In this tutorial, we learn how to use uTorrent on Windows Vista. First, download uTorrent from Download. After this, go to TorrentBox and find what you want to download through the site, then download it. After this, it will start to download onto your uTorrent software. When it is done downloading, you will be able to open up the file and access the media that is inside. After this the program will start to seed, which means it is being shared with other people on the internet. If you don't ...
Let your fingers do the walkin' and give the Yellow Pages a piece of your mind. In this tutorial, learn how to perform a very cool magic trick that will impress everybody.

In this tutorial, we learn how to find your computer's IP address. An IP address is used to know the exact location of someone using a computer with internet access is located at. First, turn your computer on and go to your main desktop. Then, click on "start", (which is located on the lower left hand side of the tool bar at the bottom), then click "run" and once that opens up, type "cmd" into the white empty space. Hit "ok" and when this comes up, type in "IPConfig" and hit "enter". Your com...
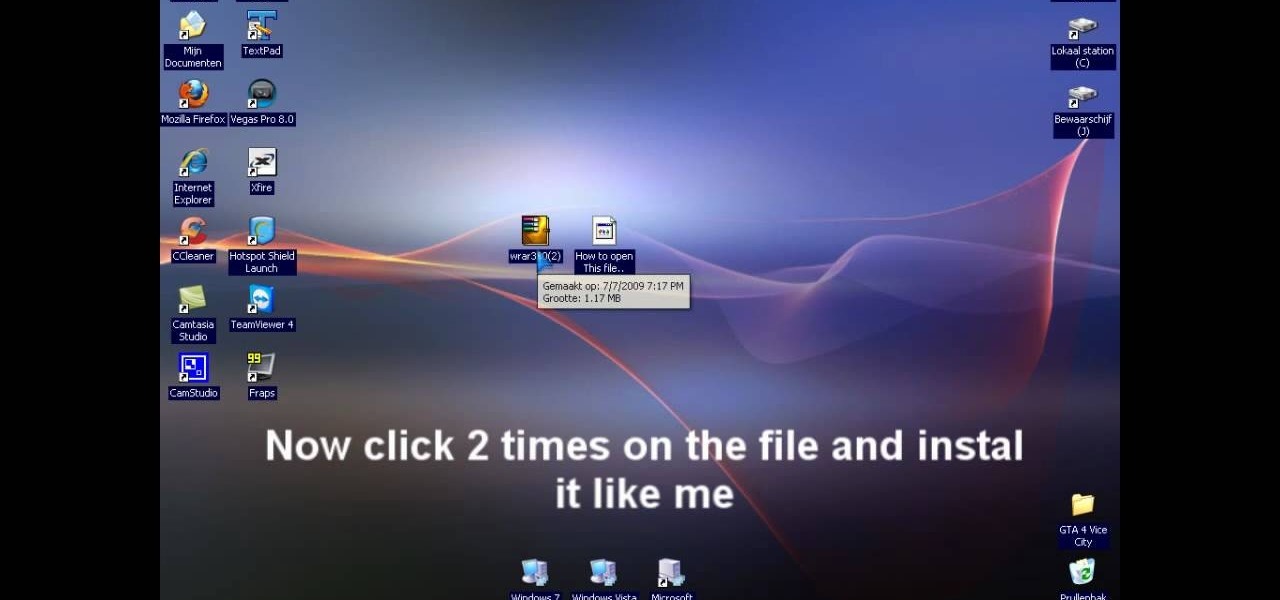
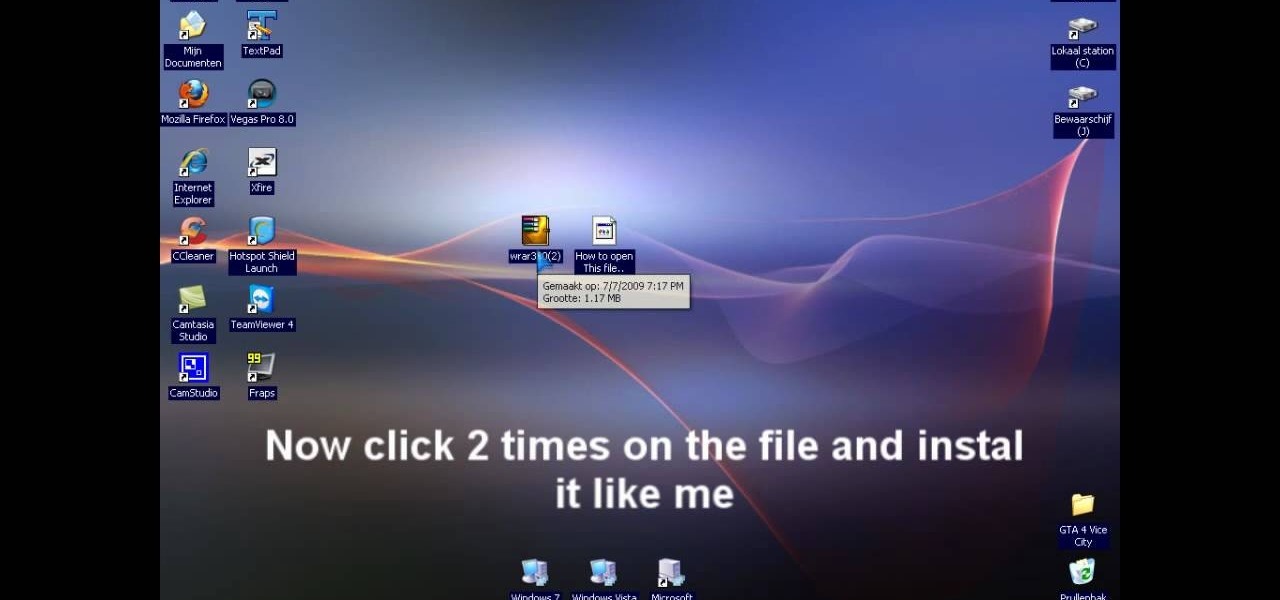
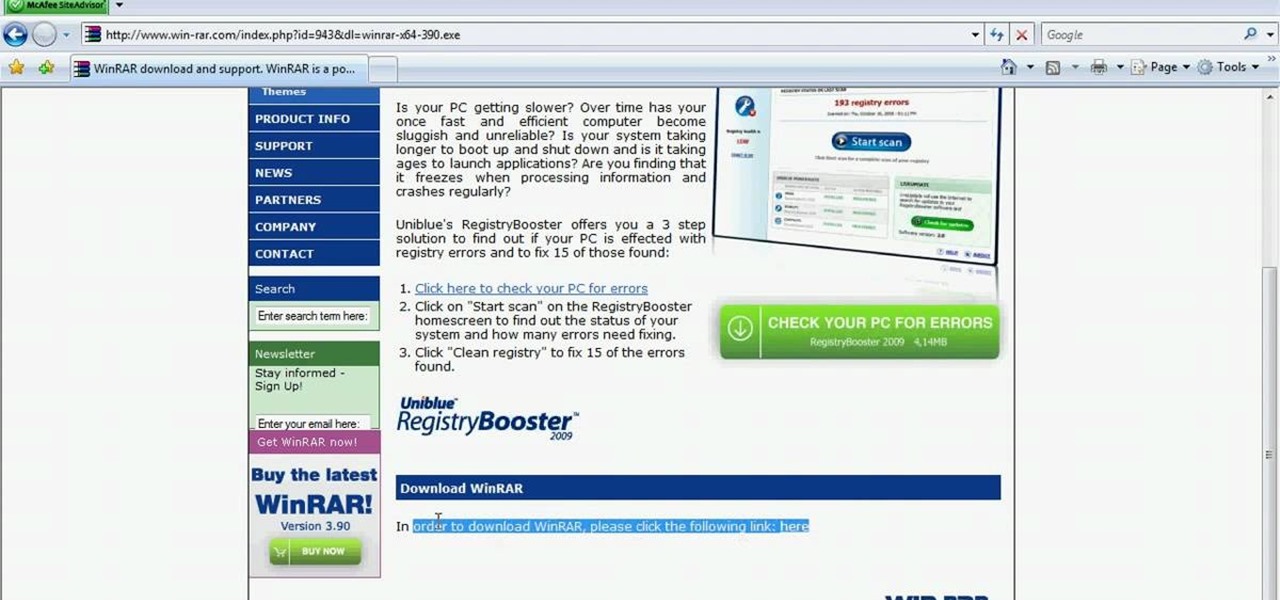
In this video tutorial, viewers learn how to extract .rar files. Begin by opening your internet browser and go to Google. Search for Winrar and select the 3rd result. Download and save the file. It is recommended to save it to the desktop to find it easier. Double-click on the file and follow the instructions to install it. Click Install and check all the file types for the program to be associated with. Once finished, open a file, select Extract To and choose the destination to save it. This...

