How many times have you been on the water and you've cast off a crankbait? You pick up the crankbait rod and make a cast, start your retrieve and your bait runs off to the side. Tuning will keep it straight. Wade Bourne, host of Wade's World on MyOutdoorTV, shows you how to tune up a crankbait.

Nothing is better than getting on a bream bed. You'll catch bluefish one after another. Wade Bourne, host of Wade's World on MyOutdoorTV, shows you how to fish for bluegill and panfish in bream beds.

If you like to catch big fish and small fish… anything… then the one way you'll catch anything is with the horsehead jig. Wade Bourne, host of Wade's World on MyOutdoorTV, shows you how to use the horsehead jig.

If you follow the Anonymous, Occupy, and IT security scenes, you have no doubt heard about a dox release. What is it? How can it hurt you? And most importantly, how can you protect yourself from it? Some of these steps might seem common sense, while others will be an ah-ha! moment. Your private info is both your biggest weakness and your biggest weapon in your battle to remain anonymous. You must learn how to use it as both.

In Google definitions a macro is defined as "a single computer instruction that results in a series of instructions in machine language". Basically a macro is a programming script that tells the computer what to do. You can tell a computer (via a macro) to move a mouse, click, type or do any task that a computer can do with automation. There are also many (primitive) computer viruses that are coded entirely in a macro script. There are many ways to create a macro script but I will only go ove...

Though under a lot of the average consumer's radar, the CISPA is now making rounds again with a coalition of advocacy rights groups. The act, known as the Cyber Intelligence Sharing and Protection Act, forces companies to ignore existing privacy laws and share information with the Federal Government. This short article will bring you up to date on this bill. The CISPA is another bill 'designed' to help prevent thefts and prevent them in cyberspace. But again, like all the previous bill before...

In this article, I'll be covering Triggers and Coils, part two of the series (see part one here). Generally, a simple EMP generator consists of four components; a capacitor, a transformer, a trigger and a coil of copper wire. The transformer component can be varied, but the coil is very important, and must be precisely tuned.

Children under the age of 13 possess insight that can blow the minds of their elders, but not the wherewithal to make important life choices for themselves. This is exactly why there are strict rules against marketing cigarettes to them. In 2000, a law went into effect called the Children's Online Privacy Protection Act that institutes similar consumer protections for our youth's online identities, prohibiting companies from soliciting personal information from children under 13 years of age ...

It's been a great year for video games, kind of. Sure, the AAA release lineup has been a trainwreck and hacking has been a bigger problem than ever. But two things have happened involving the federal government that have made video games more legitimate in the United States than ever before. The Supreme Court ruling establishing that video games were the equivalent of movies and books, not porn, was the more significant decision. But in May, the National Endowment for the Arts made another si...

Could the world really be coming to an end tomorrow? Presuming you believe the biblical prediction from 89-year-old Harold Camping, May 21st, 2011 is undeniably Judgment Day. If you have confidence in that prophecy, you're probably not even reading this because you're too busy either A) preparing for the Rapture or B) sitting in your backyard bunker hoping to outwit annihilationism.

FOXBORO, Mass. - The New England Patriots Alumni Club (NEPAC), announced that more than a dozen former Patriots players are gearing up to host a "Football for You" youth clinic in Worcester on Saturday, May 29 from 12:30-5:00 p.m.

In the news this past couple of days, we've heard of about 10 Argentine hooligans being deported back to Argentina before the start of the World Cup. I'm glad for the South African authorities showing that they have a firm grasp of security leading up to Friday's kick-off, and that the inter-agency cooperation between countries was a serious one.

Tesla coils are totally insane, yet undeniably captivating. And they can be used for many things, from electric painting to dueling musical battles. But one trigger happy fellow has a different use for Tesla's lightning shooting coil. A weapon.

The possibilities are endless for 3D printing. With your very own 3D printer, you can make spare parts, circuit boards, inflatable balloons, duplicate keys, Minecraft cities, and even tiny replicas of your face. From a more artsy standpoint, you can make complex sculptures, like this cool mathematical sculpture of thirty interwoven hexagons by Francesco De Comite:

A proxy is a server that lets a client to connect to it and forward its traffic. This enables a certain "layer" of protection by masking your IP. An IP address can be used to learn your location and track you on the Internet, thus eliminating any form of anonymity that you may have.

