If you're feeling extra adventurous with your new Android-based Samsung Galaxy S phone, aka Vibrantor Captivate, watch this video tutorial to learn how to root it in a few quick steps. Rooting your Android phone may give you a few benefits over a regular version, such as easy wi-fi tethering, better keyboard and even multi-touch browsing.

No Wi-Fi? No problem. All you need is a Bluetooth-enabled phone and laptop to surf the Web from anywhere.

In the sci-fi epic Star Wars, the smuggler Han Solo travelled the universe in an old transport called the Millenium Falcon. Learn how to fold a simple version of your own in this origami tutorial.

Check out this 2 part walkthrough video series from Resistance 2 level Battleship. Resistance 2 is a sci-fi first person shooter video game. Resistance 2 is the sequel to the best-selling exclusive PlayStation 3 launch title Resistance: Fall of Man.
This is a video tutorial on how to set up a very simple foil parabola to increase your wireless signal at your home.

This tutorial teaches you to delete files,restore files or delete files permanently in cPanel. This video is provided by Scandicsoft

This tutorial teaches how to create new folders and files and how to move them to new directories using cPanel.

Here's how to make a cool laser gun using some household junk and silver spray paint. It's a Sprite bottle, by the way. It's best if it's empty too. Really.

Kitchen utensils and computers, that's right! This video will show you how to increase your computer's wireless connection using a strainer!

If you don't want to go through the hassle of setting up a formal network between two Macs, but still want to transfer files between the two, take a look at Airdrop. Airdrop is a built-in utility found in Mac OS X Lion (10.7) that will allow you to easily drag and drop files to another computer belonging to you or a friend.

In many urban areas, GPS doesn't work well. Buildings reflect GPS signals on themselves to create a confusing mess for phones to sort out. As a result, most modern devices determine their location using a blend of techniques, including nearby Wi-Fi networks. By using SkyLift to create fake networks known to be in other areas, we can manipulate where a device thinks it is with an ESP8266 microcontroller.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

As you might know, Tidal differentiates itself from the competition with its audio quality. Unlike Spotify and Apple Music, it aims to give its subscribers studio quality audio from any device. However, before you sign up for Tidal, be aware there are few steps you need to take in order to stream such high-quality music.

The most common Wi-Fi jamming attacks leverage deauthentication and disassociation packets to attack networks. This allows a low-cost ESP8266-based device programmed in Arduino to detect and classify Wi-Fi denial-of-service attacks by lighting a different color LED for each type of packet. The pattern of these colors can also allow us to fingerprint the tool being used to attack the network.

Some of us woke up at the KRACK of dawn to begin reading about the latest serious vulnerability that impacts the vast majority of users on Wi-Fi. If you weren't one of those early readers, I'm talking about the Key Reinstallation Attack, which affects nearly all Wi-Fi devices.

Google's new Pixel and Pixel XL flagships are some very powerful smartphones, but as with any high-tech gadget, they're only as capable as the user allows them to be. So if you're a proud new Pixel owner, it's time to bone up on a few new features to help get the most out of your device.

Cellular carriers like to nickel-and-dime us out of every bit of money they can feasibly justify, so as consumers, we owe it to ourselves to make sure that we're getting our money's worth.

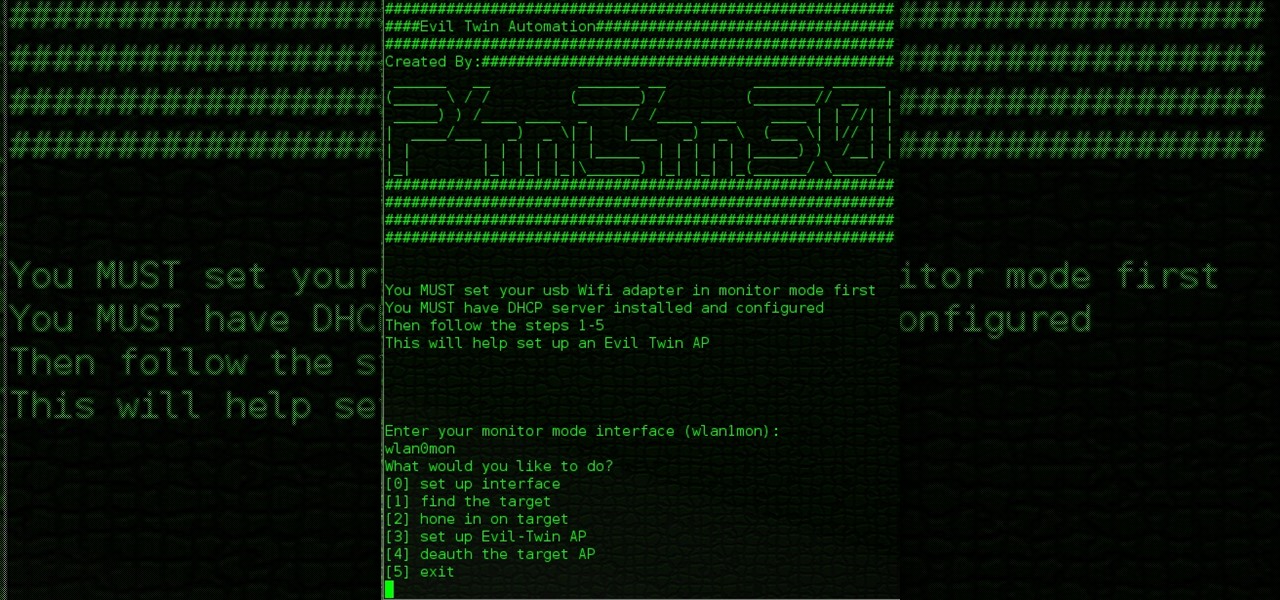
Hello All, So to recap in part 1 I went through setting up the dchp server. Part 2 detailed the bash script. Now in part 3 I will post the entire bash script. I am doing this in its own post because Part 2 is just way to much info on one post IMO.

