Is someone threatening, following, or preventing you from carrying on a normal, healthy safe life? Protect yourself from the threat of injury or physical harm by filing a restraining order. In this video, learn what steps are needed to file a restraining order.

Hula-hooping isn't just for kids. It's a fun and exciting way to stay in shape. You Will Need

Welcome back, my hacker apprentices! In recent weeks, the revelation that the NSA has been spying on all of us has many people up in arms. I guess I take it all in stride as I just assume that the NSA is spying on all of us—all of the time. Don't get me wrong, I don't condone it, but I know the NSA.

Microsoft decided to give users a free upgrade to Windows 10 if they were previously running Windows 7 or 8—but it came with a catch. Their main motivation for knocking off over $100 from the normal going rate was to get more people using new Microsoft services like Cortana and the Windows Store. To bolster these services, Microsoft implemented a host of new tracking "features" in Windows 10.

This past weekend, one of the most notorious hacker organizations in the world, Hacking Team, was hacked by some unknown organization. The Hacking Team is an Italian company that sells it software and services to companies and governments (yes, my rookie hackers, there are legitimate companies who sell their services to governments—Vupen, being one of the most famous and lucrative).

If Detective Alonzo Harris from Training Day taught me anything, it's that "It's not what you know, it's what you can prove." So when items mysteriously go missing from my room or my section of the fridge, it's up to me to figure out and prove which roommate took them.
Welcome back for another How-To on the Xbox Community Ambassadors World! In this How-To, we are going to tell you how to help someone the right way so you can get a 9/9 rating when your finished assisting someone! Lets begin, shall we?

Welcome back, my budding hackers! People often ask me, "Why are you training hackers? Isn't that illegal?" Although I usually give them a short version of this post, there are MANY reasons why YOU should be studying hacking.

Unlike the suave 007 that Daniel Craig portrayed, I am not a spy, nor am I that charming, but I do occasionally enjoy taking a stealthy video. Maybe I'm a jerk, but I often catch people doing ridiculous things and just think, "Aren't you embarrassed?"

Who am I? First let me introduce myself. I am Th3skYf0x, an -well lets call it

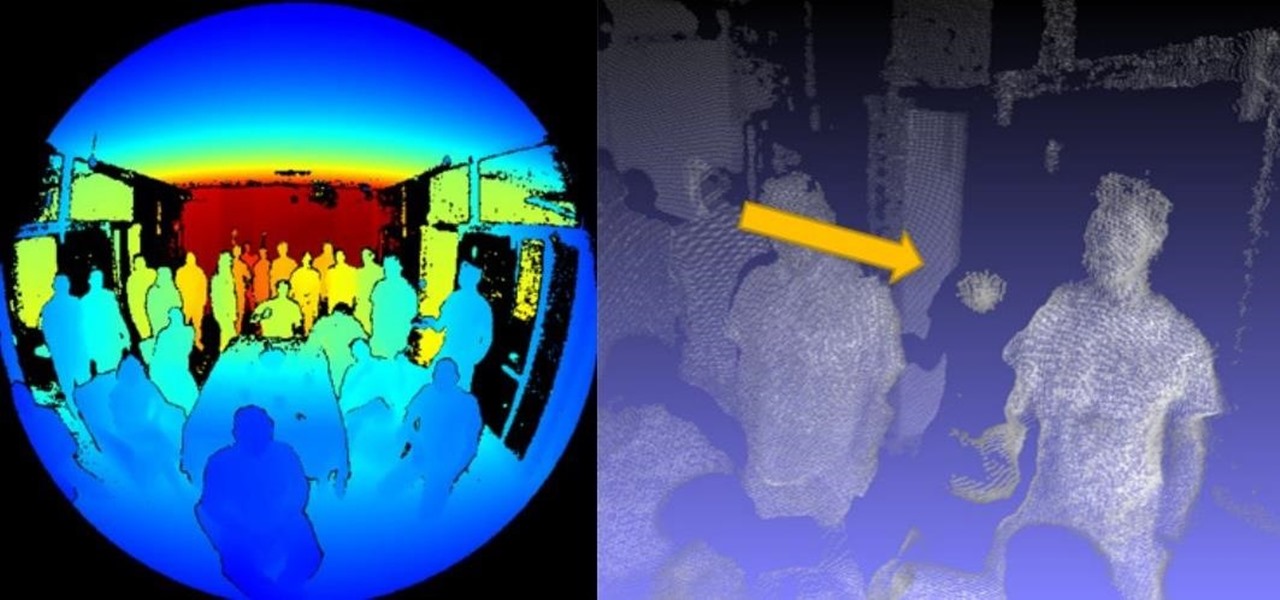
Robert Templeman from the Naval Surface Warfare Center in Crane, Indiana and several of his friends from Indiana University recently developed an Android application that is capable of gathering pictures and videos from mobile devices in order to reconstruct a user's environment in 3D. The malware would come coded inside of a camera application that the user would download. The malware, called PlaceRaider, would then randomly take pictures throughout the day and carefully piece them together ...