Web-spying technologies like FaceNiff, Firesheep and Newstweek are out there showing the world just how easy it is to see what you're doing online, but they're amateurish in comparison to what real hackers could do to you if they catch you browsing unsecured websites.

Largely thanks to Banksy's critically acclaimed, Oscar-nominated docu Exit Through the Gift Shop, the pseudonymous British graffiti artist's notoriety has skyrocketed—so much so that there's now an app for geo-locating a Banksy-near-you. If you've got an iPhone and you're a fan of the artist, you're in luck. For $1.99, Banksy-Locations detects your current location and if there's a piece nearby, drops a pin on the map, locating and identifying the name of the work. The app also contains compr...

Danny MacAskill has been a cycling and internet god since the day he surfaced on YouTube back in April of 2009. A Scottish street trials pro rider for Inspired Bicycles Ltd., MacAskill has been practicing his stunt riding for over 12 years. He gave up his job as a mechanic to ride full time, and now appears in music videos and commercials.

WonderHowTo favorite NurdRage once again triggers the inner mad scientist in all of us (well, all of us WonderHowTo-ians at least). Below, watch what happens when steel wool- found in every common household Brillo Pad- is lit on fire.

Every day of the week, WonderHowTo curators are hard at work, scouring the web for the greatest and most inspiring how-to videos. Every Friday, we'll highlight our favorite finds.

Update 9-9 1 day free gift: Farmhands!

At times during the last nine months the crew of Cork might have thought this moment would never arrive but on Sunday evening at 1947 local time (1847 GMT) they crossed the finish line at Kinsale; an emotional moment as they led the Clipper 09-10 Round the World Yacht Race fleet into their home port at the end of the final transatlantic crossing of the 35,000-mile contest.

Time to call up Guinness. Professors of Notre Dame University have supposedly invented the shortest possible game of Monopoly. Over in four turns (that's just nine rolls).

Be Still My Beating Heart, it's Heart Beet Gardening! So we all know that eating organic can be a challenge sometime to our pocket books. With tomatoes being $3 a pound some places, I often get asked how can I eat organic without breaking my bank account. One solution, grow your own! Not sure how to do that? Heart Beet Gardening is here to show you how!

Today's WSJ takes a tour of Russian billionaire Andrey Melnichenko's 394-foot insanely luxe yacht, coined "A".

Apple used to be a great, innovative company. But lately, it's filling its coffers with money raked in from selling folks on "new" and "unique" features that have been blatantly ripped off from Android.

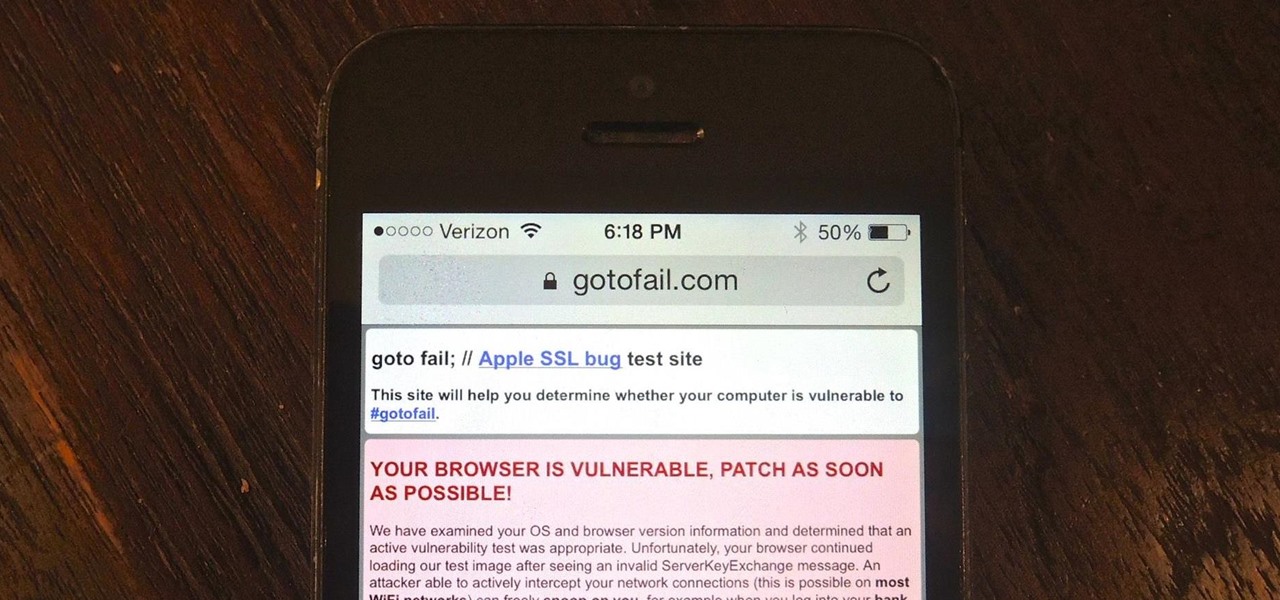
Apple released iOS 7.0.6 last week, an update to fix a serious security flaw that allowed hackers to not only capture sensitive user information such as bank statements and passwords, but also modify that same data on secure HTTPS sessions.