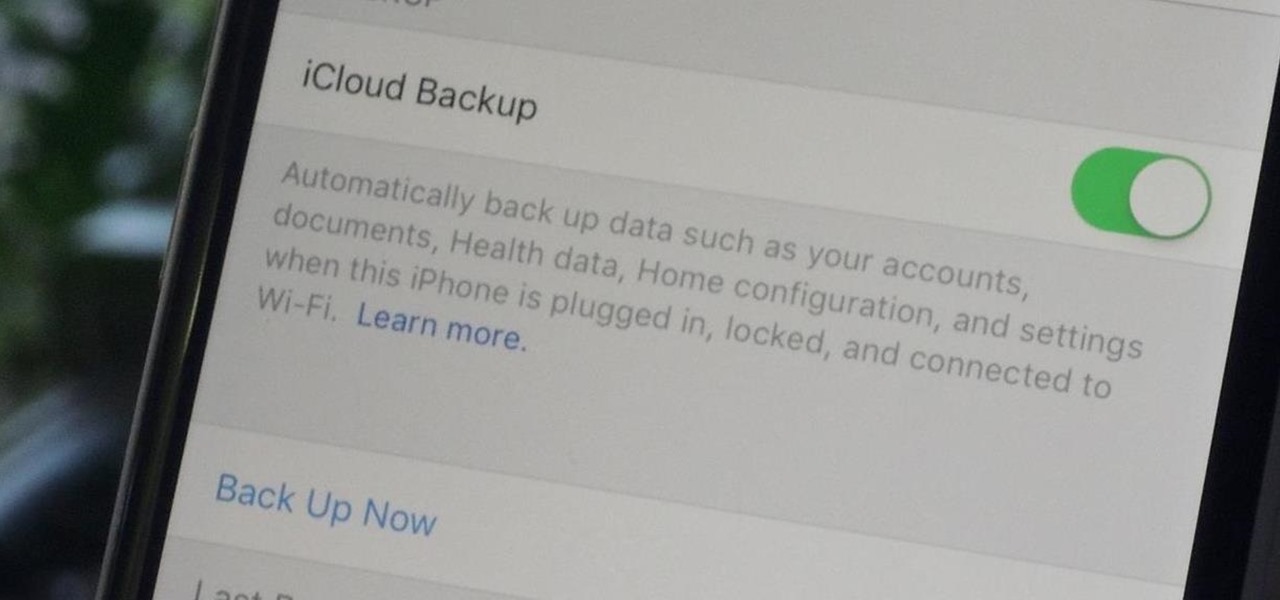
Enabled from the moment you first booted up your device, there's a feature deep in the iPhone's settings that automatically backs up your device in the background. As long as you're connected to Wi-Fi and a power source and your screen is locked, your photos, text messages, apps, and everything in-between gets safely stored to your iCloud account.

