on their computers. It makes you wonder... what secrets do your neighbors have? What kind of porn are they watching? And how much and for how long? Thanks to some public (and anonymous) data, you can now find out.