Already an impressive gaming machine, the Xbox 360 can be modified to play a wider variety of games. This instructional video demonstrates how to flash your Xbox 360 to play downloadable games from the Internet. This method only works on the Hitachi v0078fk drive and will void your warranty, but think of how cool it would be to pull this off.

The Dropbox utility can automatically sync your computer files with other devices each time you save them. In this tutorial, learn all of the steps you need to sync files with Dropbox.

Jerky is not only delicious but it is a great way to bring a protein rich energy snack with you anywhere. This video will how you how to make a great beef jerky at home. You will want a think slice of meat and you can create your own fantastic flavoring.

It might not be on the top of your to-do list but activating your Windows XP is simple and only takes a moment. No need to put it off any longer. You just need your product key and your computer and your ready to go.

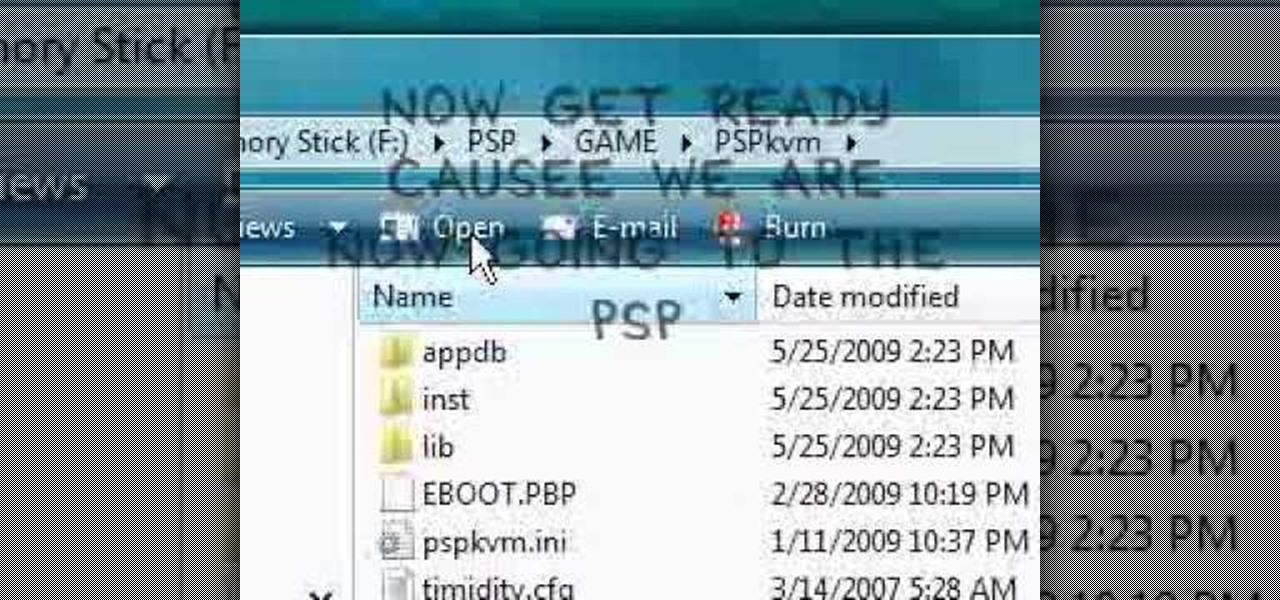
In this video the instructor shows how to play java games on your PSP. To play java games on your PSP you will have to download and install the PSPkvm. Now plug in your PSP and go to my computer and put the downloaded folder in the PSP/Game folder. Now download any free java game from the Internet. Now open your PSP and choose the game by looking for the PSPKVM. Now open that file and it prompts to install it. Install it using install from memory stick option. Now open that application and ch...

