Are you always afraid to apply lashes by yourself, or that you never get it right? Do you find that your false lashes fall off in the middle of the day? Watch to find out how to apply fake eyelashes or falsies! This is a live step by step tutorial, perfect for beginners!

Step 1: Tie a Ponytail Use clear elastic to tie a ponytail and divide the ponytail into 2 segments.

In this video clip series, our expert will explain the use of fake (false) eyelashes, how to apply them, the types of glue needed for false eyelash application, as well as tips and techniques for trimming false eyelashes.

Did you get duped into buying fake MAC cosmetics? Don't let it happen again. This two part how to video teaches you to identify real MAC makeup from the fakes.

In this great video series our expert Ryan Larson, a great jazz pianist, shows us not only how to instantly better our improvisational skills but also how to read and write music on paper. He even ventures to teach us a to play a song walking us measure by measure through it. You are only able to improvise with as much as you know so make sure the next time you're jamming with your friends you wow them with how well you know your instrument, whatever it might be!

This makeup palette is the Forest Fairy Sprite Wood Nymph created by MissChievious. Begin with regular foundation. Get a little dark gold and golden cream eyeshadow with a knife & mix it into foundation. Take a large makeup blush type brush & put green shadow around top & sides of forehead blending it up into hairline & around the sides of face, continuing slightly onto the cheek hollows as you might do a light contouring. Take golden cream & dark gold & mix them before applying to center of ...

Well, we have some potentially good news for those wanting to experience Magic Leap. The ultra-secretive company seems to be planning a big year in 2017.

Whether or not The Purge franchise will be as successful as Friday the 13th, A Nightmare on Elm Street, Halloween, or even the Saw movies remains to be seen, but it's definitely winning in the Halloween costumes department.

If you are anything like me, you have a knack for taking silly selfies of yourself, i.e., taking scotch tape and wrapping it around your face to make yourself look like the blob, or perhaps you like taking selfies of yourself in weird or unusual situations doing weird and unusual things.

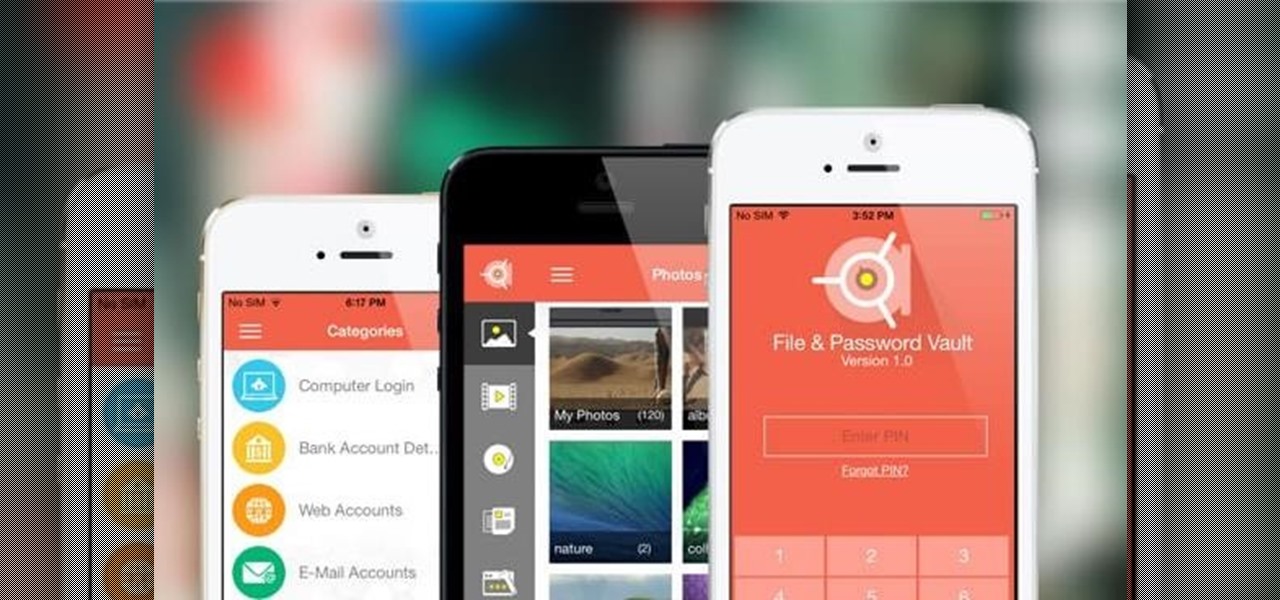
In the weeks before Apple officially released iOS 8, consumers were abuzz over rumors that a new feature would password-protect your photos and text messages from prying eyes. Unfortunately, this ended up being untrue, though we did cover some alternatives to protecting your important information using some built-in features and a third-party app. Now, there's a new iOS app that can do it all.

