
How To: Fake super powers
Learn how To fake super powers. Helpful for filmmakers on a low budget. Part 1 of 2 - How to Fake super powers.


Learn how To fake super powers. Helpful for filmmakers on a low budget. Part 1 of 2 - How to Fake super powers.

Having problems with your anti-virus software on Windows? Learn how to delete the fake virus software Personal Antivirus! Personal Anti-Virus is NOT a legitimate anit-virus software and will use spyware to steal info from your computer.

Learn how to make fake tattoos with a ballpoint pen and highlighters.
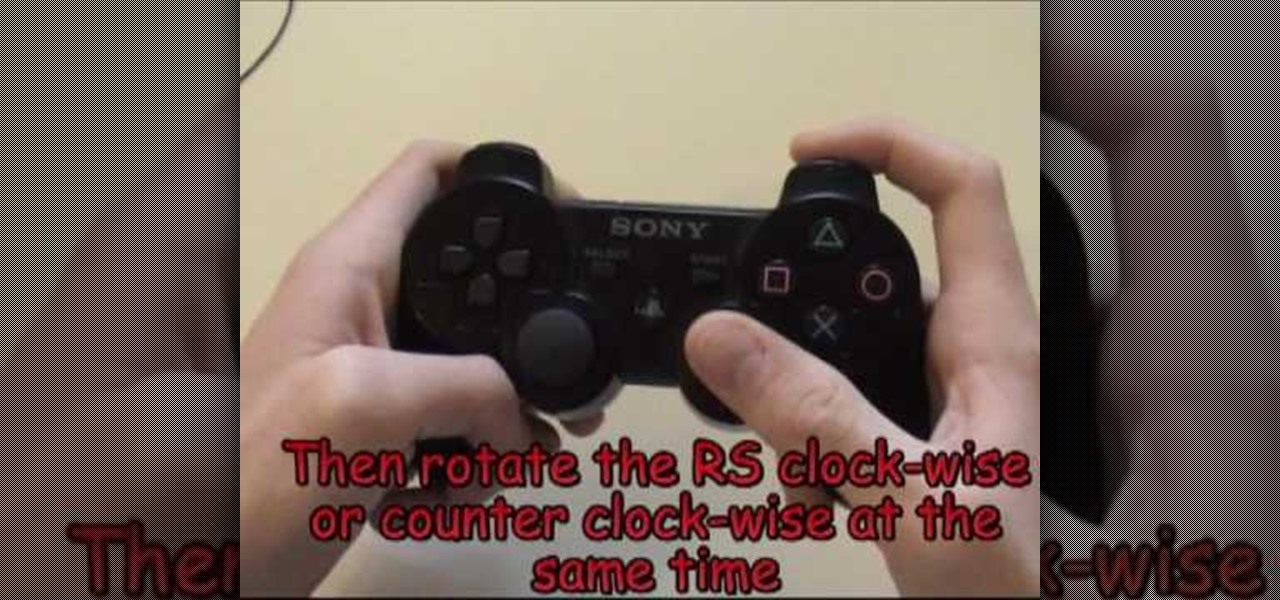
This is an advanced tricks tutorial on juggling for Fifa09 for Playstation 3. The step by step covers the following tricks and techniques for the FIFA 09 soccer video game:

Learn how to apply your own stage makeup including foundation, fake eyelashes, eye shadow, bronzer, blush, lipstick and more with expert makeup tips in this free online theater production video series.

This tutorial shows you how to use 3D Studio Max to create a 4D camera move from a 2D still photograph. You create the illusion of movement with a few simple computer tricks.

In this how to video, Sandy from Afloral.com shows you how to make a wedding bouquet using a silk bouquet arranger. This is a great tool to use for any kind of fake flower arrangement. Watch this tutorial and yu can arrange your bouquets with a silk bouquet arranger in no time.

This video tutorial demonstrates how to use Encapso K silicone to create a realistic floral display. Learn how to make a lasting artificial flower arrangement with fake flowers and silicone rubber to mock water.
This video demonstrates how to use Encapso K to create a lasting faux ice display. Encapso K is a soft, clear silicone rubber that perfectly simulates water. Learn how to sculpt mock ice for a beer bottle sculpture.

Find a good work area where you can sit down and be comfortable. A kitchen table works perfectly for this. Be sure to cover the surface of your table with a plastic garbage bags and a thick layer of newspaper to soak up spills and prevent damage to your table's surface. Get all your supplies ready at hand. You don't want to be hunting for them mid nail removal. Have them all spread out in front of you on the table. Using a pair of nail clippers, cut the acrylic nails down as short as possible...