Learn everything you could possibly want to know about the internet, multiplayer game Evony. Watch this video tutorial to learn how to max out prestige growth in Evony.

Check out this supernatural tutorial video that offers 7 tips on getting started in becoming a paranormal investigator. Just follow these simple steps:

Once in a great while something comes along on the internet that’s so unbelievably simple and yet works so well. Twitter is one of them. On the video conferencing side, now we have MeBeam. MeBeam, which requires no software or drivers to be installed, is a web application that will permit you and up to 15 of your closest friends to hold a video/audio conference (provided you and said friends all have webcams or, at the very least, microphones). For further details consult this simple how-to!

Check out this video tutorial to see how to conduct a magic floating boat science experiment.

Our expert, Joyce Moreno, shows you how to give a fantastic guy's haircut. Learn how to shampoo, condition, and rinse men's hair. Also, learn how to section and part men's hair for an even haircut. Joyce also shares advice about how to style men's hair.

Baklava is a wonderful dish for any dinner party you might be having. It is not difficult to make and does not require many ingredients to taste fantastic. In this video series you will learn how to make baklava from scratch including how to put all the ingredients together, why you should do certain things such as cut off the edges before you cook it and how to make the syrup mix to put the flavor factor over the top. So have fun and enjoy your just desserts!

To become a Victoria's Secret model, use the Internet to locate agency Web sites and register photos on-line to be viewed by modeling agencies. Build a portfolio and gather head shots for becoming a Victoria's Secret model with tips from a modeling instructor in this free how to video on modeling.

With the iPhone, it's possible to share URL's you find on the internet with your friends. Take a look at this tutorial and learn how to share your URL's through the iPhone.

Attention goths! Searching the Internet for new makeup ideas? Adora batBrat is here to help you. In this video, learn how to apply cosplay inspired goth makeup for an outrageous look!