Every year, some overly ambitious neighbor down the street amazes the crowds with his DIY illusion costume. While these costumes certainly require more work than pulling a mask over your head, they do have that wow factor that others lack.

We live in a time where privacy is rare and our files can be easily accessed by just about anyone. Having your phone protected by a passcode is great, but if someone figures it out, they can easily access anything on your phone.

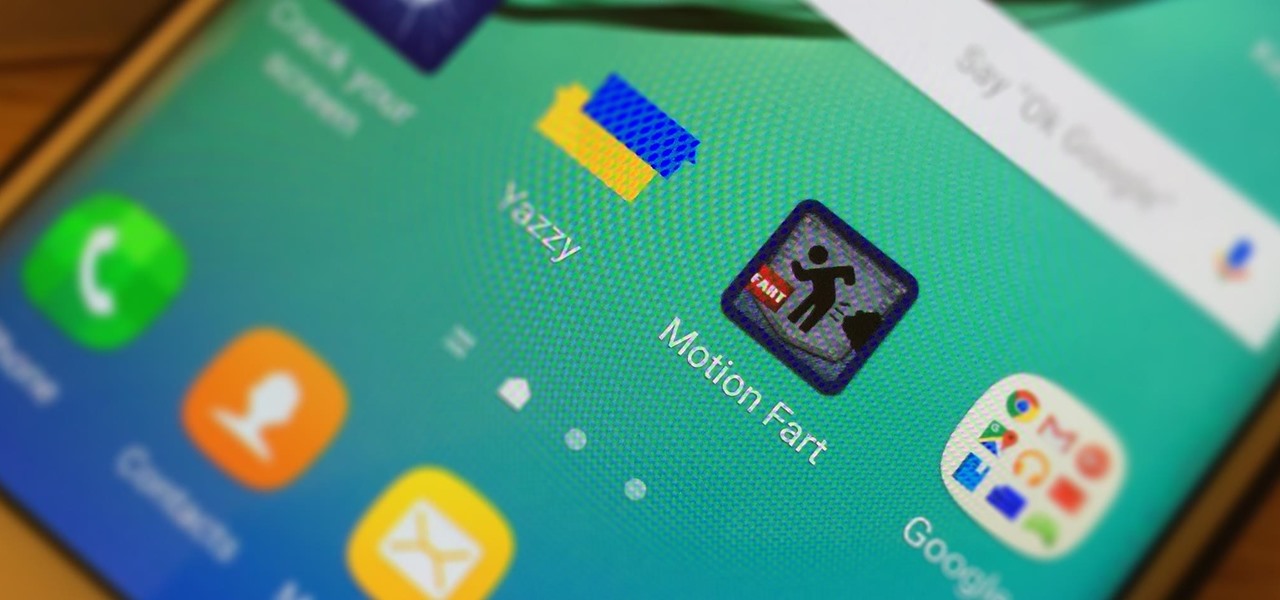
April Fool's Day, aka National Screw with Your Friends Day, is finally here. You can always pull a conventional prank, like strategically placing a whoopee cushion on your mom's chair, but that joke has been exhausted generations before smartphones were around. We live in a day and age where smack cam is the new level of pranking, so it's time to step your game up, novices.