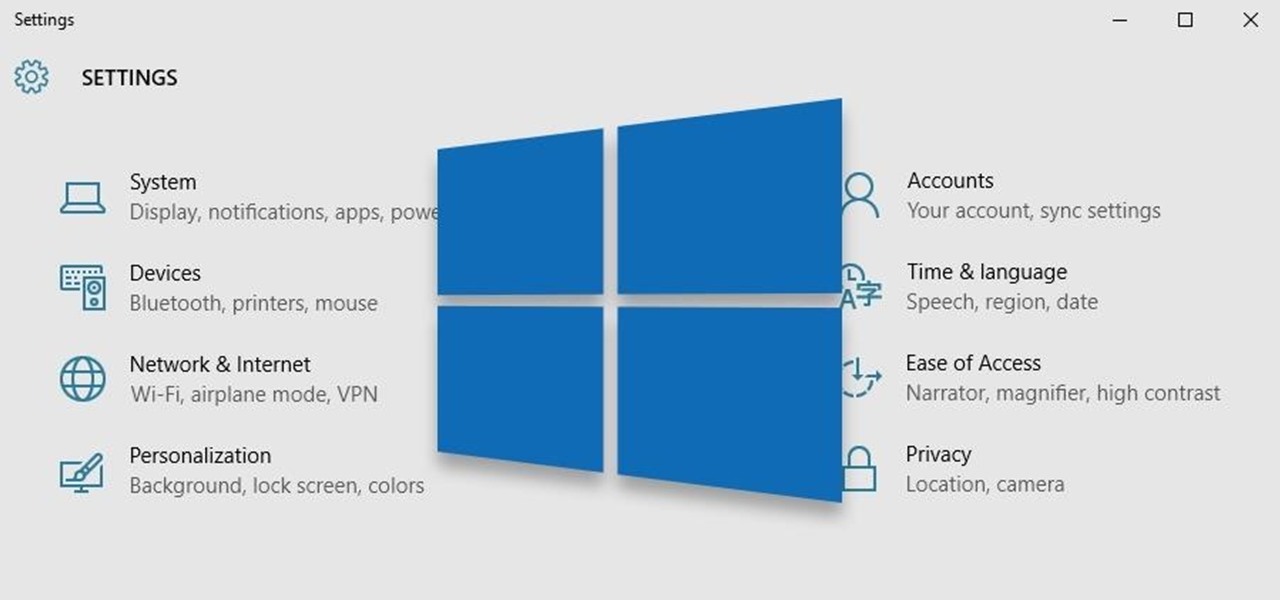
Windows 10 is the most cloud-oriented version of Windows to date—yet, while this means you get some nifty new features, it also means some of your personal data is being shared with Microsoft's servers.

One of the latest home-improvement gadgets out there today, smart lighting, has become more popular as prices come down. That being said, its still quite a penny to shell out. In this article, I'll go through a few of the top products out there today, including the Philips Hue, Belkin WeMo, and Lifx.

Hi Elite Hackers! Welcome! to my 4th post. This tutorial will explain, how to extend a (hacked) AP's range with a wireless adapter. I made this guide because after hacking an AP it was difficult to connect to it (poor connection) and further exploit it. You can also use this:

Welcome back, my nascent hackers! Like anything in life, there are multiple ways of getting a hack done. In fact, good hackers usually have many tricks up their sleeve to hack into a system. If they didn't, they would not usually be successful. No hack works on every system and no hack works all of the time.

When you're actively using your phone, a certain amount of battery drain is to be expected. But, if your device is just sitting in your pocket draining its battery, that's when you need to take action.

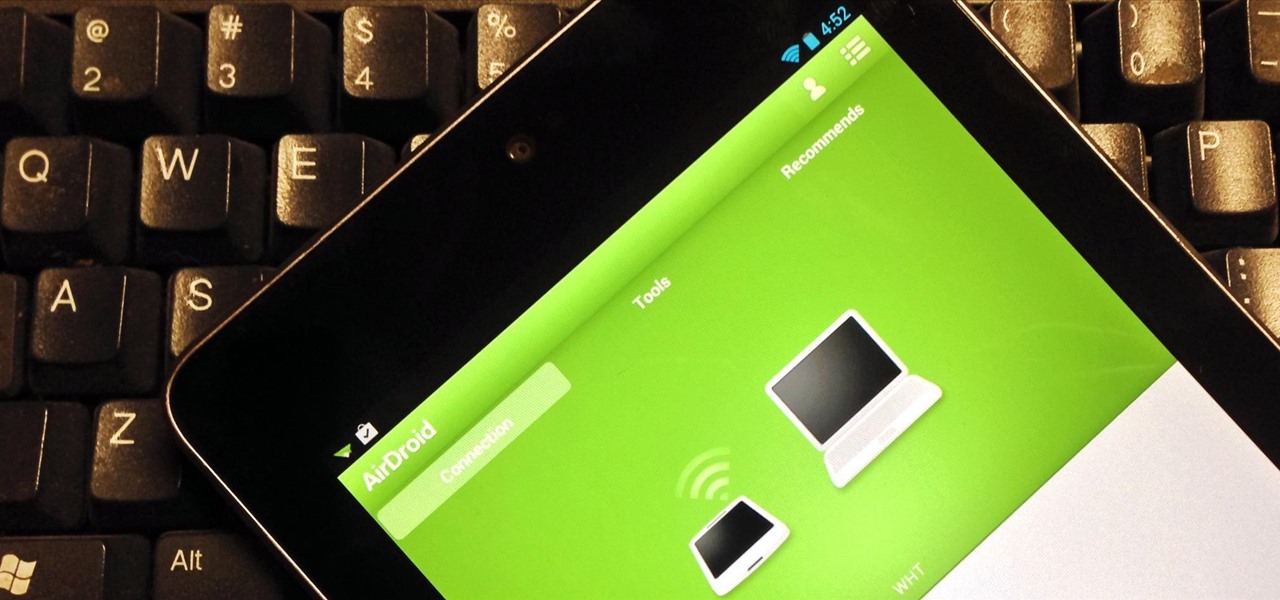
For the most part, transferring files from your computer to your Nexus 7 (and vice versa) is a simple process. Just hook up your tablet to your computer with the USB cable and transfer. However, most of the time you'll need additional software on your computer to do this, and then, of course, you need the USB cable.