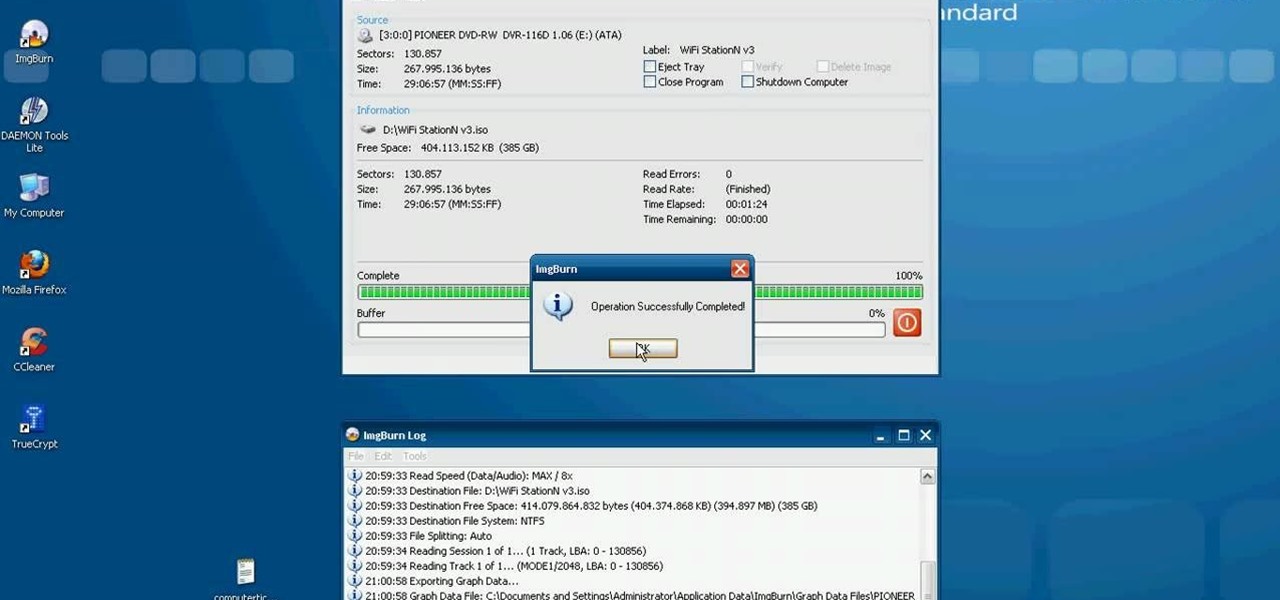
This video tutorial from computerticket shows how to use Daemon tools and Img Burn applications. First, install Daemon Tools and ImgBurn programs. Both can be easily found using internet search engine.

In this how to video, you will learn how to use Daemon Tools Lite. First, download Daemon Tools Lite and install the program. Next, download an ISO file from the internet. Once that is done, mount it on to Daemon Tools. To do that, open the program and then right click on it. Select Virtual Drive and set the number of drives to one. Next, select mount image and find and open your ISO. Once that is done, you are ready to use that file as if it were an actual CD inside an actual optical drive. ...

This video tutorial from agseo presents how to unlock applications in Facebook social internet network. For more detailed information go to www.agseo.blogspot.comTo unblock Farmwille and other applications on Facebook social network login to your Facebook account.From top menu Account drop-down list select Privacy Settings.Then select Applications and Website from the newly opened window.Select Blocked Applications (click on Edit Blocked Applications button).A list of all blocked applications...

In this video tutorial, viewers learn how to unzip .rar files using Winrar program. Begin by opening your internet browser and download the program from the link in the video description. Wait for the time to pass and click Download. Select 32 bit or 64 bit, depending on your computer. Open the file and install the program by following the instructions. Once it's installed, select the file that you want to unzip. Right-click on the file and select Extract All Files. This video will benefit th...

How to track an email address. Useful if you meet someone who says they are from somewhere e.g. LA as given in the video and you don't believe them. Go to the Rate a Bull site type in their email address and then hit return or 'find them'. The site will give you options to see information about them on the internet, MySpace, Facebook or other site or track the email. The site gives instructions on how to track the email via outlook, outlook express and other mail programs and the video shows ...

In this video tutorial, viewers learn how to hide the call ID on an iPhone. The iPhone is a line of Internet- and multimedia-enabled smartphones designed and marketed by Apple Inc. This task is very simple and easy to do. Begin by gong to your main menu and select Settings. Scroll down and select Phone. Then select Show My Caller ID. Slide the bar to OFF. Now whenever the user makes a phone call, the receiver will not be able to see their ID. This video will benefit those viewers who have an ...