Poison ivy, poison oak, and the lesser known skin irritator, poison sumac, can all cause a conundrum in the search of itch relief: to scratch or not to scratch. Fortunately, there are a number of home remedies one can try to help alleviate the itch(ing), with many like coffee, a banana, baking soda, or mouthwash likely already in-house for most.

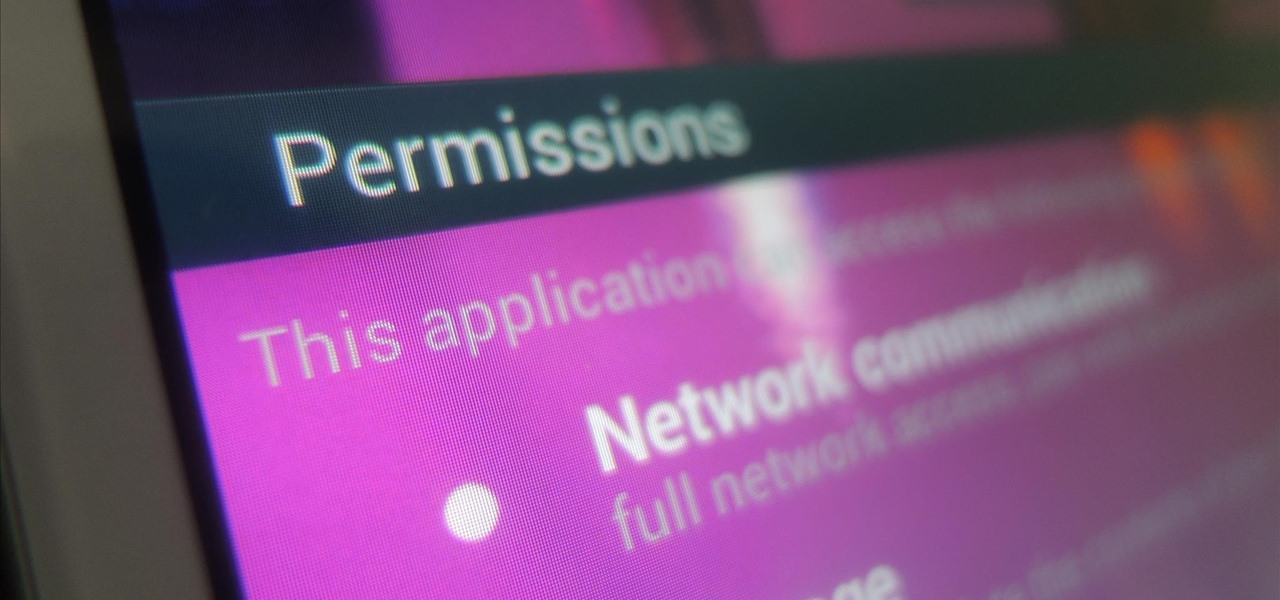
While we're usually responsible for leaking our own private information through mediums like Facebook, there are other times when we mistakenly and unwillingly allow certain applications to scour through our personal data. Some apps may have enabled permissions for internet access, thus allowing it to share said data with its external servers.

One thing that gets overlooked on Facebook is the amount of videos you can watch, and I'm not just talking about videos uploaded directly by Facebook users—I mean everything ever shared—YouTube, Vine, Instagram, Vimeo, etc.

It starts innocently enough, with a nosy friend hovering over your shoulder to see what you're texting. Somehow, that doesn't satiate their inexplicable thirst for curiosity, so the first chance they get, they're rummaging through all of your super private photos—even though you told them not to.

Learn the best way to fake a shot and make yourself open to shoot a three pointer by practicing this shot fake to lateral slide to shoot the three drill.

In this series of spooky videos about how to scare the heck out of your friends and neighbors, our haunted house expert tells you everything you need to know about setting up your own haunted house. Matt Cail, designer and director of the University of Washington's campus haunted house, shares the tips and advice he gained from putting the fright to university students. He begins by discussing goals for a haunted house then tells you how to achieve them with the seasoned advice of someone who...