If you're tired of your roommate stealing your Cheetos out of the pantry or simply want to indulge in something creepy, then keep reading. With the iPhone 5 finally released, many people will soon be selling or giving away their older iPhones. But should they? Instead of ditching your old iPhone, why not use it to engage in some Big Brother type espionage? There are some really awesome ways to use your old iPhone, but spying on people is definitely the most bang for your buck. First, you'll w...

Tyson Mao is a renowned world competitor in solving the Rubik's Cube. Not only did this Californian become a world class solver, but he also formed the Rubik's Cube Association with fellow speed solver Ron van Bruchem, which holds competitive events for the Rubik's Cube. If you want to learn how to solve the colorful and mighty puzzle, then who better than to learn from then Tyson Mao?

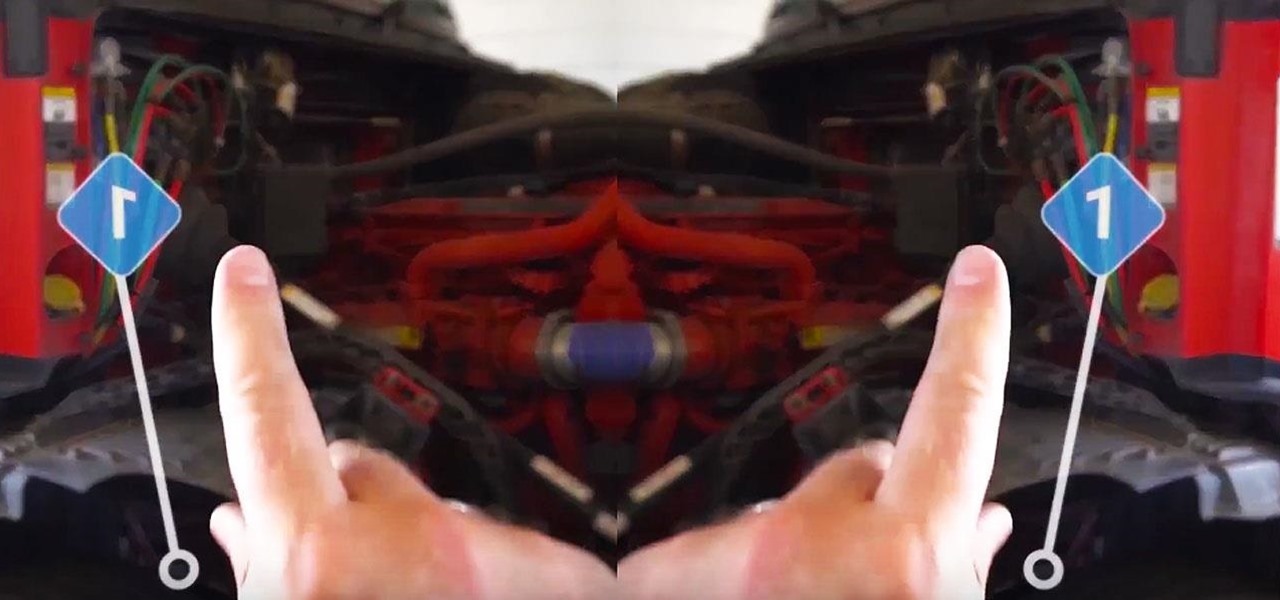
If there was a version of the Doomsday Clock for counting down the release of Microsoft's HoloLens 2, then the caretakers of that imaginary clock would move the minute hand to "one minute to midnight."