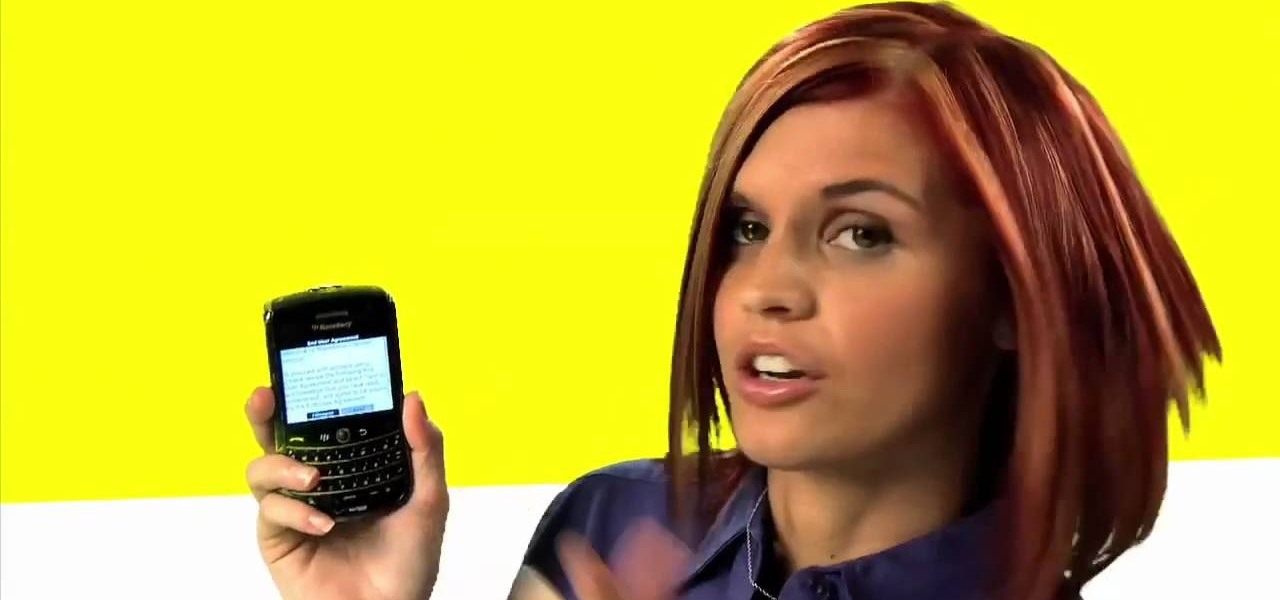
The whole point of purchasing a smartphone is the access to your e-mail and the Internet, right? Well, check out this tutorial if you are having trouble setting up your e-mail account on your new device. In this video, Dana from Best Buy shows you exactly how to set up your e-mail.

There's no better way to cheat a flash game on the internet than with Cheat Engine. Everybody's using it to hack their favorite games on Facebook, MySpace, and all of the other popular gaming sites. Everybody's hacking… except you! Because you don't know where the Cheat Engine 5.5 download is. Well, it's really easy. Just Google it! You just need to go to http://www.cheatengine.org or go directly to the download section to get the Cheat Engine 5.5 download. Then, hack away.

With the LG KU990 Viewty, you can take and view a crystal clear photo. Packed with high-quality camera features, this camera phone enables you to capture a high-definition image using a 5 MP camera lens certified by Schneider-Kreuznach and edit your photo on a large, clear, 3-inch display just like a professional photographer.

With the LG KU990 Viewty, you can take and view a crystal clear photo. Packed with high-quality camera features, this camera phone enables you to capture a high-definition image using a 5 MP camera lens certified by Schneider-Kreuznach and edit your photo on a large, clear, 3-inch display just like a professional photographer.

Print what you want, how you want. While browsing, choose the content you want then edit and print exactly what you see on your screen..

On Monday, the social media giant Facebook suffered a massive outage that, as of this writing, is still in effect.

You're out and about, and nothing on your iPhone will load. A glance at the settings shows a saved Wi-Fi network with full bars that your iPhone had connected to automatically, but you're not getting any internet. If you've experienced this, you're not alone, and there's something you can do about it. You'll even increase privacy and security on your iPhone in the process.