Cover brows with wax or glue stick and concealer that is a lot lighter than your skin). Place some of the much lighter concealer under your eyes. Stroke concealer all over face for an extra layer. Apply full coverage foundation. Set makeup with powder. Use something that'll look very fake when done. Add cream blush product in bronze shade. Apply with finger to warm it up; apply to cheeks, forehead & nose. Use mineral type skin highlighter all over face. Paint on eyebrows with black liquid eye...

You’d like to be strong and supportive for your wife in the delivery room… if only your knees would stop knocking. Keep both of you from freaking out with these tricks. Watch this video to learn how to stay calm when your wife is in labor.

If even the bats are intimidated by the clutter in your attic, it’s time to tackle the mess. Watch this video to learn how to clean out your attic.

Let our expert show you how to do super scary Vampire Halloween makeup! A vampire Halloween costume is easy, but getting the makeup right is key. Our expert will show you how to apply the various layers of vampire makeup, how to add gray shadows, how to add creepy bite marks on your neck and even how to add fake blood special effects to your lips and chin. This is great makeup for a fun Halloween party or even a Haunted House!

How to scare and prank your friends with a fake virus.

F for FAKE. This video has been labeled a "Faux-To". Commonly contested as bogus science, we believe this video to be a hoax. What's your opinion? Comment below.

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.

Get Out absolutely tore up the record books this year. And the wildest thing about it? It did so with the most ordinary looking characters and props ever (hence the shoestring $4.5 million budget). Which makes it a godsend for the time- and cash-strapped come Halloween. With Get Out, Jordan Peele is the first (and only) African-American writer-director with a $100-million film debut under his belt. The film is also the _all-time highest domestic grossing debut based on an original screenplay ...

Let's face It ... Pennywise is going to be the Halloween costume to beat this year. It's terrifying, simple enough to pull off, and with the original movie's gargantuan box office gross and the hit status of the sequel, released in September, everyone and their pet dog will get your costume.

Smartphones are almost always connected to the internet, so it stands to reason that they can be hacked remotely. Or perhaps a jealous boyfriend or girlfriend got hold of your device physically, in which case they could've potentially installed a keystroke logger, a virus, or any other type of tracking app to spy on you.

Your brain holds a lot of precious information and is capable of great feats. However, there's one quality that doesn't lie among its strengths—memory security. Yes, that's right, your brain can be hacked, and it doesn't take a psychologist to do it. Anyone with the right know-how can change your memories for their own personal benefit, and you can do so to others, too.

It's that time of year when high school students say goodbye the their past four years of coddling, ready to enter the "real world" and the next chapter of their lives—college.
You don't have to spend a lot of money on jewelry, crystals and pendants. In this video from Tap Plastics, you'll learn how to use their brands of Platinum Silicone and Clear Lite Casting Resin to create artificial jewelry. It won't fool the pros on a close examination, but it can still be impressive-looking stuff at a fraction of the cost of real jewelry.

In this sports how-to video, Farmington HS boys basketball coach Shane Wyandt and team demonstrate 1-ball, ball handling drills. One ball handling drills are great for kids who are beginners to the sport of basketball. Follow along with this video and learn to do the speed dribble, change of pace dribble, fake crossover/stutter, crossover, between the legs, behind the back and the pivot drill with both the left and right hand.

This tutorial video will show you how to apply a fake beard using makeup and other househould products. This beard could almost pass for real, except for the fact that it's made of tea.

A tutorial on some of the most basic tricks. Two-in-one-hand shower

This is a tutorial on the windmill juggle. Requires knowledge of a few beginner's techniques. An advanced juggle.

Learn to hide icons and use paint to prank friends. This prank makes friends think their computer froze or the have a virus.

A movie on how to prank your friends with fake ranch dressing. Use this as inspiration for one of your April Fools Day pranks!

This video is of the late 19th Century dance called the Butterfly. The Butterfly is where a woman/man has fake butterfly wings attached to their arms and dances with them on. This video is only a demonstration, and unfortunately it does not give step by step instructions.

Being a male, I may be the only one among my gender stating this, but I'm sick of girls using Halloween as an excuse to dress scantily. Why can't more girls skip the playboy bunny costume and get this gnarly? Below, ten badass Halloween looks executed by girls only...
There's an epidemic on the Internet, and the disease—Facebook. It's an addiction comparable to a hot cup of coffee in the morning or a soothing cigarette throughout the day—in worse case scenarios, a hit from the crack pipe. If you're on Facebook, you know what I'm talking about. You're addicted to finding out what's going on with your friends and addicted to telling those friends everything you're doing. You can't stop, even when you're at work.