The mystery surrounding the release of the next version of the HoloLens has been swirling for months, but at least some of that mystery may removed in the coming weeks.

Images captured by Microsoft's next generation Kinect depth-sensing camera that will facilitate augmented reality experiences in the next version of the HoloLens and give computer vision to untold multitudes of connected devices in enterprise facilities, have made their way into the wild.

All the cash Magic Leap is amassing is probably going a long way toward hardware development and manufacturing, but it's also becoming increasingly clear that a large portion of that cash will be devoted to content. The latest proof is a new partnership between Magic Leap and the UK's Royal Shakespeare Company (RSC).

Enterprise augmented reality developer Atheer is bringing its AR solution for enterprise businesses to the HoloLens by way of a joint venture with fellow AR developer Design Interactive.

It seems fitting that Time magazine's first augmented reality cover is an issue guest edited by Bill Gates, since the company he founded is currently leading the AR charge via the HoloLens.

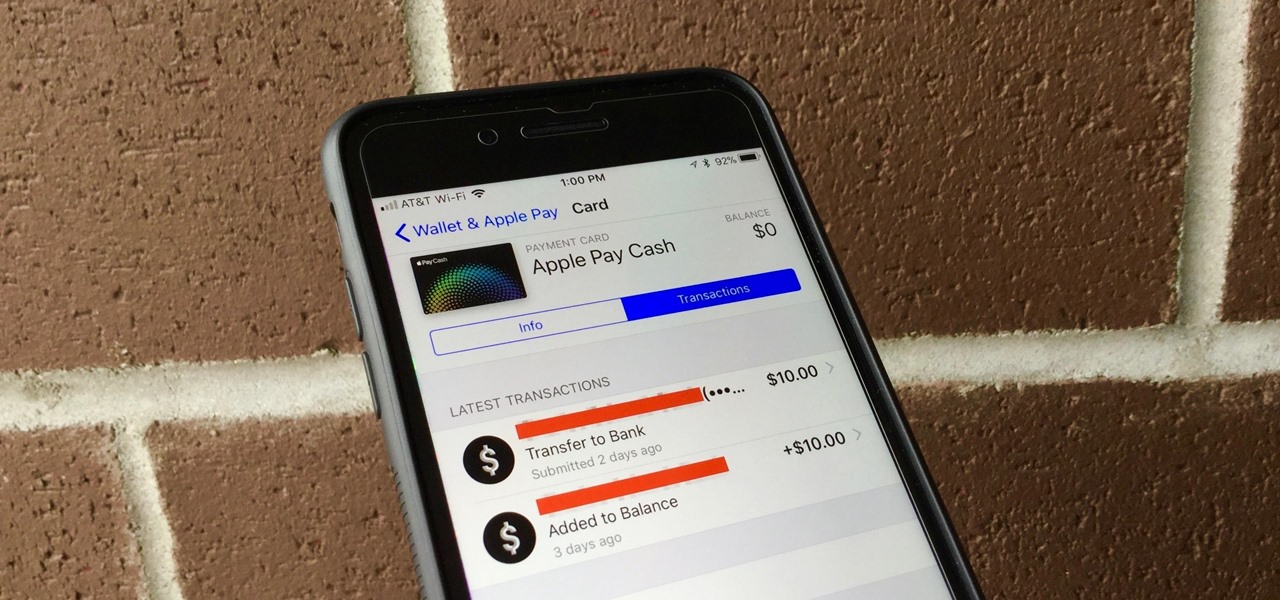
With Apple Pay Cash, sending and receiving money with fellow Apple users has never been easier. One big plus about Apple's new Apple Pay Cash card is that all of your transactions are available just a few taps away, so you can see all your person-to-person payments, balance additions, and bank transfers.