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

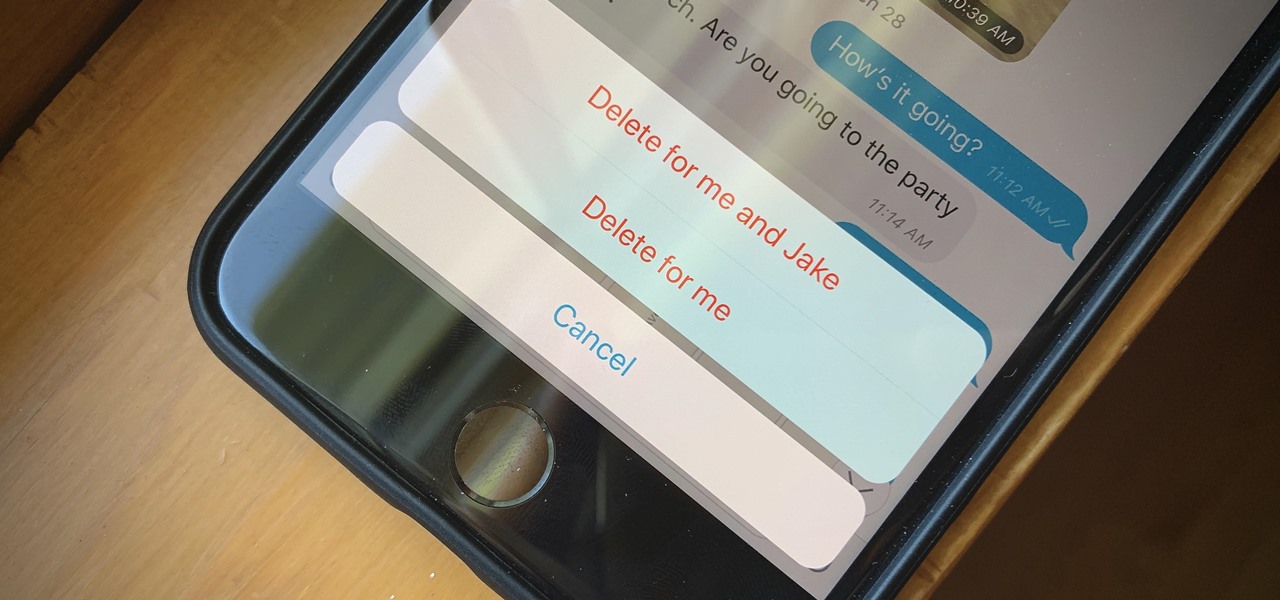
If you're looking to keep your conversations private, look no further than Telegram. Its cloud-based chats are secure and its optional end-to-end encrypted chats even more so, but you can't really prevent someone in the conversation from sharing your messages. However, you can lessen that chance by taking back your messages, deleting them for both you and the other end of the discussion.

With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

With just a few taps, an Android phone can be weaponized into a covert hacking device capable of running tools such as Nmap, Nikto, and Netcat — all without rooting the device.

Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

One of the biggest advancements in the new iPhone XS, XS Max, and XR is the dual SIM functionality that will let you use two cellular networks at once. Like Sinatra, however, Apple is known to do things its own way, so their dual SIM setup is a bit different than you might think.

Net neutrality is dead and your internet service providers can collect all the data they want. While VPNs are a great way to protect some of that privacy, they're not perfect. There is another option, though, called Noisy, which was created by Itay Hury. It floods your ISP with so much random HTTP/DNS noise that your data is useless to anyone even if they do get it.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

For all those times when an app either isn't available or simply won't cut it, your phone's internet browser provides access to your favorite websites and services. But some browsers are flat-out better than others, and chances are, the browser that came pre-installed on your phone isn't the best option out there.