When you look at the top corner of your phone, what do you see? Upon upgrading to Android 11 or iOS 14, you'll see either "5G," "5G+," or "5G E" if you're connected to the right network. But what exactly do these symbols mean? They indicate not only if you're using 5G, but also what type you're connected to.

If running out of battery while out and about weren't bad enough, the experience is a lot more painful if your iPhone has a semi-untethered jailbreak. With that kind of jailbreak, when the iPhone dies, all of the mods will be disabled after the device powers back up. Fortunately, instead of restoring your jailbreak and tweaks manually after recovering from a critically low battery, you can avoid it altogether.

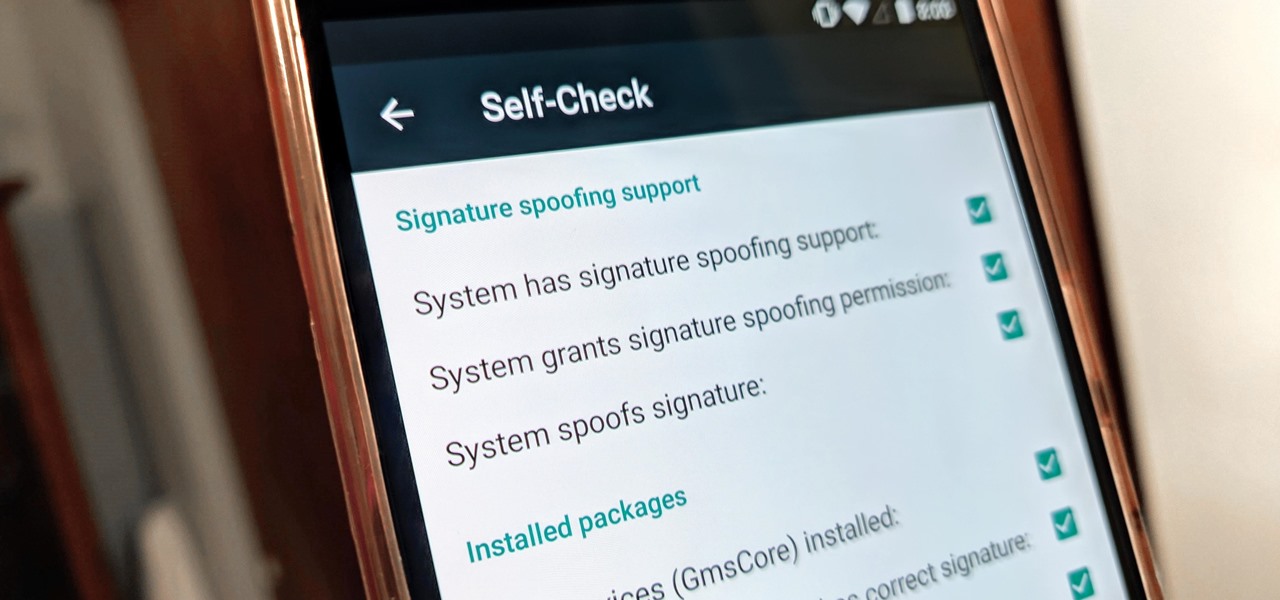
With all the talk about privacy concerns recently, Google's name keeps coming up because they are a very data-driven company. As an Android user, they know basically everything about you based on your device usage. That can easily scare some people off who are worried about their privacy and security. You do have some say in what personal data Google controls, but what if you want total control?

The prospect of loss or theft is something we constantly live with. Stolen iPhones fetch a premium price on the black market for parts like OLED display assemblies, frames, and charging ports. Making matters worse, if someone were to steal your phone, they could simply turn it off to avoid anti-theft features like Find My iPhone.

Even in augmented reality, Wile E. Coyote still can't catch the Road Runner. The latest AR experiment from developer Abhishek Singh brings the classic Looney Tunes duo into the real world.

According to a new study from the Reuters Institute and the University of Oxford, people are getting their news from ... unexpected sources. Put away your CNN app and stop checking the New York Times because a familiar app is now keeping you up to date on current events: WhatsApp.