At their event in San Francisco today, Microsoft announced that they have begun accepting pre-orders for Windows Mixed Reality headsets from Acer, Dell, Lenovo, and HP, with the devices arriving on Oct. 17 along with the Windows 10 Fall Creators Update.

While augmented reality is a means for presenting news to their audiences to some media outlets, Bloomberg is interested in how the technology can improve the way journalists work.

If you own a Samsung Galaxy S7 and use the Samsung Gear VR, you may have woken up yesterday to an unpleasantly hot surprise. But don't worry—your phone isn't going to explode (probably). The problem is with a stubborn update to the Oculus apps.

The first White Hat Award for Technical Excellence tutorial contest ended last night at midnight! We had many excellent articles submitted, once again re-affirming what an incredible community we have here at Null Byte! We had quite a flurry of great articles in the last few days. Thanks to all of you who submitted such high quality material to our community. Your efforts are appreciated and you have the undying gratitude of our community. We will not forget your efforts. I'll be reading and ...

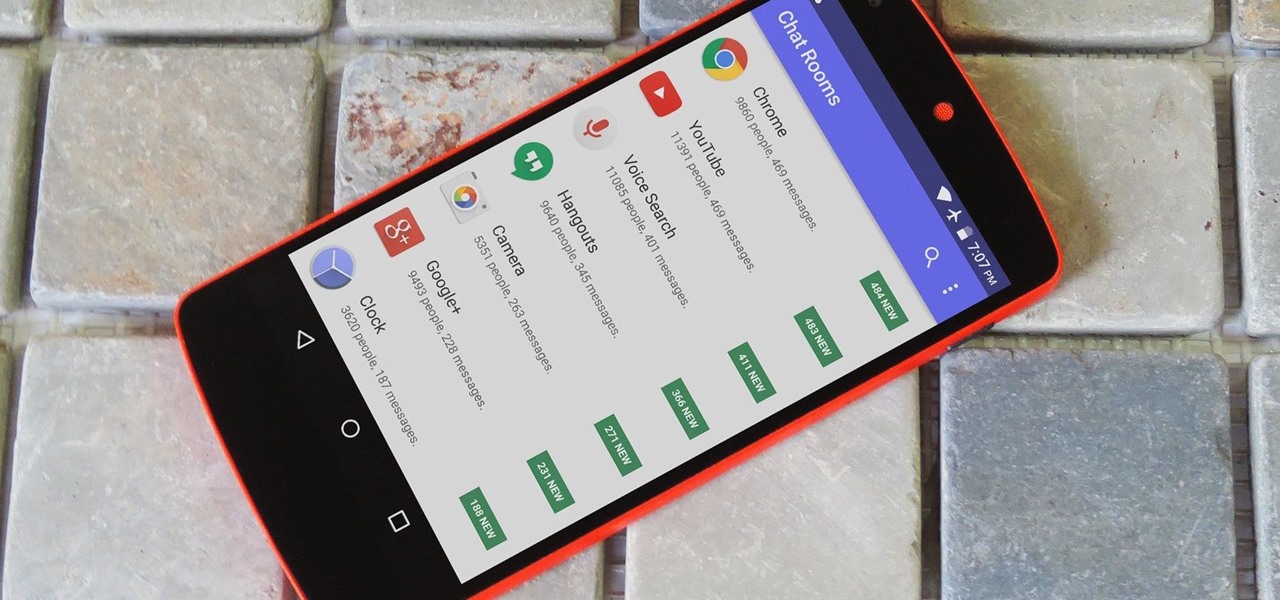
As with any software, Android apps can occasionally suffer from bugs. But finding the root cause of such issues can often be difficult, and reporting bugs is a cumbersome experience.

Welcome back my fellow hackers. Today I'm going to teach you how to preform an Idle Scan. You may be asking what is an Idle Scan. Its a very stealthy scan because you don't use your own ip you use a zombie (in computer terms).

Well Welcome Back My Fellow Hackers. What is Slowhttptest? You may be asking. Slowhttptest is a Application Layer Denial of Service attack aka an attack on HTTP. You can read more about it here and also download it if you don't have Kali Linux. slowhttptest - Application Layer DoS attack simulator - Google Project Hosting.