Deep fakes, the art of leveraging artificial intelligence to insert the likeness and/or voice of people into videos they don't otherwise appear in, typically focus on celebrity parodies or political subterfuge.

Over half of all Americans have listened to at least one podcast, and that number is growing every year. With over one million podcasts and 30 million episodes in existence, there's no end to discovering new voices expounding on a range of topics.

It's been proven that hackers can manipulate your screen with fake taps through specific exploits, so they can potentially hit the "Grant" button when you get a superuser request. This is the last thing you'd want to happen since the malicious app from that point forward has full system privileges. Luckily, using a fingerprint to lock your superuser requests can prevent this.
Canary tokens are customizable tracking links useful for learning about who is clicking on a link and where it's being shared. Thanks to the way many apps fetch a URL preview for links shared in private chats, canary tokens can even phone home when someone checks a private chat without clicking the link. Canary tokens come in several useful types and can be used even through URL shorteners.

As the stigma of online dating fades and swiping potential suitors on your phone becomes the new norm, one very real issue that you may have to deal with is catfishing: the act of being deceived by a fictional online persona. Although dating apps do their best to weed out fake accounts, a few of them slip through the cracks and take advantage of innocent people just looking for a connection.

The newest version of macOS has arrived. While everyone's mind is being blown by Mojave's groundbreaking new Dark Mode, we'll be taking advantage of its insecure file permissions to establish a persistent backdoor with a self-destructing payload that leaves little evidence for forensics.
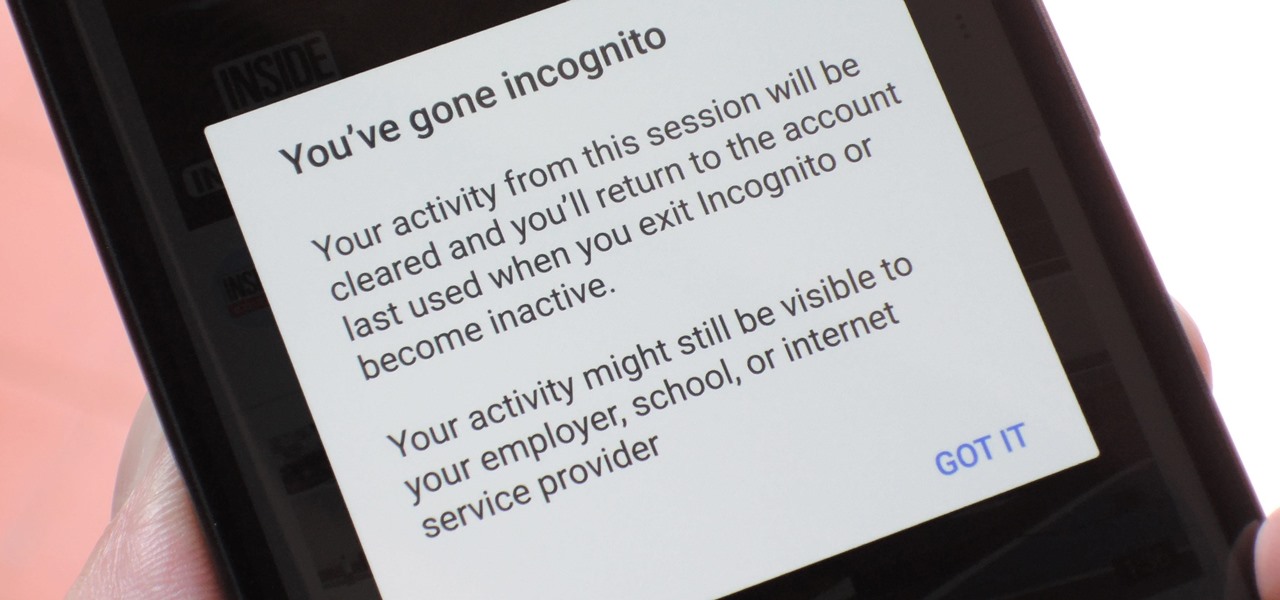
Incognito Mode is a privacy feature that was popularized by Google Chrome, and it recently made its way to GBoard. Now it's coming to the YouTube app to help make your video watching experience truly private.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.