Update: Twitter user Benjamin Geskin (@VenyaGeskin1), known for his iPhone renders, tweeted on Monday alleging that the leaks are fake:

If you ever get asked to update your WhatsApp to your favorite color, don't. It's probably spam. According to Reddit user Yuexist, a new WhatsApp adware is going around disguised as an update.

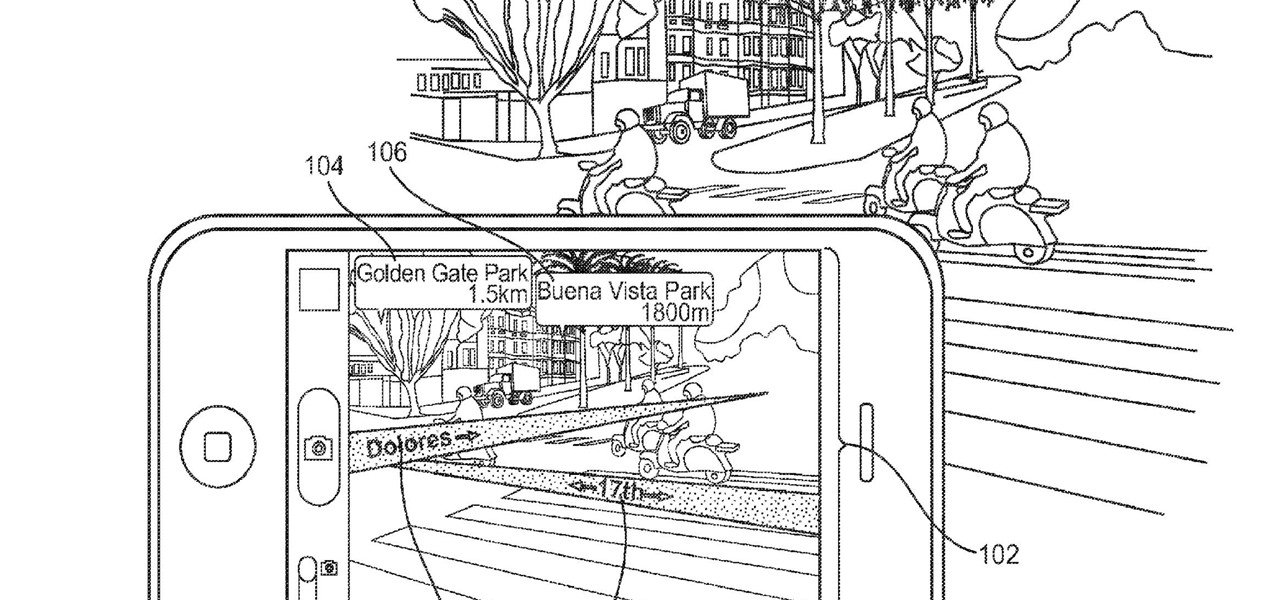
Apple is combining internal and external talent in an effort to give them in edge in the augmented reality market, though we still don't know what form their foray into alternative realities will actually take.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

If you lend someone your phone, even if it's just for a second, there's a chance they can enter an app and see something you'd rather they didn't. Whether it's a personal email or a private photo, there are plenty of reasons why you'd want to keep snoops out of certain apps.

How can you tell if the pair of Ray-Ban Wayfarer sunglasses that you are about to buy online are not a fake? Follow these 9 simple steps to verify the authenticity of your purchase. Always ask the seller to use the youVerify app prior to purchase. It's Smarter Selling & Safer Shopping.