There's no TV show that stands out quite like American Horror Story. With its crazy characters and nightmarish storylines, there are countless costume ideas hiding in its episodes.

Hello fellow peoples of the earth and welcome to another tutorial by me! Noah! you know popcap make bejewled blitz and zuma and pvz for facebook but what if you want the big games like pvz or bejewled 3 from them but don't want to pay. Then worry not as this simple tutorial will help you get those games you enjoy for free without any trials or limitations! to the startthetutorialmobile

If smartphone video games have a weakness, it's probably their inability to emulate the riveting and immersive experience that consoles offer.

There are several ways to send pictures to others on your smartphone—picture message, email, Bluetooth, and even by bumping phones together. Now there's an even more unique way to transfer pictures from one Apple device to another—with sound. Chirp for iPad, iPhone, and iPod touch

Welcome back, my tenderfoot hackers! A short while ago, I started a new series called "How to Spy on Anyone." The idea behind this series is that computer hacking is increasingly being used in espionage and cyber warfare, as well as by private detectives and law enforcement to solve cases. I am trying to demonstrate, in this series, ways that hacking is being used in these professions. For those of you who are training for those careers, I dedicate this series.

Ever since the FBI took down the Silk Road and Dread Pirate Roberts last month, many questions have been raised about whether Tor still provides anonymity or not, and if it's now broken. I'll try to address that question here today succinctly from multiple angles, keeping it as simple and plain-language as possible. The Closing of Silk Road

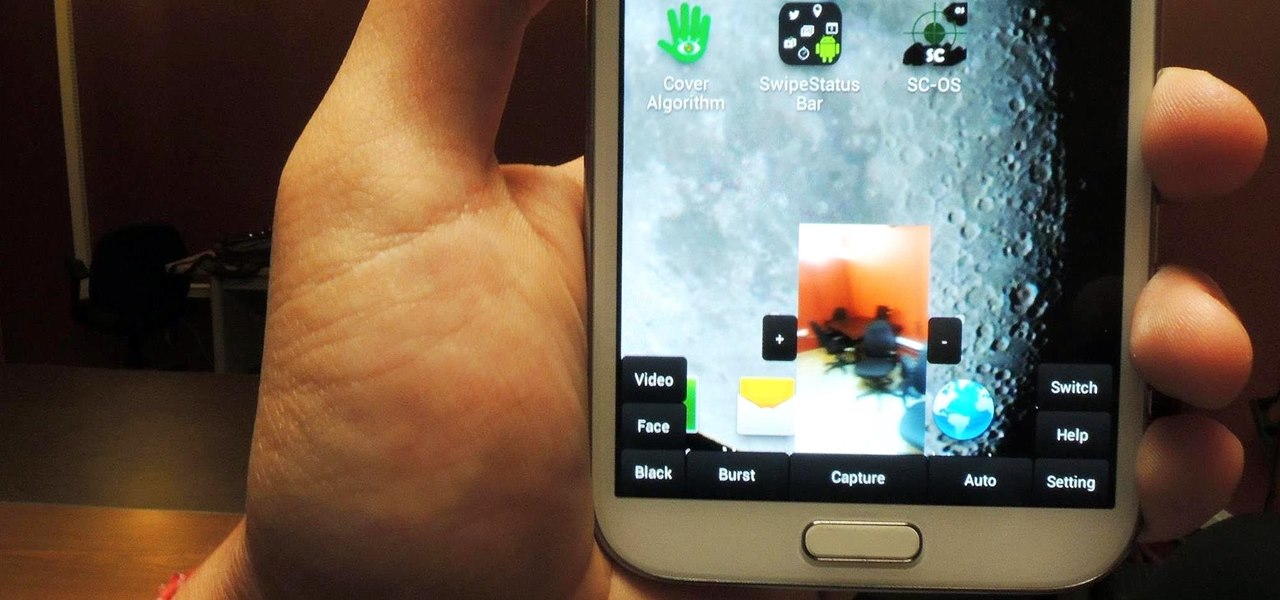
Sometimes, for whatever reason it may be, we just want to take a photo without anyone noticing. Unfortunately, thanks to the extremely large screen and loud shutter sound, taking a picture discreetly with our Samsung Galaxy Note 2 is a hard thing to do.