Welcome back, my greenhorn hackers. When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy was created to give wireless communications confidentiality. WEP, as it became known, proved terribly flawed and easily cracked. You can read more about that in my beginner's guide to hacking Wi-Fi.

One of the coolest features of the Samsung Galaxy S4 is Group Play, which lets you connect other Samsung Galaxy S4s up to yours so you can use them as extra speakers to create a surround-sound stereo of sorts.

Welcome back, my hacker apprentices! My recent posts here in Null Byte have been very technical in nature, so I thought that I'd have a little fun with this one.

If you're looking for ways to get all James Bond on someone, you may want to check out this video. In it you'll see how to turn your iPhone into a spy camera, letting you take photos or videos at set intervals, or, whenever the mic detects any sound. It's pretty cool and not hard to do! Requirements: 1. iPhone 2. iPad 3. Wi-Fi (bluetooth works aswell but not as good) 4. a place to put iPhone 5. spare time! So remember, the name is phone. iPhone.

It's funny how unevenly the real world keeps pace with science fiction. Smartphones have capabilities that Gene Roddenberry never imagine a portable device could have, but guns still use tiny powder cartridges to launch hunks of metal at things. The phasers, ray guns, and blasters of Star Wars, Star Trek, and other sci-fi works have yet to appear. Don't let that hold you back! This video will show you how to make a cool retro ray gun prop that you can use with a Halloween costume or in a film...

If you're making films on your own, good on you. Do you ever find yourself without the money or means to get the props that you need? Every day most likely. This video is here to both inspire and provide practical aide. It describes the construction of a really cool sci-fi gun (dubbed the MKX300) that this filmmaker made for his webseries out of mostly old bottles. It was cheap and looks incredible, so watch this video and either make your own MKX300 or apply these lessons to the construction...

Making really attractive titles for your films is just one of the way that you can dramatically improve them using After Effects. This video will help you make them by showing you how to create a pulse or pulsating wave effect from whence your titles can emerge. They look great, and will make your movie (especially horror or sci-fi movie) look much more professional right from the beginning.

Right out of the box, iPhone is incredibly easy to use. If you want to get the most out of every feature, you’ve come to the right place. This video tutorial straight from Apple will teach you how to shop iTunes on the Apple iPhone 3G. The iPhone redefines what a mobile phone can do.

See how to build a weatherproof compact high gain WiFi antenna for under fifteen dollars! This homemade WiFi antenna should be enough for most applications, since it's three times more powerful than a standard antenna.

It's time to solve that Rubik's puzzle of yours, but how do you do it? Erno Rubik designed these three-dimensional mechanical puzzles to be precariously difficult, unless you know a little about mathematical algorithms, then it's just a matter of time and determination.

Low battery – two words you never want to hear. Banish them with these tips. You Will Need

For years, Android has provided easy ways to view all the Wi-Fi networks you connected to in the past, and you can even see the saved passwords in plain text. With iOS 16, Apple finally gave us a similar way to view saved Wi-Fi hotspots, copy their passwords, and remove old ones without being near their access points.

You see it in the movies all the time. A character on the phone doesn't like what the other person is saying or telling them to do, or they just don't want to talk to them anymore, so they fake bad reception and cut the call off. In real life, it's pretty easy to tell when someone is doing it, and there are better ways to end a call abruptly so that it looks like you didn't hang up on them.

The only thing better than programming MicroPython is programming MicroPython over Wi-Fi. So once you set up MicroPython on a microcontroller and have it on its own power source, you won't need to use a data cable to connect to it whenever you need to interact with it, program it, upload files, or grab data.