The stereotypical geek is not good at sports. Think about it, we’re known for spending time in dark basements doing weird stuff that has nothing to do with running around and being active. So we’re known for our inability to play sports, but I wouldn't call it an inability so much as a creative way of passing these challenges by the skin of our teeth. Examples:

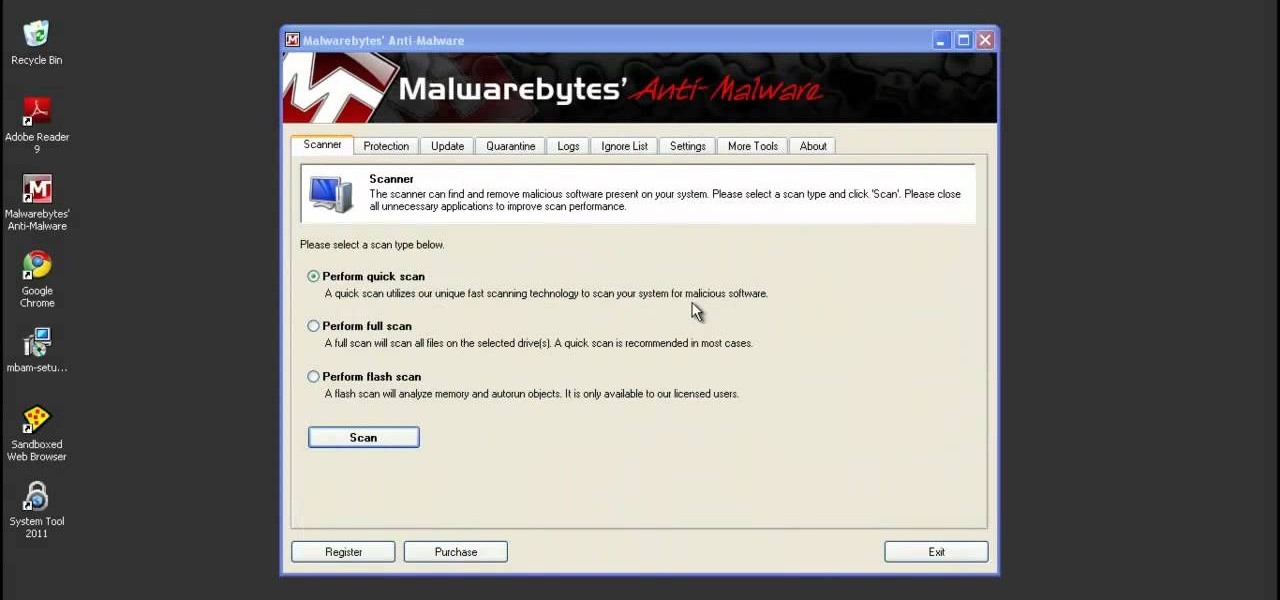
System Tool and System Tool 2011 are the most widespread fake-antivirus rogues on the internet today, infecting countless machines. This video will teach you how to uninstall both warez completely, returning your computer to blessed normalcy.

Remember Michael Jordan? He may not be in the news as much today, but he's still one of the greatest basketball players that ever existed — nobody can doubt that. Professional basketball just isn't the same without MJ, but if you'd like to see him in action again, all you have to do is prime your pencil and pick out your paper and DRAW!

This video speaks to everyone who has ever bought anything online, or in fact, anyone who has ever bought anything period. How do you know what you're getting is genuine? Is it a fake product? Is it stolen goods? Is it impure?

What's better than one prank? Five pranks! This video from the notorious Kipkay provides five fantastic, funny, and facile pranks to pull off on your friends and family… maybe even your enemies.

Release your inner wild thing with a costume based on the classic children's book. You Will Need

In this video music lesson, an expert jazz musician will demonstrate how to read through a fake book composition in B major. He will demonstrate how to play the various measures and sections of the fake book composition on piano, as well as how to improvise while playing.

The price of hacking Wi-Fi has fallen dramatically, and low-cost microcontrollers are increasingly being turned into cheap yet powerful hacking tools. One of the most popular is the ESP8266, an Arduino-programmable chip on which the Wi-Fi Deauther project is based. On this inexpensive board, a hacker can create fake networks, clone real ones, or disable all Wi-Fi in an area from a slick web interface.

Another branding team has stepped up to the bar to order a tall glass of augmented reality for its marketing campaign, this time through a mobile app for Rémy Martin VSOP Limited Edition cognac.