What if you could have a secret hard drive connected to your computer that only you could activate? You can! Samimy shows you how to hack a remote controlled toy car and make a super secret hard disk drive in your computer, accessed via a secret activation key. This hidden emergency HDD can only be controlled by your key, regardless of how many people use your computer.

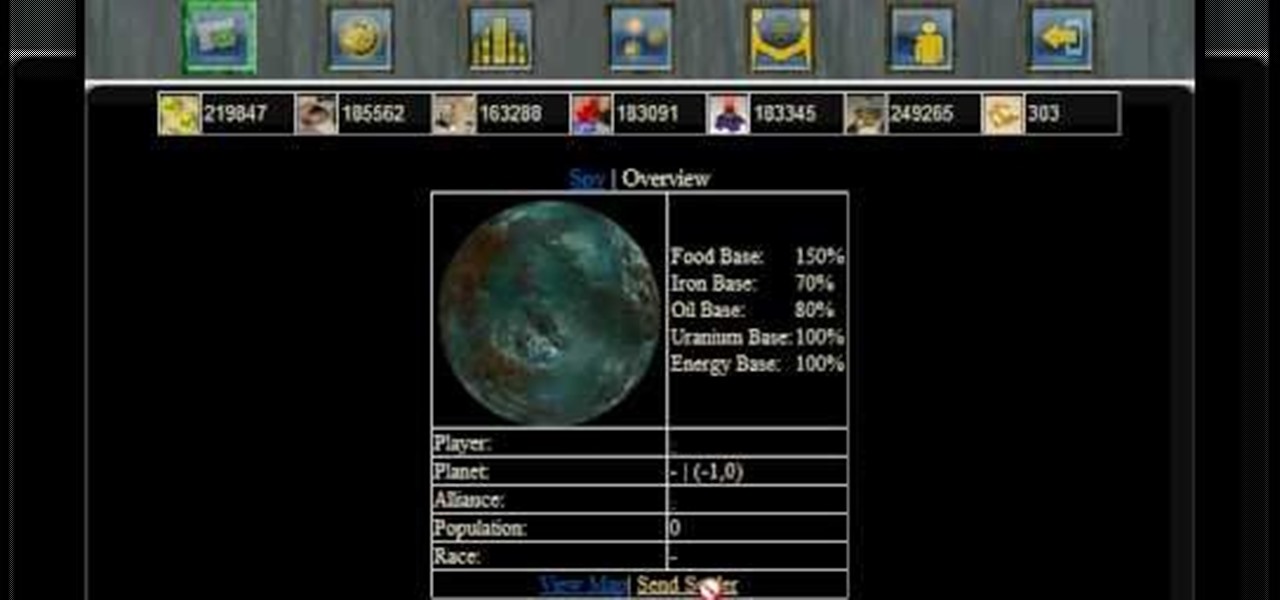
Settling a new planet will decrease your pride ratio, because your population will increase when you're settling a new planet. If you're not sure how to even settle planets...

David L. Spies shows us how to make the best toffee in the world. It only takes four ingredients - butter, sugar, Macadamia nuts and semi-sweet chocolate chips. Chop or crush the nuts and have them ready for the final step.

Who better to demonstrate bar tricks than a cute girl bartender? Sexy Francesca teaches a trick to help pick up a chick in a bar. Brush up on your bar tricks so you can impress the ladies (or con your fellow barflies out of a dollar or two). Break presents bar tricks by Francesca. Pick up a chick with this trick.

Here's something you can do with an empty beer bottle. Learn how to take the bottom out in quite the dramatic form. Perfect for entertaining your fellow frat buddies during the morning after clean up.

In recent weeks, some people have been shunned from the Null Byte community because they expressed "black hat" aspirations. This is because Null Byte is the "white hat" hacker training/playground. Although most of us think we know what that means, it does beg the question; "Who and what is a white hat hacker?"