If you want to avoid the hassle of going out on New Year's Eve, you can always host your own New Year's Eve celebration at home—and it doesn't have to cost a lot, either.

Unlike your more artistically-minded friends who've been working on their homemade, hand-stitched, conceptually-brilliant Halloween costumes since May, you need to put together a last-minute costume in a matter of hours. What can you possibly do if you're cheap, kind of lazy, and don't know how to sew to save your life?

Have one of the most beloved characters on jackass(steve-o,jhonny,bam) fake his death for the world to see, have them pretend to rob a bank and have a cop in there at the same time, so when they hold up the bank they get shot and since its a bank there will be cameras so thats how they got it on tape, remember this will all be fake but nobody will know. or you could fake a car crash and it would have the crew in there about to go film but only 1 would die and the rest would b just hurt.or som...

"Connect via Facebook" — these words are coated on over a million websites nowadays, but Facebook Connect poses a risk of leaking personally identifiable information to those third parties. If you're not convinced Facebook Connect is safe, then turn off the flow of personal data to those websites!

This is a two-part series to locking down the computer to provide maximum protection. Even though this guide will sound intrusive, we are talking about reality here. Extreme measures must be taken to protect our computers, especially when we have confidential documentation or do internet banking, which many people do. We all have to use electronic devices at some stage, whether it be for business or personal use.

Have you ever gone on a long internet binge, researching and surfing mindless things, and thought to yourself: I wish I could make some money surfing the internet and sharing the (sometimes useless) information I had just acquired? Well, now you can!

The most recent viral video on YouTube is just that. A viral video. After seeing all the hype and 'support' that the 'movement' is getting, I want to tell you that this is a misleading video and somewhat of a propaganda campaign. These are strong accusations against such a 'humanitarian' cause, but I'm here to show you why.

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Big name individual hackers and hacker groups everywhere in the news are getting caught and thrown in jail. Everytime I see something like this happen, I won't lie, I get a little sad. Then I wonder, how are these guys getting caught? If a group like LulzSec, with all the fame and "1337-ness" can get caught, I think my hacker comrades are doing something wrong.

Movies like to show hackers breaking passwords with fancy software and ludicrous gadgets. The reality of busting passwords open is much more mundane. Simple as it may sound, most passwords are broken purely by guesswork. Check out this infographic from ZoneAlarm, as well as this list from the Wall Street Journal of the fifty most common passwords gleaned from the 2010 Gawker hack. If your password is on one of those lists, you need to change it. Right now.

It's really a shame that it is so hard for people to make money on the internet these days. The dot com bubble has receded and scams are plentiful on the web. There are, however, a couple of legitimate ways to make a few extra bucks online, Amazon Mechanical Turk, or MTurk for short, is one of them. The idea of MTurk is to hook up programmers with people that do tasks that computers can not, these tasks are called HITs (Human Intelligence Task). These tasks include article creation, creative ...

Note: Little Brother is available as a free ebook download. Warnings

The United States is a hierarchical country where the weak ones are at the bottom and the powerful ones are at the top. Garment workers are at the bottom of the list although they are the most important. Without them there would be no fashion industry. They sew and cut the garments that people buy, the raiment that models wear on the runways. After the garments are sewn, factory owners send the garments to contractors to get make the clothing. Contractors make sure the garment workers sew the...